News summary
- Cisco Talos has been monitoring the BlackByte Ransomware Group for several months, infecting victims all over the world, from North America to Colombia, Netherlands, China, Mexico and Vietnam.
- The FBI released a joint cybersecurity advisory in February 2022 warning about this group, stating that the group has targeted at least three critical infrastructure sectors in the U.S.
- Talos has monitored ongoing BlackByte attacks dating back to March.
- BlackByte updated their leak site with a new design and new victims and is still actively exploiting victims worldwide.
Executive overview
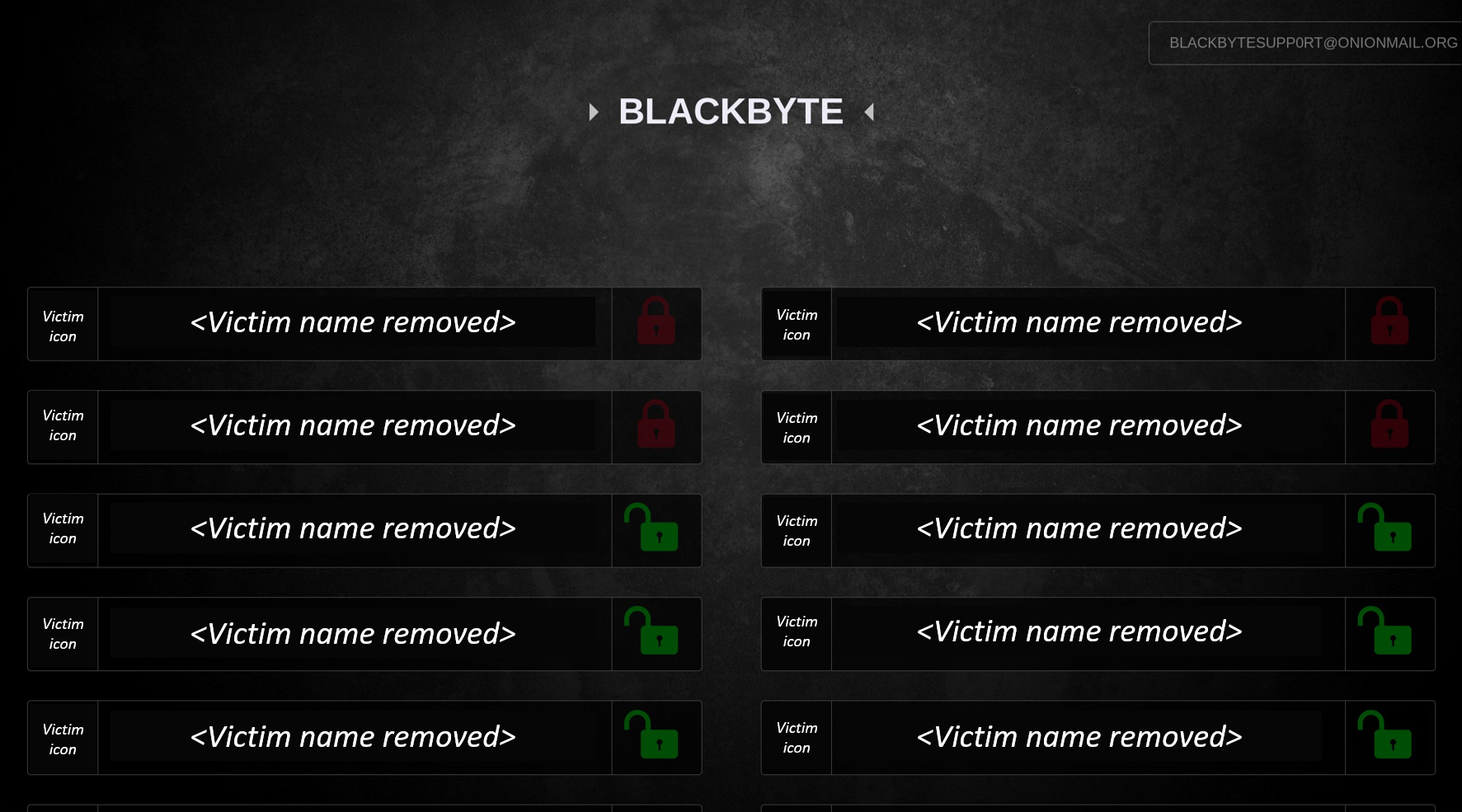
The BlackByte ransomware group uses their software for their own goals and as a ransomware-as-a-service offering to other criminals. The ransomware group and its affiliates have infected victims all over the world, from North America to Colombia, the Netherlands, China, Mexico and Vietnam. Talos has been monitoring BlackByte for several months and we can confirm they are still active after the FBI released a joint cybersecurity advisory in February 2022. Additionally, BlackByte is considered part of the big game ransomware groups, which are targeting large, high-profile targets, looking to exfiltrate internal data and threatening to publicly release it. Like similar groups, they have their own leaks site on the darknet. The actual TOR address of this site is frequently moved. Below, you can see a screenshot of the site. We have anonymized the screenshot to protect victims' privacy.
The attack usually starts with a network entrypoint, either a previously compromised host or a software vulnerability which is exploitable from the network. The former compromised host elevates local and domain account privileges and moves laterally by using standard penetration testing and legit administrator tools (LoLBins). In most incidents, they like to use the AnyDesk remote management software to control victim machines.
Technical details
The BlackByte gang often uses phishing and/or vulnerable unpatched applications or services like vulnerable versions of SonicWall VPN or the ProxyShell vulnerability in Microsoft Exchange servers to gain access to the victim's network. These are usually known public vulnerabilities that the targets haven't patched in a timely manner. Due to a lack of logs, we could not confirm the initial infection vector in the case below, but we have indicators that a vulnerable Microsoft Exchange Server was compromised, which matches the previously described behavior of the BlackByte actor.
A typical timeline of an infection looks similar to the anonymized log below, which we saw in our telemetry in March.
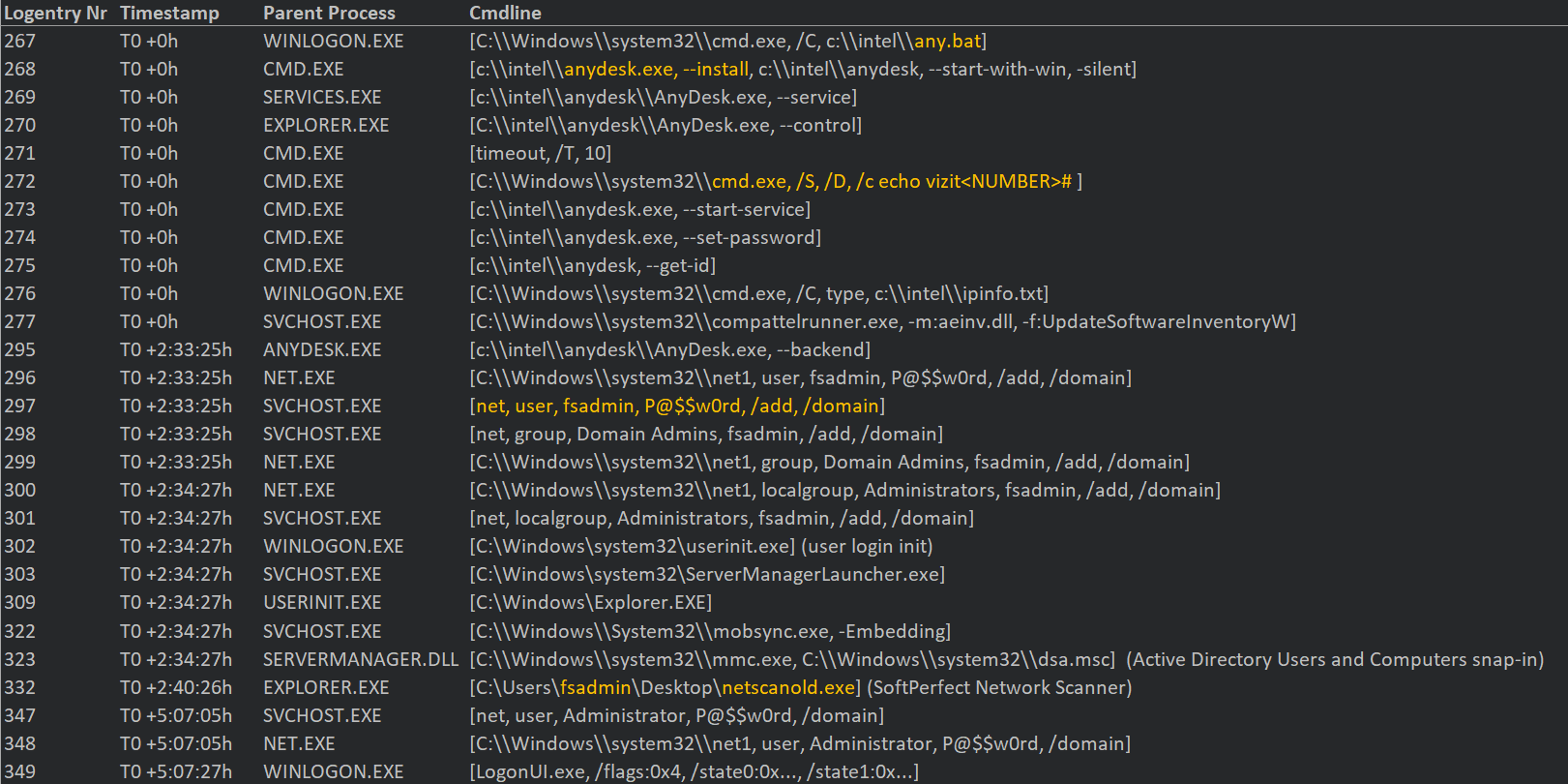
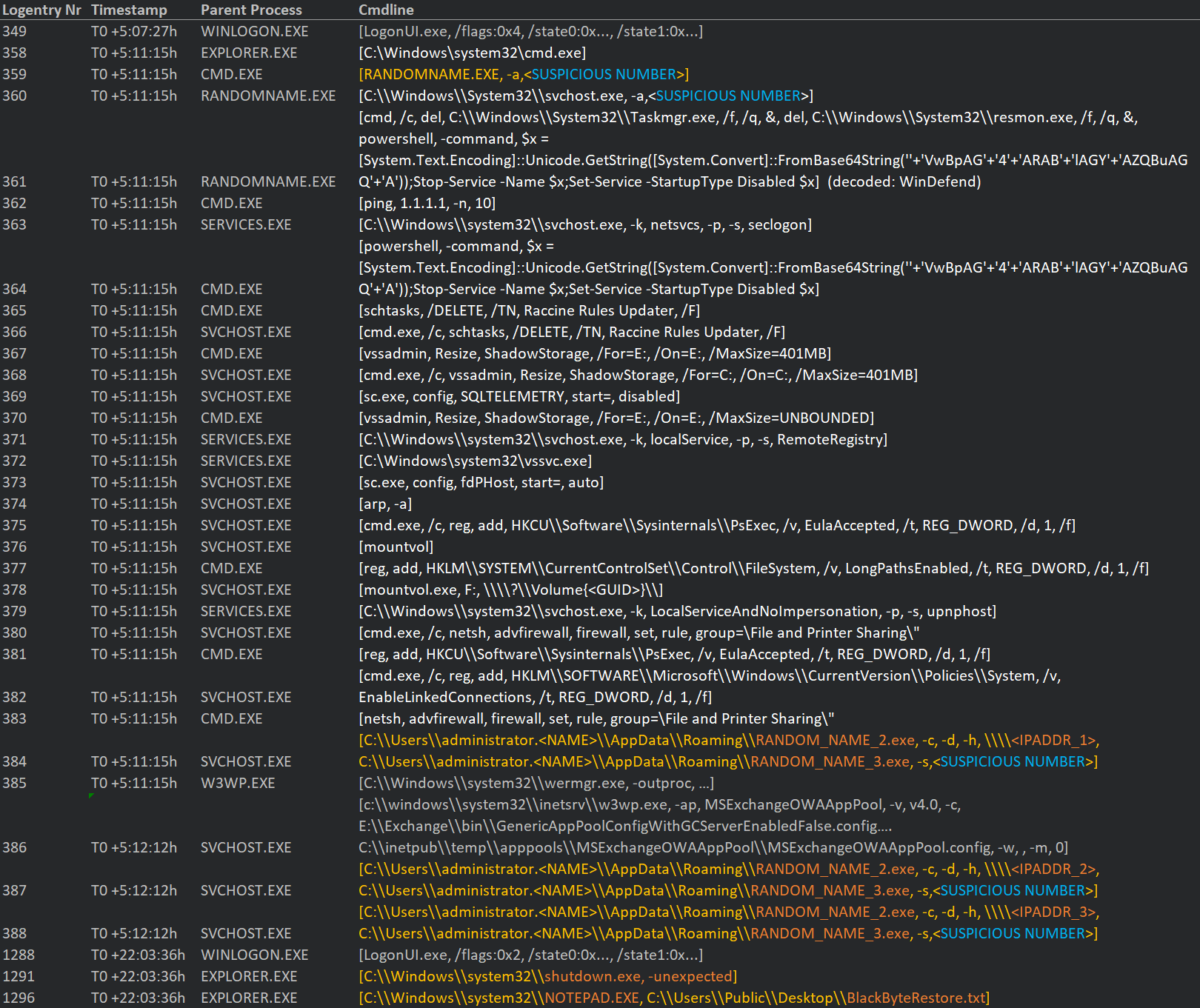
The logs above show the adversaries are installing the AnyDesk remote management software, as we've seen in Cisco Talos Incident Response engagements. BlackByte seems to have a preference for this tool and often use typical living-off-the-land binaries (LoLBins), besides other publicly available commercial and non-commercial software like 'netscanold' or 'psexec'. These tools are also often used by Administrators for legitimate tasks, so it can be difficult to detect them as a malicious threat. It seems to be that executing the actual ransomware is the last step once they are done with lateral movement and make themselves persistent in the network by adding additional admin accounts.
Unfortunately, we could not obtain the RANDOMNAME_n.EXE files, which are likely stages of the ransomware infection. We also tried to get them via the telemetry of our partners, but the hash was unknown to them, too. This points to the same trend that many big game ransomware groups moved to the tactic of using unique obfuscated files for every victim. The chat with a criminal from the ransomware group Hive we've transcribed below provides an idea of how these conversations go. We are releasing more details about conversations with ransomware actors in a future post.
Victim: "How many files are stolen? and can you share some file names?"
Hive: "Hello"
Victim: "maybe no ones here"
Hive: "To decrypt your files you have to pay $20,000,000 in Bitcoin."
Victim: "that's way too much, can you please discount and please share the hash of the ransomware file so we can at least black list it. You have already stolen everything anyway"
Hive: "We don't provide any hashes. Every time the software is unique. There is no need of hashes here. It will not help anyway."
Hive: "If you want a discount I would like to see for how much"
Assuming that RANDOMNAME.EXE -a <SUSPICIOUS NUMBER> is the start of the ransomware infection process, they have slightly changed their behavior or are just using a different packer. The FBI document states "complex.exe -single <SHA256>" launches the infection process. In our case, the parameters are different — the first one is a '-a' and the following is not a SHA256 hash, it is an eight-digit number, like '42269874' (not the real number, but similar to keeping the privacy of the victim). This seems to be a victim ID or an offset for the unpacking process. The actual behavior of RANDOMNAME.EXE seems to be very similar to the complexe.exe one described in the FBI report. It also disables Windows Defender. The base64-obfuscated string 'VwBpAG4ARABlAGYAZQBuAGQA' decodes to 'WinDefend', which is the Windows Defender service. It then tries to disable Florian Roth's Raccine ransomware protection tool and a few other commands mentioned in the FBI document.
Finally, approximately 17 hours after the ransomware infection process started, the machine reboots and the ransomware note "BlackByteRestore.txt" is shown to the user via Notepad.
Conclusion
Talos research and other public reports about BlackByte are mainly pointing to vulnerable, outdated systems as the initial infection vector. This threat shows how important it is to have a proper update strategy in place. If your organization is running a Microsoft Exchange Server or any other internet-facing system, make sure it always has the latest patch in place. The time window between the announcement of a new security vulnerability and its weaponization and use by criminals is getting smaller every year.
It's more important now than ever to have a multi-layered security architecture to detect these types of attacks. The adversary is likely to manage to bypass one of the other cybersecurity measures, but it is much harder for them to bypass all of them. These campaigns and the refinement of the TTPs used will likely continue for the foreseeable future.
Coverage
Ways our customers can detect and block this threat are listed below.

Cisco Secure Endpoint (formerly AMP for Endpoints) is ideally suited to prevent the execution of the malware detailed in this post. Try Secure Endpoint for free here.
Cisco Secure Web Appliance web scanning prevents access to malicious websites and detects malware used in these attacks.
Cisco Secure Email (formerly Cisco Email Security) can block malicious emails sent by threat actors as part of their campaign. You can try Secure Email for free here.
Cisco Secure Firewall (formerly Next-Generation Firewall and Firepower NGFW) appliances such as Threat Defense Virtual, Adaptive Security Appliance and Meraki MX can detect malicious activity associated with this threat.
Cisco Secure Network/Cloud Analytics (Stealthwatch/Stealthwatch Cloud) analyzes network traffic automatically and alerts users of potentially unwanted activity on every connected device.
Cisco Secure Malware Analytics (Threat Grid) identifies malicious binaries and builds protection into all Cisco Secure products.
Umbrella, Cisco's secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs and URLs, whether users are on or off the corporate network. Sign up for a free trial of Umbrella here.
Cisco Secure Web Appliance (formerly Web Security Appliance) automatically blocks potentially dangerous sites and tests suspicious sites before users access them.
Additional protections with context to your specific environment and threat data are available from the Firewall Management Center.
Cisco Duo provides multi-factor authentication for users to ensure only those authorized are accessing your network.
The following ClamAV signatures have been released to detect this threat:
XXX
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
Snort SIDs for this threat are XXX
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
Orbital Queries
Cisco Secure Endpoint users can use Orbital Advanced Search to run complex OSqueries to see if their endpoints are infected with this specific threat.
IOC
To protect the privacy of the victim we can only release the anonymized logs, but we hope this helps SOC and security staff to build its own custom rules to protect their assets.
Typical Log data: