Today, Talos is publishing a glimpse into the most prevalent threats we've observed between February 2 and February 9. As with previous round-ups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavior characteristics, indicators of compromise, and how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of date of publication. Detection and coverage for the following threats is subject to updates pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this round up are:
- Img.Dropper.PhishingLure-6443153-0
Office Macro Dropper
These Emotet distributing droppers use images to present instructions to the user to enable dynamic content. - Win.Adware.InstallMonster-6443601-0
Adware
InstallMonster is a software bundler that may install unwanted applications on the system as well as display unwanted advertisements to the user. - Win.Downloader.Adload-6418193-1
Downloader
Adload is persistent adware that repeatedly opens popups and fake error messages. These popups direct the user to advertisements, or download and install additional unwanted applications. - Win.Downloader.DownloaderGuide-6443792-0
Downloader
This cluster involves XmasFred installers that downloads and executes other binaries. - Win.Trojan.Emotet-6444504-0
Trojan
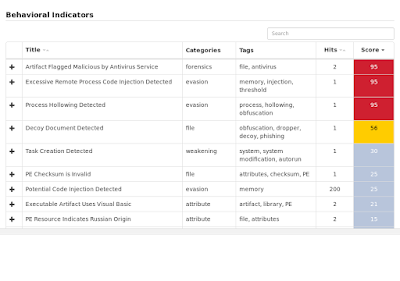
This malware cluster covers Emotet and Tinba samples. The malware is dropped by obfuscated VisualBasic executable files. - Win.Trojan.GenInjector
Trojan
This family is highly malicious and injects code in the address space of another process. Moreover, it uses process hollowing to hinder the analysis as well as long sleeps. For persistence, it sets autostart registry keys. - Win.Trojan.Zusy-6443152-0
Trojan
This .NET trojan contains a module called God.exe that creates a fake svchost.exe process in AppData and adds an entry to the list of authorized applications in the Windows Firewall.
Threats
Img.Dropper.PhishingLure-6443153-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- MC8D2645C
- MD57D8F73
- Global\I98B68E3C
- Global\M98B68E3C IP Addresses
- 176[.]223[.]209[.]113
- 212[.]5[.]159[.]61 Domain Names
- www[.]manuelaponomarenco[.]ro Files and or directories created
- %WinDir%\SysWOW64\specsystem.exeFile Hashes
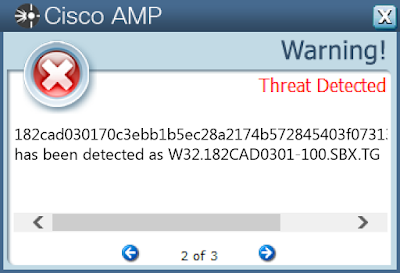
- 182cad030170c3ebb1b5ec28a2174b572845403f0731363291ccf0d16350f891
- 1aa7436383c71ed5bc878e1e52bf66a017cb6b82b4ee6fbe23b67b11403efadc
- 1d869439f6a5b2e51a92b579924395478263b897822bd76124639a0d78fe361b
- 281ae4e896a0fe96ab28bab6a1da4d9a9d36f2b4d4ff88167df990e50735d0f5
- 290dc3abf2bdb619f6c8d2abf79d12483dc8b0ae420ab5ccfca178baeece5089
- 2f82036da229db4a9600179aad8e967edb06d1c0bfa2ea8f857bcc781ed30e08
- 35de4cf3ed429504e8b8695b33f386d2ca84017373af99b76f41d5df69f5f84c
- 3927f8d5492927df58b6ea3a97197592cb9ce4ef9fc98f5e93952805d6ebbdab
- 43089883a4e0d5dcb286f4b7bc585bc418a4641a0e3d1c0919215a2112378630
- 43e7bcef39f88ca7d3b9b67d09f9264c4946e0e12a337c23e043bb8e9f634c2e
- 46acbdf64873613dceff0d9d5af2169ef6af5b71576a312d3cd2320bc2ca4f34
- 4c6203f2c7d3590948d783ce0dbf181927a3645b82167fefbad5d34a203112d2
- 4d31f25c4da2b05fbacc21035e0a2284be60e10ef103d3a1d412234717706550
- 4e9624a45f3419c398f9fc9c7e8ec2e8472b432382c11c984aeb7860e1297903
- 54144d97c81096fb6cd6464b12cd1b6c48e5f2b0ce0d8b1f16e34af0153a98cb
- 5602ba9c52386806f8d723f63265fe94d15303d3112a2c0b6bd7b6319626c32f
- 66ae2270fff3a22c0e1a65fc4952f735b42b4d03445d5729b3a4e74d9ffe5d49
- 6755c2d4855a8b5ec2eb9dd9ab20edc55230c9cd12c372080bae52997899cf2e
- 6cf585b16de1edb9dc313886ddb4b32d617290eef1c9ce1a2ef6160336c1eaad
- 6e2460dab20fcca216798641dfa821e73b5bccf510df487839f542a198740778
- 6e4a276dd2d745f57faa6e18ba90e255836ef4976c65cdfd831412b8ae4ab91c
- 6f9034646e6fcead5342f708031412e3c2efdb4fb0f37bba43133a471d1cb0e0
- 72d16e5244d6e31f29a0ce765df09b6e9f8cc096a4266458001ce1cff345a398
- 74b66767a723949e5b0837eb281bad34b6f6132d9b4aef0b3d36651193edd3d7
- 76c7d0440bee5b4f885592bc4714e5ed3c1ba6677f95702d83cb44a52907437a
- 7c344293212b1de4798beb0cf70c9bec493460d5befba2eef1ce26a83c04ad2f
- 853ce320b07e88db313df40a05307921594d83f568ec7cb5981e180d24a7e510
- 865e660b5d65cfea1cf8d595c281363bd399c0a47b0270dac8bb9b8e7dd9fcf1
- 86b774067ba5911413c1125626056f32d4e076c0c15aa38e78c606573b3f730e
- 87dc2f7b36c4423f641516068c94feb3c9a634fbaa9196244cbf03bed8f2c85a
- 9f84428908f16511529c2589a917e7f53b3568cd7a7832d966cf06333bb26bcb
- a317da8fffca78122bc24c3c39d4c6af965aa9e1bae00a0705c7cee8c231dc79
- a77e40b03e814c6f554929a939839416d80f73228a123ab953be37a1f25780b5
- a8c75f9b1e601c4c77b67ddd1bdb28bf9164c4f507b9530fa31861f2c72fb2d7
- b62230042f02ecdff4a53e7d3cb77023c1d4bdde332d568cfc2c1001500c314d
- b6600f389bf52796db5fcba03ef991df5a395a1a70b0f4096445469f9553ecde
- c412ad121682d33210402955ad330fbd182c5c57155bab2db659c7557d4a417b
- c462b00bfbd8e3bd79fe54c2bd74850b3a4a6d67b36cf3dc088462910b593b81
- cb7ce3342987424ea1303adb8172f0172f4bbead7a348263f67bd84630b01059
- d007c2ec4483fcd4dbf67233956b194d3a3a46426f700282ea7b01785a10fc50
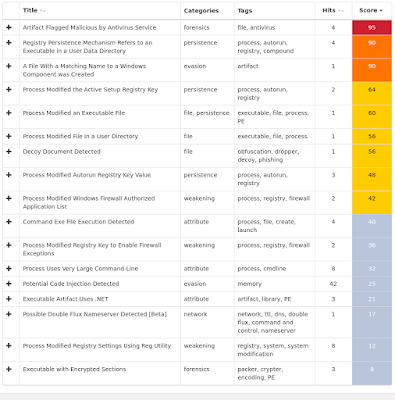
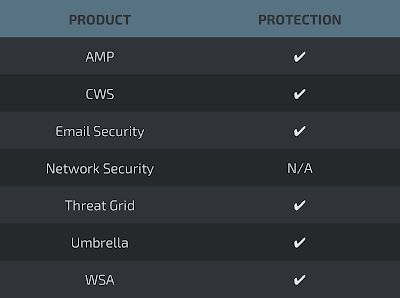
Coverage
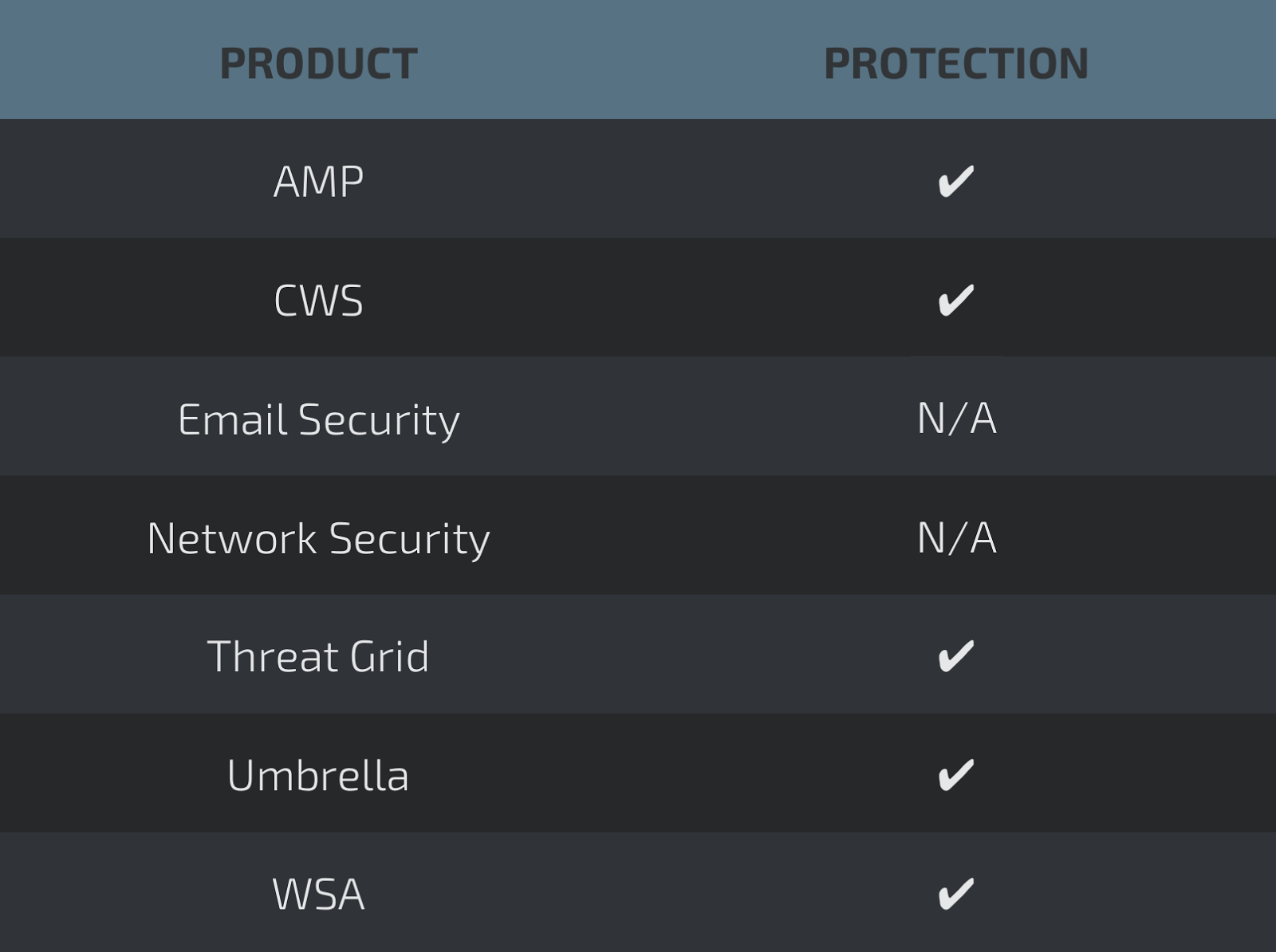
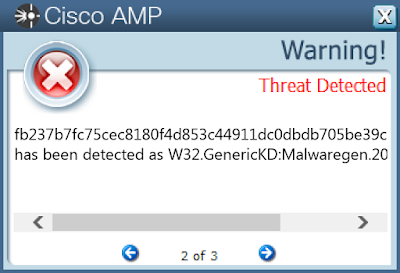
Screenshots of Detection AMP
ThreatGrid
Umbrella

Screenshot
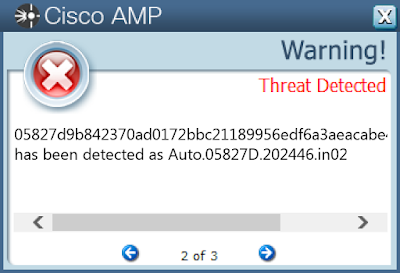
Win.Adware.InstallMonster-6443601-0
Indicators of Compromise
Registry Keys
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value: ProxyBypass
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\INTERNET SETTINGS\ZONEMAP
- Value: IntranetName
- <HKCU>\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage2
- <HKCU>\Software\Microsoft\Internet Explorer\Main
- <HKCU>\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings Mutexes
- N/A IP Addresses
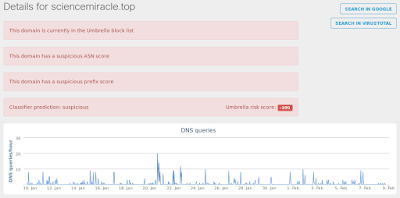
- 200[.]7[.]96[.]22 Domain Names
- sciencemiracle[.]top Files and or directories created
- %Public%\Desktop\Download Corel Painter ...lnk File Hashes
- 05827d9b842370ad0172bbc21189956edf6a3aeacabe455c3386fb294c91cbac
- 02fe9351831a92fc038f546703d9d76a84474cef38c93bdf2fe2f76d3409e932
- 049fc0a7cece52d6f40d34a5ec7f1e55e1a00b15d78fc831397f050785a92e5a
- 0b20d5bc9b5f22fde1fd769392a8df02722cb30f12954a18fad2570f6c2fcedf
- 0d10201d5be9135b7bb1676c30452fac1d82019debcf3170655a0719ba3e0d59
- 13353b13d483f3096a3c4cc98bbbecdf5f67c86e13d1af3627b9f61b8a37c058
- 16ee6d3da75a3527ce741fbcbd8424b52826fcd89510a1206d9e30df1e441ff6
- 16f734eac6b1360142b4f4602aa7543b0af21440e0c6d06f635f6f685b6d951b
- 1901b7872887beca319f88ded466061762dcce27b82964e0771bdc239d70a04a
- 1e1f00584ddd324467fd0e2b9f06d1320efdec7253f63833d19d960acc598975
- 22903e84c8be9c4cef7ec3a7280fa359cced7bb9ee71de74f815a38f07c1fcc4
- 25750ae1857c77a233d43bad1ca56b7287efb31d568c8788cddfd56e8f161f22
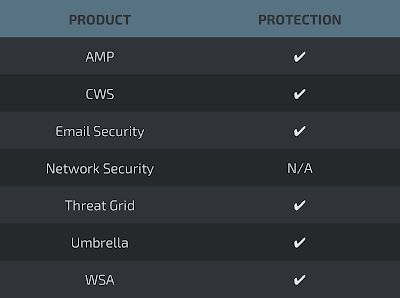
Coverage
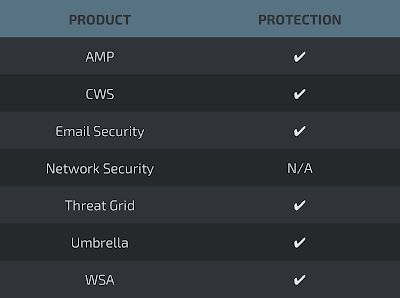
Screenshots of Detection AMP
ThreatGrid
Umbrella
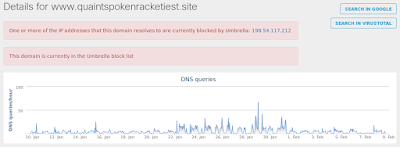
Win.Downloader.Adload-6418193-1
Indicators of Compromise
Registry Keys
- N/A Mutexes
- Global\AmInst__Runing_1 IP Addresses
- 198[.]54[.]117[.]200 Domain Names
- www[.]quaintspokenracketiest[.]site Files and or directories created
- N/A File Hashes
- 1f910886460d291aa28ce33dff560b291ee3a9040c1ffe125134d01cb8673bd3
- 1f9c34ceeb4600837359be13415e95783f4e5f7ea8d3def87ce3b06ec6a047dd
- 1d5c26af77f30dab347de49c91146a6d2d3b95df5ccd532fc1d8aee0ae63eda8
- 1474c9ed8ea883047a1f069ad93cfa3516d3a337fbbf93ae9248c17f6646c3ba
- 10b8bbff557792a03e71fb766b075cc6281976e05694b11bfac31a375863d6d6
- 0dc1235368b24fed46e7f744c6b9f9c486d3b36a3e6fa1a20d7ec869ac656310
- 0bbff365a4284eb3ab0932cb80f5d3d35880ec2a0c473daa7a75ac46c091bb3c
- 150a103d11bbc8638116a30427620db833d926e6bd74fcda12ec90d6e89dfe3d
- 0b2c3b28e73b96ab473d6e5f4c24c8c427e9639d7efe203faededaf09480c2e6
- 051826260a52420903d9c17d973a0cc78dc5706140df1af05cdafd9321d2764f
- 0473d1632bda43d83bc8fdb65d095479a5ef49ad816725b84aa9a7bf75356d42
- 25b2aeddfe481e574ee14ead95537de4d94b18d3654c8d0866dbe42631aab64c
- 1eea07045426f602a8ec956cbe99556c8b54c1d51610fe7a6806941a79deed84
- 19d41761096fdb20dc412af13a00c6ec752ca7bbb8444aa9c546aa0fb5385782
- 1978e7025d0cff47a798ce59da8e3f5dafe6b9ec39aa46ca1882fdef2a0b61c2
- 0c00f2e323696cc3f39832b7da538701850d28998610711d8d70594314436399
- f854f72ac2f61de681be53b78c6c5050580c19c589104c3efdedc8a4838e6932
- ce37d2dc789a535be7af9a44827ebce419f8637a09bb7e352696d474e07786a6
- cf5249a37d8c7526cd7daabb01e8df29eaacf7cf93759ac09b48e08db8b26c2a
- b99011d4fcafe5ed1e022534e5dcc18835fae5a86c873039a1a56617414689ec
Coverage
Screenshots of Detection AMP
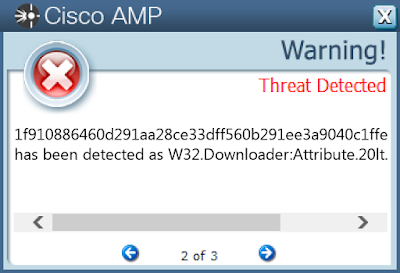
ThreatGrid
Umbrella
Win.Downloader.DownloaderGuide-6443792-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- DlgCpp IP Addresses
- N/A Domain Names
- dlg-messages[.]buzzrin[.]de
- dlg-configs[.]buzzrin[.]de Files and or directories created
- %WinDir%\SoftwareDistribution\DataStore\DataStore.edb
- %WinDir%\WindowsUpdate.log File Hashes
- 2713963eb9b15eba3254444d86bdf9fc50c0a44709eb8ee154c476786e9d99c1
- 3529872d962530a50f47e947ea5c4a367fb7bbc8d6084dde1d8089e3b48b3893
- 93974e363e38dfa5d11fd227e0de730d62b0967fd640b31e7382903b6ba5f739
- 59c68020dee3bbb7e0c071db202fff734b858aef4aa0f708054bfeee08577cdb
- bc0015c6ab7cab17c34b96111a165591b4db5fee01eed778a9ab6d285e51485f
- 902f1150f83800ac4fc2c28a3e83253f7892c297ca4998955fc66f78336fa69b
- 466fff17d182237602a6ed4897a0122a61d1b4e4bed73481b41a10fc7d5355da
- 103ee228b018a8e1e689a03c610fad4ab9d0c4d644facbba745b1b63f5ed40ec
- ad75bfc96fd6e336be402b250001620706ba1ff4b54f7ddad92a6ec4e760c320
- 70e6eaccfd29763b4bf117067e0ef378b3720616fc82406a1d8e546d51919fb4
- 1ae3646b98b09736443aa3d26e5396d7feb510a14d6275a98d010903c660e8e1
- 3c14d644d76bc09c3243305a01221246e4c30d58b5498a42c6a7248b28f29645
- 85961d3953f9830946af4fe46e6639dd57e56df6be26689c497a93bbec0543e9
- 319cbac9d24298431ce6b4451ca1751d05787a39ab298dbbb516c6351bc7e500
- f1ea59a7312d82b48c43292466b44b5533dee92b0dd50d618454fe695bfcde05
- e0c3b75a1fd23310c6310a96c2a9c1f1d6aafe6a89833aa5eb68f307e1c8a074
- 9731e93d38a6cd040102243cd9918f9ab63f23c063e51284700b4784325f7a00
- 8deeb09519b1a398409fcf5e375a6c68f8712a168a98fb41721d1fb3ea8dd8b9
- d3c318d3bbf3186e879a6dd125e0828eb480120b231df33e34156d2b9a32aff2
- 8fef976a246e440dba1e3f45671588253e1f8c46acc10fe5d1873098b9f2bd3a
- 9c8ea37c3c17728b11477936e0723de25c74ef38d66d5b17832dfca7b1788d76
- 85739ff86a8c4465f0abe5eb0dd9100f453a15dfe5c1756de34ab40247273d03
- 14d5afb6e3867b3016925a53c294b87fe2122fbf8650f468c9f5e3e1ca115b16
- 5cf9b749006d7404e09190d54d76a7f0af758471948ed6d924736dec784689e4
- 1bf58f0bfb9ae73d0735519717731e2aaf159b975b7ed6442565fdbbb496cd23
Coverage
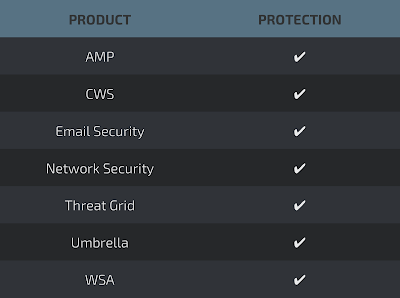
Screenshots of Detection AMP
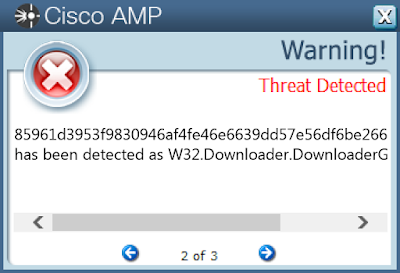
ThreatGrid
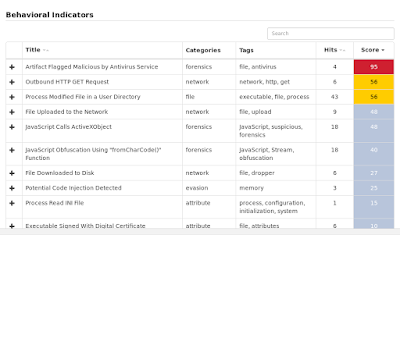
Umbrella

Screenshot
Win.Trojan.Emotet-6444504-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- FAFEB955 IP Addresses
- N/A Domain Names
- N/A Files and or directories created
- %WinDir%\setupact.log
- %System32%\7B296FB0-376B-497e-B012-9C450E1B7327-5P-1.C7483456-A289-439d-8115-601632D005A0
- %System32%\7B296FB0-376B-497e-B012-9C450E1B7327-5P-0.C7483456-A289-439d-8115-601632D005A0
- \Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01.chk
- %WinDir%\Tasks\SCHEDLGU.TXT
- %System32%\wdi\{86432a0b-3c7d-4ddf-a89c-172faa90485d}\S-1-5-21-2580483871-590521980-3826313501-500_UserData.bin
- %AppData%\Microsoft\Protect\S-1-5-21-2580483871-590521980-3826313501-500\638784ff-73cd-4f1c-a5cf-845c7e3f97ce
- %System32%\config\TxR\{016888cc-6c6f-11de-8d1d-001e0bcde3ec}.TxR.blf
- %AppData%\Microsoft\Protect\S-1-5-21-2580483871-590521980-3826313501-500\Preferred File Hashes
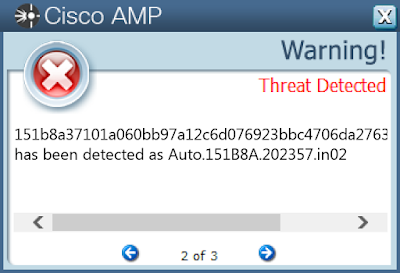
- 151b8a37101a060bb97a12c6d076923bbc4706da2763fc0bde43fb2ae5b38e3c
- 912c1c5303e782d4ef43f65146b80d0efe2d79e5a0f43e06c8cd146125a9e0a6
- de3b898b771d6e1abfbd5c4cacf7db4b806ab8048e021eb18d8885108839fe77
- c37aaa5702f75169e2ce9de7a9fe109727efb3558d582352c2b97a3cca3564d8
- 32f60f4ff601a89d6ccfce6cd6af4b19cd606d2d2278b23903e049c429c8e056
- 53eccf073cb85d00623d1c708cc13fff995ec504fe89dfab59c56a782c18c409
- 08f3c988473aea98d4ca8ab627cd5e10f075455b5f6a538a13dc53871d29a04c
- 75430b8cd13f3974be5950f0a84bcf23b31d4199c17e729e804d9dddffbc8b3a
- 2d21f1034be1e02955c906251b147ec28974e1afff7982a956ac77e951c69642
- e45c52c8115e6d396504667f7dfda58c55760eced8847ad4938c77e6128323f8
- 70580a49df3be66fdb1a0a369f478660ea55bfb16800b1f2976731c4cb9549d8
- 57ed7d6ee9ae8b07783bd1df207521cf0f3e1365951c29ac04f1afc1d4f3c048
- bb2cac71f9c861e2554933876b45fdb7d143aa20ff78a2bb73565ff014d29fd5
- 01012f164c2570e656ea7c4b99b2b5a7845a77cefcab66b9d65e02da73821894
Coverage
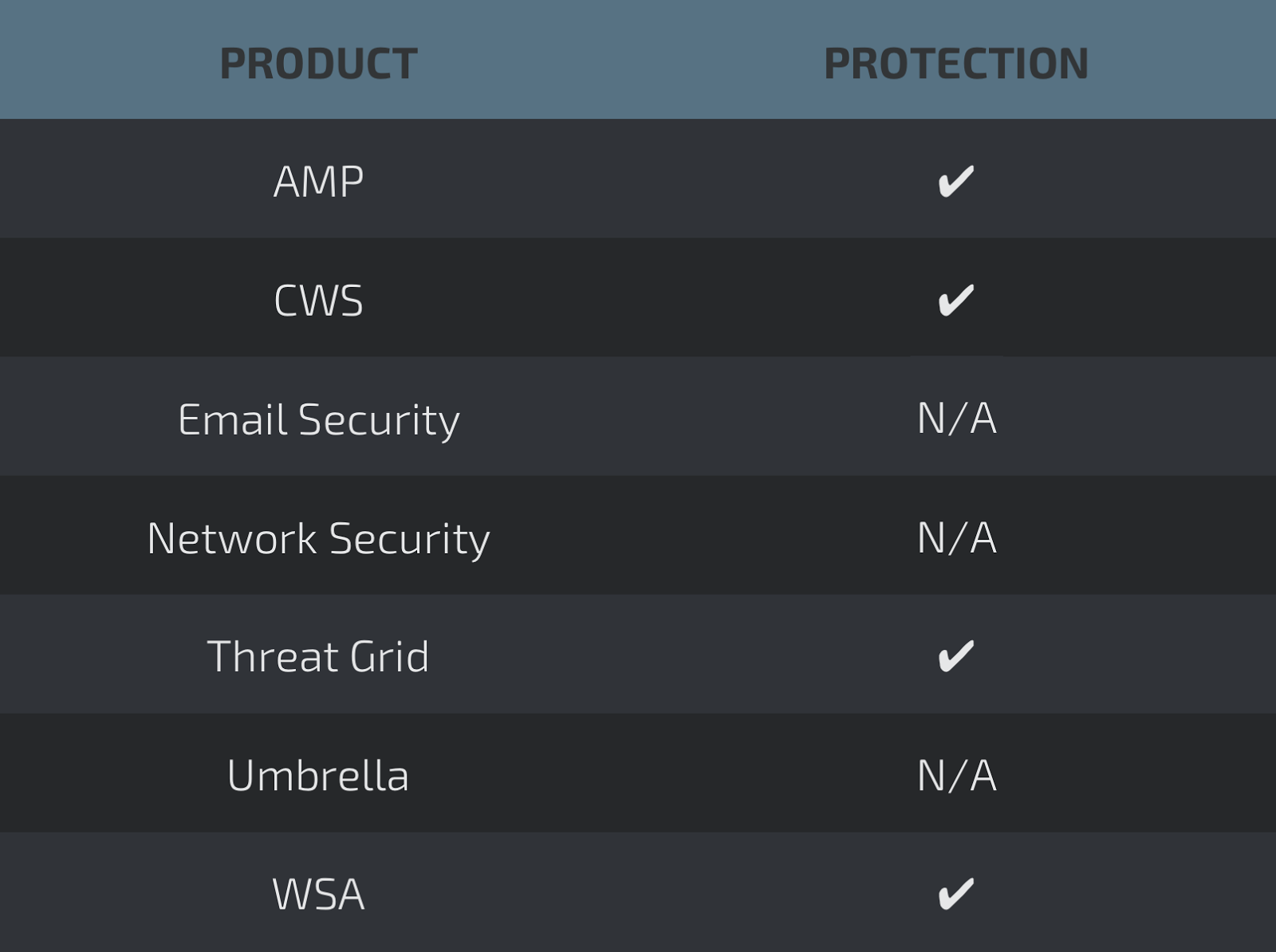
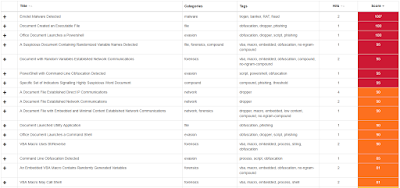
Screenshots of Detection AMP
ThreatGrid
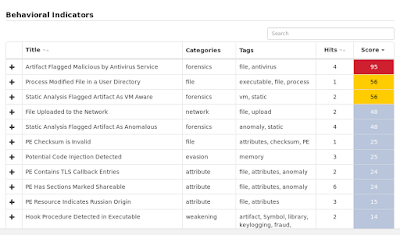
Win.Trojan.GenInjector
Indicators of Compromise
Registry Keys
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500_CLASSES\LOCAL SETTINGS\MUICACHE\3A\52C64B7E
- Value: LanguageList
- <HKU>\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections
- <HKLM>\SYSTEM\CONTROLSET001\CONTROL\NETWORK\{4D36E972-E325-11CE-BFC1-08002BE10318}\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}\CONNECTION
- Value: PnpInstanceID
- <HKLM>\������Њ�������ќ�э�����������э�В���������Г���Й��я��
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters Mutexes
- 3749282D282E1E80C56CAE5A IP Addresses
- 31[.]31[.]196[.]236 Domain Names
- u0417398[.]cp[.]regruhosting[.]ru Files and or directories created
- %SystemDrive%\DOCUME~1\ADMINI~1\LOCALS~1\Temp\284_appcompat.txt
- \TEMP\SOA October IN274348.exe
- %WinDir%\SoftwareDistribution\DataStore\DataStore.edb
- \EVENTLOG
- %WinDir%\WindowsUpdate.log
- %WinDir%\SoftwareDistribution\DataStore\Logs\tmp.edb
- %SystemDrive%\DOCUME~1\ADMINI~1\LOCALS~1\Temp\10B26.dmp File Hashes
- fb237b7fc75cec8180f4d853c44911dc0dbdb705be39c3e6f1f2a523b79ff9d5
- d90dc3f22cc7bd92f22bafa9d77b0e373849386eae57606b42239f915357084a
- e128f7ad54a882d2d269733a956f49e5b1bf2b182781f24f98f058f2d8f48787
- 021492b2cc3c242851207e402e9ba284ed32350379deac649f38426130b2c01f
- 2cd6fc2a4572f4b1a39371a8df8c664eabe119608908d441257e72eb203737f4
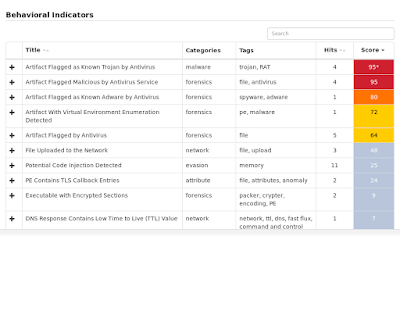
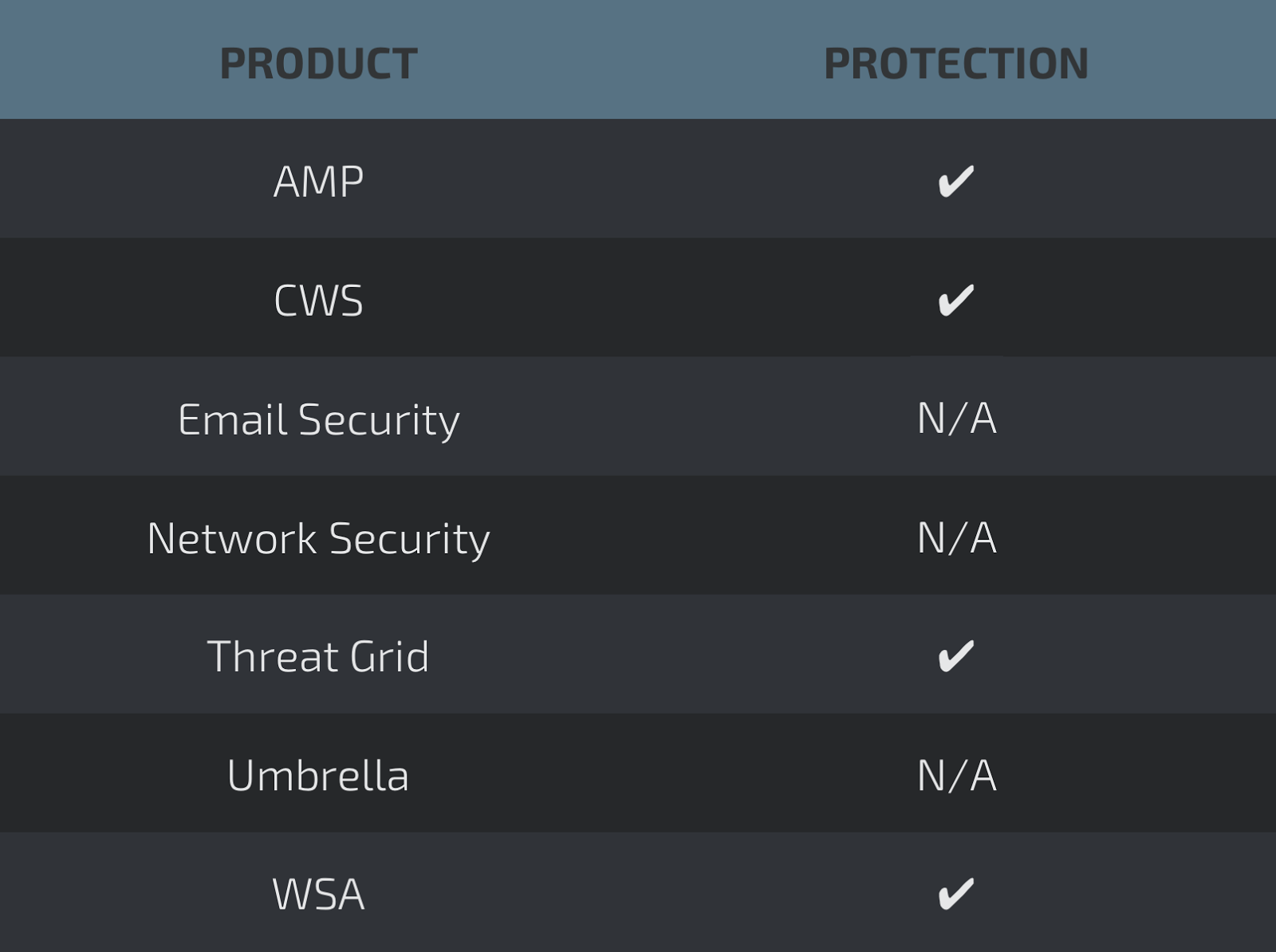
Coverage
Screenshots of Detection AMP
ThreatGrid

Umbrella

Win.Trojan.Zusy-6443152-0
Indicators of Compromise
Registry Keys
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value: svchost
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{5E197F8B-DAA2-BABD-EDBF-DEFDFDFEBEEB}
- Value: StubPath
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500\SOFTWARE\VB AND VBA PROGRAM SETTINGS\INSTALL\DATE
- Value: HFGW2HEVRP
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN
- Value: svchost
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value: svchost
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500\SOFTWARE\VB AND VBA PROGRAM SETTINGS\SRVID\ID
- Value: HFGW2HEVRP
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{5E197F8B-DAA2-BABD-EDBF-DEFDFDFEBEEB}
- Value: StubPath
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE\AUTHORIZEDAPPLICATIONS\LIST
- Value: C:\Users\Administrator\AppData\Roaming\svchost.exe
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE
- Value: DoNotAllowExceptions
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value: internat.exe
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE
- Value: DoNotAllowExceptions Mutexes
- N/A IP Addresses
- N/A Domain Names
- runeo[.]no-ip[.]info Files and or directories created
- %AppData%\mirc
- %AppData%\svchost.exe File Hashes
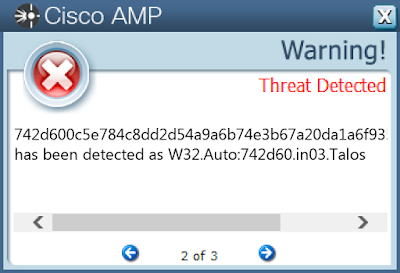
- 742d600c5e784c8dd2d54a9a6b74e3b67a20da1a6f9355511ff0c05ba48121c2
- 0328c4576287299e56877f254ea46a78f902c46fefef26c4bef7f2e9914ab378
- 07927ef357ebb94200b9ec784db1337f2a2012a9591bcdf2f27387e7992983ac
- 0e40b1eaf8bb90fbc2401ff200edbf7930957235af98d5c58ae7f1562d3a3d93
- 191281b087c742f6a99e05356bf0d8fd6e30340754c7b8ead6ae4051a595744e
- 217fd7e2bb21f0f0023f1c557bf29bd7578ea92159232e20d2d9cf34b6dfe976
- 219c813aa7aefc3db6d7de37898dfc9cb31a915f0c97d9ffd204b03df6598145
- 2d928287f5966bd08e8fba8e5682b6f0200ae92c560fd9f5b07eaf3301110417
- 3d9b06a7e27337026085feb880489db6fdf9d92eff63412385a784977825e165
- 4a6003e3c1930cd82f5be9f73b6b4554777ab453dd7783fb21cfd94478787ab1
- 4f318f15e17c6839069c53c5cc9594f50cc805867aa9d04df688daa10c55a28c
- 6e9516009a6da7c3247f058783b6515d66c11c440bd60394452112a28a815272
- 961af12739f5f34051d10edeefb90ba81d7509135de72c16fc8afefc28febdaf
- a45471269d4a0c4e4a2f207b1e69827a075ad171b30c7812e65ba1af15839d1d
- a7af202e3d506f9f52a3cec09238bc8aa8096611206807e2c3f2b17d7976db96
- ad47218986739e0072c91932f1d07a9f5f0ea7c98264978f57d0041f6100551e
- b067ecbfb6d02654c42fca66e4cf6dffe14a171a42807fd354f9cb7e7cba775b
- b8dbab7f7429309272e6608b9bae6bdc6ff75f95c130b93c78bb8a9b619a5cb6
- b9c2b5cc1df590e197d3df80584a8c077c2d68ef9aaea4888af8598541aec0f2
- bc61b85b359f344f7a00eae0d4015889fca2cdb623569fd25133400db2f2015a
- bdc949c5324235de7179b823d967220b3e92dcaaa21ee98ff452a3c80cd1c2c1
- be31db615f5a4aa48517252c57022a2fc9582f7740801e00bd8d7858d89b2bcb
- d4ff1da63afb7b0008d655bc2387f5f00452e920d6e253f23792f928ff6ac875
- e445e0d7f1a46b98400693a28c9ec427450abc8f29df4c145c1d860205dffa57
- e88b52ba0a0047a297855ce56115eacc07ea8b34a06900eef9890a577482ea7c
Coverage
Screenshots of Detection AMP
ThreatGrid