Today, as we do every week, Talos is giving you a glimpse into the most prevalent threats we’ve observed this week — covering the dates between Oct. 5 and 12. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, we will summarize the threats we’ve observed by highlighting key behavioral characteristics and indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this roundup are:
- Win.Malware.Emotet-6710203-0
Malware
Emotet is a banking trojan that has remained relevant due to its continual evolution and its ability to bypass antivirus products. - Win.Malware.Fuerboos-6712723-0
Malware
Fuerboos is a backdoor trojan that monitors user activity and captures that information to eventually send it back to a server. It utilizes a double flux network where multiple hosts act as proxies to further prevent researchers from locating the actual malicious server. - Win.Dropper.Demp-6714293-0
Dropper
Demp drops DLL files that are later injected into the explorer process. It is also capable of accepting commands from a command and control (C2) server and exfiltrating system information. - Win.Malware.Dgbv-6714452-0
Malware
DGBV is malware written in Delphi and is packed with Inno Setup, a free software installation system. Once deployed, DGBV collects sensitive information from the infected host and sends it to a C2, including browser password databases. - Doc.Downloader.Valyria-6713303-0
Downloader
Valyria is a malicious Word document family that is used to distribute other malware. This campaign is currently spreading Emotet. - Win.Downloader.Dofoil-6714608-0
Downloader
Dofoil, AKA SmokeLoader, is primarily used to download and execute additional malware. Read more about this threat on our blog. - Win.Malware.Zbot-6714649-0
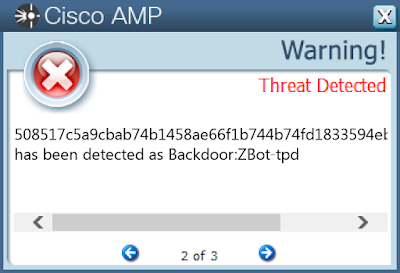
Malware
Zbot, also known as Zeus, is trojan that steals information such as banking credentials. It has numerous capabilities, including key-logging using methods such as key-logging and form grabbing.
THREATS
Win.Malware.Emotet-6710203-0
INDICATORS OF COMPROMISE
Registry Keys
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\dimcloud
Mutexes
- PEM6A4
- PEM6B0
IP Addressescontacted by malware. Does not indicate maliciousness
- 96[.]114[.]157[.]81
- 24[.]203[.]4[.]40
- 216[.]137[.]249[.]154
- 98[.]191[.]228[.]168
- 41[.]204[.]202[.]41
Domain Namescontacted by malware. Does not indicate maliciousness
- smtp[.]aavanira[.]com
Files and or directories created
- N/A
File Hashes
- 0eba4bf670ebd4381150a0d9e1fd113561898849ac53fd22e0eee1afe05de77d
- 12faaf05baa1ead6dd6559f2eed72373d78eff2e462c59fc055ac098b8ad7d38
- 1affd33a6864d27ffb7b2398630c06610a3c9d81d0f84548b7a66c431d2b733a
- 1d75775d6b05c878611b678b1bceacc76c888fb086ad2c47111aa696dad4b59f
- 1fca28e3264af2703e3e221b9193e93351b3b9ef3474643fb27d589b8c10840e
- 20dec98c8003e986251cc8a765a931783203ec75eae436e9df2248a465321e53
- 213395fba51bb15feb10d201b78df2a8c4bfcd25498f672b02391a77647cb781
- 36bc6b1def213cb8f10670fa3d574f831fdd63a9a5f2a66f66c1d580dfb75955
- 3e9e1062c311605bb78e8df525eaa11268ad5b547ae9295669a0c751e16f5a13
- 49a9333f65eb8a84e74b14a928d7ad94737c95117eae62e87bf84617637f04a1
- 6c231427d0fc1cf9ad431c7c5a8973db04e5a5cd2ef3205d6f544ae3b20a57f8
- 74e5ce08015255e67a1e21dfd2e44afb613a329b4bc6a4a678d1fb18e0d45412
- 8e0652595b5c7661ce08ef8c986ad31cef38020f80f7afcd500a9acbdd6ae774
- 995cca730bcdeecd0e497999e7ff2a4a6659fae45130e05599f0d716125c00a3
- a5a882b548a7b4faa705f9defef61566fdc778c983f58b71578896448f2721fb
- aa9c066ef31f701399812d51bf46231d88911bf062098e4428e8768002d6274c
- af253123e7bc9a5732d21ecca3d9d24db4c3a1d616fc8d8b14c3bdaa97bac3b9
- b7fab8bd7cfc07cf11cbf012b9d926cc4953df301b4d5bf8df12106d9d748aca
- c0fa19dd12030a9c24375a25dbfd413a6fd123b2b0451902af767167b313aad5
- c1ea9d852216d51cffbed3da3ef2fc23156f523096f900a9127ca91cbda542fb
- ed96c1d12554779cdef56ebd87ac4390815c006cb7771608297377cabc3a8023
- fb05b1c6edb8961620fff003d4ea496d889e5e217f28e77a7d6c37a6c73e3f17
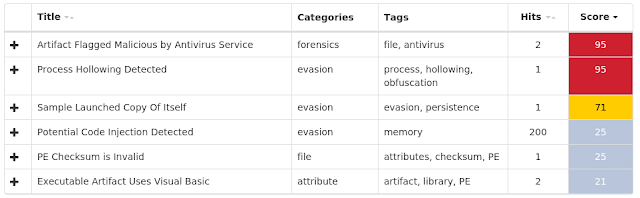
COVERAGE
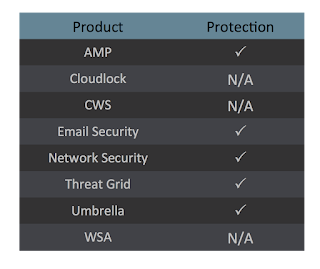
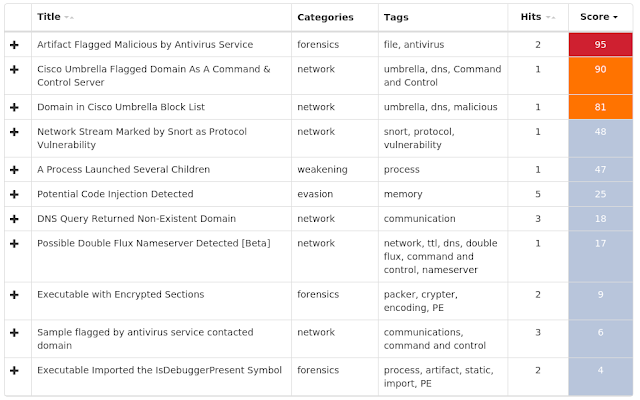
SCREENSHOTS OF DETECTION
AMP

ThreatGrid
Umbrella

Win.Malware.Fuerboos-6712723-0
INDICATORS OF COMPROMISE
Registry Keys
- N/A
Mutexes
- _!SHMSFTHISTORY!_
- !PrivacIE!SharedMem!Mutex
- SmartScreen_ClientId_Mutex
IP Addressescontacted by malware. Does not indicate maliciousness
- 54[.]39[.]175[.]170
- 51[.]68[.]239[.]251
Domain Namescontacted by malware. Does not indicate maliciousness
- s928eid19oqieuqoeu[.]com
- 11wiwy19wpqoqsos292uwoqow83[.]com
Files and or directories created
- %LocalAppData%\Temp\04pnjlnm.cmdline
- %LocalAppData%\Temp\04pnjlnm.dll
- %LocalAppData%\Temp\04pnjlnm.out
- %LocalAppData%\Temp\F256.bin
File Hashes
- 033a197eb9289e06f7541f3b66fdf308d8abce2fc4e7269776a664bde3e3945d
- 05f4d4b6a171b5dc1023b75983a6203f2a958f39a821c3483d05ee30c3a972d5
- 07783f32930a4b4b595976f347fc6272c1ac67e73b173a962ee4cb6cc92fd757
- 07b55edfd0e61cd0e120e0245dfe1dce775405c1aa12ea7717afdf3f55fae0a4
- 0d87696146e48e023816ca67ff8bc449bc326e6592d1fb588283eed4d6b80357
- 0df85fbe16e6252a12ad9096590d3f1b9af548f0972edfb9393521ac86ca26cd
- 10c075586237c573630d7361e55b910c38f67d9c8255592858b80e57c4c5b796
- 11a4da86de7617dbe52f7b89818626f10b4c4c326b71b2a7c8f4477293b5de92
- 12124b503f2989dea4dc2bbb9edc1054971075d7b326836693f5623ca46ffd1b
- 13a05b5af10b15d1ad5e296c75507b65c70f669cb5e48f3174fc28d9053e1ee9
- 14881ef04a4af32b3cd29d413557c5bee31efe0d1f35db0b5a570dac7dc0c6cc
- 19e9de7427f46bac7637d0a9a633d3b34d8e515df48b39229c1b673bf5105681
- 1df9d199d46a2f8f0b345b3fd3fdd77ac7c0449df03e156f508b3d0d1600607c
- 1fae65f06e00e08ec2d60519cd416335c7b26f0e92d4ef2b65e72f5a3d166172
- 1fd513421c26ae15b03dae61fe9932fbe7fc9bcc65a268867fed5a3987df18c0
- 23d849dd6ce38c93fb47adfdc6a29c28d7d9993534fc35eb9745396dab3c2edc
- 25466f6ed1011635a332ef93c465d5f6803e4099a09b8e3764f3d29a012e70fb
- 2773a65c5791d9382e498e84c352d5175445669c5b566c3bca150d9c320ebfe0
- 27ed0a3e9ca95105f734e9aa55fe6a65fafb196a291913af197a48c263865685
- 2ab936982eadd726bab936ab68bef211b3ffafd6f6f36dd1406830db72aae529
- 2b728ccccb05a1b03cb4ad4ccac320d74feeafe2f2be0a06f635fd9f56daec65
- 2b7cf52c1c83af3ad9349e551619be5031db6f58049cf7697e155ad25dd6519a
- 2e534b2373b08930ff05e39491405c6580be5bfd194ec6b9798dad7b5ba841e3
- 2ede38df97248bfea976a6985427a1f6dc3206b96dab218e14354653192576e8
- 30e2c4ce1d069cfbd7b3be5025a022e432a681b38dc1b60d2d83e51a160056be
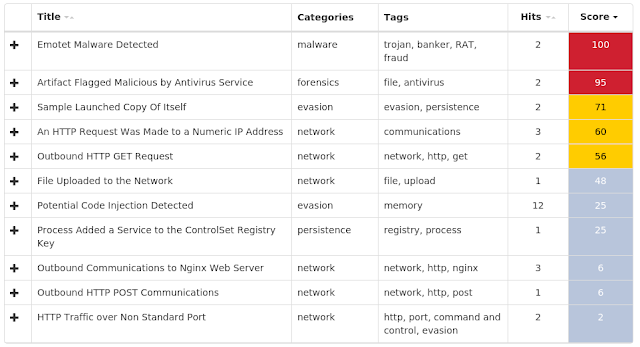
COVERAGE
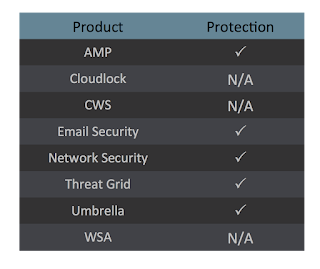
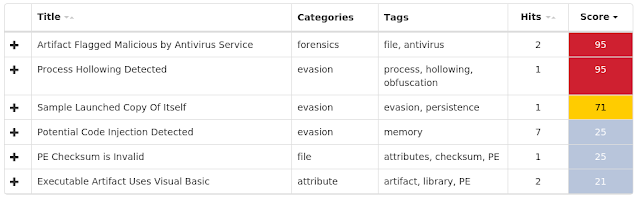
SCREENSHOTS OF DETECTION
AMP

ThreatGrid
Umbrella

Win.Dropper.Demp-6714293-0
INDICATORS OF COMPROMISE
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\Yqar
- <HKCU>\Software\Microsoft\Windows\Currentversion\Run
Mutexes
- N/A
IP Addressescontacted by malware. Does not indicate maliciousness
- 203[.]78[.]107[.]112
Domain Namescontacted by malware. Does not indicate maliciousness
- www[.]siamrich[.]co[.]th
Files and or directories created
- %AppData%\Albea\wuzuo.xuo
- %AppData%\Ebodyk\ruce.exe
- %AppData%\Ogno\ruof.kuh
File Hashes
- 1179d11e07f6bfc5e19bd4e715ffcc9ea8bb3c0e7cc6d4fe4e462f5433dab8c5
- 13bcb923aa00b7399e31fce0ad7c73c95d046b9fd9cc61fdad54a2001a24ef52
- 1751b6a0e5e0eb5709e63cf05f362e0256aff5c56bf919ce510cfa88836e7a3f
- 1dade14775862a6978810f9edc71679d7d7c128d469f2275258717ed88906d25
- 2e224ae755c32a914bc7be948a805b358fcc26ff1a95a04c6a05117501b164f3
- 5cb4338d783396dea3968b5f1ef16a3db4fca907a2c03e715aaafc61200eb20b
- 68f758a0d97e4f1a3dfa4c637c3d19332217c1c0fdf04e416d708cb9a7f47e10
- 7ee688e6cc5e3d6f27cb09c82842d7094f8de6d0900fba7c7686fe6e5edbb314
- 87dc7ea718d5dc4916bdee2a1b928921babc884f1754d5e01152b8bc868b6124
- 8f615ff9e9bafa6c0278fd4914bad01d4457689ab7a271d674ef0c7da569390c
- 967cf3782024def1f1bb478d12ab3658aa9081188a5f8a1b97bfb9daf37f1d98
- b816f28c64b91a88e8675191bdfc6fb6cee14808a475bd23594637a033bfa3a9
- cc7264cc4f7b0692935640eeaaccd71319a0459fe094f9b16cd055fa3cfb6ad7
- cf020f6d42ef17fb0afcb5d9abf51721fd2de655e61a565fbc3891574b278e57
- eb88635d91cbb0f85d235a2aec00fca2217fc16f076a5fb79cb6764c16eb002c
- ee8a67421a69bfd280bb7429e19efb3ee7fc403db592315963934409c841fed4
- f7589669d7b57285986b0ec280083fe66fb80aadc8b9d0ff279daac8459eb50d
- fbda080d12a9da511c5763b8269b393c3f76a511ff05a4c740cb017d933605fc
- fc9f06ce525f321e664d8a9c94bc7d8fe8420aadead196300451f5ade6867bff
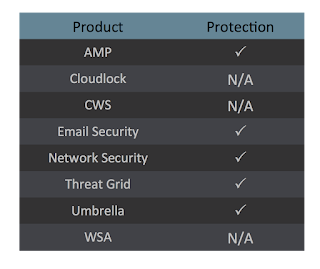
COVERAGE

SCREENSHOTS OF DETECTION
AMP

ThreatGrid
Win.Malware.Dgbv-6714452-0
INDICATORS OF COMPROMISE
Registry Keys
- N/A
Mutexes
- 3749282D282E1E80C56CAE5A
IP Addressescontacted by malware. Does not indicate maliciousness
- 45[.]122[.]138[.]6
Domain Namescontacted by malware. Does not indicate maliciousness
- filitimonieenama[.]com
Files and or directories created
- %AppData%\D282E1\1E80C5.lck
File Hashes
- 1d9cbdafba2ed47d7a420ea42b690664d06245f5c25b94cfdcbc3a1a33499164
- 23100d1c82e06b6b899d4f04cfdd393c05ca656767c7a7648981fd14973ee7a6
- 418d65586f05d278901417b0c8d7c4752ea7415b2c8fa6c093a460a434c02c52
- 58be850629c361f619da13c0106a8e7a1e61e07855fc23aa956e283a626ccaa8
- 60ae0309004f39b41fb96fa278219875668ad139974a35a6b5bee5ad42caf985
- 6ce5513f53a548aad74508dd376456b2cb7a91323c4ea27e2410ead309300b86
- 78e19745a107b3d196d476f81feeeb01663787869910f369b176c23c3536aaca
- 7dfd6d093b0fd406f734d92b3fac5e59631c0649170670c220743be74344634f
- 8b6348185f0d21c809f2d924f868bdf8ee2ea7b9ba59c41783a35817dfaf17c9
- 919d0e14a92fee33c9ec402b0e02b5282fd5cae502aadc2c490d3bfdf4350ad8
- bbd0a4000591033769be4ab26ca2fbe334440c4b56acb329433fc98c3405ceff
- c0a6d9b38153cc61dd042e7b9ea02df9b8d0958f27f31d5be5d89dd66303b0b4
- c6def90e73d83bfdfcaff20902a343f7d600f84ecb0a6531aff7b59a06ea8455
- c9abc638ac5e06271bede0ee3880ef8e034a11bd0cda260ef82d4b6ee978c292
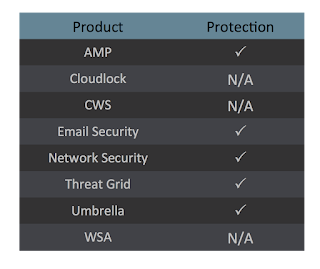
COVERAGE
SCREENSHOTS OF DETECTION
AMP

ThreatGrid

Umbrella

Doc.Downloader.Valyria-6713303-0
INDICATORS OF COMPROMISE
Registry Keys
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\dimcloud
Mutexes
- Global\I98B68E3C
- Global\M98B68E3C
- PEM758
- PEM60C
IP Addressescontacted by malware. Does not indicate maliciousness
- 12[.]139[.]45[.]113
- 216[.]215[.]112[.]198
- 81[.]215[.]192[.]201
- 113[.]193[.]217[.]34
- 96[.]254[.]126[.]140
Domain Namescontacted by malware. Does not indicate maliciousness
- optics-line[.]com
- ironspot[.]com
Files and or directories created
- N/A
File Hashes
- 0a212916b4767564de4a7b5ae348c56b4d9c5a799723e901352280a3e8d64761
- 0b62c13a5558d201266446b870d97eb458a82eab17d69a3d566a6e5abb158c6a
- 171e0e8440bb8152cef9ae20dec4a170f93b1312aadf782490cc36adf5c301a4
- 17b6cacdac7e3dc56d0b60ea7367e5073048e30aff6742e65b0a6f2b52b6255a
- 1b90e481327517deced0d43590dfd5715ac0d1645f78f65239aa091f653f4c07
- 2456f8835a6452a6bc07db97990ac81977f1102f41b53ffc68ed935022caee67
- 2581d63d7d772a3b1ac3b5ae095b03a9a76e771b3d153ac3e95ead93759880de
- 3c985296fc326089a695b2ffb78ab22b5bf6b0c28b62c9f8532281487479c99c
- 400d3ec69470e65f173f5ced9fd5bbedfa0458332639d5f48d4d46ad93f19c8a
- 50c4e66b9f3cbbab3298dc9113b16e485c17feecf296cab4829607942e6b63d2
- 5e3034a30bef39ff753853f3712bedc99baf5c0e3e84b8de6665e21716e9bf87
- 63ed9611ef53d62886a487b66638d5b4e022fb791182130d7fcef35a07f79080
- 6886615f85136e0c0624642251d7b5396c57f7ba5cdce955d2dd0b1f0be7e6f5
- 6a5ce4ce91c196918807df2bcfefe256d76970e5b8e87b40df1757639943090e
- 6af525481cb0998d33e3a3c4954da1545f0f6dcb25b899b450d98a4bc3b17c13
- 7603db9e307d728676caadf8d1e42733071087e6dc72a7a3ec747372fa0c965e
- 8319cf7cd706879ced641e96ce84ae78286c5eb3a8de911aaa449a922e2af6d4
- 8cf4ea0f49b0d6a0df0bcb066bea9bf27ee10ac34dd3e240c7cb19582b9041c7
- 97c4f7a023bf61ca96d3de53931c0fad28ca2197740999e930c8d702a346ffb7
- 9b58e48bc55057f200d72f6f6646097a4e1285bdea85073c3e0313bd953ee13d
- 9c8cd646405cc6c78665e8702051107b0531f7918829985335e6f5348c20a873
- ae445853c56dddcbdf899ab132adb7cd9cfe9eb7048ee643838bb85b7422ac37
- afddef6744bf508b82295fa1478a03e8016d10c6647925c46a8f0f8ea6bb3a3b
- b11cc1ae5ed0b068cc101b046a9c2c8a270d751273cf320934b790fe5afb91a3
- c77fcc0be04543148bbfab87443d2d81a712ba16c24f22963a0670275eab6bb4
COVERAGE
SCREENSHOTS OF DETECTION
AMP

ThreatGrid

Umbrella

Win.Downloader.Dofoil-6714608-0
INDICATORS OF COMPROMISE
Registry Keys
- <HKCU>\SOFTWARE\07771b47
Mutexes
- C77D0F25
- 244F2418
IP Addressescontacted by malware. Does not indicate maliciousness
- 77[.]182[.]47[.]152
- 77[.]214[.]6[.]192
- 77[.]198[.]181[.]15
- 83[.]226[.]115[.]86
- 77[.]253[.]52[.]129
- 8[.]123[.]232[.]109
- 94[.]227[.]178[.]89
- 8[.]110[.]105[.]136
Domain Namescontacted by malware. Does not indicate maliciousness
- N/A
Files and or directories created
- N/A
File Hashes
- 01ce9f47d246b23480249c21385f28af4f8f6c6f72de0e16f0d5995add2cc4f4
- 0b1e8ab791aa74ec379a8699c6e50fcda918c02b08aa4460bea8a842931cfb1b
- 0defb11ec4549eb802fb841cbb58ec72f8bde65bbed48245e0d83c6c942d941d
- 2273e345b799cc3ed8954fd82b62ad47f16615cb59531355039349d7ee84de23
- 26f4a9f28493a8250d38061536289c0249bb88b8e12cd304a70ae06475b4072e
- 2e2aa0b99d225a1583cb40ca233054fef69fe724190cfff0b7ffcd6c805223fd
- 303a92f502157d4a99c21c2ec6cd05cfa2400497df59a2e9ce322333ab6f78a9
- 404f7030cb01a7cdbae2ab38adafd587aa5da0cfc5bb55b92e7cf7b095ac543c
- 47326515c02c1fb96899aebf38fd18919682d79a1445ffa343dfa26e70261231
- 4c509d782de2ef525b83dbd61f70a59a2c64b1bbc8d02f063c0e081a2bc6b214
- 53b5bc66cc62f04439d75203bd7e0ff040e055c90598741f9dc26c59ce41dd64
- 5746ac7b26eab61a51ca790eecc9bfdf120fc711f4173c54c99ea653d154bd4b
- 5a36ad9f59dd0c8906cf6dd9c395785ba449c9dddc3843cc2d9a9aecd5f78c47
- 65360c29dd0b0cddcbc77cce83af3761439423c72276dd425755e6dbd3bfc171
- 6653fe7c4e305c524ca7d59ff8286bfe944af1e4672e11f8a08a7cea0a2dd332
- 6a8a02f29f22cbdcf42ca25ee3d26e4220c70cb133595bc9b3354742bb4a3a2e
- 743e3645040914b245661a2e145fb3237237cdb30a82ce6ee59461cd83505841
- 7ca20063faa25398f5e4ddc7d08e5bd39e71d816caeec5214bcb14c261d5ed25
- 83e460c7faf4d06a0b255a8ad4175577e9b8cdd8bb88645dff1a8841fc4c72ae
- 8b9e1ef2b8e37a459b1ead71b6b5c684aa5589b3f6a3fc7aacba4b7c0c3085d4
- 93fd66843eeefba26d494abf82bd69f972913c59e109a97a8871f1150e75ae01
- 95c587cce682887a0d9d6297e966a9fd82590cf557aac4767eff29ceafa373e2
- 99f203e4a8ee38b92ca80807b5350974d809505539284fa53d64b83aee28a749
- a48b79aa1d76c9c8480466757d3d198bfefa19434fe4697129d73bce75a412b0
- a593ae31f46ba0871580a5d7af3a8abd29fccd164c92dafc6c53f5b69487f717
COVERAGE

SCREENSHOTS OF DETECTION
AMP

ThreatGrid

Win.Malware.Zbot-6714649-0
INDICATORS OF COMPROMISE
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\Waec
Mutexes
- N/A
IP Addressescontacted by malware. Does not indicate maliciousness
- 176[.]99[.]4[.]7
Domain Namescontacted by malware. Does not indicate maliciousness
- N/A
Files and or directories created
- %AppData%\Gybyoq\uzbu.ecu
- %AppData%\Iftovi\ihuk.exe
- %LocalAppData%\Temp\tmpbed48548.bat
File Hashes
- 075954d09355c42653ebb8340916245a18e28b8ad5d7c701f2f3208f639922a9
- 168c7ecd964fcae27d56aeb73ebb5917b2a7f025d708019b870f184e92cf42ab
- 22bdc85124aa553038e1d5b27411c67b931406597cebdc3ab7eb149077695599
- 259f3336bd8bb16138f45cf341f7290e7edfbee2872a9927184d02643ac86b85
- 31903b752e05db104908f6e2853597d5990f0fb5378573f98870c57509765b28
- 480e51e1bef08a8870a7d852abab4ac58179d2fa8031a9a080ce8a5a04a3f073
- 508517c5a9cbab74b1458ae66f1b744b74fd1833594eb319592416d7825f5d83
- 5a8b1aecc07c0c707aabfe22e52a7f70cc65aeac7127f7fd87ddf74a172212dd
- 5b9b975f6f67ed9bf8f45db61117330b31770dc26aecd0262253531106bc74ad
- 5e0535beb2b18aa4a2a5db338485f6e87fba66cd79fb0afb0c1cc18a3d526b22
- 62bbd7305b5ccb36a11f1f8d81065daa537e1716fb1983d8b411993d365b2fda
- 829cc5bc44063c564e0cbfda5d7c4538df9c6eb54f37eb09cf14757dda2f6ad5
- 897527a34498f81ffac99f626abcc0045cc5953173c84f90766280d38edc4f73
- 90e57a0f986925b7bf5a9114ff99d0c764c82c2348ae9694cb3b49a10de49ee8
- 911529ae29929ba58e3e2f7c2b1db4c8697df181bc1122ed2a96268429eae8c6
- a3ea8684813d8849686a07809e576ea5276fd63de74fe65406871f7b3b3f185d
- a52de51d2c4ca3bcb65d3c35b0a02c2b83142d784e420cd06c79d500d24587d3
- ab3e38a476d1d7e136c670d16afeff8ac0a3f82578d0398ba1ec91792c447411
- b398d2d8c26361f98d8341bb38e42f9553b107756c0aeb5985688de7af309de6
- c25837b0eecbcac9726e6f6b41502b65796f5ddd20a42aa0311f18ed85302809
- db58802e343b45a0d173a3bfab5fae9fe1c6188a6a175042a496f2e7ae1b906e
- ecb59e655db783f2d4515b90f1045b154827820de20b09ebebe382895726bbcb
- fa1962bf247694be787999b8b94dba8a09728cb258776b067a01128d3e073d01
- fa9c078a6fbc67f8545381c4dbef455ce3e4e69c518ffdb6080103b98742b00b
- fab9b2ba302d819180f19df41bf91abc7370b22fa0a08d35bc6a55dcb9751471
COVERAGE

SCREENSHOTS OF DETECTION
AMP
ThreatGrid