Today, Talos is publishing a glimpse into the most prevalent threats we've observed between February 9 and February 16. As with previous round-ups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavior characteristics, indicators of compromise, and how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of date of publication. Detection and coverage for the following threats is subject to updates pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this round up are:
- Win.Packer.VBashcan-6450053-1
Packer
VBashcan is a packer written in Visual Basic and has been used with trojans such as Umbra and Bozok. - Win.Ransomware.Gandcrab-6450061-1
Ransomware
Gandcrab is ransomware that encrypts documents, photos, databases and other important files, and adds the file extension ".GDCB". - Win.Ransomware.Godju-6450274-0
Trojan
This ransomware appends the extension "cypher" to the files and deletes them. It also creates a file called "encryption_key" in %AppData%. Like other ransomware families, it uses Tor for its command and control communications. - Win.Trojan.DNSLock-6449722-0
Trojan
This family changes the DNS settings and redirect traffic to malicious website as well as insert additional advertisements on the victim's browser. Moreover, it contacts domains to notify the infection and gets commands. The main process also attempts to inject code in another address space and executes PowerShell commands. - Win.Trojan.Generic-2-6449654-0
Trojan
Win.Trojan.Generic-2 is a malicious sample that can perform different nefarious actions. This sample steals passwords from web-browser password stores and exfiltrates them through a legitimate SMTP service. Note that this domain is listed in this report but our products do not block it since it is legitimately used by many users. - Win.Virus.VMProtBad-6450060-0
Virus
VMProtBad is a packed file infector, equipped to detect several VM environments. VMProtBad is known for installing web browser toolbars & generating unwanted ad traffic.
Threats
Win.Packer.VBashcan-6450053-1
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value: internat.exe
- <HKCU>\SOFTWARE\MICROSOFT\SLAYER616WASD
- Value: UID
- <HKU>\Software\Microsoft\Windows\CurrentVersion\Run
- <HKLM>\SOFTWARE\Microsoft\slayer616wasd
- <HKCU>\SOFTWARE\MICROSOFT\slayer616wasd Mutexes
- \BaseNamedObjects\slayer616wasd
- Local\ZonesCacheCounterMutex
- slayer616wasd
- DBWinMutex IP Addresses
- N/A Domain Names
- ilovetehpussay[.]host4star[.]com Files and or directories created
- %SystemDrive%\DOCUME~1\ADMINI~1\LOCALS~1\Temp\QGTPN.txt
- %AppData%\SystemWindows\WindowsService.exe
- %SystemDrive%\DOCUME~1\ADMINI~1\LOCALS~1\Temp\QGTPN.bat File Hashes
- 014cd0a944bebca326a3bb496667c29f5670858e67238ff4c074e789a07204d9
- 01cd6fc630c195ea59fb7755e530923f1cae383c57221a73bf3b6178e5d1a06d
- 0301c54ae3d98f0c84e03c6a64eced91f2b1130a861fd38cdd5488c25cc9844c
- 0333951a3a4d82639d620afbd43b2ba689970f68e29626ed15dcdbb2d7832829
- 03a5edbab584f197d5c6075fd2b825ad94fa8896988b1d3b77dce03aac586bfa
- 044898d63b8386f2d02ebbfd3f73997cf5731dfa1f3e27b55401e55901e512c6
- 048c444cf63f2afd1fdb07bc036141d93bb924f6abc1cbd39fb31fcaf2cef2b5
- 0515b6cb220f4db2154315eb57a8ca7703a481f5e5a9016a32cbae98425a4492
- 06a30d49fc05ef2cdbc4aed1db26020a7b1ec81a6b953f44e0c62d2a3e3e3531
- 07c5bea52f4e5a671b58b4061fc5721bb491682dafc25b06ef8692395d1012d1
- 07f21a783ce8944c9f0c40d9459a2ffdf7c15fc0c5ce0639584035655ebff7f0
- 0833aa53278f36a75131a2534db0d28bb833fa922579383e530469adb41d3478
- 08da00c849bd1aca5321e06f0e750e4d984f042d63f91db98b91f4967349b842
- 0cfc1788d54d5073d445cad67edf2ee76a9228f44734ed1341148b1cc82ee89b
- 16fc9a2c379c9e6664d668614a8e4df0f4c48170a9044288aab835c08fef5f0b
- 181dcac94cc3df4312a36af18a9d5ae0f25b5d718116d2b7af6f4d0aaa261c2c
- 1c2ab5729f056f3aa5f06c8cd342f7f543d3b30c1baf2ccd1dbdf5f15234d553
- 1d5173fee0e02d7df5c586871e0be2f30d7e88220d77bfb63caf505c1d671045
- 1da5e6084bd897b84b21b787b54f17a1b8cd88c388a13f3dcf9cec6395bb28a9
- 1f85629cd0d0b97d5a3372dd28062068e41bb8a74a70ab336dcf4ba8bb47b930
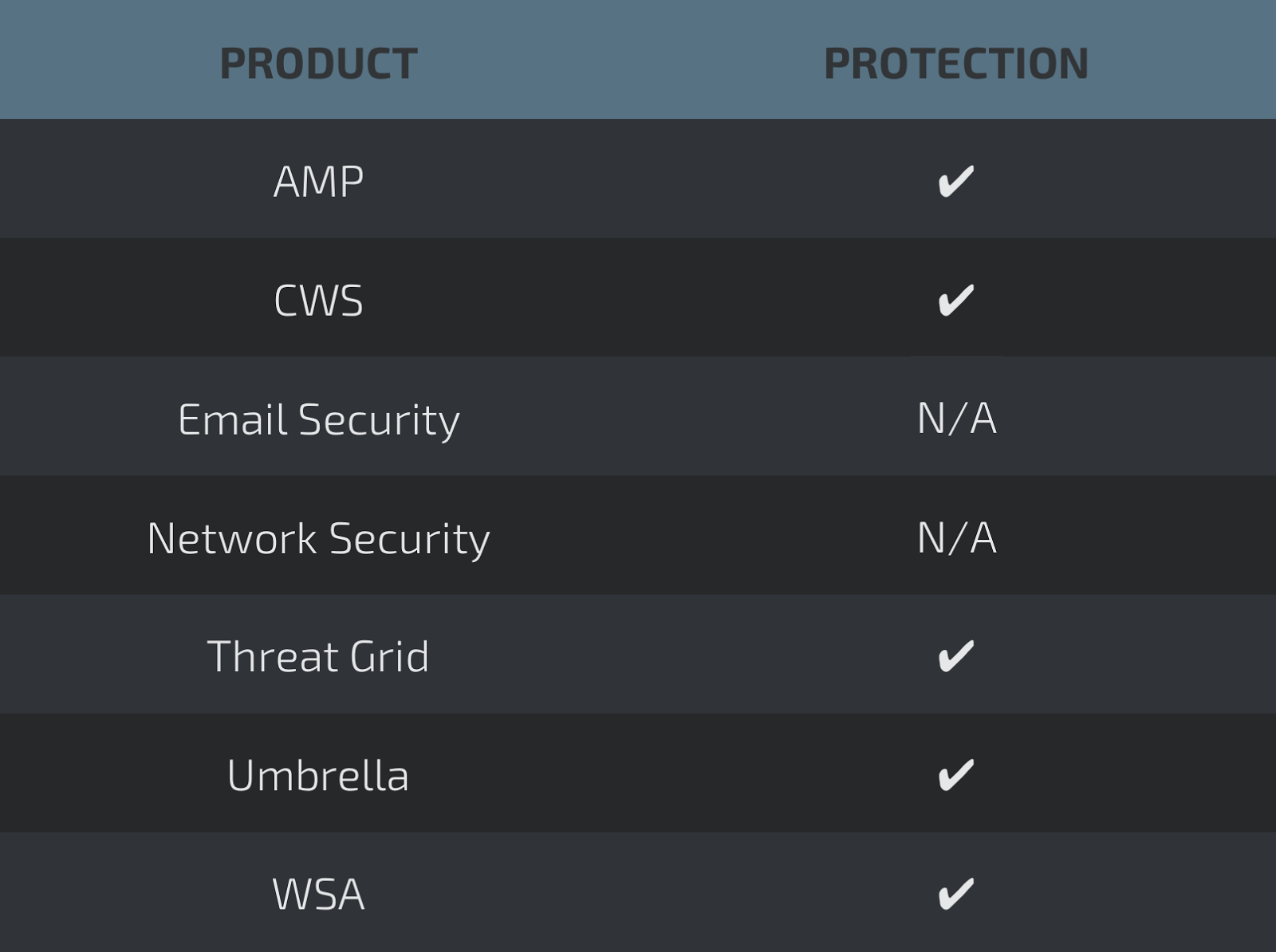
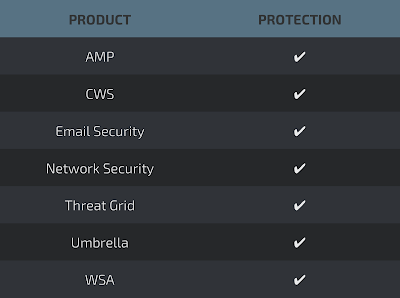
Coverage
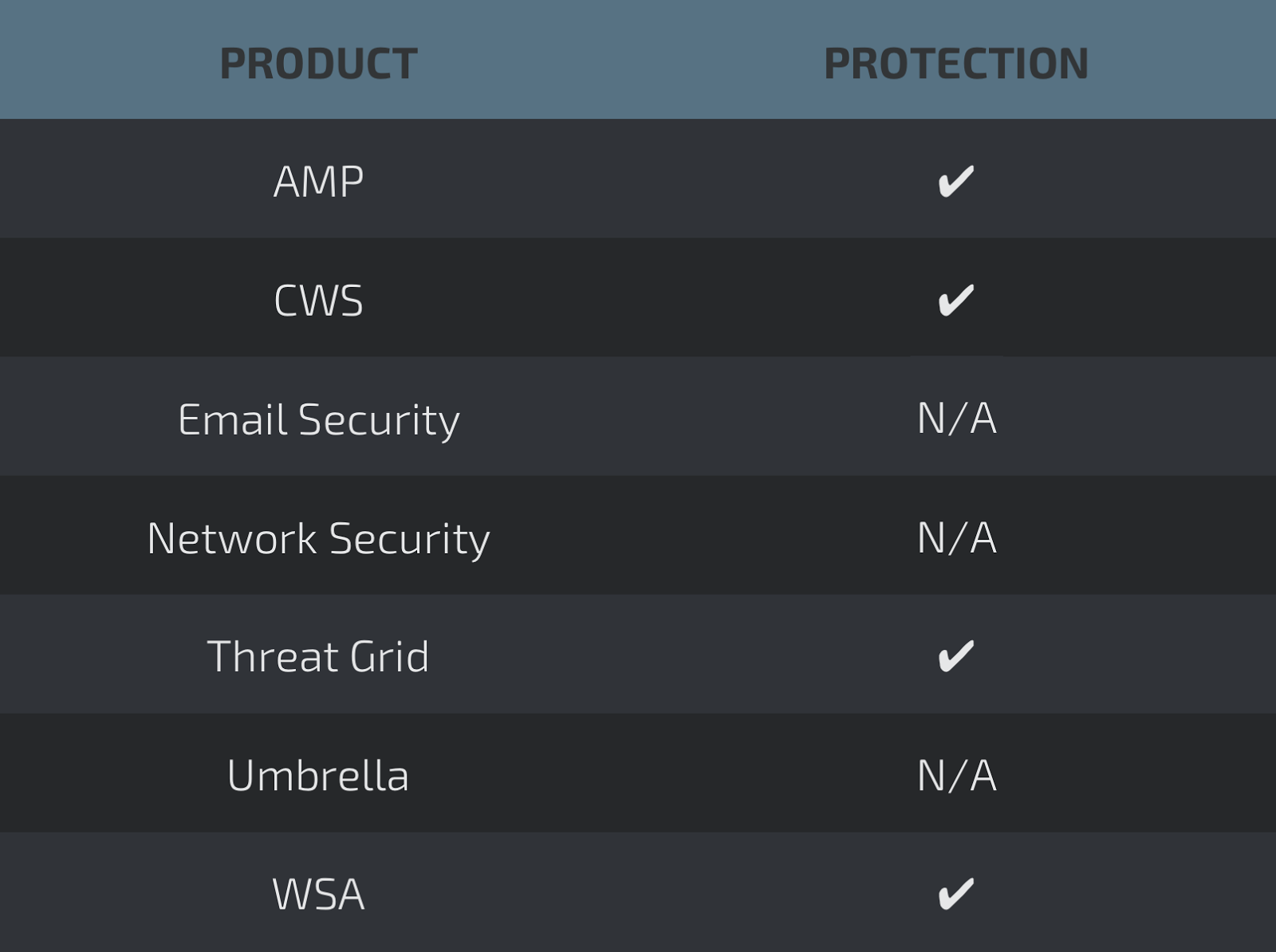
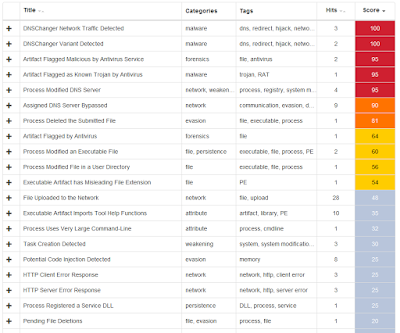
Screenshots of DetectionAMP
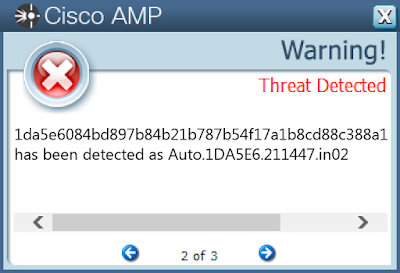
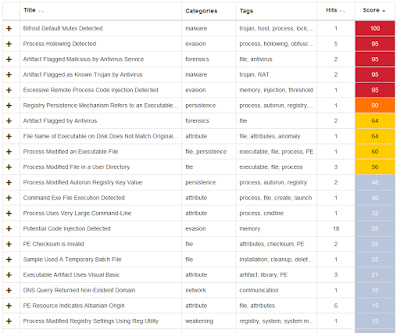
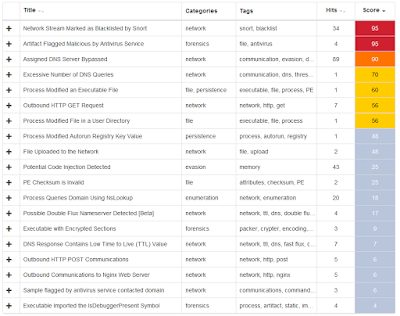
ThreatGrid
Win.Ransomware.Gandcrab-6450061-1
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
- Value: isnnswathsi
- <HKU>\Software\Microsoft\Windows\CurrentVersion\RunOnce Mutexes
- \BaseNamedObjects\Global\pc_group=WORKGROUP&ransom_id=359814f23c28b0e4
- Global\pc_group=WORKGROUP&ransom_id=4a6a799098b68e3c IP Addresses
- 95[.]142[.]39[.]101
- 66[.]171[.]248[.]178
- 193[.]0[.]179[.]152
- 94[.]103[.]82[.]89 Domain Names
- nomoreransom[.]bit
- nomoreransom[.]coin
- gandcrab[.]bit Files and or directories created
- \Win32Pipes.00000490.00000017
- %AppData%\Microsoft\bkxmfm.exe
- %AppData%\Microsoft\kqrnbq.exe File Hashes
- 022024c7db211df7da83d533d24c795eb4178f5a7b9a27acf752874bcdbd5477
- 02e90fb6cd303ebced661c5c7c9af249241835285e0e64b1092731485584ab8a
- 03c8bece3db3e2d6b26cc9769d2a694071117cbcf21830aa143507b03b402681
- 04ef7221209f5ea957312704743139e6000e24dc4399ccc46d5e102ecf2ab3db
- 052a7544e45619190ee911406cdaff1708951c9d0a4070a5f7a69cc541f2e558
- 0664a3cca1d5c0c9f2b7f0e6b2f0f20e99b3f902e98e9e709f0bb8ac1cadb867
- 075c9b925c8a0c5cea4d26b1f3c23666c99cede647c9769503f8e35a96c098b9
- 084d5c8161764da9af2b1dde0146a7f9b51491c562d8036aa28b85a4a1a32aaa
- 0a2ebbf4d5ba25049b8225cb253f7f99423b706f9a239c877595eaf696058f56
- 14426a13dc4620932fd0af40005fb3f508d6a6d69eca897ef5af4f58f7761d3c
- 15b3a69b86710122a8824ce17996c3301e96b1c629b7db3d9919012954903c85
- 15b705ee101e26b1ba39d62d6c816409e059f395de8a1a5bfdd35d0e20b705da
- 1bbee00688a4632749b40312e4109fdc58afa0b5a9e8603718d386fca095a015
- 1cbcecc05259b821d7d82f6b2e779de2f4d4dd1561445a213a91db8617e61c4c
- 1f941ec87c3d98827d051ae46d626702960a690bf1f62645828b0ea5cbd6c5ec
- 22ddc024bf53ae71ff42cb79564f1bf8c9eb4f59d7c2ce3bc378c70ce067b250
- 261fd62f71e3b566c8ae77e44760f0346c4f353a25f879ee5401e4755745ba10
- 289d660ede22b4062d102307d5830a2af10da669ce573c279db8e055e6fbdaaa
- 299edfd4bbf81f20fb8f8e2dd9d0fc4d26c925dbd1cf4372d9172bc2644d3ca5
- 29a86b3a5c2f1a7a5ad325ccf5c906b532bb2275b79071e2ec98a281a290aadb
Coverage
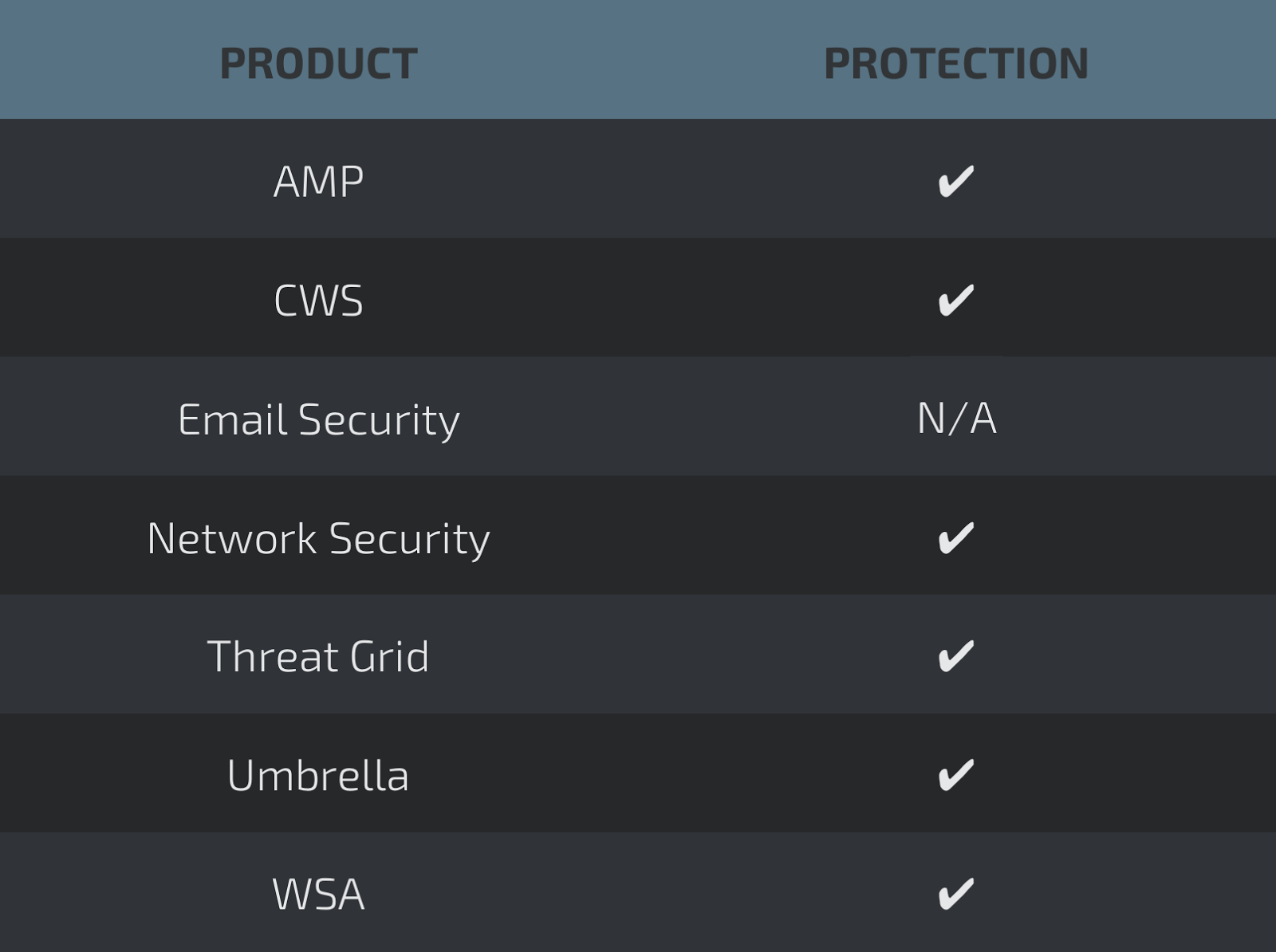
Screenshots of Detection AMP
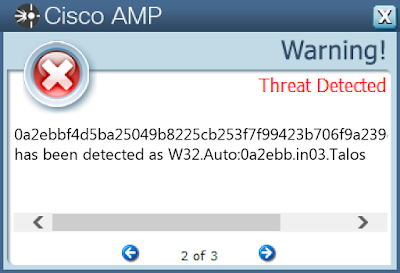
ThreatGrid
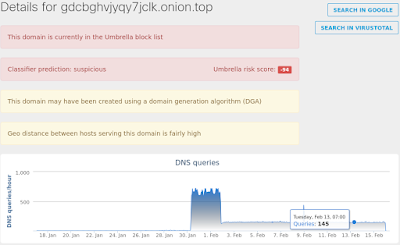
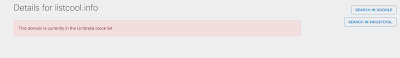
Umbrella
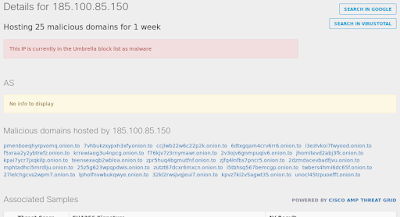
Win.Ransomware.Godju-6450274-0
Indicators of Compromise
Registry Keys
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500_CLASSES\LOCAL SETTINGS\MUICACHE\3A\52C64B7E
- Value: LanguageList
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500_CLASSES\LOCAL SETTINGS\MUICACHE\3A\52C64B7E
- Value: LanguageList
- <HKLM>\SYSTEM\CONTROLSET001\CONTROL\NETWORK\{4D36E972-E325-11CE-BFC1-08002BE10318}\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}\CONNECTION
- Value: PnpInstanceID Mutexes
- N/A IP Addresses
- 185[.]100[.]85[.]150 Domain Names
- kdvm5fd6tn6jsbwh[.]onion[.]to Files and or directories created
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I0Y9SM6.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I0Y9SM6.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I0ZU5JT.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I0ZU5JT.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I478AKJ.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I478AKJ.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4FI238.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4FI238.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4FKVBH.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4FKVBH.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4QK3KJ.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4QK3KJ.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I5QX7W9.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I5QX7W9.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I77RW1L.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I77RW1L.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I7J37KF.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I7J37KF.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I9NSD58.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I9NSD58.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IANXEE8.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IANXEE8.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IBC53OO.xml
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IBC53OO.xml.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IC5NB1M.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IC5NB1M.txt.cypher
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$ID60W3E.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$ID60W3E.txt.cypher
- %AppData%\encryption_key
- %AppData%\lock_file
- %AppData%\uuid_file File Hashes
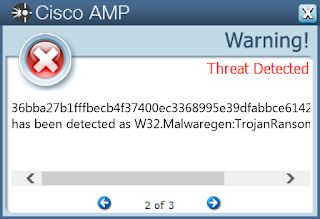
- 36bba27b1fffbecb4f37400ec3368995e39dfabbce61422531a55a36c7696c33
- 0622fcb172773d8939b451c43902095b0f91877ae05e562c60d0ca0c237a2e9c
- 412ce2fea4821c63074f3cd6223c9e9d7f074f18d5cd88dc1d7a36a1bb2f919c
- 4f888e9b613765653355f7dc2be015e7f32d677ae25fa7ff0298dc252339dce4
- 7005535e034576fdb66b5b32eb198b48d7755758e77bd66909f8dd7288c1e069
- 9690fec193714171652f8e0c7498d8ee3581fd0b074693a3a0ba07e5d95a141e
- 9a1794d3ae09b0a8c7a36fb27514760bb0227943d1ee37a7e81ffdfa9f36ec48
Coverage
Screenshots of Detection AMP
ThreatGrid

Umbrella
Win.Trojan.DNSLock-6449722-0
Indicators of Compromise
Registry Keys
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: AddressType
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: Lease
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpDomain
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: LeaseObtainedTime
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CERTIFICATES
- Value: 26D9E607FFF0C58C7844B47FF8B6E079E5A2220E
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NETBT\PARAMETERS\INTERFACES\TCPIP_{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpNameServerList
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{C2614C30-28EE-47BC-B044-C1025E72F15A}
- Value: Hash
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{553E2A9B-C5DC-4F54-9BDD-0DC2B010EC33}
- Value: DynamicInfo
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\43191B4E617CFE98
- Value: 1
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value: {BD2E97E1-0A85-204A-AB40-40B403D0844F}.job.fp
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{553E2A9B-C5DC-4F54-9BDD-0DC2B010EC33}
- Value: Hash
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\3013565826223049618
- Value: config
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{1C8E1F51-8675-4AF0-A985-1A0086FCB8EA}
- Value: Triggers
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\HANDSHAKE\{3B84A94B-68D0-41DF-9C58-9CD44ABFE648}
- Value: data
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{C2614C30-28EE-47BC-B044-C1025E72F15A}
- Value: DynamicInfo
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC\PARAMETERS\PORTKEYWORDS\DHCP
- Value: Collection
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\BITS
- Value: Start
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpNameServer
- <HKLM>\SYSTEM\CONTROLSET001\CONTROL\NETWORK\{4D36E972-E325-11CE-BFC1-08002BE10318}\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}\CONNECTION
- Value: PnpInstanceID
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\{B3797BAB}
- Value: nt
- <HKLM>\SYSTEM\CONTROLSET001\CONTROL\SESSION MANAGER
- Value: PendingFileRenameOperations
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CERTIFICATES\26D9E607FFF0C58C7844B47FF8B6E079E5A2220E
- Value: Blob
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS
- Value: NameServer
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{C2614C30-28EE-47BC-B044-C1025E72F15A}
- Value: Path
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value: {4797FAD9-D20B-54DC-98FE-7C614E1B1943}.job
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\3013565826223049618
- Value: rs
- <HKCU>\CONSOLE\%SYSTEMROOT%_SYSTEM32_SVCHOST.EXE
- Value: WindowPosition
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\{050B0847-7A0B-787D-0511-780E0C7E1109}
- Value: Index
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpInterfaceOptions
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS
- Value: DhcpNameServer
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\11598763487076930564
- Value: 0
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\3013565826223049618
- Value: rd
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{C2614C30-28EE-47BC-B044-C1025E72F15A}
- Value: Triggers
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: NameServer
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: T1
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{1C8E1F51-8675-4AF0-A985-1A0086FCB8EA}
- Value: Hash
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpSubnetMaskOpt
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DHCPNameServer
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\NETWORKLIST\NLA\CACHE\INTRANET
- Value: {9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{553E2A9B-C5DC-4F54-9BDD-0DC2B010EC33}
- Value: Path
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value: {4797FAD9-D20B-54DC-98FE-7C614E1B1943}.job.fp
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{1C8E1F51-8675-4AF0-A985-1A0086FCB8EA}
- Value: DynamicInfo
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\43191B4E617CFE98
- Value: 0
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpConnForceBroadcastFlag
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value: {050B0847-7A0B-787D-0511-780E0C7E1109}.job.fp
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpClassIdBin
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value: {BD2E97E1-0A85-204A-AB40-40B403D0844F}.job
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\{BD2E97E1-0A85-204A-AB40-40B403D0844F}
- Value: Id
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: IsServerNapAware
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\{B3797BAB}
- Value: 0
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\{4797FAD9-D20B-54DC-98FE-7C614E1B1943}
- Value: Index
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\{050B0847-7A0B-787D-0511-780E0C7E1109}
- Value: Id
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: LeaseTerminatesTime
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{1C8E1F51-8675-4AF0-A985-1A0086FCB8EA}
- Value: Path
- <HKCU>\CONSOLE\%SYSTEMROOT%_SYSTEM32_WINDOWSPOWERSHELL_V1.0_POWERSHELL.EXE
- Value: WindowPosition
- <HKLM>\SYSTEM\ControlSet001\Services\Tcpip\Parameters
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpServer
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: T2
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\{4797FAD9-D20B-54DC-98FE-7C614E1B1943}
- Value: Id
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value: {050B0847-7A0B-787D-0511-780E0C7E1109}.job
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS
- Value: DhcpDomain
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpIPAddress
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\{BD2E97E1-0A85-204A-AB40-40B403D0844F}
- Value: Index
- <HKU>\S-1-5-21-2580483871-590521980-3826313501-500_CLASSES\LOCAL SETTINGS\MUICACHE\3A\52C64B7E
- Value: LanguageList
- <HKCU>\CONSOLE\TASKENG.EXE
- Value: WindowPosition
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NETBT\PARAMETERS\INTERFACES\TCPIP_{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpNetbiosOptions
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\BITS
- Value: StateIndex
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\3013565826223049618
- Value: jc
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpSubnetMask
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS
- Value: DHCPNameServer
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NETBT\PARAMETERS
- Value: DhcpScopeID
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{553E2A9B-C5DC-4F54-9BDD-0DC2B010EC33}
- Value: Triggers
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- Value: DhcpDefaultGateway
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\AUTHROOT\CTLs
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\AUTHROOT\CRLs
- <HKLM>\System\CurrentControlSet\Control\Session Manager
- <HKLM>\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\3013565826223049618
- <HKLM>\SOFTWARE\Wow6432Node\Policies\Microsoft\Windows\BITS
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters
- <HKLM>\Software\Wow6432Node\Microsoft\SystemCertificates\AuthRoot
- <HKLM>\SYSTEM\ControlSet001\services\NetBT
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CTLs
- <HKLM>\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{b3797bab}
- <HKLM>\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{29017980}
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\Certificates
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\Interfaces
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\HANDSHAKE\{3B84A94B-68D0-41DF-9C58-9CD44ABFE648}
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\AUTHROOT\Certificates
- <HKU>\Console\%SystemRoot%_System32_WindowsPowerShell_v1.0_powershell.exe
- <HKCU>\Console\%SystemRoot%_System32_svchost.exe
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CERTIFICATES\26D9E607FFF0C58C7844B47FF8B6E079E5A2220E
- <HKU>\Console\%SystemRoot%_System32_svchost.exe
- <HKLM>\SYSTEM\ControlSet001\Control\Session Manager
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TCPIP\PARAMETERS\INTERFACES\{9EB90D23-C5F9-4104-85A8-47DD7F6C4070}
- <HKLM>\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\15233773854796355610
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\NETWORKLIST\NLA\CACHE\Intranet
- <HKLM>\Software\Wow6432Node\Microsoft\SystemCertificates\ROOT
- <HKCU>\Console\%SystemRoot%_System32_WindowsPowerShell_v1.0_powershell.exe
- <HKLM>\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\11598763487076930564
- <HKLM>\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\6aead233391fa002
- <HKLM>\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\26D9E607FFF0C58C7844B47FF8B6E079E5A2220E
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\NETWORKLIST\NLA\CACHE\INTRANET\
- <HKCU>\Console\taskeng.exe
- <HKU>\Console\taskeng.exe
- <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CRLs Mutexes
- X29d2562703480b92 IP Addresses
- 54[.]236[.]192[.]172
- 81[.]171[.]14[.]67
- 52[.]77[.]199[.]193
- 52[.]206[.]149[.]50
- 18[.]220[.]249[.]233
- 82[.]163[.]143[.]176 Domain Names
- zambi[.]info
- amous[.]net
- listcool[.]info
- monoset[.]info
- riyah[.]net
- dyn[.]com
- listcool[.]net
- www[.]hostgator[.]com
- dynarunner[.]info
- passportinfo[.]info
- bubblesetter[.]info
- hostgator[.]com Files and or directories created
- %AppData%\{39C4A9FA-8E6F-1E51-87DB-35E186454CDD}\B063E134-07C8-569F-D402-4219FE2A8B75.exe
- %System32%\Tasks\{050B0847-7A0B-787D-0511-780E0C7E1109}
- %System32%\Tasks\{BD2E97E1-0A85-204A-AB40-40B403D0844F}
- %WinDir%\Tasks\{ED590CE3-5AF2-BB48-A127-A8DCDA9B22BE}.job
- %AllUsersProfile%\617cfe98-5007-0\BITBA2F.tmp
- %SystemDrive%\DOCUME~1\ADMINI~1\LOCALS~1\Temp\72909457.t.exe
- %AllUsersProfile%\{BB098D39-0CA2-3A92-C225-C429A39F94EC}\61CC9F6E-D667-28C5-AA39-29C86F125189.exe
- %AllUsersProfile%\b3797bab\9c3ac369.dll
- %AllUsersProfile%\{37454187-212c-0}\BITA113.tmp
- %WinDir%\AppCompat\Programs\RecentFileCache.bcf
- %AllUsersProfile%\{769e331d-612c-1}\BITA0B4.tmp
- %AppData%\29017980\2fff851b.dll
- %System32%\Tasks\{4797FAD9-D20B-54DC-98FE-7C614E1B1943}
- %WinDir%\Tasks\{780B0A47-790C-7D0A-0F11-080D7808110D}.job
- %System32%\config\TxR\{016888cc-6c6f-11de-8d1d-001e0bcde3ec}.TxR.blf
- %TEMP%\{006714f4}
- %WinDir%\Tasks\{67D0E6A3-41D4-1B09-02A0-1F3933D2EA6A}.job File Hashes
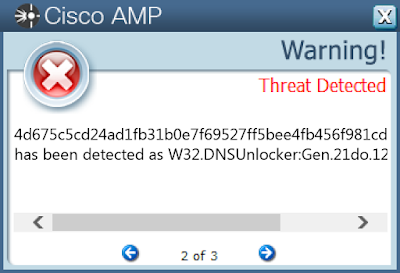
- 4d675c5cd24ad1fb31b0e7f69527ff5bee4fb456f981cd71423bc967af6eed38
- 1886e03f7c9fa7160333467eb61afd49521477c246db67a4cd77eb328315bbe7
- b0c8ca8e4d3ecaa3f77760b7e7cac04185a96ed9001b563f969b8f24378da737
- 99b86f98266db8238315609f850af04f32967782f78470ab655217da79ade490
- bb448628a9c7f39f1704705c8bd27bf3b01ecca76ad1e540e511dbd72c520ae3
- 1749e2cac4f7c526e1dc32f0e96093cc823c581954e25ace5a479f1e19ef222d
- f9e0b981c4e51303f4b6f0199222e95b1d9a822dcf28f6d8ed27733d70e5448d
- e59262af5fa77645cb9c081efd5c9f95dc929a5211624528289413bdf21e86b1
- 871a9d8a090dc17a0f7f49e2aa382aadf7633530c53b4b9e77318d0dc7464d6b
- e802bb930657a5fad11f6f493f081f11c12b88859037636ab6aa5595af53a371
Coverage
Screenshots of Detection AMP
ThreatGrid
Umbrella
Win.Trojan.Generic-2-6449654-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
- 173[.]194[.]175[.]108
- 173[.]194[.]175[.]109 Domain Names
- smtp[.]gmail[.]com Files and or directories created
- N/A File Hashes
- 41d52ddff7d3b2135ba379f7988aba7ae535dc7e628f450aff841503b020efc4
- 63695a0a294612e6666006283c90fd86f64eff0f244cf559bdf488f2e4193041
- 69c10d78fd6a4accfd7533cab25068fc85113431445227ad9847ec3ca42f949b
- 75818e658a9a4b02897a5808a2ccea33cdb7afe8c6827b13b2b4e8805de1ce2b
- 787de9917c7871afb7c5b13ed54adc98a0b1507d104ccd25ef8573740ae08919
- 7ee01720f1c00dc3ed39d6cccc1a99cfb6f5d249f0df24a4669f2f729f9d8c31
- 93685a69cb9a78b6b86bfce0250019f8c08c6ee429b4effa895d1d84da2c0d0d
- aed337b11888de4ec146551c1bcae46e62c3d14b20e7387ed72d0f72bbe49c61
- b16228fa8feae74e5e751110b23ebb1c6aacc36cb6f2511d7e38f55c40703fd0
- ce510906b105627044b9f35845e75897f94f6530dcc1155eae1b1eb2edd49c4f
- d3a8088cd1796240c66110bc6fd964abac305d77071bda7f9040c88a45f6965e
- d48fd05d443a1552e6affab7cfc65eb7d804a0ebe80f4b7056b8685dd9e9c70a
- f3c143fe7856d71ea5a91c2d8bb96ddd4cb3c4c3dc7898d766be716cb4852da6
- f9ec96f821fe757421b1934675cce312e2bf42df4446416bcd0908653af7415d
Coverage
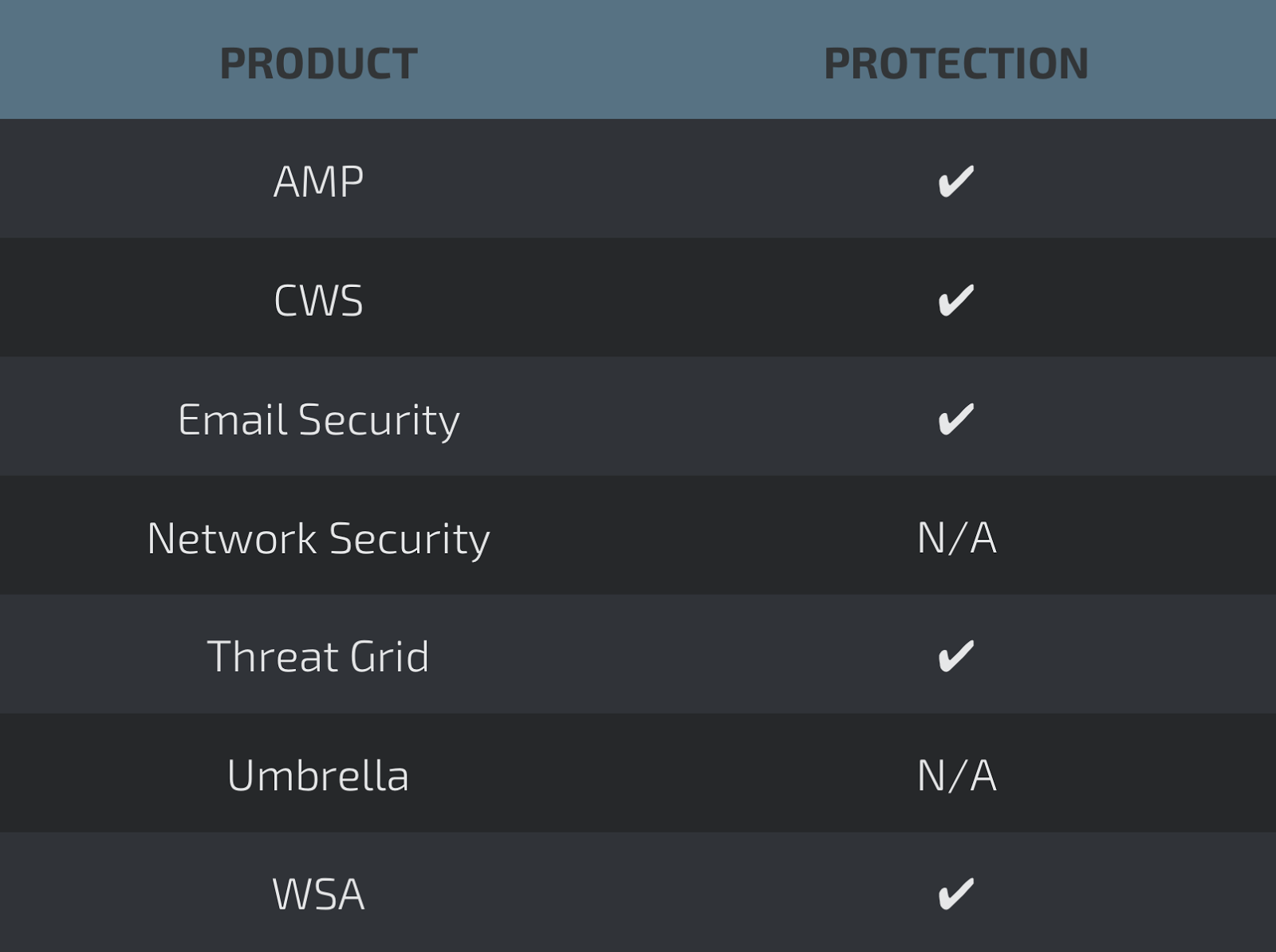
Screenshots of Detection AMP
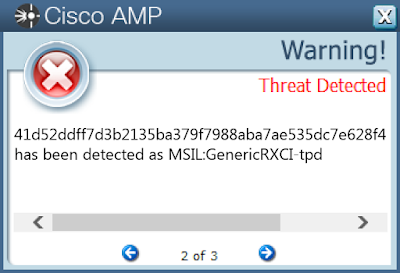
ThreatGrid
Win.Virus.VMProtBad-6450060-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
- N/A Domain Names
- N/A Files and or directories created
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$RUI79S5.html
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$RANXEE8.txt
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IDBK7UZ.html
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$R9SCMWR.lnk
- \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$R7QS1I3.lnk File Hashes
- 66c9cd00579297128b36295f8c13cffb5a6d805f73e3086cabceaedfb361c37c
- 8ee03ed6082b418b4ea91cc8e63848ac8113ed29c65ec9e3403e8f1f90c41b4a
- a6660d922577539a08e5dc02984affea031b7bfea22b6bba53113fe2177fab06
- 7312bd55e79b5813ae8b064e0f1bc11592a79494a79e854626391e26dd2b6b7e
- a4cc65474efd0b0e3aeaee8614b397dbc9bd3ecf7a95a8526d8ac84ed3848ee4
- 4e2624a133a42107d3def6ae7ffcb5e1a5c372ca2d8638438a03a4a040802517
- b2e43a6ac8301d5304715b8528c40da58c5e2f473995738178d9f5444d52785a
- 135f254c202229f708d7e4d0eb36d4d14ed8b43029b994a0401327efb9f63461
- f9225972bdc9d23e545a4f530f79760913eba49f8a78e53fc6b361cee499547e
- 246569246bb8a4694f7b48e9c7abdc6e732b7e1c73b2c802c045d5cda03ef3da
- 67694e083c8b54090afe2a580da0242d9d05746953832b34af1c11290efe544e
- ecb1e4e860ea7612793420677588c7411fc5717825470c956f1e21c30b5325d6
- 59880ac464244c14deea6569d4d79377fec91f63b7951f137bd457985528f3f7
- e70aa134607b6e5c85dad94749e382afd11052d789dad93027756a8ad9c1b5cf
- fd7fe9120abfd3da2124357680acaf010d1768fdaa570e471b30207a4e8d9dae
- 28d599079555f858bb7496dc8fe8fec7fb450aa083f039e90a1c9e11ed7d9094
- 2e20f3dc237275d5579b96c46195aa05f79b206a356918a0e1bc990a42979111
- aeab4107c498f7ebb963452b3157c70fa36f7c0c6936067b89d6d2f2fdd7dd09
- c55447abc07f82e59c4573b50038117d494bc8069bd868e2f4755cea405ec104
- 81e852b22956bea616f384424f2ccbc60224bd497e0885b3472e1019ecd941aa
- 5aad686faa09afc69b067b67cb3db992820f96d3cadb5e160878255510194dc5
- 09c953e9fcc681daee3f311513308988048049bc687f3d10d9ae4e6462cdd4b8
- 0507d30d8ae08a46acbfd85e6c945530505509df8b4658a5d7b846c8eec51d0a
- e8e31878a125c47e835ceea2f783fe7938bc9882869a98d9d2cb67c756c8cf97
- 0412d1da28e300a2677e46ea1af64d664ee47f845336d1081d15df58d3e9016a
Coverage
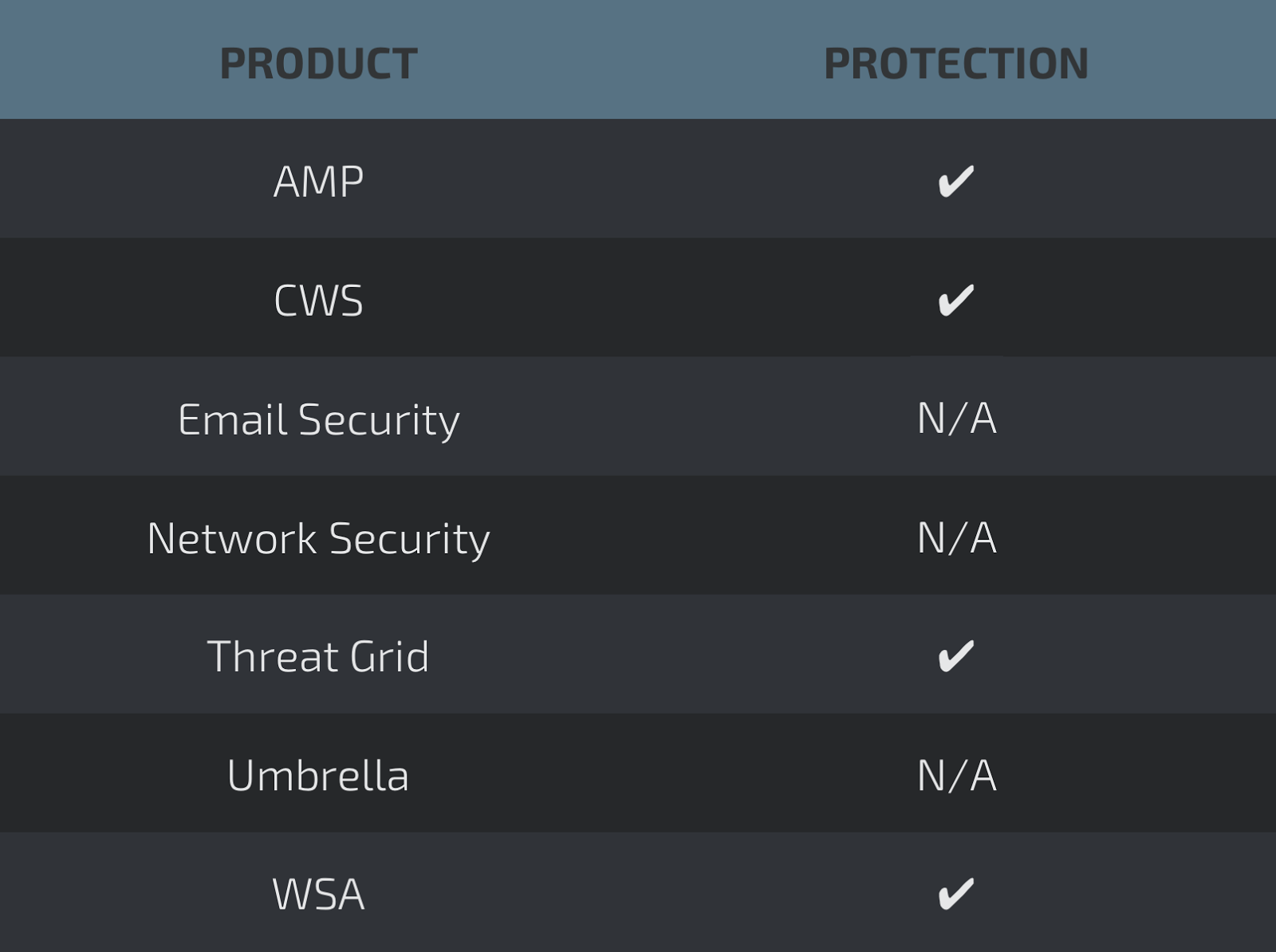
Screenshots of Detection AMP
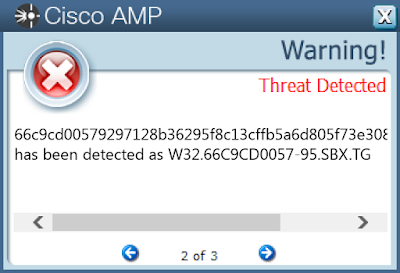
ThreatGrid
