Today, as we do every week, Talos is giving you a glimpse into the most prevalent threats we’ve observed this week — covering the dates between Aug. 31 and Sept. 7. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, we will summarize the threats we’ve observed by highlighting key behavioral characteristics and indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this round up are:
- Win.Dropper.Generickdz-6671833-0
Dropper
This is a BobSoft Delphi application that wraps malware. In the current campaign, the HawkEye spyware is installed. The malware uses process hollowing to keep itself hidden from detection, and achieves persistence across reboots by leveraging an autostart key in the Windows registry. - Win.Dropper.Kovter-6669952-0
Dropper
Win.Dropper.Kovter-6669952-0 is a dropper written in Visual Basic. It is distributed via email, and makes use of PowerShell scripts and large objects in the registry to conceal its embedded malware. - Win.Dropper.Upatre-6669126-0
Dropper
Win.Dropper.Upatre-6669126-0 is dropped by a Word document in our ThreatGrid sandbox. The sample potentially performs a code injection circumventing Windows' DEP through memory pages allocated with PAGE_EXECUTE_READWRITE permissions. - Doc.Dropper.Valyria-6668024-0
Dropper
Doc.Dropper.Valyria-6668024-0 is a malicious Word document that drops malware. The campaign currently spreads the Emotet malware. - Doc.Dropper.Chronos-6667983-0
Dropper
This malicious Word document was discovered after it dropped an executable in our ThreatGrid sandbox. The campaign currently delivers a banking trojan, which will redirect internet traffic through the malware's proxy and try to steal banking credentials. - Win.Packed.Generic-6667111-0
Packed
This is a Visual Basic executable that will change proxy settings on the victim's machine to inspect internet traffic and thus steal information. It also tries to steal local passwords from the browser's password database.
Threats
Win.Dropper.Generickdz-6671833-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\33fd244257221b4aa4a1d9e6cacf8474
- <HKCU>\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\3517490d76624c419a828607e2a54604
- <HKCU>\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\4c8f4917d8ab2943a2b2d4227b0585bf
- <HKCU>\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\00000001
- <HKCU>\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\00000002
- <HKLM>\SOFTWARE\Wow6432Node\Mozilla\Mozilla Firefox\
- <HKLM>\SOFTWARE\Wow6432Node\Mozilla\Mozilla Thunderbird\
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: MJOXV418GJ Mutexes
- 8-3503835SZBFHHZ
- 59802CRW6VIZ62Az IP Addresses
- 141[.]8[.]225[.]75
- 43[.]230[.]143[.]219
- 198[.]46[.]86[.]224
- 122[.]14[.]210[.]142
- 52[.]5[.]251[.]20 Domain Names
- www[.]americasculturalstudies[.]net
- www[.]danhbaviet[.]com
- www[.]kegodanang[.]com
- www[.]www970234[.]com
- www[.]vhecha[.]com
- www[.]sevbizleadservices[.]com Files and or directories created
- %AppData%\59802CRW\598log.ini
- %AppData%\59802CRW\598logim.jpeg
- %AppData%\59802CRW\598logrc.ini
- %AppData%\59802CRW\598logri.ini
- %AppData%\59802CRW\598logrv.ini
- \TEMP\2995593463.exe File Hashes
- 00394f8ccd70206920aea6b84cbd14fbfbecd31b9bf7542673793a5c5a35707b
- 02acbf303617a6661d7f4e994e70508bfd22664452bf27a40af78d7d6e811a1c
- 046089a17b9742839f5b173f0bf7694e5326e7dcb1a641357cd79827e75f5c51
- 059e7346e2e8307976cd22f25c51c881d09d11cc59e68e7c7de912ad108c17af
- 0843abfc1b86ea35e3042507656e81ed7edfff6805702bc418189ac3dd5f6f81
- 098766c1ee42b13020947978225d9c48e9666c3b326c1f991daf20cde18fb3e0
- 111b5ab7085c2ab5b75a159eab016668e8c8143b036a8d702be12a69c59be2cd
- 1157af4bb297bce9c745c387cd66ac19ae4d9f7ee4b5e7a63a6af74defdd389d
- 12668eb53e18ed75aaac9e82e5ff5ecbf62dfa3034fd4870bbe33b1abe3c89f6
- 14c8abf43a6cd9337a963f408a8057a880a9c64e383d853829e7f3e4dc354d78
- 178d41ab9c193b735b37f10e3ef74df84da6cf21fc1bd6c322116d71f6afceb5
- 1a4054a1714bb64958e6823aa2418a9317d25b24b20f0666199aceb39b5c1c8f
- 1d4c1dbf89ce24cc7716c9a71a9f8564b93777d715ef484b25fa81bb368c944f
- 1f4018562d03ff36c05bb9c6691eaee8e4e9ff7965799bd8abc557b86037fe2e
- 24a76b75a5d387f434a1f4e0f4cfc2aea7176b293ceb9a9511f0aa0c64191e28
- 29918b68f79c9fb878be4e91dbb81322684b93f0ae9e5743c94de962c7df21ef
- 2a45c9616dd0518b91c14c6ace489938010886acc7a9dd9a0c3280717fc8d76b
- 2b4b76c60b34230544419025df8bde3521435d2224e6b0953f5c9417068f6902
- 2b56221522af3985b09d9ddce4c064a6b157c82698795645a6f5113a177558ff
- 2c867c08a31b7dd9e4b5c82f16c13431e8a739b983b1e065d40d2768575e7676
- 2cf0f40a3edc2df3aa1f7be9cdb7100b91b5f9c32575fd6a5e22aad9fc113546
- 2f62e170384a7960dd937d2242734fd3eddef43ebed31d57d51d69d0eb5ea376
- 315680ac90ad07c9d05301fe99f23e864b1c38cd1950caf9e7f3ca9447b16b13
- 328ba025dadc6148fb83dc34d03b519642de0122d41baabd046133efcfe69eca
- 36b321fd86f75d186e978708789000e45a2a38e436e862c0814524aff5832a8c
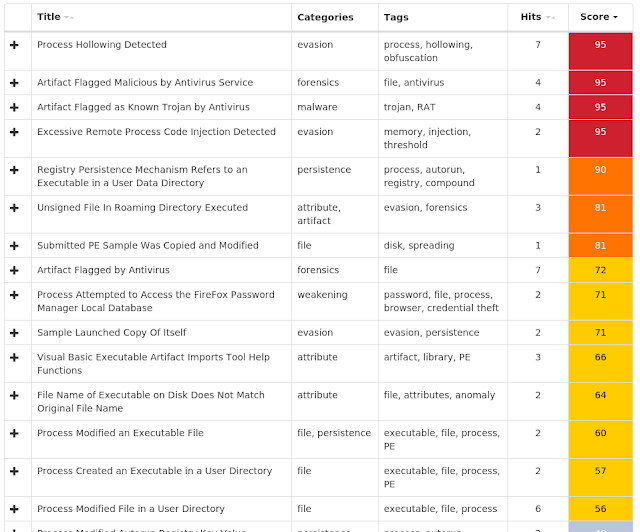
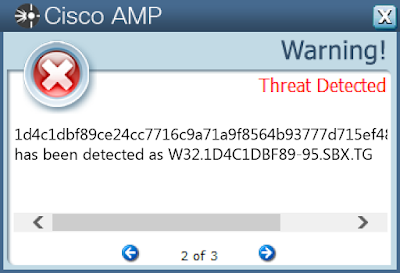
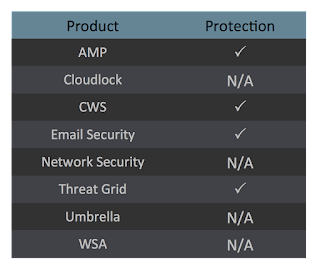
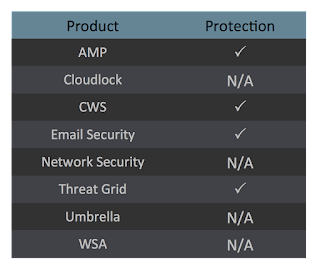
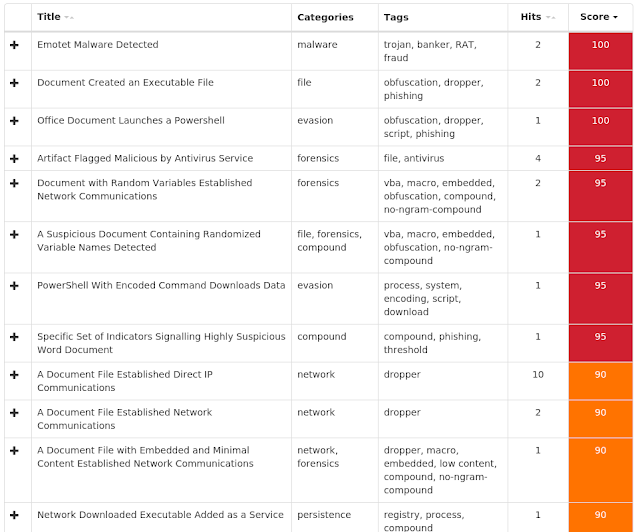
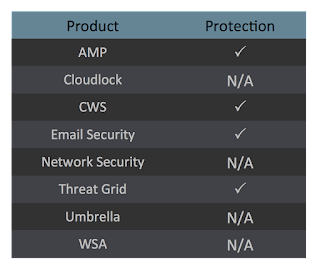
Coverage
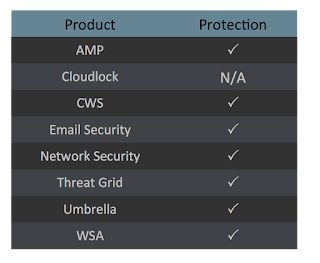
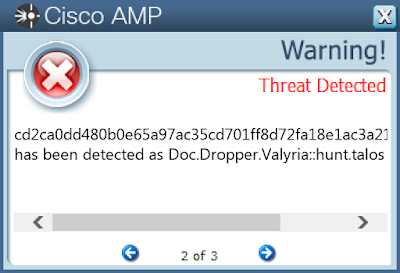
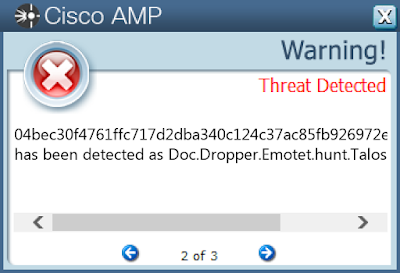
Screenshots of Detection AMP
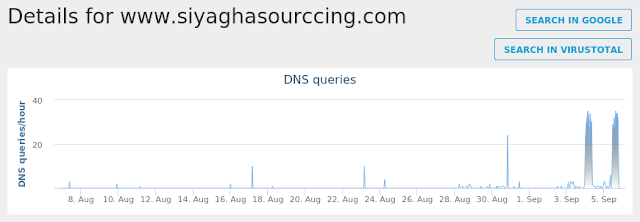
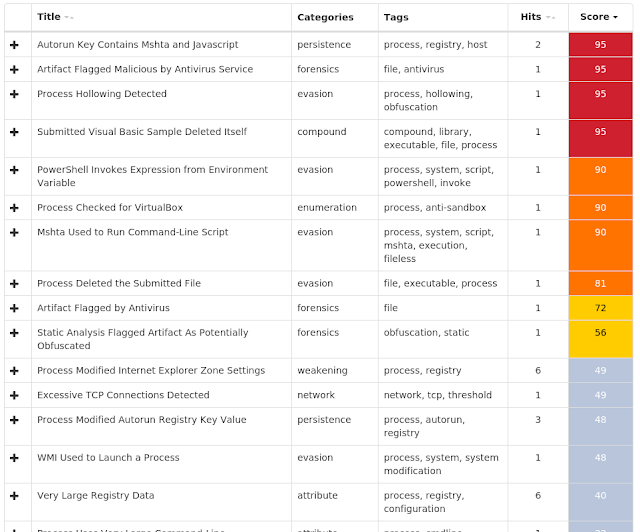
ThreatGrid
Umbrella
Win.Dropper.Kovter-6669952-0
Indicators of Compromise
Registry Keys
- <HKLM>\SOFTWARE\WOW6432NODE\3E00E5E2D21AC4F4EC6F
- Value Name: CA640AB774DC8DC9D58
- <HKLM>\SOFTWARE\WOW6432NODE\EDXF9XO
- Value Name: MWZPeJZV
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: 8567f942 Mutexes
- B3E8F6F86CDD9D8B
- EA4EC370D1E573DA
- A83BAA13F950654C IP Addresses
- 178[.]137[.]207[.]147
- 68[.]143[.]202[.]61
- 20[.]143[.]75[.]211
- 23[.]175[.]186[.]69
- 130[.]197[.]216[.]217
- 211[.]129[.]1[.]101
- 179[.]8[.]135[.]228
- 27[.]108[.]150[.]40
- 99[.]223[.]4[.]221
- 64[.]94[.]71[.]76
- 89[.]150[.]126[.]91
- 106[.]243[.]136[.]116
- 100[.]246[.]196[.]247 Domain Names
- N/A Files and or directories created
- %LocalAppData%\Temp\pygjwa3p.ah2.ps1
- %LocalAppData%\Temp\tgzjqzza.auy.psm1
- \TEMP\b9a27f6553f2b34d18b9c1dd49e5877e30a9c9a38147f376b20f2cf9913aabad.exe File Hashes
- 02ae96fd92bfc617880a78a74775b470530b8a59e4f262f9f2f203df3d37e2e5
- 05f9a381f9effeb6f4fc839190fa4c543e0f1bdcf63fafceeb5db42a987e0f85
- 06215d43b7cddf9072b2f1ff0e8d0706327869253be4517691be138f9aa29268
- 09ee56b008a1b971d845770057eb2f4e775b3706e412d827a1f3e573d78f1cb1
- 0a905d26c03a3cbd88f90f97b5e0849b3ec5b9c25c1992ac0871efd93d9772a5
- 0bf1866ee7b371ea3ffcbe049693010be5f5ab74517256e970383a3449899c52
- 0c7b21d7d7bde5649d9b0a27e5199b3619daa79541ba74d78ccece91be32fadf
- 0d078dd1069c996c028a71c2f10e899ba57530462893976221575ae8002ee87f
- 0dd870a8f9a739f4c0086222ae8c2b1b1d854915a41ddadb7da850a4238be5ea
- 0ec00e8c4277610ef9eeb5a002211b55989fa86272a020a4f1a79da996ed135f
- 0edf3f0a681bd1d63e52e37fd0f97c679c91ec081c122542eb3e62e516523ac5
- 10d2611321e6dd0c1afaa76ffe9c84590e64b99be2411364367728e5075dfdd2
- 11800040629ce430c329e00da4a3ffc58abb3127f4ea2406d5901a72523c20e8
- 11dd6cab51f57bb544e6716c280dc69168a2c6ff1581fde2dc2f8c1b1fcc5f3c
- 12a724b16c05304dcee66991b14c8ca0cc2f3378f5453a1c8dea2bd6211ca95a
- 1756ea4aa42a81db282be52f2286c746e82a9b87c8c9c10e86f921431e4709df
- 184cc70b7587abded0ed5631efbdbd86f9fb8f6095339004b589305040dc0bdf
- 18a7c88bb1278d0cab2e6d5921766bd9896005438a65cb8b5a13546504051d3f
- 1f8496e44016241a59b753bb73b542f703ad6e7ea098d2e50ec348b773248fe3
- 1fc7cb727185acd0e714ab24e36639ff5ecc00958ef62ff7287f64e388d777d3
- 22bada759f4bb6df82936b3572a79f49717dd49d584c48ce89f7b264ba187be5
- 22c56863b80073a1e6a32c508ff5ab4300af300d773e06732dd6666dfc0d7809
- 24dc47adb4ead7d8672a4acba6b6aeb80604237ab85ef40aa9cd2e9abcddfe1b
- 24f462ad25761340aceec33dc166d393e49d8f577ff479d59414f7ecfad49ba1
- 2782831911a60287dd208a98abc012276b32165c04c86ccd43909471a1d557f9
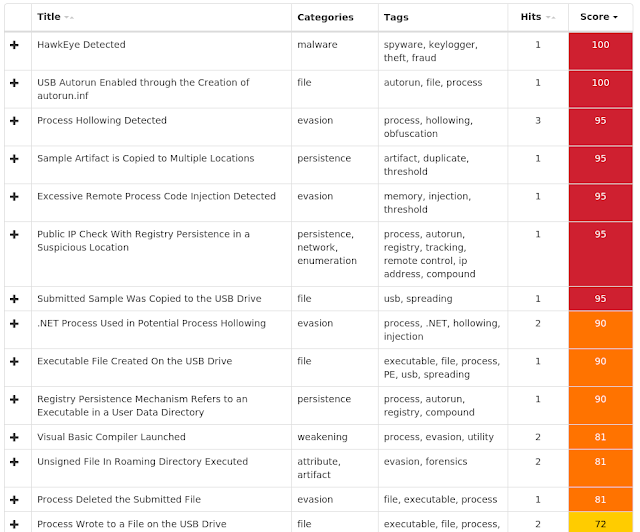
Coverage
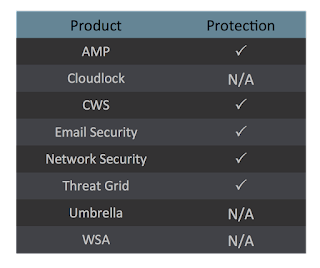
Screenshots of Detection AMP
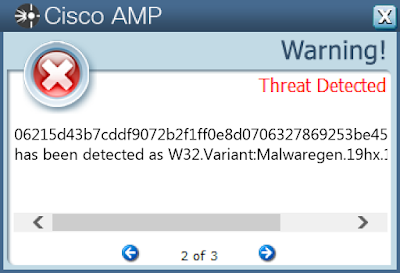
ThreatGrid
Win.Dropper.Upatre-6669126-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
- N/A Domain Names
- N/A Files and or directories created
- %LocalAppData%\Temp\vipkewek.exe File Hashes
- 00d293d627361d3618fa9e362b2ddac1fcf1a04b05a922955433a4c6954a3be7
- 034c2de6a80f13e6ad299baaf194d14747f6b29a1b31c0e4f76505430d2dcfe9
- 04e26fd503240400e6f170f9d58b2a7779d55792353420ba5a69d41d1a336917
- 0dce7497a6ecd7fdeb0507686a599143b50c94b6026fa5d4a9521b511197a811
- 105e7235d88d55a70081661f8faa327bc70a40202158b54c8042dc1ff29bd1ab
- 11c4857c3aea5fc889f39c16a934c975519b1681fcc9fd4c1d8d68fdf6b48ecb
- 18ba26eae4fd5e66b71d0d2fc666c4a5214bca27fc9af00fc9a59be3ac308618
- 1e729c31ef2c631cab9b51dc554c4639c86a627faeacf9f6fb73c50b71dea394
- 26b78a06a970f10e4cf007562c13bbe2d0f0e467681fcf5be0e1770b167dc7b2
- 273610d574c0af8b0d38eefb115c2b7794dab0c898262997f735755503881291
- 2fb5f53517290027fbb94b0c0f639aa8cbb974f726f650bda8ea09ee38a9ce54
- 3199bf691f8a15477f1a5c82e060c80a83bee44d30b6a1874bd7c6e1015e1ec3
- 4cbdcf8cd9e6b5137e1f0917bea59a4af48387ef07239d47ca68806de7f04f2c
- a3dfa314702e5e2d7c9242952b33f80ea17e458704d8e6cff49a79f45e1bc7ed
- ac711b4cc1dd6a307459fe054a1087539e498fd4990867e53c3b8ed85b223e9c
- b1ec88fd601802d028ec2f6e4501c5a7e934dd1a92ed0934a6d5505ac691fe9d
- bd0b11fc2ac479598c102436512cff35712af23384a2d7e4ae0b3c329069017d
- bd1291cb722bcbd10d2c059c672901835d1951d16e35b5091c3b5a44ea081913
- c19c02baf1bd12e1d8fb4cc31d70b34e8a5f9110ac4423677cd82fdaa019c5fc
- e6a75ac727881f772f2dd936b8125de06e3c31f3faa86ff285c5540d671faedf
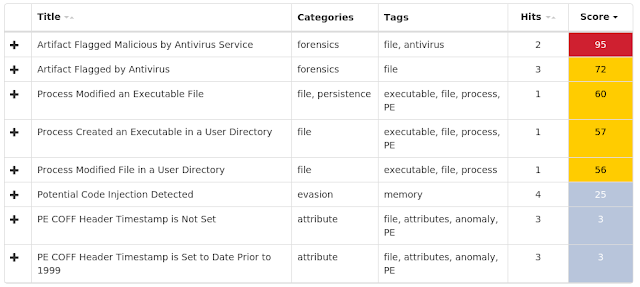
Coverage
Screenshots of Detection AMP
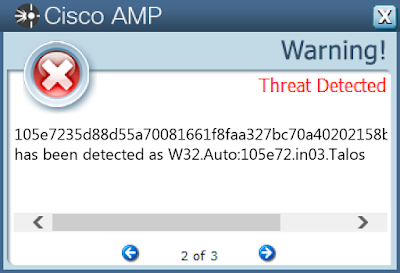
ThreatGrid
Doc.Dropper.Valyria-6668024-0
Indicators of Compromise
Registry Keys
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\WPAD\{CFFE6C1B-C698-4A68-B86B-DD768F696445}
- Value Name: WpadDecisionTime
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\WPAD\94-AF-8E-F4-CD-0F
- Value Name: WpadDecisionReason
- <HKCU>\SOFTWARE\MICROSOFT\OFFICE\14.0\WORD\RESILIENCY\STARTUPITEMS
- Value Name: ld3 Mutexes
- Global\I98B68E3C
- Global\M98B68E3C
- PEM1E4
- PEM1A0
- PEM9C8 IP Addresses
- 69[.]201[.]131[.]220
- 66[.]115[.]238[.]16
- 67[.]222[.]19[.]143
- 213[.]123[.]182[.]53
- 138[.]128[.]170[.]114
- 198[.]71[.]233[.]104
- 128[.]2[.]97[.]187
- 103[.]215[.]137[.]24
- 200[.]58[.]111[.]124
- 8[.]39[.]54[.]102
- 211[.]100[.]47[.]32
- 62[.]254[.]26[.]235
- 151[.]236[.]32[.]35 Domain Names
- blog[.]bctianfu[.]cn
- tropicalislandrealtyofflorida[.]com
- smtp[.]office365[.]com
- mail[.]vcacademy[.]lk
- mail[.]lareservasuites[.]com
- imap[.]1and1[.]co[.]uk
- mail[.]serviciodecorreo[.]es
- mail[.]1and1[.]es
- mail[.]billsmachinesvc[.]com
- mail[.]royalholidaypalace[.]com
- mail[.]goodleathergroup[.]com
- mail[.]tlb[.]sympatico[.]ca
- smtp[.]gmail[.]com Files and or directories created
- \efsrpc
- %UserProfile%\707.exe
- %WinDir%\SysWOW64\LDCjSm5OOdIv.exe
- %LocalAppData%\Temp\zzdz1frv.zq1.psm1
- %LocalAppData%\Temp\idwlwvc1.j0h.ps1
- %WinDir%\SysWOW64\nZJz1AtlwhH6.exe File Hashes
- 1027dcf0ac13ba9da3a74edd293537bb91a0aa56a6bc35037dd07d0e7c134785
- 10def6ce3d027c88fdd6d14f8d48cbcf1bea538c6c5d7bba1535b7da8538d625
- 115e66ae406dc1849e4436bd5123aa11a23140d0e5499df0db4a79bc54d9b0a2
- 19299ca446bd6e4f35f779b6645e754c447b4b3c3eff47b52ed35dc2f4b9c33a
- 204fade0f54fcc7004a5c92e267c4b10f2c7e34abe2c23d81148a1da050cd0c4
- 20b3fd1e9b961bd1ebf99ef2acaf836fd222e7e8e275ee5fe98d147007956476
- 2411c862c3a10016a8c77ca30260edd0b1578681b2c0e7efb283305d1a06a2d6
- 24e266c12f9624da9ffb2dfe7ee7ed47aeba644f269389ff65360b2ffdfa665b
- 26af093d1ec8917ad9e3bdfeb0bb6d0d03d29f936f61e3f3d5f54b3758934cff
- 2b849aca5039234ac9b5e82e02f1c4f4aef45722f76acb1a340a6077f53f5c30
- 352db4336e0b680ceede9e99aac261e4181201d1cad868215986cd54f2391efa
- 36f67278cb1b1667ca13192886f46a2a446a77a87718ba41db95c60493bb33e8
- 37832082f728da1bacdf336f3781f3fbc2678bb7231369eaffd4bc4c6444c64d
- 3b738dd4585e5b66bb122670c9e84042111999c9e20e62b0e5e52d475e5b5f5b
- 4bfb545cbbae97c960f49c26525ac7b138049f1921d007b597c0196a4d9d36ec
- 4ce483f322ebfbcb4860fa610b9b4b1970423901ae8df689cf5363fa4306a353
- 4e6b73e7da25b55ddfd245bfba2edd5a184c8b4ad7e5580ba592be66006b0264
- 4f73d7c59c7f1373e99d93cc4ba0babbe1fcc366269c427753b4a431ad97af8a
- 584f0539d4110583adacb68d2e38d05164aeeabfec95a0826c3a495dd41059c4
- 61d340302fafed7644737b27631807d326d68acec8c32462adb5be6668af3a1a
- 6a85007df58be36c0a7010cd2e153a5949af8e54575a5f3633fbd1e73ec0672c
- 6d25187f8c2b1d9dbd4ec7daa8239839acd599c263ef5a7d1892be7c755e6209
- 6d4da277bb48fa1afdeb949e7a806ed3b02dd738c824aa64b4992b5b05ecd23f
- 7282cdd99960d70cd2baa1526b15aa59a5983c0de21d6b3e65bfd9b140975175
- 745d9941a7ac2aa275e81dbcbdf4288cc6a04f9e480318ad3c43cad77131473e
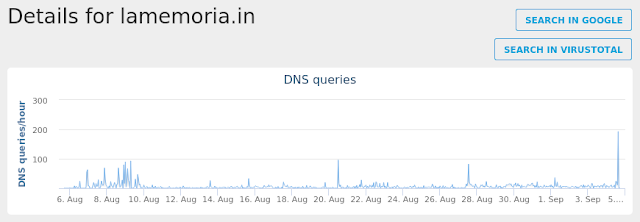
Coverage
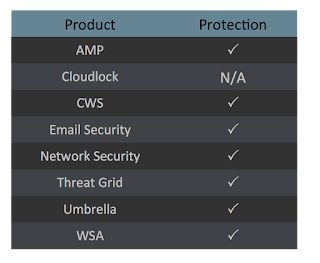
Screenshots of DetectionAMP
ThreatGrid
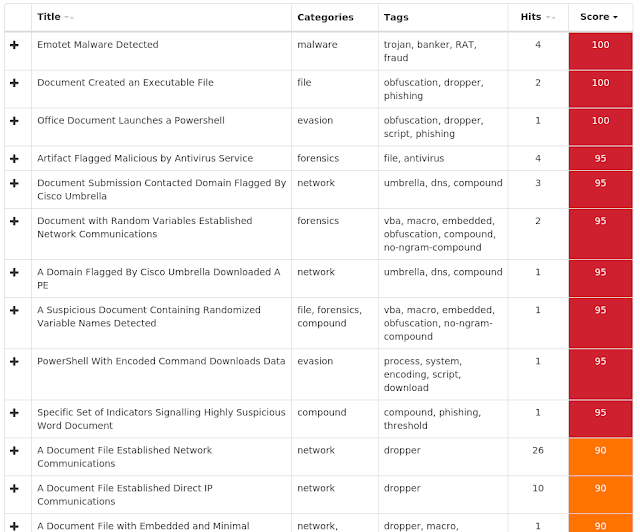
Umbrella
Doc.Dropper.Chronos-6667983-0
Indicators of Compromise
Registry Keys
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NETBT\PARAMETERS\INTERFACES\TCPIP_{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpNetbiosOptions
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NETBT\PARAMETERS\INTERFACES\TCPIP_{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpNameServerList
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpDefaultGateway
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpNameServer
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpDefaultGateway
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpSubnetMaskOpt
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\DISALLOWED\Certificates
- <HKLM>\Software\Wow6432Node\Microsoft\SystemCertificates\Root
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\TRUSTEDPEOPLE\Certificates
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\TRUSTEDPEOPLE\CRLs
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\TRUSTEDPEOPLE\CTLs
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\TRUST\Certificates
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\TRUST\CRLs
- <HKLM>\SOFTWARE\POLICIES\MICROSOFT\SYSTEMCERTIFICATES\TRUST\CTLs
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\CONNECTIONS
- Value Name: DefaultConnectionSettings
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: ProxyEnable
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: ProxyServer
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: ProxyOverride
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: AutoConfigURL
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: AutoDetect
- <HKU>\.DEFAULT\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\CONNECTIONS
- Value Name: SavedLegacySettings
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: ProxyBypass
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: IntranetName
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpInterfaceOptions Mutexes
- Global\I98B68E3C
- Global\M98B68E3C
- PEM1A4
- PEM558
- PEM948
- PEMBE4 IP Addresses
- 68[.]203[.]247[.]140
- 124[.]121[.]192[.]186
- 176[.]219[.]82[.]79
- 173[.]236[.]55[.]90
- 185[.]129[.]3[.]211
- 24[.]253[.]16[.]214
- 189[.]253[.]126[.]66 Domain Names
- withachoice[.]com Files and or directories created
- %System32%\config\SYSTEM.LOG1
- %LocalAppData%\Temp\5jhjztfi.inm.psm1
- %LocalAppData%\Temp\dgnniruc.yui.ps1
- %UserProfile%\Documents\20180906\PowerShell_transcript.PC.s2CSwKhg.20180906171831.txt
- %UserProfile%\157.exe File Hashes
- 04bec30f4761ffc717d2dba340c124c37ac85fb926972eb80c0aeb7e34a0b5e5
- 218ae537669d9dfd02ccf61ca948acef60fdf89104d3e2ef03dcececdb9babbe
- 54580f2ca416dd89565e0286ddb05c7aed1a5aceeca2766928aa6b90a63f4c34
- 6969b1dba448683c5b5cfdfe4ccdb9fac72e5e1b67f4534027202571e2b81c15
- 6bb5037a3a338bea45c96563bd6497a331a9f6efa96bbc5f6536ebc623e7ebb5
- 79765635b755992b9035560d4e00b550c3690c4a75d4e022b5998f11db4db738
- 81925e948f9d7d14fe216c3513e9085996d0f9ba1208b0f3e0a2cb69a1843b2f
- 9c089c555d580ac18b55b2874e92232c5dc86517904ae107ad79cbaf945170d7
- 9fff7343b067f08e84ff62c3c6c70d514847c19092a07b9d55c6b42025108ff0
- a0d51ee8ab2770a2587ccc1ad99286463c919a0300010a48b4278594e560f30b
- a3d5721ae44c6ee97fcffe4d40599fab488d981b6240b8e4514bd744d09990c5
- bccc98a17302f93b04fddd810bfc194b6382ed6b36fe58c3f8f401e58d36d2be
- d0bdb2938216c29798bfb752f10c72922b9d8f19f81d838d935f12912ebe23b6
Coverage
Screenshots of Detection AMP
ThreatGrid
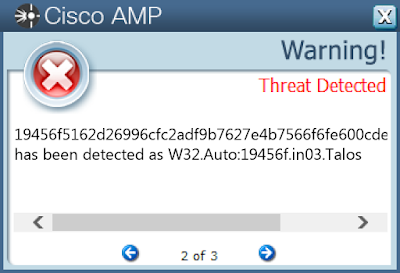
Win.Packed.Generic-6667111-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: ProxyBypass
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: IntranetName
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: IntranetName
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: UNCAsIntranet
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: AutoDetect
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: ProxyEnable
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: ProxyServer
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: ProxyOverride
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: AutoConfigURL
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS
- Value Name: AutoDetect
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\CONNECTIONS
- Value Name: SavedLegacySettings
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\CONNECTIONS
- Value Name: DefaultConnectionSettings
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: invidiadriver Mutexes
- N/A IP Addresses
- N/A Domain Names
- rapidgens[.]info Files and or directories created
- %LocalAppData%\Temp\AFUVT.bat
- %LocalAppData%\Temp\AFUVT.txt
- %AppData%\system32\intelgfx.exe
- %LocalAppData%\Temp\LFPKG.exe File Hashes
- 01856d473c35bfe514c75fcab72b65a38795ee257cbab923a9fbc6ec6048bea8
- 01cee3dae8d1578107a5229e51cf491d8ec67891f11b41b11df4bcf4f7dfa033
- 01ecd0f01d99fa67cde837666df5eb89b81876f3f272b77cd9599950f52dcda1
- 034ac9f6da8dc800ba756c56db6d412ca56ca80bf8809014eb13311e47ed3d0e
- 044e60eea0295cc8a7d899f194ec94a642e4dc9f344971a7b4e2b62bcbd52589
- 0466a2a72c2a9b573e18f9f2d6acd5a319ce3e78c8fad29e751c9fe86b0de6ae
- 047e9ee436182dd252d40aa1ba48eb4da2f03575080f054303a07c52801dd4f0
- 06283385bae75ca1771192347384d498df104f57feb89fed273a2c90d45173f1
- 06f5bbf71529e4ee25f23ccc117e1db3cb49a2ad31df2573882e2cdf2b9c5a0e
- 097da1809fcd49df77925fdb4f8eba77a5ccc888b7d3856101cdd0a2700f2aca
- 099b04e2c212aceb3851c2532fc57cb59f12cf574a7ce79d3c609e3bd4145db7
- 0a75f754c2fb13fa8f006ea3781119fe2e48d8fbe516782f658f9e39431f2466
- 0c93afa3ca6e94e7a97075e7a187e66b060f0e6b520fb3398b69dbd83d14ed7e
- 0d4d97ddf1d86e17df6203f777f994f162a55aea1eeb3908df1e29b697324c62
- 0d615bec997e4e9f02a698cd3faf0985f24aa28ecead3e5ee1a8e2602e2f9a9d
- 0fb822636382d6c306ee21efa4b1a4f0a8e0d4b5e22b704934cef706fcd24de4
- 1045a01bc6e0bf8bab6c0b51d5ceb8840485a02b698ab3b691466e0e646863ac
- 11481494804da9f301b47ec5a4caa3e6479e9cf901b54633d4114c7d7706e254
- 11cb98ac7c0b4b3dce3831ab511c09f8d8d958ef41396b2ef93121b28ac4aa6f
- 12b84d0786d49c283d7a3dc3c985af8ff371b133b6b8301cab3c2bf839f2ce42
- 16c0224bbe0e0bb43002fb7f83f8c6eaba16b0873d3455a570f58cc89fa0d762
- 1822abcaf9005035798b30c09ff722fe2815f298615c5c59f1fb6cb278301161
- 19456f5162d26996cfc2adf9b7627e4b7566f6fe600cde3764c71523f2dc795a
- 1a0a601961f2c46525ebdc772126c0fb4f7802b533033f15a5e6217c5f266aca
- 1b7d7642e95d7d9152b4d8e8c59d7e1d7000996999c62f45d9a51c50d00f1833
Coverage
Screenshots of Detection AMP
ThreatGrid