Today, as we do every week, Talos is giving you a glimpse into the most prevalent threats we've observed this week — covering the dates between July 6 and 13. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics and indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is not exhaustive and is current as of the date of publication. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this roundup are:
- Win.Malware.Jaik-6607437-0
Malware
Win.Malware.Jaik-6607437-0 delivers a powershell-based miner that may consume system resources without the user's notice. - Win.Malware.Generic-6607409-0
Malware
This trojan may execute malicious actions without the user's consent, such as collecting system information, monitoring keystrokes or the file system, or establishing remote connections. - Win.Malware.Dbel-6607389-2
Malware
Win.Malware.Dbel may display advertisements without the user's consent, and can perform other malicious actions. - Win.Ransomware.Hosts-6607383-0
Ransomware
Win.Ransomware.Hosts first gains persistence on the system and performs process injection to conceal its actions. It contacts an external site and downloads a sound file that it reproduces afterward. - Win.Malware.Daws-6606625-0
Malware
Win.Malware.Daws will gain persistence on the system by modifying the registry and dropping files into the disk. It will also contact a command and control (C2) server, which is flagged as malicious, that may allow it to control the infected system remotely. - Win.Trojan.Urelas-6606624-0
Trojan
Win.Trojan.Urelas gains persistance on the system, uses temporary batch scripts for its execution, and contacts IPs flagged as malicious. This trojan may perform different malicious actions on the infected system, such as monitoring user keystrokes and the file system, establishing remote connections or executing other software without the user's consent.
Threats
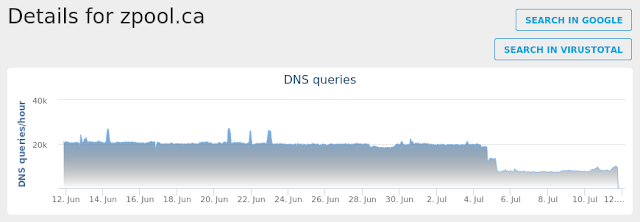
Win.Malware.Jaik-6607437-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
- 104.25.206.114
- 104.27.144.1 Domain Names
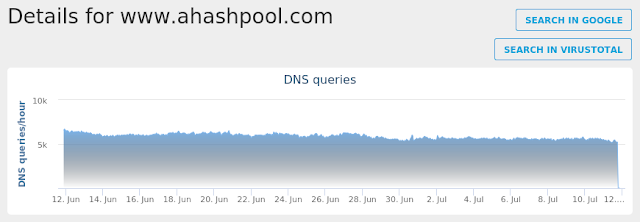
- pool.hashrefinery.com
- www.ahashpool.com
- zpool.ca Files and or directories created
- \TEMP\Engine.ps1
- %LocalAppData%\Temp\yh1rekdj.kyw.ps1
- %LocalAppData%\Temp\tvo434zg.kys.psm1
- Engine.ps1
- %LocalAppData%\Temp\53C4.tmp\53D5.bat
- %LocalAppData%\Temp\53C4.tmp\53D5.bat File Hashes
- 4b40436146cee215c59870e36f4f968345f877a3da99f25848d44afa3f1b31c7
- 59ca65691aac6fb4fb6b5455a8aaf519a9ccfe58a0711ebd80f2fda578d7a695
- 5f23072d7826fa01e40f03cf61f414766a47ec1f356b6ccfdb38e2d070e41d2c
- 6efac03160a2ca2b69827d8c86c625e68bf0f1d72f981fc4c8ec69fd5cdabd87
- 9785045b4b9a6da30e786ac0c387787bc8e2b52b730eb8a0fcc9c9eb2093cdce
- 9c6965c2b2d7db282de183d631693cabcc8a64ac50d8e2d9a28bba6dae7140b8
- a221912cebea541e80bc04bf11a1b79169e2143dd4f98529a9e1ffe2ef514280
- aad0d72aa2b0b52ef45f6ce12ca2c0cdab082a70f03b4675ebd479c1d376e048
- b740f63d827ae99159c51f04f2c247273573d4db19578ff16405284e701cd1a1
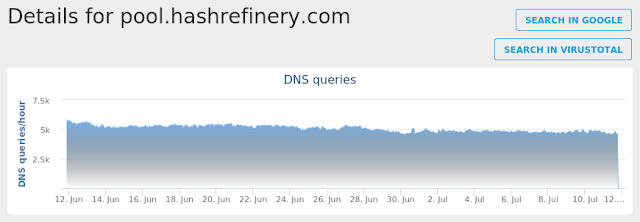
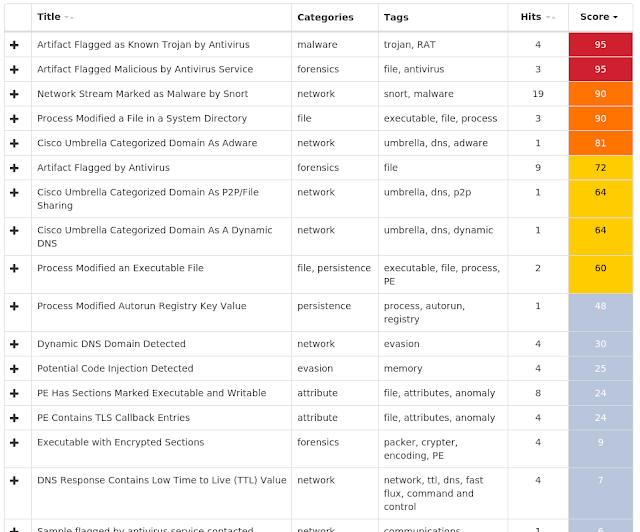
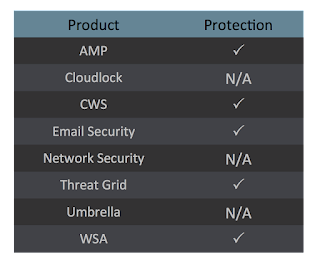
Coverage

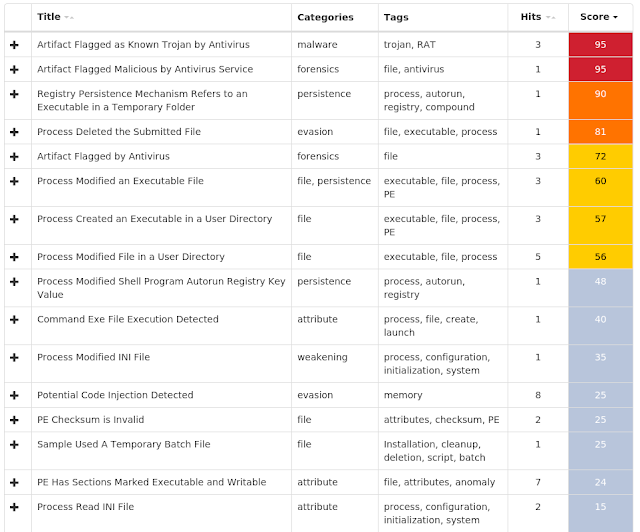
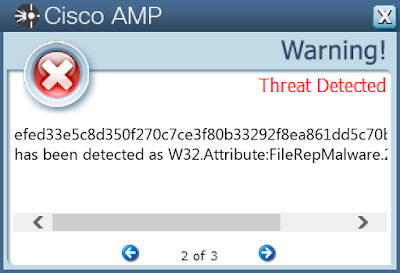
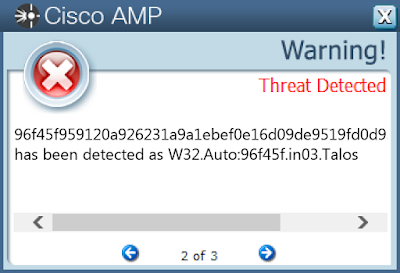
Screenshots of Detection AMP
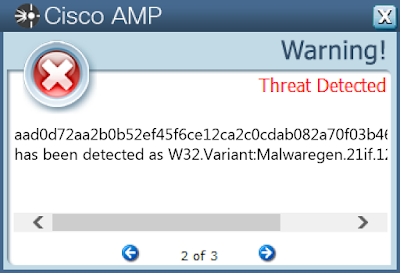
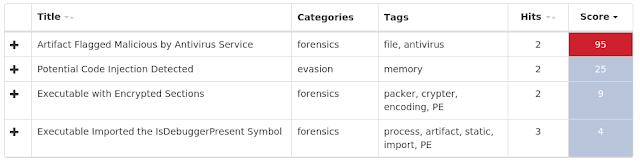
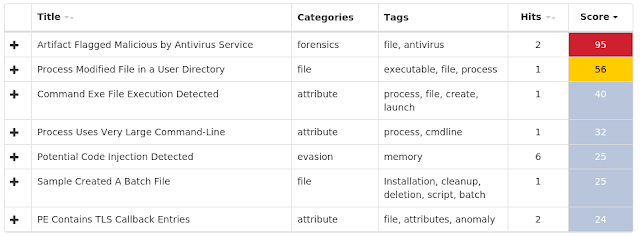
ThreatGrid
Umbrella
Win.Malware.Generic-6607409-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- Local\MSCTF.Asm.MutexDefault1 IP Addresses
- N/A Domain Names
- N/A Files and or directories created
- %WinDir%\ServiceProfiles\LocalService\AppData\Local\lastalive1.dat
- %WinDir%\ServiceProfiles\LocalService\AppData\Local\lastalive0.dat
- %System32%\winevt\Logs\Windows PowerShell.evtx
- %System32%\winevt\Logs\Microsoft-Windows-PowerShell%4Operational.evtx
- %System32%\winevt\Logs\Microsoft-Windows-NetworkProfile%4Operational.evtx
- %System32%\winevt\Logs\Microsoft-Windows-Diagnosis-DPS%4Operational.evtx File Hashes
- 0304c1aabe233566025b24140d43f882e002cbe74abea4c243d78bf8a04c1068
- 139bd7f69953d5dccc274e6a6f2e958d11a43abb2281b8576f387b79dc19c197
- 13a84666419bdcb611b1f1d361578d7abd9d0397325564b4ccb7b4a52d523935
- 1d41d24f744d82aebb31db5757fb8b7b0c50e8b1de75e97717769968fa0d1d10
- 1ee26bc768fbb572b9e690b6e3f41db4265e812800794197c8208c666767e59b
- 2df1bd9cc78c2e9603c41b650ca606f99ef4ba52aebee9b39dbd2d110ad4c45a
- 332870f1b71e77fd1521ceac1db6f72454d44bab3d8253f94359889a1a0f8322
- 33c5bdcb00c39040bc42db0ddbb1d43540e446111dd344358cb166635a7b7875
- 432d7c14056525b1de7bec20a9ed80f1744eccf9928d763d2948c0d5ae55b3f3
- 4ea449f4ef2a4bdcd96d8cab961168a541ec7bbc51144503f47e2ed3e6bfad20
- 50687a27477a80574af7b836e90083330d486815804e9b7a5eccf3547d62e8f8
- 5b9aa3c388e1ac3dc9d4dd0e427590ce4a1f977787b7a2c5bd846b9d984008f0
- 62852003a07eaac1dab52df33a58cc979dd8fff6cc240b5feb330b3f7ffa2755
- 63d6e4a25bd071d8c62f4741a76cad0fe8ca4c03253bc351d82e8f6abf1336e8
- 63eb562c673e24528af73f6d90ebf1b2fc575287d5f971dbff3e19200f4eae0a
- 79d55737580d069816c1745d410caab32cba85dc9839683bc295b1df5de6f929
- 7f38bbf4562cf0e03aa11a1c9ec229fdd5c52b173f14584552f234f80a826853
- 7f6d6308a0fe8a6d4898d56dbfc7a32bd6850acd6fd774b8e0827240859c2e41
- 8318315039d9fcb04ee94442b07180cdda204de131bfb7cb9a69fa270545085a
- a68842e74598619367c06558d42495bc861a1f6404545f7e66731ccaeef2e45d
- a76026549238f7a716ab32de68d09a2b8e14d975d6f8ae170b3d0b8a05fab282
- b5196c00282c2bad55540793382b00661edc9d121fd28b473d98042f6860aa7a
- d9e0a3afbf6250e23c6cbfee3126ec8b40a4a7663159b96de88ea7c80ba3c783
- ddd00f7ca8445e8c5b870d499599e105a1c3a95c2c1ef61622e9e3c4792d87a0
- eb4ae7da4cc7e83b8511b892860cdca5abc2bfb25e7280150bb401d593db1127
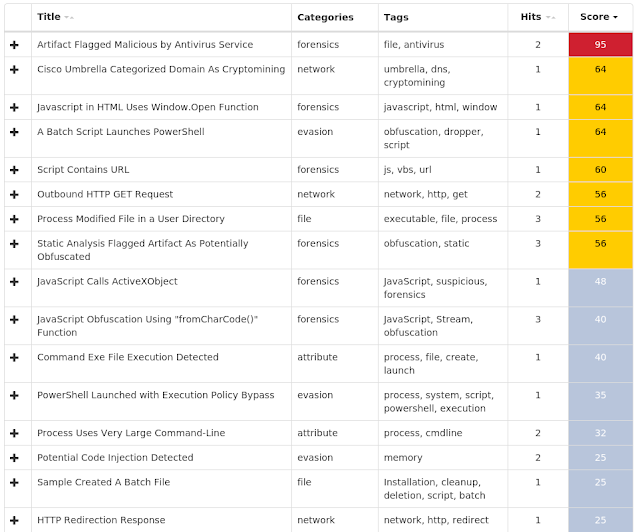
Coverage
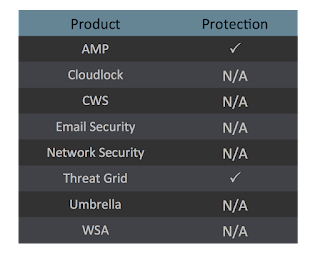
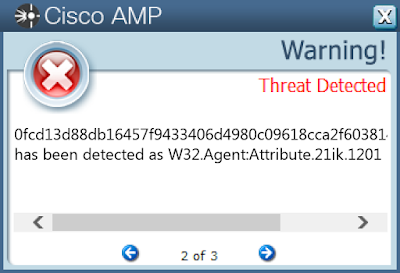
Screenshots of Detection AMP
ThreatGrid
Win.Malware.Dbel-6607389-2
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
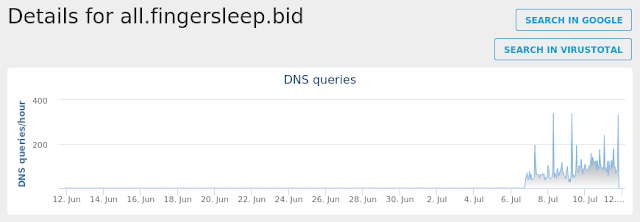
- 13.32.81.92 Domain Names
- all.fingersleep.bid Files and or directories created
- N/A File Hashes
- 091caa24acc44bd5898784480f2c3260982ded40ce62f48d4dbe38c45a4c0d4b
- 09b987244a583826dc9bc222e26f8f3e65726eff2db388b55c04ae66b46c8eb9
- 0a1bfce878c1bdd816537faaac7cc2353b2a936a77207a2a977367f258475049
- 0dd1f6ee91132936f0dbf28de674daf0faf0f24fabacabb9b9dc774c37056f06
- 0e44e2374c17aa24491a983697492b6959aa1fe8a88115941221e8bab7b1df35
- 0fcd13d88db16457f9433406d4980c09618cca2f603814c93b8f0668d4750052
- 0ff7deba9749c4052e44b2126ff0bc4b247aa705b0a08131e2796fcb0a8147e1
- 1020c323397bb9bec65e2b407ac08ad60967a3b2274117d2ae8e0fd86ce3dc00
- 11e5487b2871708ab06220dc24e11952bef82744ceb620895932b8a444f9fd17
- 156e39ec36273b4ee35fd949ea73b22d4eaf8e30b3d6a5b769a17c7ff3328dbe
- 1f5552f125424c23601987d9a7d08a7e408e2545e30c7fd678ccefbcb19d35cb
- 20607e1efba4dd19618384a3cd81cf83ed9199cf98e95072695f3335b9f1edca
- 230de1d3cbaec2530bdfa3baaaab3de627036e36de6d41ad8d722a178ee76e40
- 2a5b2558b069a188168013d13fdae0140db5591042f0600aae96f791aeb10cc2
- 2f1a27c79aac8a2832bbed6ab2eba63bd3af4e3cdae608fcfa2df473b43b3bc1
- 33f13e96394048f90ba1171becc45b503352dd2f7c93ddfe6d4c1692f50ade0c
- 340cb86784d60dcd8f181b52b70ed8840db818fd07f71b2e08123853db9110fb
- 3e19a6dafc60c42bf2519e7f608b36b2bcc1fe49be79a7b90c2057334e1c7189
- 3ef67512f826f552e8ed94a71ffec10605fafee6133bb456c9eb8cfebcc8ccd3
- 41db8921036c29be08be7f894bd8596df6d9848f6754f82fad27c635f177abb1
- 422f80129d4c71fcf4db6780cfc81b58f5c4e29b412046f0a17285d98284f5a8
- 45547b35cadfea536f117f375f6a8c8dd7926a41f4be9be23fa4be983777c9f2
- 4926f1a5e295d0498c6ece78dfc82443589aa541e57fb0d0cbb59ddc61bad57f
- 4d4603ca66e76b8f5cafe5b1bf5368124836b6879734e3212f5fa94a2e632fbf
Coverage

Screenshots of DetectionAMP
ThreatGrid
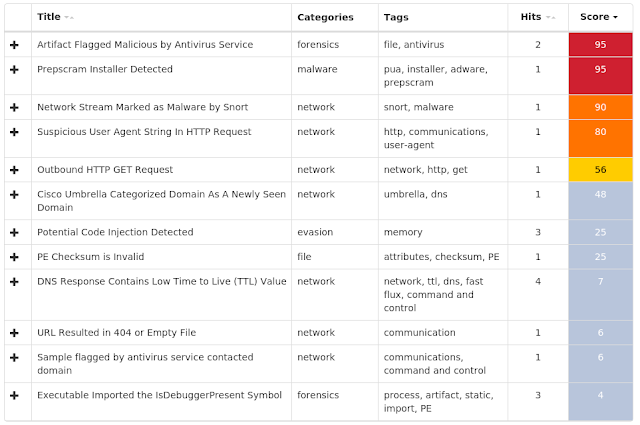
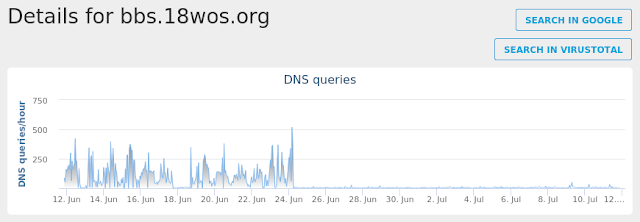
Umbrella
Win.Ransomware.Hosts-6607383-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- Groove:PathMutex:tzanqCjN6dCs1QGzbKslin0UfIk= IP Addresses
- 98.126.20.12 Domain Names
- bbs.18wos.org Files and or directories created
- %LocalAppData%\Temp\8ECHPOST.bat
- %LocalAppData%\Temp\8ECHPOST.bat
- %LocalAppData%\Microsoft\Windows\Temporary Internet Files\Content.IE5\SSZWDDXW\Sean_Paul_-_Ya_Not_Ready_(;yanotready;)[1].mp3 File Hashes
- 0bf91ab95e85012f58d4b9a67e09841f04ec21666bdceadc5f16a93e4c4a96e3
- 1c3953149711add3b2335959c8c6579f29956ec02150b8a241af83c302c5ca59
- 312418dededf7fa07ee39314ac977b06b9a7c22550b4f269852cd801cd062d49
- 3b8a6b0dcbed99f23cdc57de2822fcbfabdabd82af3dfa664294f9e12cee8c97
- 49d27a252212601cee8b63ee5b9a2ce06a33d20964debe19bd656495ee7598ee
- 786dba298d82bb0b39404f5885bf5d9ae00db54ea34d337a628eca0aa6eab1fa
- 7c00d5a389b840bde49372c8c2eb2470607e916a899e0f03dbb441200a2967c7
- afa7d63202387891c1727a6fafd5e30ae0be97c617c3eef38f650a7655605a56
- b22e72a5875b8ce68d15f74bc454186171f920374e7dd13a57991cdd8e45d24b
- cc6d69ab51542ffbe4986797a6f1b36644a5ba7d2728d32ae1978b138ae8cd19
- d2e091f59406dd59211f81756f08d8baaf255615001b64afd57f8b7935775cf1
- dfd0180feab22a765d735e4c4e022e79f313ed177013e9d506f29aeeba9576f9
- e309e767073f099f8c0c2a187e641deaf76af4f78da784abb3441650ebcb039d
- e41ca39270846dba275b367a53f18ed98673d546f6c16a0010fc0fd877080232
- e5ff9cb29268551c867506bd251e6c7ca80a3bb5d5dee8ca4f80822c14c94f62
- efed33e5c8d350f270c7ce3f80b33292f8ea861dd5c70b8ffa64c23a9a0c69b4
Coverage
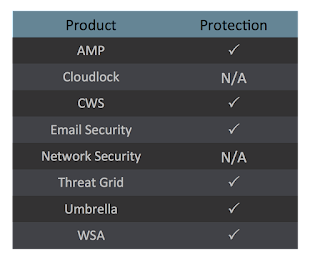
Screenshots of Detection AMP
ThreatGrid
Umbrella
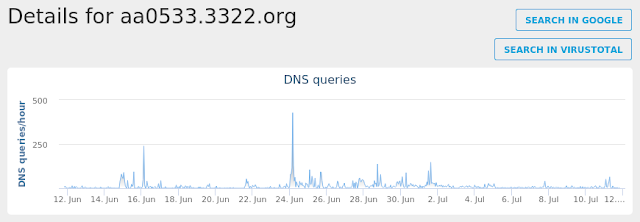
Win.Malware.Daws-6606625-0
Indicators of Compromise
Registry Keys
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: Kris
- <HKLM>\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run Mutexes
- aa0533.3322.org IP Addresses
- 157.122.62.205 Domain Names
- aa0533.3322.org Files and or directories created
- %WinDir%\svchest000.exe
- %WinDir%\BJ.exe
- %WinDir%\BJ.exe File Hashes
- 0a843d45cf437e0298edb7e1014528b3381eb65d054cf8904d23b8142f19dae6
- 2ad4073ae1de153fa8a5b337c2ecbdb76a9ac21ea8ac242a05421cf354e7ab3c
- 38589756ca7eec53222f1c5bc2a2e46dcaaa3628a52b779fcc7a61bcf6ccb596
- 47ff4094684b1e2b01f5b76b8b97d7e5d30a62c286d461af985f2bc2ee4fad73
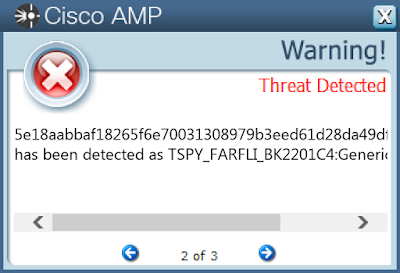
- 5e18aabbaf18265f6e70031308979b3eed61d28da49dfd3bfe7789b52d63d593
- 7aaca0b23200e62d6847d6e63b584d552aa7e73cbeb693de816ad0e73989849c
- 80f00a79fc76f6c4686d136517a6f5e62e93f19edb427ea774e7b2f9f7b6e4ca
- 8341a9af1d9ba6a84cb77b52a064ac8fd6ee9bfee39fd46e740e80720efbafb0
- 8a3421926d5e66c331dbc32d47c99164b68e55fce84005ab602f52ad9ce28054
- e9cc6a849aed6306da590ed8de295b5a8f22519d323ee7300f09261ddf74a7bb
Coverage

Screenshots of Detection AMP
ThreatGrid
Umbrella
Win.Trojan.Urelas-6606624-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWS
- Value Name: TrayKey
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWS
- Value Name: Run Mutexes
- N/A IP Addresses
- 218.54.31.226
- 218.54.31.165
- 133.242.129.155
- 1.234.83.146 Domain Names
- N/A Files and or directories created
- \TEMP\2871954827.exe
- %LocalAppData%\Temp\ziufv.exe
- %LocalAppData%\Temp\_uinsey.bat
- %LocalAppData%\Temp\juexb.exe
- %LocalAppData%\Temp\golfinfo.ini File Hashes
- 0d57c750f39cbb9e4ee8504658348835b45dc4241d7c099ec58ed7bfe5a628a2
- 260dcb0f2fffeb4ae9c3c7a200396f8264333d8cb63ba4c3f368dde36cdb98a4
- 3149e9891bf310b3f4f8de7484f105ee407b58615af36baf67d62ad19218bdf4
- 387ea2cd50f3a5e563f37af14a525ef675ca98b7f38c49c5809d1d42b51e9519
- 704d7bbc772efcaa18b585c1ab782da7a643e0c45bc19bb18ef7cf258abb22f7
- 7c8be40eb56a11302d8490bd6d72203ab213ce34e17db004e568f578711b7327
- 8522e1a14f9938d30096bd7b50fee6d03dae7acaf660202b3e037d1a37c7bc84
- 953e5ab16bcf1558588f3ea041800007dfcc119f64792ed659bd303f8c20a68b
- 96f45f959120a926231a9a1ebef0e16d09de9519fd0d93f35b0996973305f8b0
- 98cf27a77174fb7287ec781d9edb9b81670d52bd02923ae24bb2e3522d5743ac
- 9c08285d4d9043c372e5758358964ea75ba55e3455575c5785b6065806c37940
- ae8d0d4996f4d722748d28e5495101a223e9fdd0829656f23c7d98011da80447
- b2d2bfea661ed1fff2bb8ab465d0dff71106136505febe5040a7a27e2ce44c7a
- c8b7316ce2e3c30145f469ca30d8b051392237e9f99cf6cf731f592582d9b78f
- c9bdf7fee2f610c90127564b409f69f9931ea1e6957026dca45ff30bc6f8bb93
- d164f9ef0a8e1f36798b0543d8978eee384dd992c3da90c3640f716958ae4281
- d90c453ba89ee35f04b5344490b201fad5fda97b442f40a2c9d710e7a06fe9d4
- ef870ddf8b97e256e229303eb71e2189c881e8269330978c10cad77518a3d092
Coverage
Screenshots of DetectionAMP
ThreatGrid