Today, as we do every week, Talos is giving you a glimpse into the most prevalent threats we’ve observed this week — covering the dates between Sept. 28 and Oct. 5. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, we will summarize the threats we’ve observed by highlighting key behavioral characteristics and indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this roundup are:
- Win.Malware.Gandcrab-6706045-0
Malware
Gandcrab is ransomware that encrypts documents, photos, databases and other important files using the file extension ".GDCB", ".CRAB" or ".KRAB". Gandcrab is spread through both traditional spam campaigns, as well as multiple exploit kits, including Rig and Grandsoft. - Xls.Downloader.Valyria-6704496-0
Downloader
These variants of Valyria are malicious Excel files that contain embedded VBA macros used to distribute other malware. - Win.Dropper.Fqdq-6705253-0
Dropper
This dropper attempts to access the Firefox Password Manager local database, uses a temporary batch file to perform additional malicious activities and uploads files to remote servers. Additionally, it might inject code, read INI files or use Visual Basic scripts. - Win.Malware.Genkryptik-6704925-0
Malware
Win.Malware.Genkryptik is oftentimes a generic detection name for a Windows trojan. Some of the malicious activities that could be performed by these samples, without the user's knowledge, include: collecting system information, downloading and uploading files and dropping additional samples. - Win.Malware.Zusy-6704537-0
Malware
Zusy is a trojan that uses man-in-the-middle attacks to steal banking information. When executed, it injects itself into legitimate Windows processes such as "explorer.exe" and "winver.exe". The malware attempts to trick the user into entering their login information whenever they visit a financial services website. - Win.Malware.Razy-6703914-0
Malware
Razy is oftentimes a generic detection name for a Windows trojan. They collect sensitive information from the infected host and encrypt the data, and send it to a command and control (C2) server. Information collected might include screenshots. The samples modify auto-execute functionality by setting/creating a value in the registry for persistence. - Doc.Malware.Emooodldr-6699885-0
Malware
These malicious Word documents contain embedded VBA macros, spawn new processes, drops files and remove Office resiliency keys.
Threats
Win.Malware.Gandcrab-6706045-0
Indicators of Compromise
Registry Keys
- <HKCR>\LOCAL SETTINGS\MUICACHE\3E\52C64B7E
- Value Name: LanguageList
- <HKCU>\CONTROL PANEL\DESKTOP
- Value Name: Wallpaper Mutexes
- Global\8B5BAAB9E36E4507C5F5.lock
- Global\XlAKFoxSKGOfSGOoSFOOFNOLPE IP Addresses contacted by malware. Does not indicate maliciousness.
- 50[.]63[.]202[.]89
- 93[.]125[.]99[.]121
- 137[.]74[.]238[.]33
- 94[.]231[.]109[.]239
- 185[.]135[.]88[.]105
- 146[.]66[.]72[.]87
- 87[.]236[.]16[.]31
- 217[.]160[.]0[.]234
- 69[.]73[.]180[.]151
- 104[.]31[.]77[.]95
- 171[.]244[.]34[.]167
- 217[.]174[.]149[.]130
- 70[.]40[.]197[.]96
- 223[.]26[.]62[.]72
- 80[.]77[.]123[.]23
- 178[.]238[.]37[.]162
- 51[.]68[.]50[.]168
- 104[.]28[.]30[.]160
- 67[.]227[.]236[.]96
- 66[.]96[.]147[.]67
- 179[.]188[.]11[.]34
- 89[.]252[.]187[.]72
- 194[.]58[.]56[.]95
- 104[.]28[.]28[.]142
- 104[.]27[.]163[.]241
- 213[.]186[.]33[.]186
- 107[.]178[.]113[.]162
- 87[.]236[.]16[.]29
- 188[.]165[.]53[.]185
- 173[.]247[.]242[.]133
- 77[.]104[.]144[.]25
- 191[.]252[.]51[.]37
- 202[.]43[.]45[.]181
- 192[.]163[.]234[.]40
- 217[.]160[.]0[.]27
- 209[.]182[.]208[.]245
- 94[.]73[.]148[.]18
- 45[.]33[.]91[.]79
- 87[.]236[.]19[.]135
- 52[.]29[.]192[.]136
- 178[.]33[.]233[.]202
- 92[.]53[.]96[.]201
- 186[.]202[.]153[.]158
- 104[.]24[.]104[.]13
- 213[.]186[.]33[.]3
- 188[.]64[.]184[.]90
- 95[.]213[.]173[.]173
- 103[.]107[.]17[.]102
- 103[.]27[.]238[.]31
- 50[.]87[.]58[.]165
- 104[.]27[.]186[.]113
- 104[.]24[.]102[.]153
- 77[.]104[.]171[.]238
- 194[.]154[.]192[.]67
- 87[.]236[.]16[.]41 Domain Names contacted by malware. Does not indicate maliciousness.
- www[.]litespeedtech[.]com
- big-game-fishing-croatia[.]hr
- www[.]lagouttedelixir[.]com
- dreamhost[.]com
- www[.]himmerlandgolf[.]dk
- hanaglobalholding[.]com
- top-22[.]ru
- zaeba[.]co[.]uk
- ispsystem[.]com
- unnatimotors[.]in
- www[.]macartegrise[.]eu
- blokefeed[.]club
- bellytobabyphotographyseattle[.]com
- diadelorgasmo[.]cl
- www[.]bgfc[.]hr
- www[.]wash-wear[.]com
- yourmine[.]ru
- www[.]reg[.]ru
- www[.]poketeg[.]com
- boatshowradio[.]com
- www[.]perfectfunnelblueprint[.]com
- perovaphoto[.]ru
- www[.]cakav[.]hu
- www[.]billerimpex[.]com
- evotech[.]lu
- www[.]ismcrossconnect[.]com
- help[.]dreamhost[.]com
- www[.]fabbfoundation[.]gm
- alem[.]be
- cevent[.]net
- mauricionacif[.]com
- smbardoli[.]org
- www[.]aco[.]dk
- cyclevegas[.]com
- lucides[.]co[.]uk
- krasnaypolyana123[.]ru
- hoteltravel2018[.]com
- oceanlinen[.]com
- 6chen[.]cn
- koloritplus[.]ru
- asl-company[.]ru
- www[.]krishnagrp[.]com
- test[.]theveeview[.]com
- cdnjs[.]cloudflare[.]com
- picusglancus[.]pl
- bloghalm[.]eu
- api[.]w[.]org
- nesten[.]dk
- simetribilisim[.]com
- pp-panda74[.]ru
- wpakademi[.]com
- dna-cp[.]com
- h5s[.]vn
- bethel[.]com[.]ve
- vjccons[.]com[.]vn
- www[.]rment[.]in
- marketisleri[.]com
- www[.]byggekvalitet[.]dk
- royal[.]by
- gmpg[.]org
- sherouk[.]com
- tommarmores[.]com[.]br
- graftedinn[.]us
- www[.]mimid[.]cz
- maxcdn[.]bootstrapcdn[.]com
- panel[.]dreamhost[.]com
- relectrica[.]com[.]mx
- acbt[.]fr
- damt7w3yoa0t2[.]cloudfront[.]net
- topstockexpert[.]su
- goodapd[.]website
- www[.]n2plus[.]co[.]th
- aurumwedding[.]ru
- devdev[.]com[.]br
- www[.]toflyaviacao[.]com[.]br
- mimid[.]cz
- nhs-foi[.]com
- www[.]iyfipgun[.]com
- wash-wear[.]com Files and or directories created
- %AppData%\Microsoft\Internet Explorer\UserData\MA3SBLRS\spid[1].xml
- %UserProfile%\Videos\98b689db98b68e303c.lock
- %UserProfile%\Start Menu\98b689db98b68e303c.lock
- %UserProfile%\Start Menu\SGMNP-DECRYPT.txt
- %UserProfile%\Videos\Sample Videos\98b689db98b68e303c.lock
- %UserProfile%\Videos\Sample Videos\SGMNP-DECRYPT.txt
- \??\E:\$RECYCLE.BIN\S-1-5-21-2580483871-590521980-3826313501-500\98b689db98b68e303c.lock
- \??\E:\$RECYCLE.BIN\S-1-5-21-2580483871-590521980-3826313501-500\SGMNP-DECRYPT.txt
- \??\E:\$RECYCLE.BIN\SGMNP-DECRYPT.txt
- \??\E:\98b689db98b68e303c.lock
- \??\E:\SGMNP-DECRYPT.txt
- \MSOCache\SGMNP-DECRYPT.txt
- \PerfLogs\Admin\SGMNP-DECRYPT.txt
- \PerfLogs\SGMNP-DECRYPT.txt
- \Recovery\926583e2-ef64-11e4-beed-d6738078ad98\SGMNP-DECRYPT.txt
- \Recovery\SGMNP-DECRYPT.txt
- \SGMNP-DECRYPT.txt
- \TEMP\SGMNP-DECRYPT.txt
- %UserProfile%\Videos\SGMNP-DECRYPT.txt File Hashes
- 211484d0deda5cb97b16b27538b7d1d2c26af6ae3aac3c888085a0e8ddf2d8bd
- 46b702851cb5c1df0a97d1ae9e3202316d36ef2195395a9bcc3699dd1d247733
- 4e2ba4638d01c1473f0959fae6d31636456cde0ab995fa5f3fad1efc2cb7bf0e
- 69fd1808c32fe3209f384fba8f79df13bec479e9b081f7edcf8720f6257f7dfe
- 8b5c1735800d8ad69b535a863f4ae1941604b3e57261961e230a26b16b4b98ec
- 9ec54c9d6ec39c34c8e011fcb10fb2ae5334d1d0632e63a61d94b36b9f9c8a9b
- c394e7fa3604f5ee26419a913dbfeb0988d59bbf8ed25d852ebf62a48cc1688a
- c4a126172b27777413ee4efcd0ce8656fbef52e81c984993af3fa63d5264cc8e
- d81aa5dbd9272f9be6e4a0def514a9284220d88f219ac6fd908ab2c942b92cdc
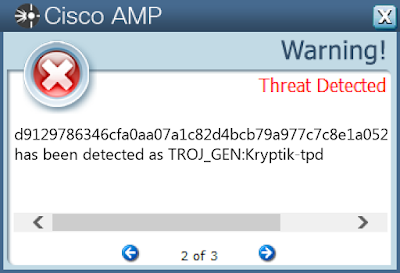
- d9129786346cfa0aa07a1c82d4bcb79a977c7c8e1a052916a34b6cde4c09c006
- e41697a99da83a32bf8a56f993123fbfaef378d5e6f61286a272536fe10b6d35
- e50a28068fcae51a609946fad1637a5dbfbda8add88063ddb117cb8e0cfc4a74
- e8502aa65a4da371c0e378b245374af7340b809140a5d2e3bc3bfa67a92a2bde
- eb9347f0fbbb675ecc61beb1f2be8721871e203357b124ad9858037a641709f5
- f77825b0388a6220521219030ad70bdb6fcd3216a590d092ec4aa22a506a17b6
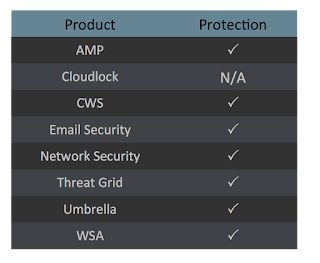
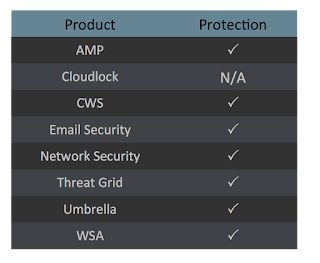
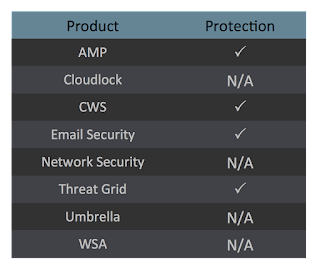
Coverage
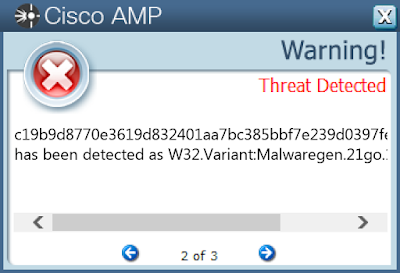
Screenshots of Detection AMP
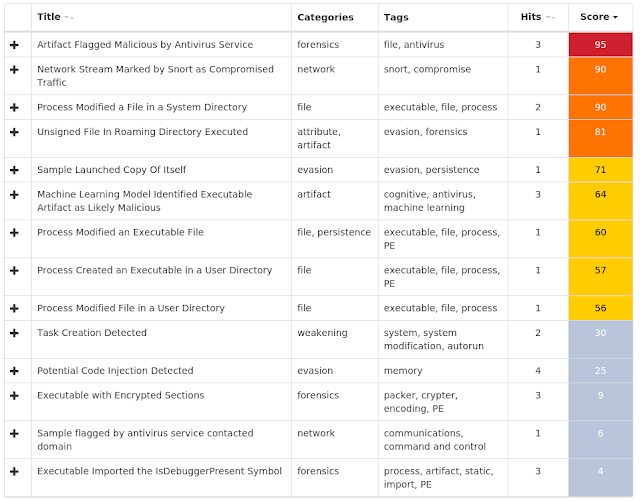
ThreatGrid
Umbrella
Xls.Downloader.Valyria-6704496-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: UNCAsIntranet
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value Name: AutoDetect
- <HKCU>\SOFTWARE\MICROSOFT\WISP\MULTITOUCH
- Value Name: MultiTouchEnabled
- <HKCU>\SOFTWARE\MICROSOFT\WISP\PEN\PERSIST\0\1
- Value Name: HidCursorName
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\WINDEFEND
- Value Name: DeleteFlag
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\WINDEFEND
- Value Name: Start Mutexes
- Local\10MU_ACB10_S-1-5-5-0-57527
- Local\10MU_ACBPIDS_S-1-5-5-0-57527
- Global\316D1C7871E00
- {773F1B9A-35B9-4E95-83A0-A210F2DE3B37}-Default IP Addresses contacted by malware. Does not indicate maliciousness.
- 78[.]47[.]139[.]102
- 107[.]180[.]25[.]0
- 103[.]110[.]91[.]118
- 89[.]163[.]224[.]250
- 199[.]249[.]223[.]62
- 185[.]220[.]101[.]12
- 89[.]27[.]96[.]42
- 208[.]113[.]131[.]196 Domain Names contacted by malware. Does not indicate maliciousness.
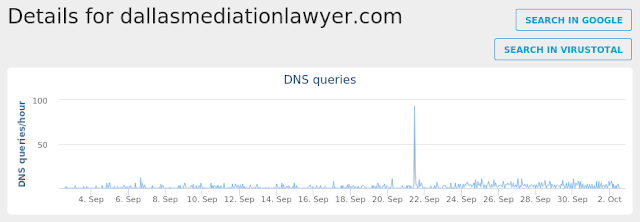
- dallasmediationlawyer[.]com
- myexternalip[.]com Files and or directories created
- %LocalAppData%\Temp\character.exe
- %AppData%\mssert\chasactes.exe
- %LocalAppData%\Temp\const_cast.bat
- %LocalAppData%\Temp\whzxixx5.jdj.ps1
- %LocalAppData%\Temp\xgxfy2dc.eju.psm1
- %LocalAppData%\Temp\21iyllij.ncz.psm1
- %LocalAppData%\Temp\erifm5li.lo3.ps1
- %LocalAppData%\Temp\wmez5d0g.r0g.ps1
- %LocalAppData%\Temp\gs0jrz4i.yd2.psm1
- %LocalAppData%\Temp\qgh0kqvv.ce5.ps1
- %LocalAppData%\Temp\tkzdlipn.odo.psm1 File Hashes
- 0276895b76757b5b2726c1c2fbb50d98040dc2dc46aedff1e5b9709f168b4a8d
- 0f792637a859a3c2919e1e45a9500e1bdf2b5f4e07bfc4d8b5e24cf7c8003e5e
- 1114fd2ee387df04c4e7ed0bb6d088b220e893c8a1ee07386977c7369681e5d3
- 1c2f39f6a608c70b16a79ed4cfb228c412852caac8a8b8bafc4e0819d038aa2c
- 2ca6d57dcfacd0f59f8b390ccbf138b557b8e95a157a53de6fe864c5eafbcf80
- 4682a95f9ed32657ee61b7aec758ab6bbdc17a52e2812e1372b3b2a9776cadc1
- 655f60c338658334723310c79033b26daa207b61fd89ebaf4abbed93802c65be
- 672aac7a017a8417608dfe687fa4023fdd1e90a7d77f6e1d9b035a070c9d9c40
- 6ff12e83f44e19de6515c03108fccfd98abd3a70bbab1088171954a3c6113d3b
- a407d2cfb849a1822895fb5770db7c24b707422da3a193e7d8f5d9e39bfb3896
- ccbac43307cd046f896283deac0341351b5dc83e6be5cb2292a0c28cdfd34650
- dafd70b7b82551b0feb905f8d466d2b02784ce6e5d5c2b8d6d00e82b27487ae0
- dbf3533e970aacc291d0342289943605537407df18217182ca39d52a8c9f8970
Coverage
Screenshots of Detection AMP
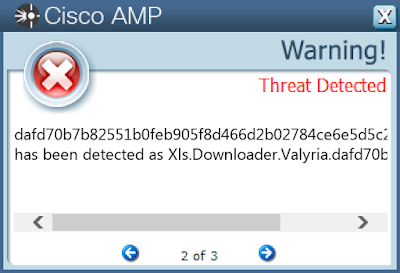
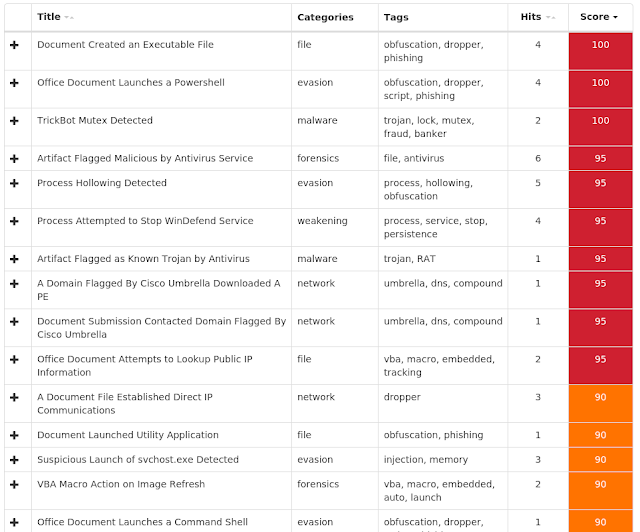
ThreatGrid
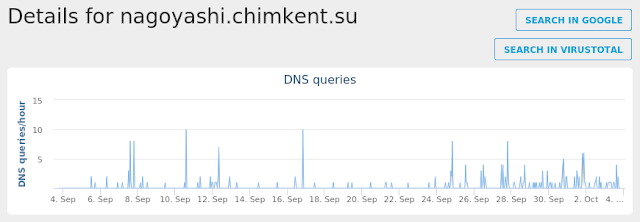
Umbrella
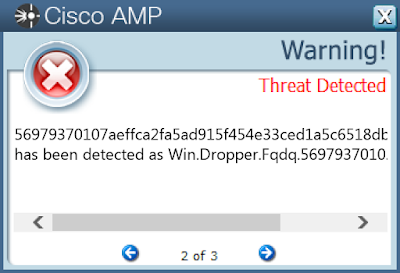
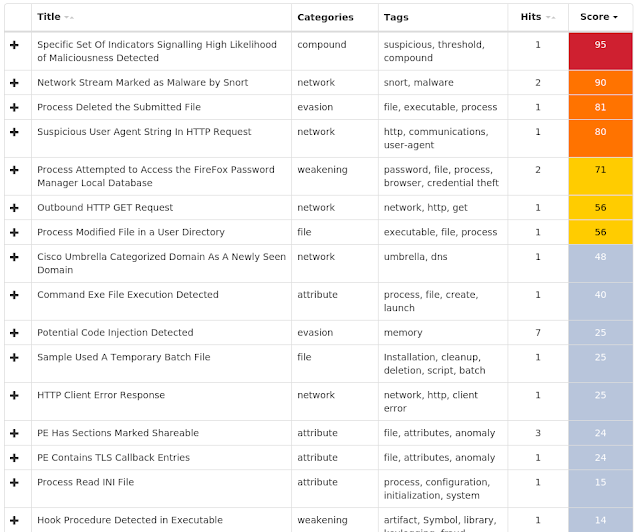
Win.Dropper.Fqdq-6705253-0
Indicators of Compromise
Registry Keys
- <HKCR>\LOCAL SETTINGS\MUICACHE\3E\52C64B7E
- Value Name: LanguageList
- <HKLM>\SYSTEM\CONTROLSET001\CONTROL\NETWORK\{4D36E972-E325-11CE-BFC1-08002BE10318}\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}\CONNECTION
- Value Name: PnpInstanceID Mutexes
- 3749282D282E1E80C56CAE5A IP Addresses contacted by malware. Does not indicate maliciousness.
- N/A Domain Names contacted by malware. Does not indicate maliciousness.
- baxishop[.]ro Files and or directories created
- %AppData%\D282E1\1E80C5.lck
- %AllUsersProfile%\Microsoft\Vault\AC658CB4-9126-49BD-B877-31EEDAB3F204\Policy.vpol
- \PC*\MAILSLOT\NET\NETLOGON
- \lsass
- %AppData%\D282E1
- \samr File Hashes
- 030290f026a913226735bc017a37997180f130b9ce1fdc3b990e050aea4bc39e
- 07abd686b7cda16b61c65d82cb72f464e2ea31bb8bb165f01bbcfa693f1bd22a
- 1258790e008879340d7cd8e6b303e25183345a05d81b6583164f0a690323405b
- 12963b31f9719d9333f6cbdb46426c32179bba4a31976b094d192588eb4439ff
- 2627bd09fd4886f83a7ca589518523606b581ad026968f3d013e1cfb221f7811
- 2c18a46ea35314f065b21e151d37787cfa5b7696207226ca80f7732176659ee9
- 30a901d40309ac1e42e98ad59044e1e1f97f985ca397628e8f0deb8f67f39d1f
- 31ef4c98208464b43dd337b92cba0cfa05d0924ebc732e0b1ee88120495f503c
- 34f159a5b3ee64cbe520c18e9abd66be61b583dad385bbec9cadf054942827da
- 35c1410cfb084bb4f4ef5a7c3d92c7b78ddd33849864e41f22e09f5b1c3997b2
- 3a69eddc3ab09e947703dbfd7e279e9e6e867190c9f72f395833fe94a1b6903a
- 4688f04b2498695705ea718ba724e9f0c04d92d09d75505f7fa1b1ad19bfe795
- 4e79a2473921ee6132c3e73f9b4de0395ec350cb476981cf2cb19171034f9405
- 56979370107aeffca2fa5ad915f454e33ced1a5c6518dbc01ed15689b92e83dd
- 582f2175b65814e7558fca9ebc7e1a6f97402ce3079f43ece47fdc17c3f7324e
- 5f83ff3b7d094547fd00dacabe669e389bdd04af09dcbc7790f29a63f797a00f
- 6448bc9787a96f76cc6716294a204df6d1cbd6db9cc441abc78b31161529e00f
- 7a2868174590c11d2f95794260792700a1fd567b5315702decfd1cd6611ed0d5
- 8b7a4bc0f2ea0f3e54b0cea9fa2928ddd0a85aa80a64071985cf95301c0d5ac3
- 9030a6efd1e15d5e78b727700863ab45b667a7c532761b3a148aa222f7e17b87
- 946de8d2685ded47c74e4b7c9490e8961598462a87be7ca5bef22693745f7cfa
- 951860ee7f7283a3b238cbfdb6e161c09fcb6a2b7975bb142412c442fd2590fd
- 95b99dd7dd7814724287c89e2435aa65cc82e91c5aabd453be1a0532d50bd936
- 96397b26ba4ee4244704c2cadd71c3d3d4c12e988f6de1d695f3602432bd94b3
- 9c5acd9297928707ed7e472e9316b125b55b2cd98870aaa4b4630dcd0fece734
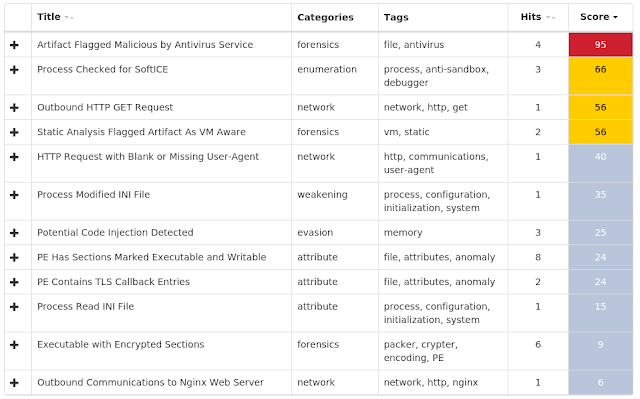
Coverage
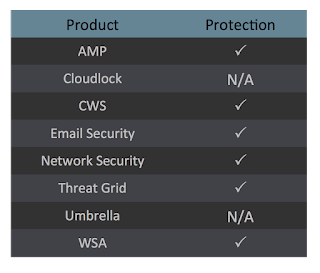
Screenshots of Detection AMP
ThreatGrid
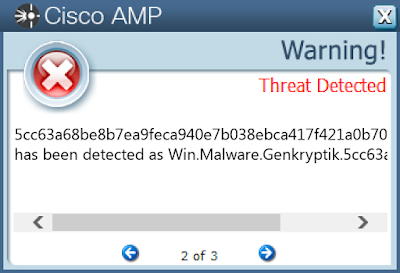
Win.Malware.Genkryptik-6704925-0
Indicators of Compromise
Registry Keys
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS
- Value Name: DhcpNameServer
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value Name: DhcpNameServer Mutexes
- !IECompat!Mutex
- !PrivacIE!SharedMem!Mutex
- Local\VERMGMTBlockListFileMutex
- Local\!BrowserEmulation!SharedMemory!Mutex
- Local\URLBLOCK_DOWNLOAD_MUTEX
- Local\URLBLOCK_HASHFILESWITCH_MUTEX
- {5312EE61-79E3-4A24-BFE1-132B85B23C3A}
- {66D0969A-1E86-44CF-B4EC-3806DDDA3B5D}
- IsoScope_1e0_ConnHashTable<480>_HashTable_Mutex
- IsoScope_1e0_IESQMMUTEX_0_303
- IsoScope_1e0_IESQMMUTEX_0_331
- IsoScope_1e0_IESQMMUTEX_0_274
- Local\URLBLOCK_FILEMAPSWITCH_MUTEX_480
- IsoScope_708_ConnHashTable<1800>_HashTable_Mutex
- IsoScope_708_IESQMMUTEX_0_303
- IsoScope_708_IESQMMUTEX_0_331
- Local\URLBLOCK_FILEMAPSWITCH_MUTEX_1800
- IsoScope_708_IESQMMUTEX_0_274
- IsoScope_4b4_IESQMMUTEX_0_274
- IsoScope_f8_IESQMMUTEX_0_274
- IsoScope_20c_ConnHashTable<524>_HashTable_Mutex
- IsoScope_20c_IESQMMUTEX_0_303
- IsoScope_20c_IESQMMUTEX_0_331
- IsoScope_4b4_ConnHashTable<1204>_HashTable_Mutex
- IsoScope_4b4_IESQMMUTEX_0_303
- IsoScope_4b4_IESQMMUTEX_0_331
- IsoScope_20c_IESQMMUTEX_0_274
- Local\URLBLOCK_FILEMAPSWITCH_MUTEX_524
- IsoScope_f8_ConnHashTable<248>_HashTable_Mutex
- IsoScope_f8_IESQMMUTEX_0_303
- IsoScope_f8_IESQMMUTEX_0_331
- Local\URLBLOCK_FILEMAPSWITCH_MUTEX_248
- IsoScope_6e4_IESQMMUTEX_0_274
- IsoScope_6e4_ConnHashTable<1764>_HashTable_Mutex
- IsoScope_6e4_IESQMMUTEX_0_303
- IsoScope_6e4_IESQMMUTEX_0_331
- Local\URLBLOCK_FILEMAPSWITCH_MUTEX_1764
- IsoScope_4e8_IESQMMUTEX_0_274
- IsoScope_4e8_ConnHashTable<1256>_HashTable_Mutex
- IsoScope_4e8_IESQMMUTEX_0_303
- IsoScope_4e8_IESQMMUTEX_0_331
- Local\URLBLOCK_FILEMAPSWITCH_MUTEX_1256 IP Addresses contacted by malware. Does not indicate maliciousness
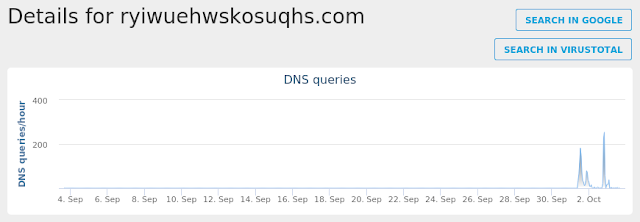
- 13[.]107[.]21[.]200 Domain Names contacted by malware. Does not indicate maliciousness
- ryiwuehwskosuqhs[.]com
- goldenmemb[.]website
- dolikulooospo[.]fun Files and or directories created
- %LocalAppData%Low\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico
- %LocalAppData%\Microsoft\Windows\WebCache\V01tmp.log
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\dnserror[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\httpErrorPagesScripts[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\6YL4T24G\errorPageStrings[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\6YL4T24G\httpErrorPagesScripts[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\7V3XNPL2\NewErrorPageTemplate[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\7V3XNPL2\errorPageStrings[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\NewErrorPageTemplate[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\dnserror[1]
- %LocalAppData%\Microsoft\Windows\WebCache\V010000F.log
- %LocalAppData%\Temp\~DF4B1ABF6D6A9DC6E3.TMP
- %LocalAppData%\Temp\~DF88BBAB8557CDD7E3.TMP
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\errorPageStrings[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\suggestions[2].en-US
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\6YL4T24G\NewErrorPageTemplate[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\7V3XNPL2\dnserror[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\7V3XNPL2\favicon[2].ico
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\favicon[1].png
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\favicon[2].png
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\6YL4T24G\views[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\7V3XNPL2\favicon[1].ico
- %LocalAppData%\Temp\~DFDEB0FC636A1346E9.TMP
- %LocalAppData%\Temp\~DFEBFBFB87C6F7EC1B.TMP
- %LocalAppData%\Temp\~DFFC172A87F8554CB4.TMP
- %LocalAppData%\Temp\~DF81A97BC70E347BD0.TMP
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\httpErrorPagesScripts[1]
- %LocalAppData%\Temp\~DF8AA772D245BBB59D.TMP
- %LocalAppData%\Temp\~DF90B11BDCE6092786.TMP
- %LocalAppData%\Temp\~DF9FFAF3D7E7318657.TMP
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\1NSKV6K6\NewErrorPageTemplate[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\7V3XNPL2\httpErrorPagesScripts[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\NewErrorPageTemplate[2]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\dnserror[2]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\errorPageStrings[1]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\errorPageStrings[2]
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\httpErrorPagesScripts[2]
- %LocalAppData%\Temp\~DF5DDD3B43947F7CEA.TMP
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\6YL4T24G\dnserror[1]
- %LocalAppData%\Temp\~DFB15BBE1A2AFF7D7E.TMP
- %LocalAppData%\Temp\~DF1D30A03829232972.TMP
- %LocalAppData%\Temp\~DF38E2C66D6383AD19.TMP
- %LocalAppData%\Temp\~DFCE77235CFE7E5202.TMP File Hashes
- 060707050140235807d6e6ac6933fa26cf0c230d68f574b880e99a699bdf506a
- 088a6e8da14dbeab941702b1515b85486544dffc83885112b95997257f8d32d5
- 0dfc771e0fbdf05facc54643341dfce97b745efe13867b01049bc977624d14b2
- 0e21eb1c5f15689329bc6d46d78eb7d0f4eccc6fb8da4f41d17e6205ae7a847b
- 0f71ba5f0fbba5d9810a4f816c5ebe1d545c4c65b34c180c769c2cd3467b0737
- 130649d3f09197d1c2e895cc06fd9ecd6feb2e663562a6b99d95ae4ce66eddb8
- 139ac3f5d2e5351c0edcd0edb384d0a75e482e8007724f181c7a4204f5895ad9
- 13c3313b910f18431ea183b00632deacd266561a73bcf837f4b46f1f73b31bcd
- 24b6c693551ed33b55d7ce6baae96dcca9e3cb55e9b94637d5ba59edc109d402
- 27cec90ae8c84a79dd2ebb2928152bdea1b07cab3b2f1ad98ed8fb3f17cc339b
- 28b54e5cf1be89766c177bc7f4c8692abec0bb4bdf299a59709d10120f7bc205
- 29b845365404070e98840dcd74eb3c23919b0990b14bd0905b0921220f8b4bb9
- 2c3fad4307c0739c336e50ec670b61d00029d2a2be260676419f883835ce8818
- 337ad107eb3e1fc497af4b3f6006e12ae74a55d6535f28a67c9b231807e15f24
- 3394d5ec6ba4c548289008cbfea8238318af52d51e8e2110b5060635425db74c
- 378a4e27208c7fee9c7ac33d11d8872db902fe5242aceabba11343bf11a95155
- 3a136b2b6df645c3e6b3c0febb821a5dda5bcb4bd35f674fb33aa10684b58004
- 3c4e171d1f0b29b6f40f8bdf6af0c1161b092591c453c66734f4c6f54a0ac36f
- 3ec415b8f411c2004892c7dedcd25e4683d0f0fded754c8b9a0f784f087dddcf
- 420c05993a014331992918e89dda914851c0e31a2e196446309e3da07dc0c31a
- 43d9e51c98400b09bc499f0e2857e2b797254167c29c9d2234f6506d7cf7f98e
- 4ae9179659e2ba267b87478ea0f48c6c1caba252b4d2bcdfdc4b6ba873028d87
- 542b5b23123a0a71d79181adeda4edfff6b91cdaf0068aafc55ee03bdc928ab5
- 5bbc6d14ed5d408d0c7bb115853dff092c236517223c14b92c709a7ffa2c5742
- 5cc63a68be8b7ea9feca940e7b038ebca417f421a0b70c17d3e6ebfca4212e16
Coverage
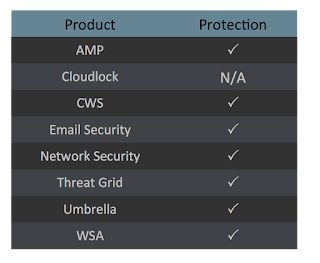
Screenshots of DetectionAMP
ThreatGrid
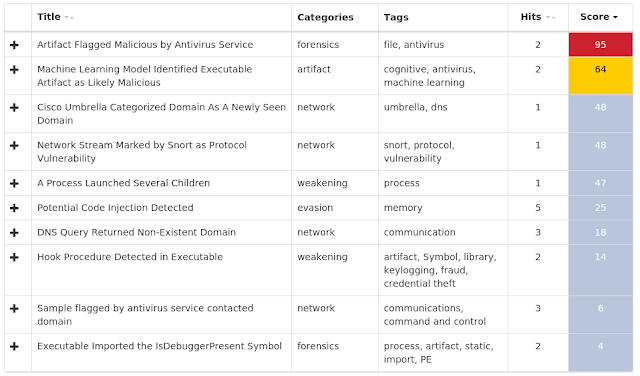
Umbrella
Win.Malware.Zusy-6704537-0
Indicators of Compromise
Registry Keys
- <HKCR>\LOCAL SETTINGS\MUICACHE\3E\52C64B7E
- Value Name: LanguageList
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters
- <HKLM>\SYSTEM\CONTROLSET001\CONTROL\NETWORK\{4D36E972-E325-11CE-BFC1-08002BE10318}\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}\CONNECTION
- Value Name: PnpInstanceID
- <HKCU>\Software\Microsoft\RAS AutoDial Mutexes
- DBWinMutex
- NtHack IP Addresses contacted by malware. Does not indicate maliciousness
- 139[.]196[.]204[.]190 Domain Names contacted by malware. Does not indicate maliciousness
- www[.]bilibili[.]com
- wpa[.]qq[.]com
- bbs[.]nt47[.]com
- www[.]nt47[.]com Files and or directories created
- N/A File Hashes
- 00b657fa1270930f868fcd06c38af4b1514baa727c0db576e50340cc2f1c49dc
- 0f6f850198e9afb8ddfe5552dad5ae6151c3cdf41f5ed8964a1e46ce62ea0d2b
- 1bf8402a3da8797a130c528ff38fcca42403a5e878943d8dbaec420433c55edf
- 2c0996f013b00833a28d1612acc545a66264b613e7127738ccf3536ddb04501c
- 41cd6b708c56e1bad9b185ab09de02efd1f57d7c6691a9910d00b18489e59ec7
- 4733b5c290c00ca10bc72c248d6a014c6bf5fe21b92592b941cfdd8ac6870610
- 55099d0d5b7f5f677e431ebaf4c9a71877ab7b10887cb027ac78540ba1631779
- 680e98f78b16e05b2f55e1432f8553341cfd02ece47cedca652a04e1f4c901cf
- 6f496ef1284e79d93693374672e416d46b55c6590f8ab7737303b12f7316c2dd
- 9085e78cbbf63b30c42a4801cee1b67fa41f4c4308d0f163c3d39d7f76c00bf8
- 98e0df2e9cf8ba02d05cdc1bdea0cccc861855197f2a009f4a8fed152770b499
- c19b9d8770e3619d832401aa7bc385bbf7e239d0397febbb441621efbb539f72
- cca199364abfb50ec1dd467035fd2c637056abac9f8351393111dcdce8243e38
- d346a3d9a4be88b2e6fe2b78b391efa47d4de3c9acb23aeb31c0b0e1868d9817
- da9e5e6a5379284ca1b4e9be680bbecdcbca2378d8d8ae9e76e5601ba4fd9dcc
- eba22d087a40a79daa58a95e6337f53cf98885400019ad9e8417bb4ce2f2c8ea
Coverage
Screenshots of Detection AMP
ThreatGrid
Win.Malware.Razy-6703914-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: system
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{4LW407K6-M06A-64Y6-80K0-13CK6KK8U041}
- Value Name: StubPath Mutexes
- - IP Addresses contacted by malware. Does not indicate maliciousness
- 217[.]12[.]210[.]23
- 82[.]205[.]63[.]221 Domain Names contacted by malware. Does not indicate maliciousness
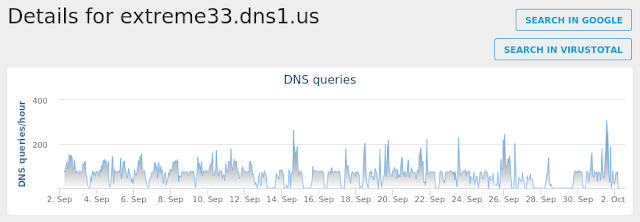
- extreme33[.]dns1[.]us
- mdformo[.]ddns[.]net
- mdformo1[.]ddns[.]net Files and or directories created
- N/A File Hashes
- 00e3f5ffeb38495cefce0f1c9522743764adf1ee6ce51b91c9c4726726562a12
- 01a7bdfdc6502db6bd237fcbc64596d8f76052e942c2c87e897f1ae786b7cac2
- 02c5fa1012b9cf0d46801cadcc4fe6814b4f75d50104e948031d00ff3ca7b93c
- 035f91568ca2bad43ce3fde98a2ae0418821e5f558c62b919c786c3b07bc0fe2
- 03970d185025e7e226c704b5bcd13de89730677345d3d57081d07895966567d4
- 052862be7afd84bbd167be8b83918d828608b35e1423600571747e67e66dbd16
- 055865fb005e3969e6d9e7feba2e81a8bedbe3048bf2a9cd3a9fbfe8ea6076e5
- 063e213ee0ecae95132a3cea557203b782de3c63b753fbd405ed670e83fbf573
- 07912d5cd0bf4ef89355a76c1fc36497e90333111b127dcf07d76cbc8ab76838
- 081fbe8f1c01676f9765ff7742b5d348433e2fd073136355100fe9f054140e6a
- 08627d7fbb6313bcdd42ac88152b71f4700dadf0446fb985b269c614bdd3f9af
- 08c257d2e5938dc6539b463ba0689982b79c112c8ad0aaf1be247726622ea487
- 092b86ef5f0e69ac5e1d554304189d289f27534fa4c7835ad4137f380a25979b
- 09c9b81d40f3c97876eaad0f29d7e9694c58c9a9cc4dc38b167611ecfbda3d75
- 0a032738a8ffc58b6cdce62ef209b247e008f597b6955d87da71e1654da970ef
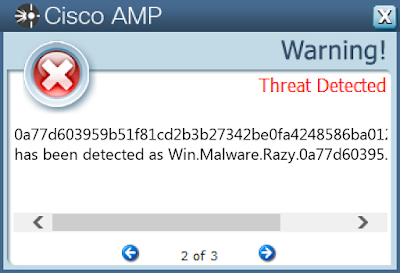
- 0a77d603959b51f81cd2b3b27342be0fa4248586ba0121779f1a9959fd701d11
- 0aa93c8240a9c593d6a8d5c226d4f0b7ac033cef70b39524281c52d92a97fb0a
- 0afde5386ca8587bca67577727f02c3e71b883b7b5fc72e25a0d542f6c5819c8
- 0d794619980f35738bd57712d170542d6d8ff58248d21529754a0881c0b139a4
- 0f4fc18209bbb1d979cb504b807142e1a24aa8ee831e33ce8825a5bd350096fa
- 0ffca4c710e5af160e813f686181131c963123caaeeea9762f86296822b8c883
- 10427e9a0ee1b4e3d349d61839e1f09cb86b2a68d23e41933127dd5ce2da0134
- 1343648c8b4748294191cfdca4b4881a57cee96db4051530c514e7c56e1152e3
- 1495bb27a646d27162b28bce50ebf25abc5182e7417ced315f1b93060f7e99a0
- 17983b493cd46b604ef3846516da1cda1628ec855b896be8b54a9558ae83058c
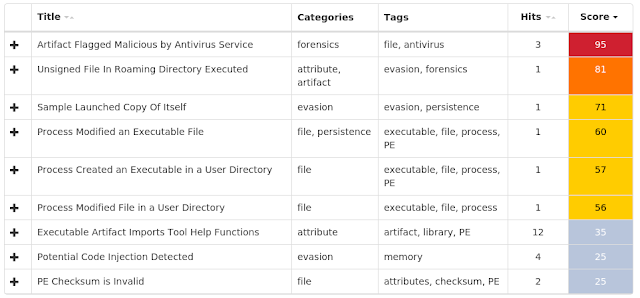
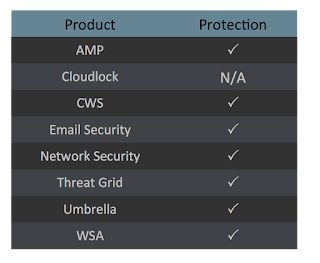
Coverage
Screenshots of Detection AMP
ThreatGrid
Umbrella
Doc.Malware.Emooodldr-6699885-0
Indicators of Compromise
Registry Keys
- <HKCR>\LOCAL SETTINGS\MUICACHE\3E\52C64B7E
- Value Name: LanguageList
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\PRINT\PRINTERS\Canon PIXMA MG2520\PrinterDriverData Mutexes
- Global\552FFA80-3393-423d-8671-7BA046BB5906
- Local\ZonesCacheCounterMutex
- Local\ZonesLockedCacheCounterMutex
- Global\PowerShell_CommandAnalysis_Lock_S-1-5-21-2580483871-590521980-3826313501-500
- Global\MTX_MSO_AdHoc1_S-1-5-21-2580483871-590521980-3826313501-500
- Global\MTX_MSO_Formal1_S-1-5-21-2580483871-590521980-3826313501-500
- Local\10MU_ACB10_S-1-5-5-0-57527
- Local\10MU_ACBPIDS_S-1-5-5-0-57527
- Local\WinSpl64To32Mutex_e162_0_3000
- Local\MSCTF.Asm.MutexDefault1 IP Addresses contacted by malware. Does not indicate maliciousness.
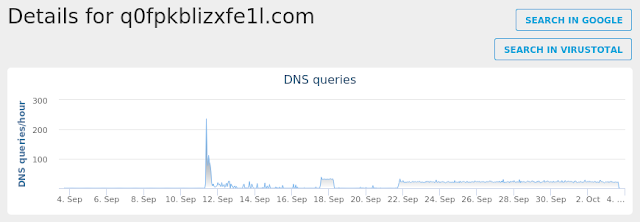
- N/A Domain Names contacted by malware. Does not indicate maliciousness.
- q0fpkblizxfe1l[.]com Files and or directories created
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B106E8EE-597B-49CA-A6A4-5BA8ABCC8F6A}.tmp
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{43E9ADDD-30D5-47E4-98B0-7E3A5536CACC}.tmp
- %UserProfile%\Documents\20180928
- %UserProfile%\924.exe
- %SystemDrive%\TEMP\~$8241024f69edc258237f01170ea088fd5064c5908267e943f97bc9e2a6ea1d.doc
- %LocalAppData%\Temp\CVR41E8.tmp
- %LocalAppData%\Temp\~DFD053DCDB50AFFE51.TMP
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{0EF83731-611B-4C55-980D-4D5CFC5BF353}.tmp
- %AppData%\Microsoft\Office\Recent\5f8241024f69edc258237f01170ea088fd5064c5908267e943f97bc9e2a6ea1d.LNK
- \TEMP\~$8241024f69edc258237f01170ea088fd5064c5908267e943f97bc9e2a6ea1d.doc
- %LocalAppData%\Temp\bdmwft0z.slp.ps1
- %LocalAppData%\Temp\tjkn23yi.53a.psm1
- %UserProfile%\Documents\20180928\PowerShell_transcript.PC.ceUgAgR5.20180928074741.txt File Hashes
- 06f0ec25e8b014b407402207afa8b6c0db494ad270d910534399c2137204e81b
- 0a8d4f2ac74485345284950b158da4be071633f33b0c7b9fa18d1f3e4d28732e
- 292b28d2f08fbd08ee8f1c2ed6f765b08c883031c0fae8dd84480ba0e1ca940d
- 3371fc7b0cf2d389571002c3ca26c9268edc373b79486e47bd6c349120f560c2
- 33d078881456e3b930c480803902fa28142b17c8550f3932e7cf4a1df0eb9213
- 567fe3794a9eec27697ae0634861d284279261880887f60a7374c6cbe63b7674
- 5f8241024f69edc258237f01170ea088fd5064c5908267e943f97bc9e2a6ea1d
- 91f0264ea76628c6b8825f358cd9cb8e1255604108fc059e0ac283d49c0dd852
- 933f5c822937fdec9325d1c99c5e0a5fda92296ef7c51ce7cd2dfc72bbe95b82
- cf8f98b1adf802ed2b24345161a38c4cfa499b36f17b0466a1da74edce84ba4b
- e469ba3bad870a5e7596035f69f2ba4cbb849cbdf9a8019890ccdea02c60e4d6
- f368d4a10770c42316d9c1024a0894b85048020526be03b2e824165b5b66e978
- f88ef62f2342f4d1105cfe85395b735efd3f0308b79551944983ce245d425510
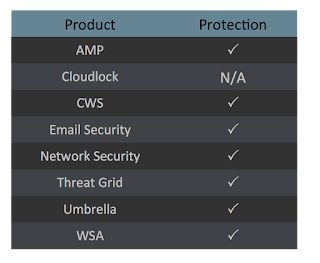
Coverage
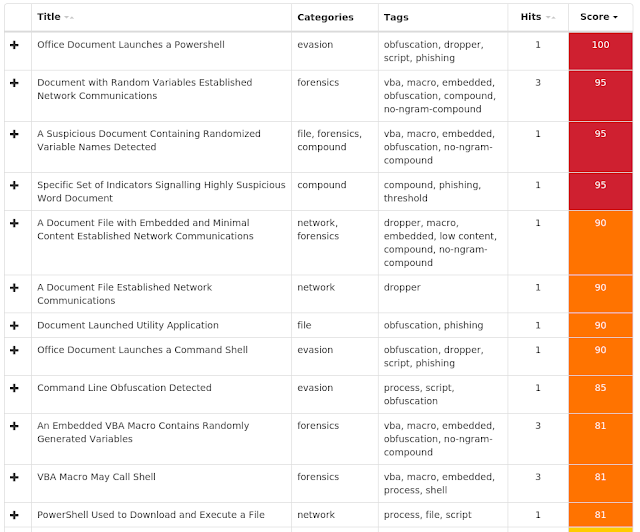
Screenshots of Detection AMP
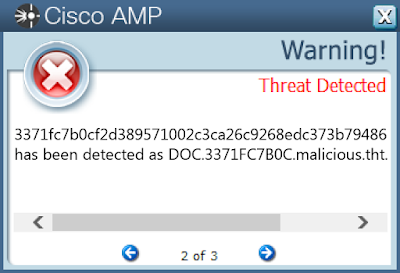
ThreatGrid
Umbrella