Today, Talos is publishing a glimpse into the most prevalent threats we've observed between June 22 and June 29. As with previous round-ups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this round up are:
- Win.Trojan.Remcos-6591502-0
Trojan
Remcos is a commercial RAT but it is also available for free with few functionalities. It can be configured to have anti-vm checks and hinder the analysis. This family is able to receive and execute commands from a C&C server. The commands may activate and record the microphone and the camera as well as the keylogger functionality. Remcos is spread with aggressive spam campaigns and by leveraging Word/Excel macros. - Win.Malware.Separ-6591487-0
Malware
This family is a spyware delivered via spam campaigns. The malware survives reboots and is able to collect confidential information by capturing login attempts. It disables the Windows firewall and it invokes scripts and has also FTP functionalities to upload the collected data. - Win.Malware.Tspy-6591475-0
Malware
Tspy family is a malware with several functionalities. It is able to execute itself after every reboot and in this way it is persistent. It contacts domains that are related to RATs and are generally C&C servers to upload data and receives additional commands. The samples are often packed and contain anti-debug tricks to complicate the manual analysis. - Win.Malware.Jaik-6591471-0
Malware
Jaik is a botnet with several functionalities. The samples are able to communicate with domains and perform code injection into other processes. The malware has many features and some samples have also DDoS capabilities as well as generic credential harvesting. - Win.Malware.Delf-6591417-0
Malware
This family is a generic malware and it is generally the first step of a more deep infection. The payload once executed on the machine downloads and runs new binaries. The malware is interested in credentials and focus its attention on well known applications such as Outlook, Thunderbird, Firefox etc. - Win.Malware.Ursu-6591377-0
Malware
Ursu is a generic malware and it has many functionalities. It contacts and C&C server and performs code injection in the address space of legitimate processes. It is able to achieve persistence as well as to collect confidential data. It is spread by email.
Threats
Win.Trojan.Remcos-6591502-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
- N/A Domain Names
- N/AFiles and or directories created
- %WinDir%\ServiceProfiles\LocalService\AppData\Local\lastalive0.dat
- %System32%\winevt\Logs\Windows PowerShell.evtx File Hashes
- 0007bb868ae54ff5be81cf04d7ff4c38c1d36ee18fbc3ee166d1f6298b8e4176
- 00171a400fb86b6f6489875fdf65079b765255e2240c30f174b1f9aff6a17dac
- 04bb108e21aaa1b3832e2ff483237559c02dda2ddfc03e2b56e7bc818614d0e4
- 074dcfd66274bec7d3ac3e23fd77d21baca17efa497eb94d748e46add97e8c27
- 07b31ec3eabb4967f7ed54d437de2d4a3e9271810f4f9c2b238bb6ba7829f180
- 0913592e52b43087d0f2a23700e5c625c0cdd4d391354233dc692a5477416ca9
- 094e5d7bce863dcf7652873c15d18dfce918eca631c471bbe59f739fccb770c8
- 09a7a2aeb1af80aa666c5920765e4409e367a051c161d948f1a193adbe5040a3
- 0e953857e78b91fa30011d345fccf6f86a8697318935b227d69ac4dd4915889b
- 10173267784ffb1934d59ce8bd822f9f9260bbc7420eeafd0c8affa8a62e840b
- 1323533b1caa1537b50c0ddb43b5f692901d2bb3b38f11e0fb380d72149ef53d
- 13aeccc984e1570bf36d8440df9b293277b25f26bb299179d187ac47b3500488
- 13fbdc096406f0f975d02a160448d98fd9d49d3ce7d338151668001017dbe397
- 144b7841ed6f8181b99e6be48533a77db7ec1183cd3700fecda0cfdc4b5bf3bb
- 1623edf8271a3a77d74658adcf67d5f99f6102bf178c0665dd68bc932b0c1228
- 192f60438d4707d0edb60c2ab1b69df72943b7812bd77bb393182db0636be982
- 1a6c169c82fd99a1b607100c42cae0c39f964ea2dbe6e0216479171d479275df
- 297ce1753eb30ecc82b016aac7ab694eb0bd4ded06fdecc5cd42a2464e4831db
- 2a0d2df8c466bbe5bf538e9745286f124f3ca426d3ece80fbb675863281c46a5
- 2a4a9722a20800038438c88d240083b65c729004d30e0c993f67202541f60811
- 2a67165161c7cbeed1fb43aa27b770b627b0eabe7a647387382fa4cff0acbaa3
- 2bbed3835b0efc4efe05d8fc806ab9fa5313202d566d18060542d23a3cb80fed
- 2d834a721aa72e59378d795f16b179e6cc8fc0040441d72b293f19d863cd22ad
- 318d9318e4e204f378f8ffeb7d831a6f251d6ca4e827f8e48449be0812e2cb25
- 31aa91dfa01203239b8aa25649c05a084e62de8814e101c24f3fbd5f2d234014
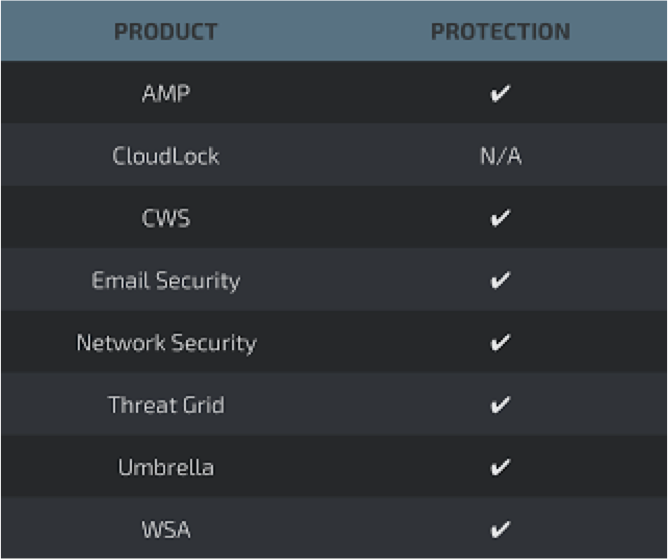
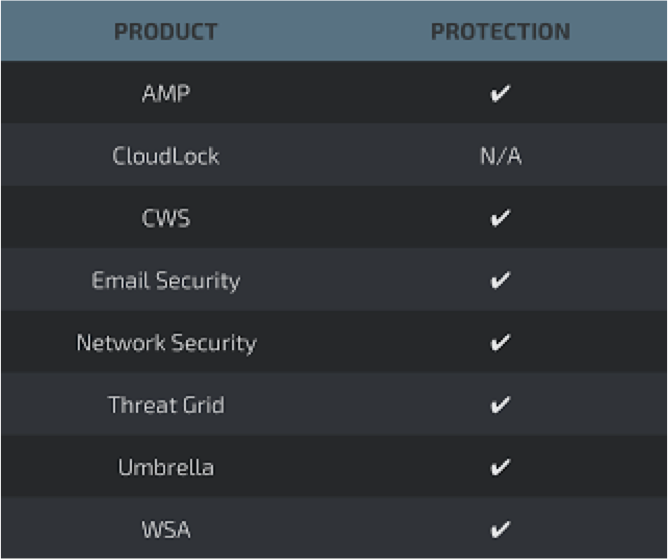
Coverage

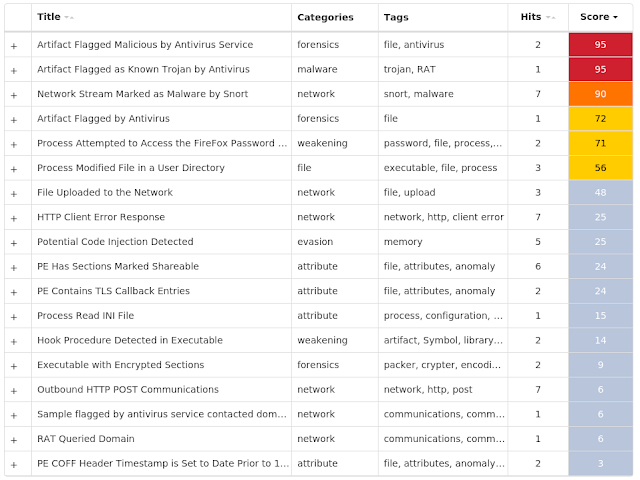
Screenshots of Detection AMP
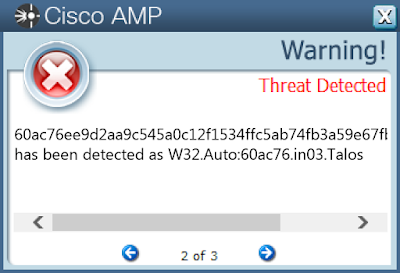
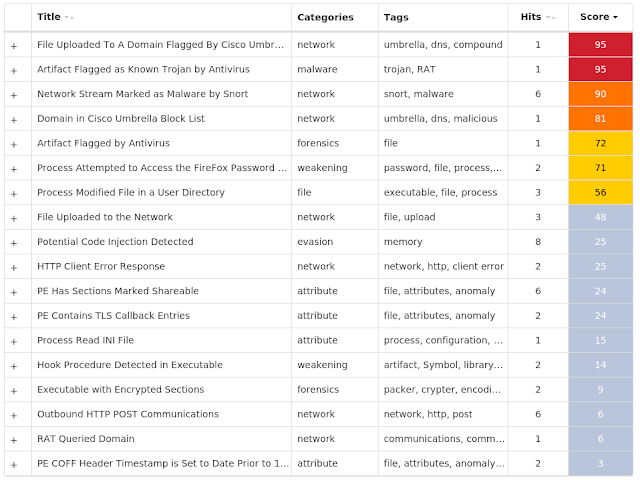
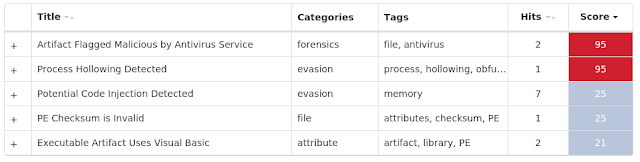
ThreatGrid
Win.Malware.Separ-6591487-0
Indicators of Compromise
Registry Keys
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters
- <HKLM>\System\CurrentControlSet\Services\NapAgent\LocalConfig
- <HKLM>\System\CurrentControlSet\Control\DeviceClasses
- <HKLM>\Software\Wow6432Node\Microsoft\Windows Script Host\Settings
- <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EVENTLOG\APPLICATION\CHROME
- Value Name: CategoryCount Mutexes
- RasPbFile
- DILLOOEP
- DILLOCREATE
- RAL716BCAD1
- Global\GS-1-5-21-2580483871-590521980-3826313501-500{D19BAF17-7C87-467E-8D63-6C4B1C836373}
- Global\G{D19BAF17-7C87-467E-8D63-6C4B1C836373} IP Addresses
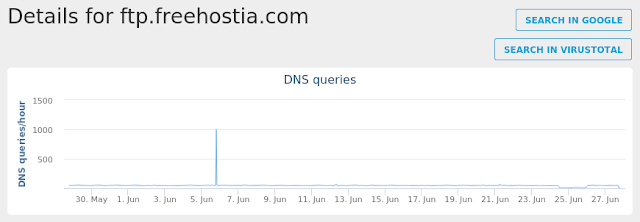
- 198.23.57.8 Domain Names
- ftp.freehostia.com Files and or directories created
- ZREA.vbs
- \wkssvc
- BReader.exe
- aijw01.bat
- Adobeta.exe
- adip2.klc
- adbr02.ght
- adbr01.ght
- 870.afr
- %WinDir%\TEMP\gui9381.tmp
- %WinDir%\Temp\gui9381.tmp
- %WinDir%\TEMP\Crashpad\settings.dat
- %WinDir%\TEMP\Crashpad\reports
- %WinDir%\TEMP\Crashpad\metadata
- PSTools\PsExec.exe
- \scripts\PSTools\PsExec.exe
- sendemail\sendEmail.exe
- sendemail\sendEmail.pl File Hashes
- 0426b3265ac921a904ba9a2a4e23bf86c18863bd020f1b50b4b1f85eafed66c4
- 09ebe700700a0e5e49d994093786f6c1bc9d3c400edc94b31693ef5961250d81
- 12e2ba4b4a310edf9cd97405541565e20d9ea6259d86d96a36fc8b676babb228
- 14c4a3fd18cad81c55ff4aa192803b748d8810900602c89c26114eb80c9db988
- 21d006b8f12a6b2e3126f3a6cef4f621c314a9dc21be6ffe51950f816f6a88c9
- 306d1f5e2b8292344d86d611dff2704920fa44ddd6fdc0b67a3e7e0f34d29d18
- 354cf3031b2679f885969746afef780bb1765b0f32613afb6490d5e60b7fe6bc
- 3ef31d4a0bccee0994a4ee525b679da1fd2664f3d96d20371297f6f6645a2ced
- 3f735ba16d51af841f5a48c9be5a2cb004df275c71cbbdd3497bfe34460f9c93
- 403d91b31d44acb4a67b5b0dd7679971bedc722244f1b705adfa095632d18cf3
- 4f7b768262e30ac52c97566a03646de84081ea148c932aedb84ca5bb46a10da0
- 5b4afe3563869522e85cfab2ae3d2e57a55f98a9c565c915dac81aaa0282deb4
- 61540809d55eaa23ba0ac82ff4b530823c93fbc8e7097ccaeb8329e0eb1e48c1
- 64a76e220bdff00633c5cd8e0282ec61836a60cf6b2f9f1b135ce3a3b040ca52
- 675402f0a4a31c59011e4356207a3189b171f0dd81b0117adf59e6e120b90295
- 6d7019e4f1e02713046fedb121d15c9a423b8502e792ff42c7896c3b4d9f826d
- 6df2b4fc352d822b4df9c164e7282fe387adc6ab0b7e036a12f4c3c57641564d
- 6f13c5e83ae42cbb755a44c3c45075043983d0eba2846b63442471577bdf6a98
- 70a30928df9e590846105947070d1fde660aa4bb933e0468713a89960c587a9f
- 7115ea1ab97a7187b2a1bb6936fe3df44bc754ec06f70c9f880d9787e605ea60
- 79789706985bcb5afeffed63805994cbe09966da0544e18a0a059a57064d7039
- 7e4ed04b95f0b07272223308b8e49db2fd64b144db28d5322b51ae879f58f8aa
- 7eefcb90a82546e4b71895a11a95a8dc38f49fe4713fa7d7a52ec68f511533cd
- 81ca06e244e541b585ff763df011560dc2b58eb7ea434eeef74439ca8bfd01b2
- 82a5963922e08c70521648fbec9849f621bfd0d25b0d6193b1e9a39ecab05111
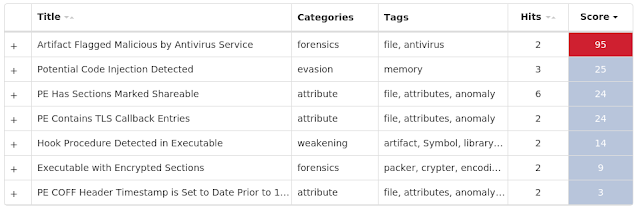
Coverage

Screenshots of Detection AMP
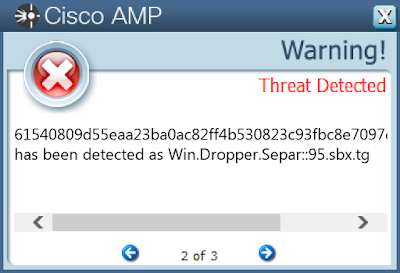
ThreatGrid
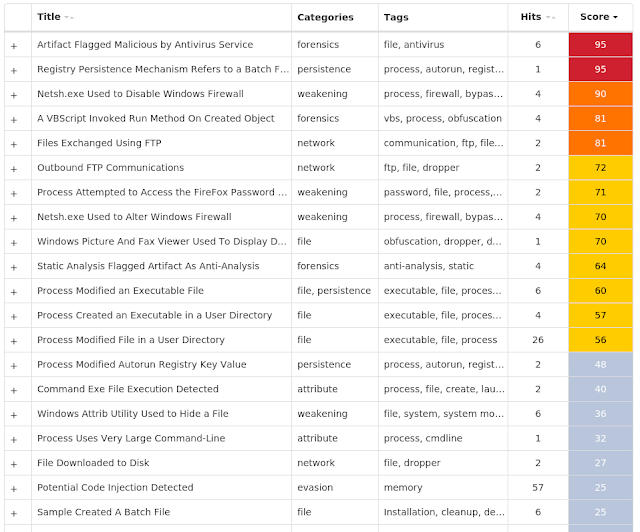
Umbrella
Win.Malware.Tspy-6591475-0
Indicators of Compromise
Registry Keys
- <HKLM>\SOFTWARE\MICROSOFT\RAS AUTODIAL\Default Mutexes
- 3749282D282E1E80C56CAE5A IP Addresses
- 207.174.215.154 Domain Names
- azmiry.com Files and or directories created
- \samr
- %WinDir%\ServiceProfiles\LocalService\AppData\Local\lastalive1.dat
- \lsass
- %AppData%\D282E1\1E80C5.lck
- %AppData%\D282E1\1E80C5.lck File Hashes
- 05a6a94d66a8b222553c9210b4e370d02a6fffe8ee49be8142d75dd37c5c7fab
- 0f11515c0a57068b0636a8a4283b8e25bf7c72fe55c486fc108a8cbf02b50c41
- 16ae2ef60aad481f1a340a9e6e7421258a57e7cbba46d9dca8c1dc063a699ef3
- 19c97ae2501ccebf5e2e4e5f88d3323141aeca73e9016d69eacc11f79fd4e803
- 1d8cda39dcf193f04d41ca364e038ddf7ae51ff5cabc56c687a38c41773b5d95
- 2ec87871a0a83639fc814ab764d69147f2dccc13cdcd6dd6af4a9aaaebdb5283
- 3651567230a6f02d69659133e1e915d87903994f20ac3108310c214d9cab163c
- 36f23f39d5bf737e10c2a253f046741f530ebabe20216ec535b3aab4bc9efe5c
- 4ec361e23ab8e05a13532c2c669bf8a37adb1e918124b308f83e3ed59a4c2abc
- 4ed4a8509a45db8c5ff416c738cb25a877b47bd1066b30b1c611644f92b051d6
- 4f44cbd14878c3f8d6415c0d7d103224354323d624ef3e0906f3695d3c9c06e9
- 505086a1799dc039d72a0e691641af6660ed9b2b97e7ff9b1379b59971fc9701
- 574e0c9876b887373cb06e5873f99decb58c10e97d87f930b86d4156a4585e97
- 5b037ffcf5d7627fd5e722fa9b24f9a7108fd65069f47bed25e0c72618450774
- 61847bfbc04c932876fa453db940c2ae04c71476f4852f1799fd1de2e8a649af
- 6dba2d229e5170601495ae923bff1f46ec581b6d858bc2b19a8db3ed210b8791
- 7a93669bdf9192314b505e49e3d80e3974683a024f12f92ba0103e8b640a7d2d
- 7e113d90f3f9a6dff9a99479d7377ee1b19fa3534ba3874c98495cc8b5ef3a3e
- 86d5dff17cefb0f8c99c92a4e5890086d2674ccfb46ad80bf202df6961ed5d4b
- 87f83003dbefa877b6256c34ceddb4447880d4db632656a3718fea5a0428515d
- 9617d56a748b5f29e7e97260fb61ee99b9035521ec4e4d134fad9411e74d950b
- b29235fc7596b5ba81c8edac236b03e8ab86b0457297151b4f410277939f12ee
- c421dd4f20f4b7d99e740352db8e727a0b3c88c34ab2053849f039b508d73f71
- d454f075a83bd4d4541ed25898a4cb8ac5ef903b5b4269790a911450ff0a76ff
- ea09bb3b764c057f45134b132793654e0937701d4cc731298cc7791b1e1b1b88
Coverage
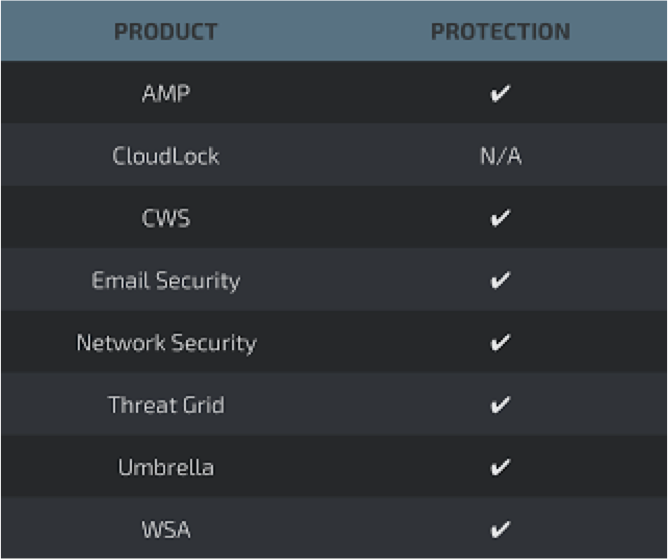
Screenshots of Detection AMP
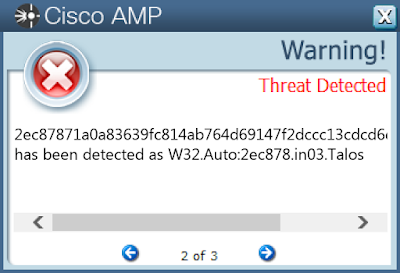
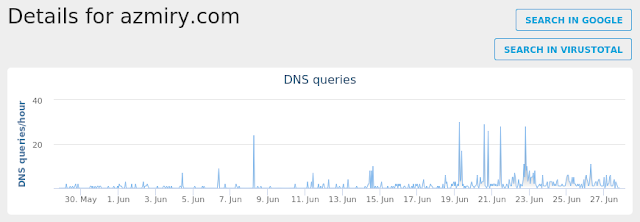
ThreatGrid
Umbrella
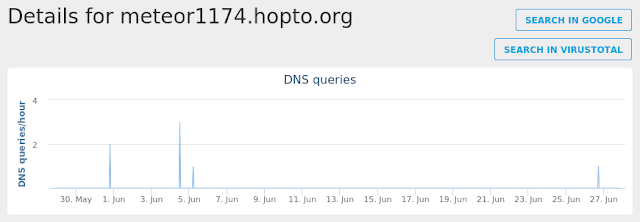
Win.Malware.Jaik-6591471-0
Indicators of Compromise
Registry Keys
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters Mutexes
- N/A IP Addresses
- N/A Domain Names
- meteor1174.hopto.org Files and or directories created
- N/A File Hashes
- 07bef3ef1d45fe1bbc7c16f7e7ad211e1e81264cf9ef119232d10bfd2245e778
- 2ae2fcade0f57faf7fbabbde56e60ad080df9011ed70dee957aa7fe13a961c80
- 2bab01741cc5796155d61543a7efe5cdfa96bde3507f1d85ea2c96ec0f1f7c0b
- 3329a848c569b7048f60a733cdf217d84baa1820fb4c1c423662e799fa1b9331
- 36ac6881149050ac9aec57972ccc3e8063c51e66529d16b0a2647b9ab8700715
- 49646325555c83e70ced5a1b4b2ef7f128ff912593c95c017703f332c83e0914
- 58a9f5613ece73717b322ab7518d887fdd391011cef6afbcb311eef74b677df9
- 5c20c7e6b9aa1dacafff644088c71388374329a9e0a218fdc944fb802fc5928c
- 5eb6c33a3e6dbf7067de22799ef42d58fc8696f74a29bef655993508e9b9d018
- 622fa10ffe94bff99be638991472cbfda178d186d6d95adc2bb87c39d2f9c1fb
- 709da9c32f18848efbd955bef0d1717a5adf56435a3bf0d1fdac34aeab25b725
- 70e53202023b2615c92a7987590161ab2a18410e827a6535ffc1df83eec6821d
- ab551f56024f9443b83107091fe741ab301052c03c34c167717f781f9fab36a7
- ad459b9f19ce38d60470ed2889895d23f618f2be1aae8e49b172e83faa69c2c4
- af9f5370fa6758440ef40215c4412b1b266c33effc541c97766b7c6f4dd076b8
- d0a55070ae9fdb2b7ac3b113025200257d4e02c223606038e5f19e963bf2c9e4
- db5025e926aefee22c19bea499ed4e79c8d28dac511ac82016823a34ae9f20b3
- e35cda507a9d6fc95a409f8e9946bae206a02063d51296017d82382ff28ead88
- ec67e3754964d9c2ffb67837cf56eacdd51557012e31014fcbf29a01254d6fe5
- f10fd36eb803b00e3173b20a2c19fc99a82a51fdecb7eb5b41417ca8365a98c4
Coverage

Screenshots of Detection AMP
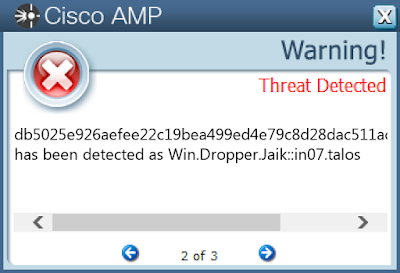
ThreatGrid
Umbrella
Win.Malware.Delf-6591417-0
Indicators of Compromise
Registry Keys
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters
- <HKLM>\SOFTWARE\Wow6432Node\Mozilla\Mozilla Thunderbird\
- <HKLM>\SOFTWARE\Wow6432Node\Mozilla\Mozilla Firefox\
- <HKLM>\SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion
- <HKLM>\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
- <HKCU>\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings
- <HKCU>\SOFTWARE\Microsoft\Office\16.0\Outlook\Profiles\Outlook\
- <HKLM>\SOFTWARE\Wow6432Node\Mozilla\Mozilla Firefox\20.0.1 (en-US)\Main
- <HKCU>\SOFTWARE\Microsoft\Office\16.0\Outlook\Profiles\Outlook_2016\ Mutexes
- S-1-5-21-2580483-2483680211483
- 8-3503835SZBFHHZ
- O40QO-SR7BC0x74z IP Addresses
- 162.255.119.150
- 93.89.226.17
- 198.54.117.212
- 50.63.202.36
- 52.5.103.164
- 54.80.160.147
- 184.168.221.32 Domain Names
- www.exodusenerlytics.technology
- www.davenunn.com
- www.bkinfoprosdiscountworld.com
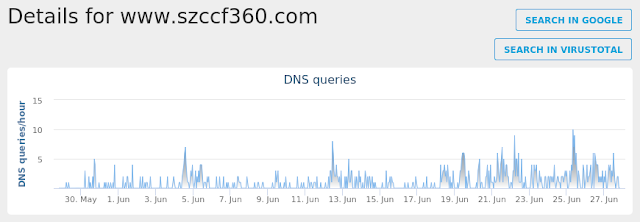
- www.szccf360.com
- www.diligence.agency
- www.curry.estate
- www.nordraack.com
- www.titandevelopmentgroup.com
- www.iqtlab.net
- www.dem45.com
- www.sinevizyonajans.comFiles and or directories created
- \TEMP\tmp8gR_uW.exe
- %ProgramFiles% (x86)\Nldp\colorcpl8pjxn.exe
- %AppData%\O40QO-SR\O40logrv.ini
- %LocalAppData%\Temp\Nldp\colorcpl8pjxn.exe
- %LocalAppData%\Temp\Nldp\colorcpl8pjxn.exe File Hashes
- 05e73d8ba52f08aec1a2ef518882919038bafc5de2ed55d392b6ccea42ea2dd3
- 09a45c4027bda13479438300bc335bce71d55867062c959c73ce5403ff00c612
- 0b23ebf80d0733874699afe7ce80553b6b4a61a1e624e1e07b623b51f7860691
- 0d0f137cb556858c93f1997cbaca1be7cf6ef24cb727fae6a0c803960c584eb0
- 14a68cb7a2930e6646657e26dd45fb5a78516756b7109ee12003bcdc822ad9a6
- 173fbe68a341e3ee14ae0d1b28668200573f48062621e76ca5dda051effd4e05
- 17fec1525d222eee566d9659723e31758615f38f11737f92e553bcbd1e38536b
- 1bd6c972c2e3d832da416d007c99a29c262eae2e8f33fe01a8a21e28351e35cb
- 23387c5a36e1238a0c7d0c2d5e085104633c5d241b640ce5c0c141298e690bb6
- 253a4ae4cbf315b3b22bb9c17dc10c56ebeb81a9b5b9f7914f6fa5fd427b5f06
- 28ba614d48c8193e3281dd382b2e20572ec74dd1f3566aa587f8b4f3e245a7a0
- 2b2ef2273c974fb2645c6f89780f227f9361f3d70ea7c016ce04cb9723d8b35a
- 2bf9a152694a78137a1a65528ba0ec59d4d104353ff8546e81f95dc93c057836
- 2c5b196d892dc0ced1b53bab03a485b7b8e82bc94a8f3117ab4eed0eca98d1a2
- 2cfce9a60463f25ce69d2a0ed56e026db274be7d55215c8dd02de6df6e9b51a4
- 31c70b829486f54898eb15bb28dfcf2c56f3860a9dca3872ddf2c1b0a8f52e99
- 31e7fd07d03a0e11510f49056d99252abfaa1cc326ded44fe8c3b21a22fde5f9
- 3342fab27758ae8bd7acb18aa622b0c0e2cc5425b38c404059f742eaa5c437ee
- 34058b038b01acf371ff2124cc8090c078514cb90bc40aa71e6147cafe9323e3
- 39b16f474008113649b0177624a320ce91b7522c791985eee9c044aabb888802
- 42635253472eab8f4e242db7705ba5de5ab3088bb6d366696219974ed2817383
- 4292e8ecea77bd64adb39b58e02c24745d52485c376a1f950aa5adc2e8a3cc44
- 4372ad95f57701da72c2fd9e191beef564d613d473a53cb3034eab407229eb8f
- 441d9da5829e5e263ef7c0bd43dc097d6e4221273be576072335e8c3226d7309
- 44d6b38d0cfac3a4f96c2c65997d203fa6d45b8de07fcf0908ca6eb8771d5286
Coverage
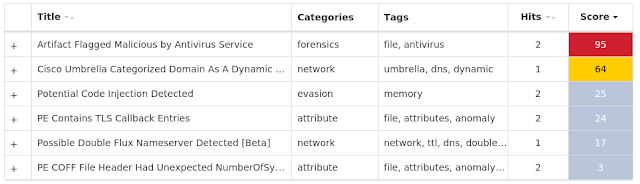
Screenshots of Detection AMP
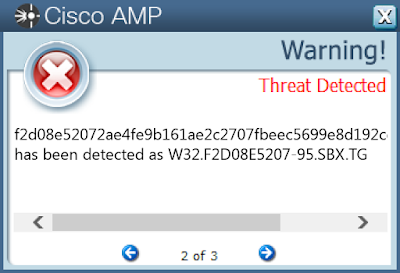
ThreatGrid
Umbrella
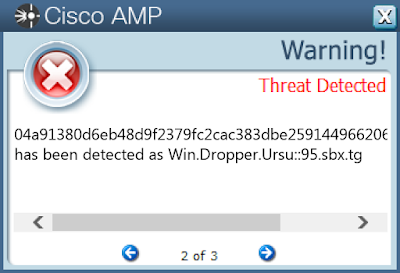
Win.Malware.Ursu-6591377-0
Indicators of Compromise
Registry Keys
- <HKLM>\System\CurrentControlSet\Services\Tcpip\Parameters
- <HKLM>\System\CurrentControlSet\Control\DeviceClasses
- <HKLM>\Software\Microsoft\RAS AutoDial Mutexes
- 3749282D282E1E80C56CAE5A IP Addresses
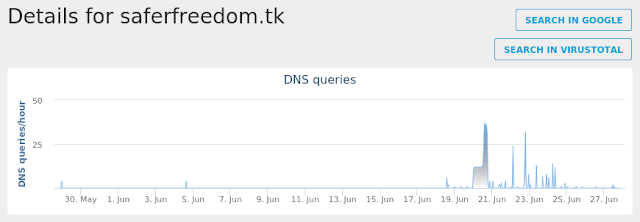
- 104.27.133.70 Domain Names
- saferfreedom.tk Files and or directories created
- %AppData%\D282E1\1E80C5.lck
- %AppData%\D282E1\1E80C5.lck File Hashes
- 00671219067cecc386d3b250b4ff757a5497a4b3722aeb0dd3befe3b452d422d
- 04a91380d6eb48d9f2379fc2cac383dbe259144966206869dda719a66242bf0b
- 095244d601513670f12b135767eefc69bb321a36d04c2a2f930631dc972bf2fa
- 2551d70b3860021190a1261539cc7f95fe9a9e4e38491f3c57f7547ad8e908a3
- 3c19f663bd6a3e2bc4a9532d087b8df17e2b2ac13c601b61cdbb484df6573210
- 55e214ccca87524499ce3b9cda713412671acc465fd89d37e05aeed883235e67
- 7b298711a73ca51baa7ae7150b70e0be7753e8cdf1ec0cfd051a59f30e4b0676
- 848b95a4454433a35d600de4fca65d177daf06c0c049d7c8e0419cca7145e0b9
- afe462e1e36845bb140053d0697d30df68228b57657451d31807ffb6596189ac
- b126c7530385ff1842b2db06161ee5cb09afc368d486f679b6e88bf62199ed34
- b961c0416728d78d875807fce6313c1eafecffde4d0b586227498edc09b8bc35
- ba0e40371cefac1880961c60a33c54f1cca57e883da1a603df04f162941f9b28
- bff4edac75f61c111017c92e248e977adf795afee9e8b9b4dad9accb5650060c
- d1ede616a2a66853bdf7603f56f4e128e722883a2ef4b9b54de8d2fd1e79f3b6
- d69ece607dc234195e07a4df139aaa83b8958b3ac3bcaee1d1af19f22b1ee049
Coverage
Screenshots of Detection AMP
ThreatGrid
Umbrella