When the WannaCry attack was launched a little over a week ago, it was one of the first large scale attacks leveraging the data that was leaked by the Shadow Brokers. At the time the real concern was how quickly we would begin to see other threats leverage the same vulnerabilities. Over the past couple of weeks, Talos has observed other malware variants that are using the ETERNALBLUE and DOUBLEPULSAR exploits from the Shadow Brokers release as part of their campaigns. Among them were Adylkuzz, Uiwix, and EternalRocks.
Adylkuzz is a piece of malware that uses ETERNALBLUE and DOUBLEPULSAR to install cryptocurrency mining software on the infected system. This attack actually pre-dates the WannaCry attack and has continued to deliver the cryptocurrency miner.
Uiwix uses a similar technique to install ransomware on the infected system. When the files are encrypted, the file names include "UIWIX" as part of the file extension. The key difference with this malware is that, unlike WannaCry, the Ransomware doesn't "worm itself." It only installs itself on the system.
Another malware variant we have observed being leveraged by attackers is known as EternalRocks. In this case the malware gains access to the system using ETERNALBLUE and DOUBLEPULSAR, but then just uses that access as a backdoor to install other malicious software on the infected system. One of the notable features of this malware is the 24 hour sleep/delay that the malware does before downloading the final payload which includes multiple other exploits from the Shadow Brokers dump. This is effective in evading things like sandbox environments.
Following the success and the media coverage of WannaCry ransomware it was inevitable that we would see attacks using similar techniques to exploit vulnerable operating systems and spread other types of malware.
Adylkuzz, Uiwix and Eternalrocks are just first examples of copycat spreading and is likely we will see more attacks using the same infection vector in the near future. The combination of the exploit (ETERNALBLUE) and the backdoor (DOUBLEPULSAR) allows attackers to install and run arbitrary code on the affected system.
When mitigating risks, it is important to remember that the best way to prevent attacks exploiting CVE-2017-0143 to CVE-2017-148 as described in the Microsoft Security Bulletin MS17-010 is to apply the security update as soon as it is possible for your organization.
Coverage Talos has observed an increase in malware leveraging these vulnerabilities. The final payload has no bearing on the protection for these attacks. As long as they are leveraging the exploits and tools disclosed by the Shadow Brokers, network based detection will stop it.
These attacks are exploiting vulnerabilities that have been known for at least two months and, depending on the exploit, have been covered by NGIPS and NGFW technologies dating back to mid-March 2017.
Snort Rule: 42329-42332, 42340, 41978, 42256
Open Source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase onSnort.org.
Additional ways our customers can detect and block this threat are listed below.
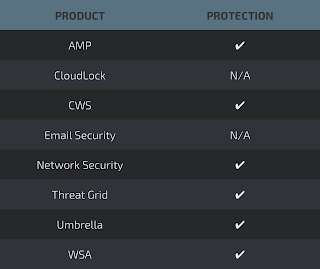
Advanced Malware Protection (AMP) is ideally suited to prevent the execution of the malware used by these threat actors.
CWSor WSA web scanning prevents access to malicious websites and detects malware used in these attacks.
Network Security appliances such asNGFW,NGIPS, andMeraki MX can detect malicious activity associated with this threat.
AMP Threat Grid helps identify malicious binaries and build protection into all Cisco Security products.
Umbrella prevents DNS resolution of the domains associated with malicious activity.
Stealthwatch detects network scanning activity, network propagation, and connections to CnC infrastructures, correlating this activity to alert administrators.