Vulnerabilities discovered by the Talos Vulnerability Development Team. Blog post authored by Alex Chiu.
Securing your network and environment is a challenging task, especially when organizations need to keep track of various software packages that are used on a daily basis. Productivity suites, such as Hancom Hangul Office, are an example of critical software that organizations need to track and patch amongst other things such as operating systems, browsers, and antivirus. Talos is committed to helping our customers be as secure as possible through a variety of means, such as identifying zero-day vulnerabilities in critical software packages. Today, Hancom is disclosing 8 arbitrary code execution vulnerabilities identified and reported by Talos. Hancom has released a software update that addresses these vulnerabilities and Talos would like to sincerely thank Hancom for their cooperation.
Hancom Office is commonly used in parts of the world and is known to be used in various government organizations, public institutions, and non-governmental organizations in South Korea. In fact, the South Korean government previously made Hancom Office its official productivity suite for use on government systems. By some estimates, Hancom has around 30% of the productivity suite market share in South Korea.
The fact that there is a sizeable installation base of Hancom Office makes it an attractive target for adversaries to leverage and exploit. It's believed that the North Korean government is behind several targeted attacks that exploited vulnerabilities in the Hangul word processor. Other companies have previously documented these incidents in 2013 and 2015. In addition, Hancom is actively looking to expand its market share in South Korea and abroad.
Vulnerability Details
Multiple vulnerabilities exist within Hancom Office Hcell and Hshow that can be exploited to execute arbitrary code on the affected user's machine. Exploitation of these vulnerabilities is achievable if a user opens a specifically crafted Hshow file (.hpt) or Hcell (.cell) file that exploits one these vulnerabilities. This would allow an attacker to execute arbitrary code of their choosing in the context of the current user. Scenarios where these vulnerabilities could be exploited are spam and phishing campaigns or websites that host user-generated content that an adversary could direct users to download and open on their own host.
The following is a list of each vulnerability Talos has identified in the Hancom Office suite. For more detail on each vulnerability, please refer to the vulnerability report linked or visit the Vulnerability Report portal on our website.
Hancom Office HShow
- TALOS-2016-0144 - Hangul HShow Unspecified Structure Integer-based Heap Buffer Overflow Vulnerability
- TALOS-2016-0145 - Hangul HShow Unspecified Structure Integer-based Heap Buffer Overflow Vulnerability
- TALOS-2016-0146 - Hangul HShow Unspecified Structure Integer-based Heap Buffer Overflow Vulnerability
- TALOS-2016-0147 - Hangul HShow Unspecified Structure Heap-based Out-of-bounds Write Vulnerability
Hancom Office Hcell
- TALOS-2016-0148 - Hangul HCell Workbook Table and Pivot Styles (0x088e) Heap-based Buffer Overflow Vulnerability
- TALOS-2016-0149 - Hangul HCell OfficeArt Record (0x00ec) pConnectionSites and pVertices Heap-based Buffer Overflow Vulnerability
- TALOS-2016-0150 - Hangul HCell HncChart 0x7ef0 CFormulaTokenSizeModifier Index Overflow Vulnerability
- TALOS-2016-0151 - Hangul HCell CSSValFormat::CheckUnderbar Off-by-one Heap-based Buffer Overflow Vulnerability
Known Vulnerable Versions
At this point, Talos has only confirmed these vulnerabilities to be present in the following versions of Hancom Office:
Conclusion
Mitigating the risk of compromise requires that organizations exercise an appropriate level of diligence and awareness. Making an effort to fully identify, document, and patch all the common software packages that are used as well as ensuring that secure development practices are followed are important. Equally important is for defenders to help identify vulnerabilities in software packages and disclose them responsibly.
Talos will continue to research, find, and responsibly disclose the zero-day vulnerabilities we identify in a responsible manner. Developing programmatic methods to identify zero-day vulnerabilities and making sure they are addressed is critical to our efforts in making the internet safer. In doing so, we can gain valuable insight into how we can improve our own development practices and to help secure software that might otherwise be exploited by adversaries.
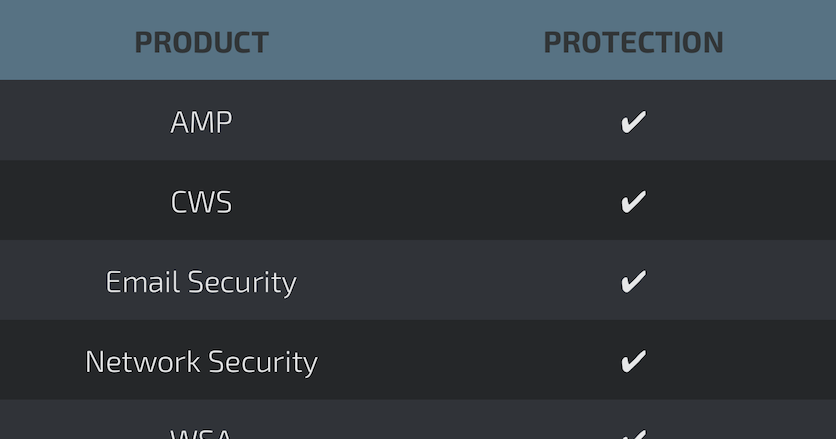
Coverage

The following Snort Rules will detect exploitation attempts of HPT and CELL files:
38856-38859, 38868-38869, 39049-39050, 39110-39111, 39757-39762
For further zero day or vulnerability reports and information visit:
http://www.talosintelligence.com/vulnerability-reports/