Today, as we do every week, Talos is giving you a glimpse into the most prevalent threats we've observed this week — covering the dates between July 13 and 20. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, we will summarize the threats we've observed by highlighting key behavioral characteristics and indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this roundup are:
- Win.Trojan.Generickdv
Trojan
These DarkComet-related samples install a mwalre that is persistent and provides backdoor access and logging on the infected system. - Doc.Malware.Valyria-6615927-0
Malware
This is a Microsoft Office macro-based file dropper. - Win.Packed.Razy-6615989-0
Packed
Razy is oftentimes a generic detection name for a Windows trojan. These samples attempts to spread via USB infection with .lnk shortcut files. They collect sensitive information from the infected host, format and encrypt the data, and send it to a command and control (C2) server. Information collected includes screenshots and the sample installs for auto execution. It uses the pattern %AppData%\<company name>\<company name>.exe - Win.Trojan.Darkkomet-6615953-0
Trojan
Darkkomet, or DarkComet, is a freeware remote access trojan that was released by an independent software developer. It provides the same functionality you would expect from a remote access tool such as keylogging, webcam access, microphone access, remote desktop, URL download an program execution, among others. /ding-your-rat-has-been-delivered /reversing-multilayer-net-malware - Win.Malware.Gamarue-6615948-0
Malware
These files collect credentials from Windows and from browsers. They connect to C2 known to be associated with LokiBot.
Threats
Win.Trojan.Generickdv
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: HKLM
- <HKCU>\SOFTWARE\vítima Mutexes
- _x_X_BLOCKMOUSE_X_x_
- _x_X_PASSWORDLIST_X_x_
- kingofthedead_PERSIST IP Addresses
- N/A Domain Names
- N/A Files and or directories created
- %LocalAppData%\Temp\XX--XX--XX.txt
- %LocalAppData%\Temp\XxX.xXx
- %AppData%\logs.dat
- %SystemDrive%\dir\instal\win32\svchost.exe File Hashes
- 8c87d29fc3fae2fa8f5056a2c02686c901cd79cc4529bf5a29ae08042aaab746
- c2fba20c7753baf7616eddbf784f4f4ff67891b0e578c0209e264a4a477cb6cf
- c857b44b7591ede89b6bf8899aacf155f15cf92c95af494a0f8d3df202124f73
- ddab332853644fd0d13c87f93c1a05caa1de7396c7da03650b2de1a812b6f156
- e85321b89e3f28bfca8049e0a25f819c8e9897db956056df3b8e65f825d898db
Coverage

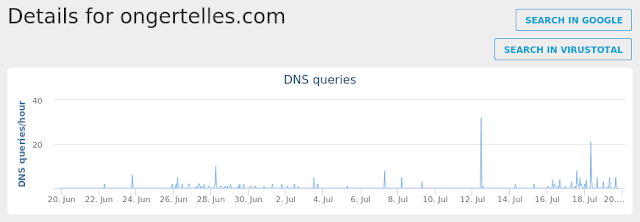
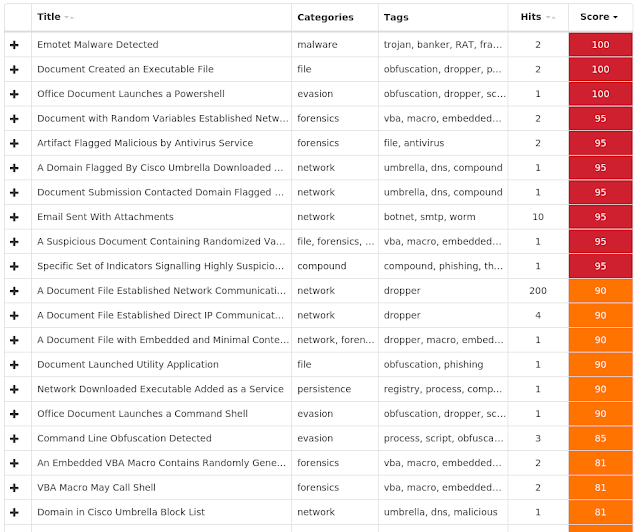
Screenshots of Detection AMP
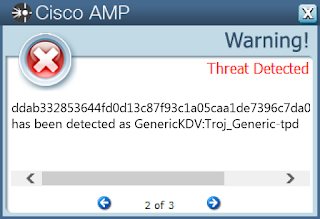
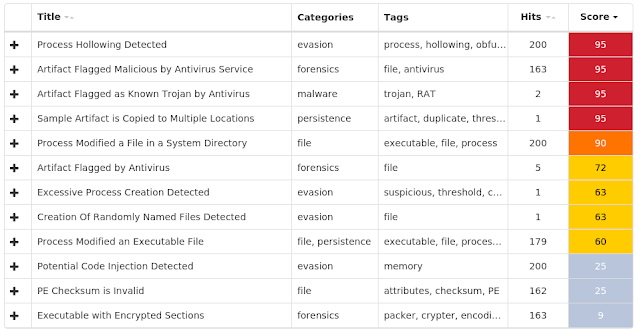
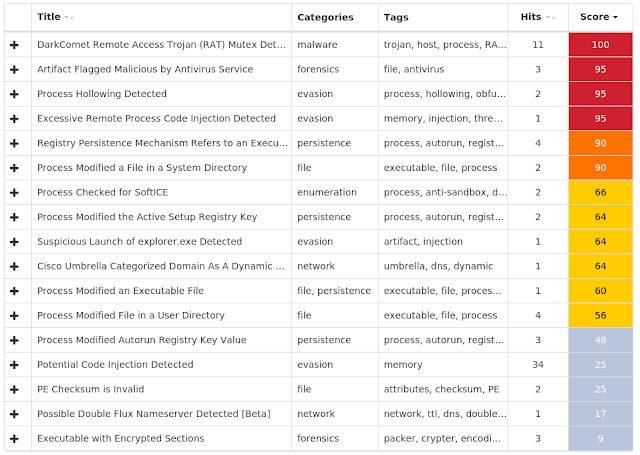
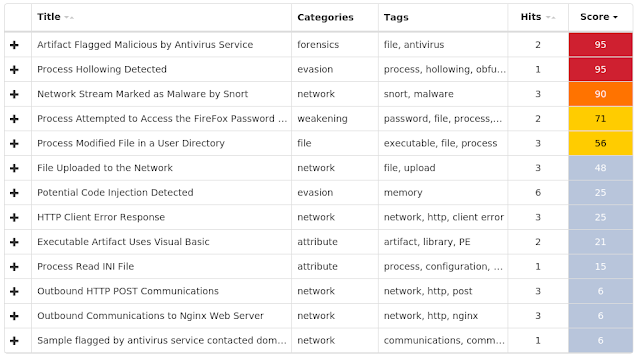
ThreatGrid
Doc.Malware.Valyria-6615927-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- N/A IP Addresses
- N/A Domain Names
- N/A Files and or directories created
- %LocalAppData%\Temp\320.exe
- %LocalAppData%\Temp\es1uuzqu.xfn.ps1 File Hashes
- 00592b51236463fc3e8b7d530a555e55dc46eaf0d741f2c6a06bf1016a8fe6ca
- 04f46cc8eea2154477cdfc3b893ae9f625e662cd401c3bd172dd9943e92032d4
- 053363bf7d81a002ab526c913be41803c7eadfa958fc1e94a28f440c9707ce6c
- 060f8741f10f260d0103a93b3242235fbbcaee823259d86b5eb6ff339b8c23d8
- 1440592b86f68fb240ec526a026f10b2db953f5ea946280aabf2e97ee1022211
- 167de913f71eff1ac2aa1e1d1ecb60ae113d2b47cc6848584235d6f76c17f2c4
- 1b35d8b84c971ec3563ee2021b26e318f199894228831ca9749196000679c8d3
- 25d000f24e86937a202b12dcce7edfdacd42dbb967c76829eb94d5965590e5c1
- 2ab506076a0f2bd1b3971285b5b90b859dec3ad1e2ff0a0b117824ca16c55cab
- 3708636d74732da211c6a27d4919e81bf092deecbe3127cafabada1825756d34
- 471d40b6df9e40c64f49eb73903840a6d01a6a5a8df5350a89312c6355fc5f28
- 4d5ce5b8a4729716cadf818b0eeaaa94694147d72377b2618a0832d6878cba51
- 523986d86f1d157dc7c0ee71fef4b7db3d603cfc8290ec8e477d530825421709
- 559bad49d16cf86b0904f0413fe987fde19cebf88c5f8cf343c0fd5fc029c668
- 5836e5d29581870a533010f4e83ff5a5241b253330fc058c5610004e874b0f4e
- 660d4a7fbb3a9b2cda39dd9cf070b23487a150d7eaac569d1dcd5e658b5b3e73
- 759f6aa2a7105f84a4857ea959402c348719c920adede9f1b525b926f680619f
- 84db21d753f64d64f83c378ba344e19600d1467543a22a64af790407179208c3
- 85027897d5c0608e88483ae483079d16dc3851e746b6ae18f8cf335c10334f5a
- 8611f5f17e11d5180cc162509aaf2623196d44d09a80813ce21336f3cb0be4a0
- 925ca30ebfb42ee1a9dcf7e567397f3a266f70cc6d20158929c905642a94917b
- 965b382513154b06f1cbfdb0a9214fabeb204954e106af0abc9fe7b279ee3479
- b658943488d9fd1886d7848cad19322293558eb62648ca60c54083c8e710b710
- e49851a85e17e21159a43fbbd1bdc1183a95202a86bd328769e2049a9dd9a886
- e7db2087ef7f0f80640c7f62a493da43eadb8db5f5af90ef1cb55e68a465696a
Coverage

Screenshots of Detection AMP
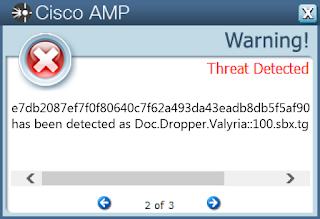
ThreatGrid
Win.Packed.Razy-6615989-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: Pactiv Corp Mutexes
- N/A IP Addresses
- 216.146.43.71
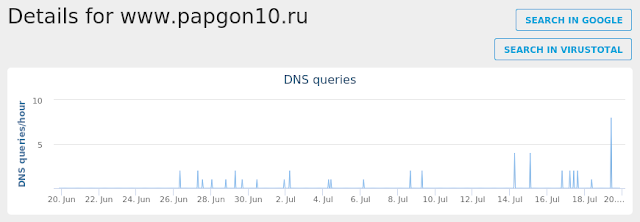
- 148.163.124.20 Domain Names
- checkip.dyndns.org
- www.papgon10.ru Files and or directories created
- %AppData%\Pactiv Corp\Pactiv Corp.exe
- %AppData%\ScreenShot\screen.jpeg
- \??\E:\$RECYCLE .lnk
- \??\E:\scr.exe
- \$RECYCLE .lnk
- \scr.exe File Hashes
- 03517ae084fa51e60f9f71ed80993adf8ff104eb44225377b8cd6e7fc3a9d663
- 0b83306197f922b8a89054be66ecce742b166457c9b22118ec0adf256e1ee6a1
- 0c2aae41be90b95f45a3845afc90626f995f8ec9b56529f09ac66a7983748abd
- 0d2c77209a75a0f78e751a07653078e7e2ca6e04830d89389d3b483bb09cd139
- 0d8d7edc72504fad53c5b46f6d74a37160474356d69418241a47c0fcddc9ac4e
- 11be51ab233c8b4e6261dd2e336c8b3f404cbd6b4e4c45abc9d3e95751151d3c
- 1b2f67ba7f479e6bc061dbf5f9ba983963f436a3cc64d99b6a8b5240db165ab0
- 1d0d2b945f206f3dc068c12b78c57def633b9aba4866ab11afb191264195e33b
- 1dfce6d161a6ebf19fc77feb10123b721c92125d2b899e51411346986febc71e
- 1f17c7a22259c8da0510c7b0aff257bf031621ed6745a5b8d60cde153057a91a
- 1fe7a461de250c6149cecacc7efce60cb6532ac139d426e59a9ca9ac978e9626
- 234886ab9eed46dbe1751cdaf9e1f0b53637aacb4c81877b44af818efd038c36
- 23f7178047915b7c2130c0cec7a98675ee4dd02d10491b7966599296d97cc1f9
- 2a9a5d363e0b7bc059577dfee812927ea3408955d532f40bae2c524d18814f78
- 2b7ac5ebcbd34434ba3b78849022346ac3e1a20339e7046740439750e3271295
- 31b695748122457b592bbdba8e832ea16451ed43b41bba88090b91c99b14e565
- 3cf6b0c34bb13e2532cbcbaa424d0ce06286c02025e2613d0e2e71662705ba75
- 3fb1cb1530b46c77b60d3225bebcbe33bafba69eb67ee659f1107a68c9c9da5c
- 407a9edc6ea979673f4f65741c6c7b55387fea59012be25073ec5c9c1993e30e
- 408eeb5088f25d51e9acc96d5d2d2a41eee87c1e53456065af70c7481fc9427d
- 41b3ceb6e29b3958032245d78e17100b255d2db8180e11ac3f4efe0e5a609b0c
- 43d7b9dd5c8441079308aa79cdbd300ae94836f97e6a02d8122e895ebd82f9de
- 4db761271220b7a4a9469570ab470f3303588b2201c2d5971b27259769d9e06e
- 5285379abf7be3d20375f077c4e251364a291f5634ad24db59999a187b2bb321
- 538f1559eeced8c9a3e088b6e700edad0f86919eb790084638e1c051a37272d6
Coverage

Screenshots of DetectionAMP
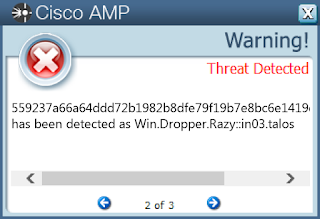
ThreatGrid
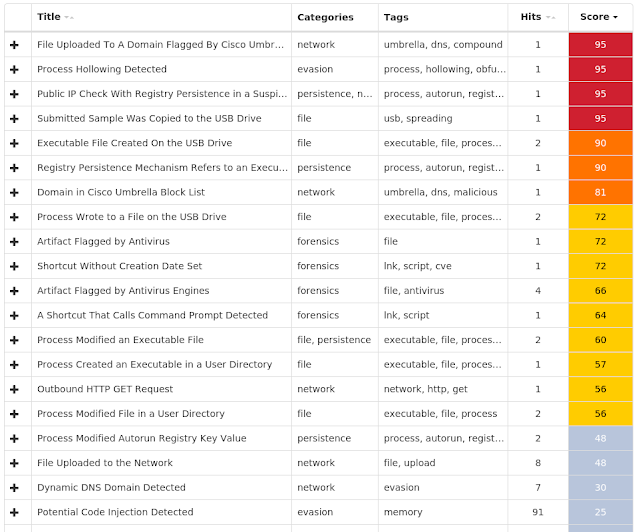
Umbrella
Win.Trojan.Darkkomet-6615953-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN
- Value Name: Policies
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: Avgnt
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{M0VU6C11-0FI1-AFG5-1IVW-7R8T24K13MKV}
- Value Name: StubPath
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\PLUGUIN_RASAPI32
- Value Name: EnableFileTracing Mutexes
- _x_X_BLOCKMOUSE_X_x_
- _x_X_PASSWORDLIST_X_x_
- _x_X_UPDATE_X_x_
- Pluguin
- Pluguin_PERSIST
- Pluguin_SAIR IP Addresses
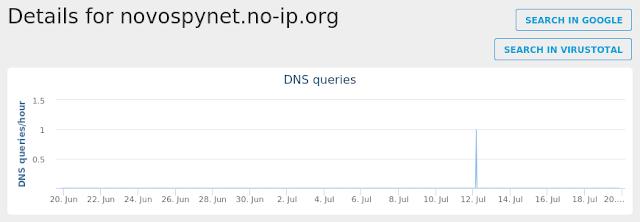
- N/A Domain Names
- novospynet.no-ip.org Files and or directories created
- %LocalAppData%\Temp\XX--XX--XX.txt
- %AppData%\logs.dat
- %LocalAppData%\Temp\UuU.uUu
- %WinDir%\Microsoft\Pluguin.exe File Hashes
- 02cc0b650b55aeb6be4d18da928a9991b4c3730391979d8f8b67501867aed8e0
- 072df24ab3e41e1ed93e49429d86b4051903a7975018dafb1edf5af952ade6ec
- 0883c9976aef73092fa17769b97945eae82f991f07ac681938ab2e16b597b861
- 115f6b1a6b33e394826c0fdf77b8fdb7087e8737b42fde1cd31e894eda670563
- 11fb3c84ab7c9122266aa4020454f4110c48992068197ba430c1a7d2086129a3
- 18e363cd178037c5b6407635d5c61784e0603eded5f0051cbc540ac47d61a8f6
- 22804ba41fb3ee8ee121af5821df4df5bda36e194e0d8683013dd8e0b1ec71ca
- 263175c9a3e5d16c3bcd661a56b70786da11e263a02c6f12d2278ec1ebfca0b8
- 27d3bc3bc2eaa3934c27665feda1b75893148309cf7b19818f58c31db22be625
- 2e1c2f41704f487779cc6dc4132ee9db933af3a3c9e93692f34e231c4f27d820
- 3267e3ad1d0518d1ee6510b3e94d7b2f19252e779d08e644738fbb7648181f1d
- 3d1748d38b40300e81c077df971040a564b81f0c0cbdd299417a7690e48e21a0
- 3d28e808850728796ca6b96c6cfd94c003e70f12024ac4090c8f68175be61614
- 4194529ebac0afda1a468befd4534edcc196b737e62ceae1bf02a4c73f8d079b
- 49b3c5991721fcb0ad9b2e65151c37d35c48fee9558acbb9652265417f06e566
- 4baeffdf44452fc62f5c9c14f99329a0d44245c14b5f2cddfcb113a8e09a5dcb
- 4fed4a7ade1fe8c0c3f76788dac4499cb769cd25aaa5556fefb268dbcdfd08be
- 510bd585e1a49af7ded8a0cc996783a93042cc4492c3e4bbac03befc2f2b8e62
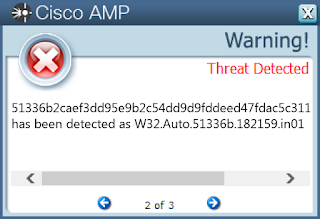
- 51336b2caef3dd95e9b2c54dd9d9fddeed47fdac5c31163cf2b291446e42f329
- 53feb1987eba78c921a683a57a75b6a455b7ad3087a7ddc287a33fbdf9c93c9a
- 5c5112540e79c47806dd35fc65bd351c82dfa6ff97faf0759330191fc54bd52e
- 63723f92c8c6121e428646c937b40745f4122748d9c949493d28e6b5542feefc
- 6990bd74cd90afa10eae1867763c2c0d83b88e27ebec7536039bc5567fe241d6
- 6a0ee362d1d633d42769865e14d2eb776903ebdaea809f08f048e0a79bcf0744
- 7464f1c4e20b3eb4bf4894a1ae0659e7898f276b48565a55c03b4b3b517c5fcf
Coverage
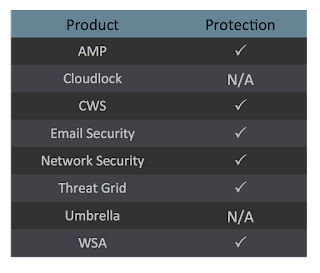
Screenshots of Detection AMP
ThreatGrid
Umbrella
Win.Malware.Gamarue-6615948-0
Indicators of Compromise
Registry Keys
- N/A Mutexes
- 3749282D282E1E80C56CAE5A IP Addresses
- N/A Domain Names
- ongertelles.com Files and or directories created
- %AppData%\D282E1
- %AppData%\D282E1\1E80C5.lck
- %AllUsersProfile%\Microsoft\Vault\AC658CB4-9126-49BD-B877-31EEDAB3F204\Policy.vpol
- %LocalAppData%\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28\Policy.vpol
- \PC*\MAILSLOT\NET\NETLOGON File Hashes
- 12f9752a1b9a35d5c8caecc5c8d0a443bf54aad5470bd7d00ee75fc018a39cdf
- 1e4d5ed6676259a1664729528025d741638c7294a7bf4145559893e004933ee2
- 6532e8315e7fd4a5e82bba7971f4c434e3c3c417dba41fee512fa51245686fd1
- bff1dbf4c514881537694fd27bf3baac1bc52c5a6c617b5d28b526e0ecd62aee
- c79e2c39343f78b05a45509bd8e407e9c7ea92456905b4d392a1a425d3dfce11
- d180cd252c0d7574a0805a8c2bb3f4a9ca6b0a85ef8d46a0b3941e6ce8b514a4
Coverage
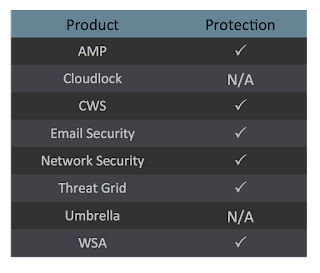
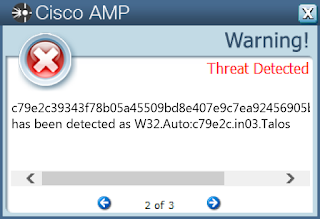
Screenshots of Detection AMP
ThreatGrid
Umbrella