Today, as we do every week, Talos is giving you a glimpse into the most prevalent threats we’ve observed this week — covering the dates between Aug. 24 and 31. As with previous roundups, this post isn’t meant to be an in-depth analysis. Instead, we will summarize the threats we’ve observed by highlighting key behavioral characteristics and indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net.
The most prevalent threats highlighted in this roundup are:
- Win.Dropper.Zusy-6664573-0
Dropper
Zusy is a trojan that injects itself into other Windows processes and the browser to steal valuable information. The malware also has anti-debugging and anti-VM capabilities. It contacts a hardcoded command and control (C2) server. - Win.Dropper.Zbot-6664565-0
Dropper
Zeus (AKA Zbot) is a trojan package used to carry out numerous malicious tasks. It is often used to steal banking information by man-in-the-browser keystroke logging and form grabbing. - Win.Dropper.Ponystealer-6664556-0
Dropper
This malware is a dropper for PonyStealer, a bot that attempts to steal passwords from web browsers, email clients, instant messaging applications and other software. - Win.Malware.Generic-6664552-0
Malware
This malware cluster leverages common Windows registry persistence techniques to execute malicious Visual Basic scripts and executables on the system. - Win.Dropper.Llac-6664551-0
Dropper
This malicious remote access tool (RAT) uses registry persistence and stores various data on the disk to exfil it to a C2 server. - Win.Dropper.Weecnaw-6649176-0
Dropper
Also known as Razy, is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host, formats and encrypts the data, and sends it to a C2 server.
Threats
Win.Dropper.Zusy-6664573-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: {AA2468DC-A531-6EB0-5169-325772D6D0FF} Mutexes
- Frz_State IP Addresses
- 23[.]253[.]126[.]58 Domain Names
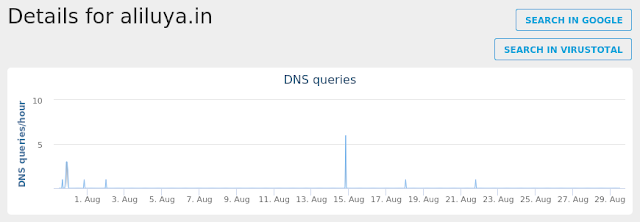
- aliluya[.]in Files and or directories created
- %LocalAppData%\Temp\~DFB720FA4531A3BD3A.TMP
- %LocalAppData%\Temp\tmpc080dd22.bat
- %AppData%\Media Center Programs\mgrMediaCenterPrograms.exe File Hashes
- 0086199586b4d80cf759ee7496d67106ea778c6d0d09b806af0d9942927b95a7
- 0b4d9d3231a26031b91afb86601e02ae8688311f4ad171a9ec7583df21035c4b
- 0c62bb710b7ae67438d05221daf95d71816591ec19add296e3c461ad6ac2ad89
- 1c40de31f1d99b153d9c1195e41873b064f28d1169376fb5989927fefb7e279e
- 1c6d8fd83497dade09939bda7e62803b3a271b0ddd91de8189666f2d33e52813
- 3256780354a83a758a07e4b705ad83be599edeebeb26ace0586913fabe4457bf
- 38184b0b4f6d7216d9d81a74af724285ae22c13c19d95e5f38703507d6abebe7
- 391e0759858ba5f58888afffc6b26594da9d79dbd8ba50c56828d7855d2e5ee9
- 56a4a40bccde01c52092ef1d5b241adac4ee7825d9556fdbef84c12c1feddc73
- 59c83f47fa21040feaf2885f4edebcb06eff21f24b9df980647e7a4d3fb9a2d0
- 5aa0c86a9e558671bd930e5a812b88ed19a7ebff291ed6b5a55c781b16dc7ea8
- 5e900d84431fcf62677eafa305ae03d03300c5fe74a98d825e3dfdf184c040b2
- 6963f52b20f628e9e31378ce0fdd3e2124010d8f775e05af3dab4a94b2a30b75
- 74d50d5b7c750105f2797bf2d145ff43eb0b2c76851b6c7de665464ec8642210
- 75872f30f9518032f327d82c602349f1cb304fc82a694d668ad7b5e0f6db2bf5
- 7636612f4b131119c7590757bc9c76b0fc3bbe40b8558b83b532ece91f6732b3
- 85f65115b4cdbb9401720770f1eaeca347b036694565d643c69d09b3be1e849a
- 928be3e04601466e47a567e422c7da279383bf6e23e513c352298a02d85823cb
- b323a535c8aee0c715e1a9821fe3d60c52a309ebf269b0173118dc91eaab700e
- b81bad519ab37a8b7ea6083113007202d6bdc52a357c4a82ab3433c3b1d86c6b
- cb6646bb13c59f72a36ef4c626dd93979caae8cdf26be0dd00be810af7d0cc53
- db942618b5b1a7c8d86b02aad84cde08642d482194104d194c9022216ca01234
- e0ed7aabff9ea95e2f839cad7acc9e7ffe2d2e458282b29c0d2db486c487a5d1
- e801b71fcb36a12a577668df03fd60ff1a4688fd8b4cbeb410d23731c5d62dcf
- eb5e76483e2c73c0a4a7c3701840ce932858268be01f4cda6dda69edd31e750a
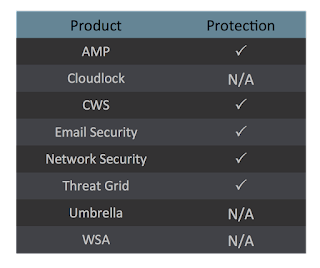
Coverage

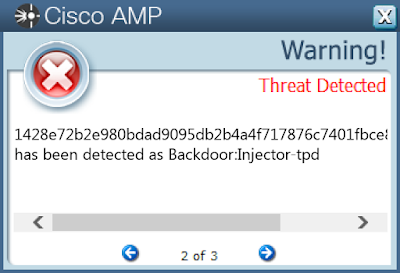
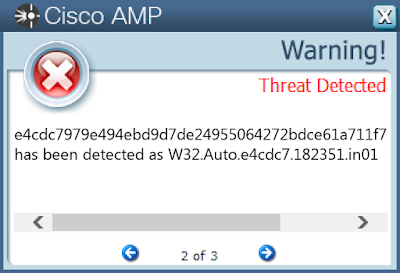
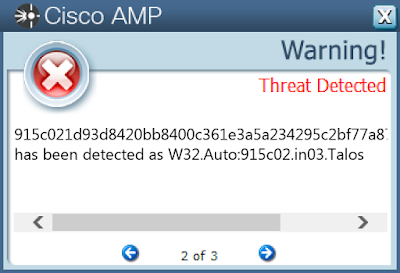
Screenshots of Detection AMP
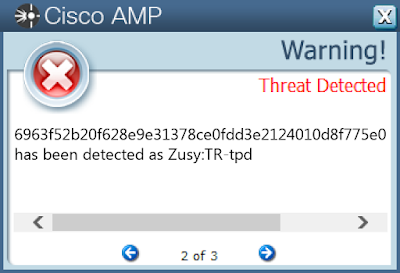
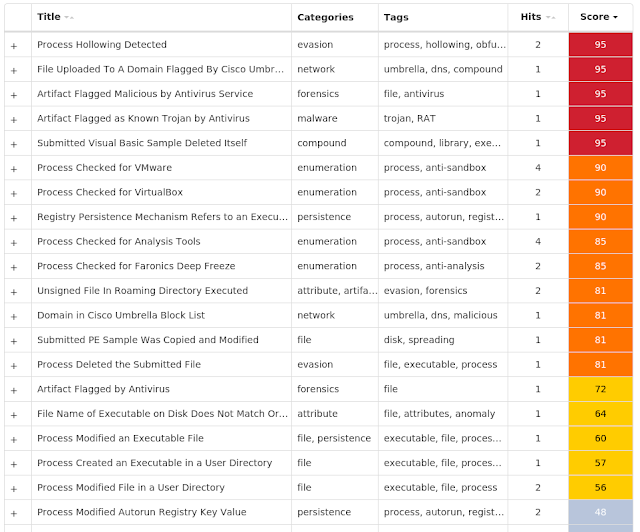
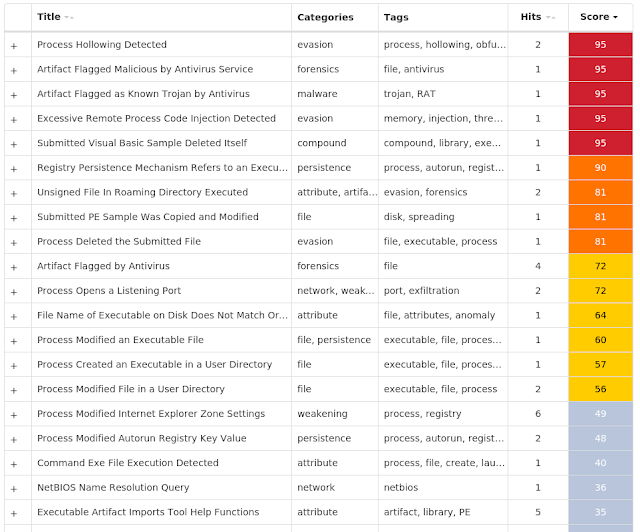
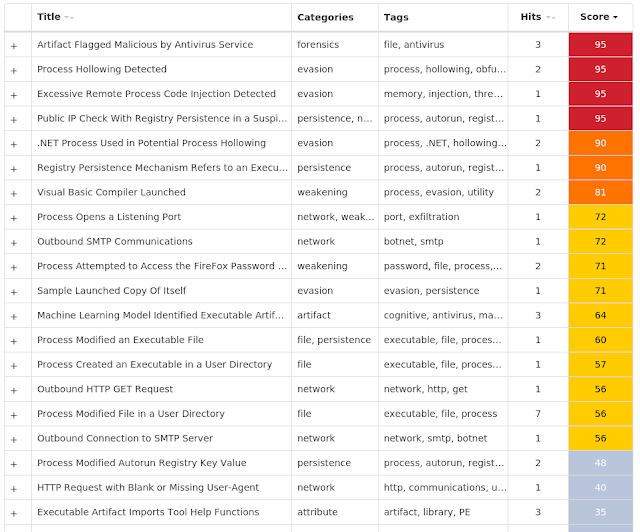
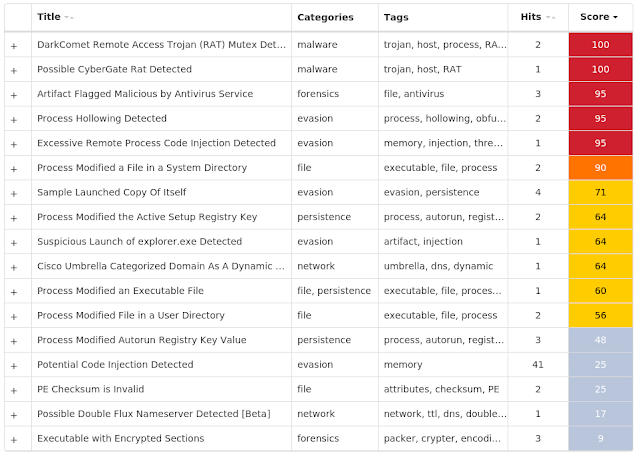
ThreatGrid
Umbrella
Win.Dropper.Zbot-6664565-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\INTERNET EXPLORER\PRIVACY
- Value Name: CleanCookies
- <HKCU>\SOFTWARE\MICROSOFT\SEUQV
- Value Name: Ugtu
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: {06D9E66C-0AFF-8E20-8FE8-15D3DC7C7959} Mutexes
- N/A IP Addresses
- N/A Domain Names
- neosz[.]org Files and or directories created
- %LocalAppData%\Temp\tmp8bb49f41.bat
- %AppData%\Xenyed
- %AppData%\Xenyed\ilcoa.exe
- %AppData%\Ymcap
- %AppData%\Ymcap\noapb.dat File Hashes
- 0285541620b688aac940d046ab3f4c7e60069512421ea353f4a556c5797fa9cf
- 07d1cf27ef446b7a9396f11ecbb3bff7a87af12aeee9fc883dffbd936cce57b4
- 095f4d3c133a236117fcc1c9f4ffac1dbe79da38d8f9e1dd29a60f24066875e6
- 1428e72b2e980bdad9095db2b4a4f717876c7401fbce8eaa89ab0c819ee757cd
- 282f842a03a9410b88b53f53bb63164a9c0a3f6da18e2f96591dac878ac7aa57
- 2878b048863aae2873ed90682fef68c8736188abd794f2c36b417e747edcfaed
- 28f8077f0bff09d8ea3da43c62872941219f1b6a982617df44b416279e3d349d
- 365ff8a7502272e69efe70386f40eb84a4098576564b188b41cec2c797b5d444
- 5ea643b56af71e4c3940a4796de973ab70e923b88a8d3b3e53c66cae64ea9a21
- 7230a35ea0eae6f00f6227eef9e1cb3fd0adf716bee3ff2e7285c9fc44209f28
- 731dc53c805261be26238ac99f28e5e505a0afe3396e18d76817330832b95815
- 856cf0c277af096077fe168c2036538c5d23f62eb125e6b63c48cfbf39c3507b
- de3bf89db7d8312fb6c9a6309ddda2ad8925915e57ae3509ffaa8e55a2479a7b
- ea8fa87b2501b9ac4d884fb53ec14fcf55f7877f68536640fd8c990f42997318
- f74da9f23d40cc7a7a6f513710a34e1693defa1b26356aaa5a93465454c900d3
Coverage

Screenshots of Detection AMP
ThreatGrid
Win.Dropper.Ponystealer-6664556-0
Indicators of Compromise
Registry Keys
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: AGP Manager
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value Name: AGP Manager.job
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value Name: AGP Manager.job.fp
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{2AED832F-FA37-41E1-9869-53556FC4E018}
- Value Name: Path
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{2AED832F-FA37-41E1-9869-53556FC4E018}
- Value Name: Hash
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\AGP MANAGER
- Value Name: Id
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\AGP MANAGER
- Value Name: Index
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{2AED832F-FA37-41E1-9869-53556FC4E018}
- Value Name: Triggers
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value Name: AGP Manager Task.job
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\COMPATIBILITYADAPTER\SIGNATURES
- Value Name: AGP Manager Task.job.fp
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{5BA6AC36-8FC9-4BF2-8699-D1C5E4B53ED2}
- Value Name: Path
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{5BA6AC36-8FC9-4BF2-8699-D1C5E4B53ED2}
- Value Name: Hash
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\AGP MANAGER TASK
- Value Name: Index
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\AGP MANAGER TASK
- Value Name: Id
- <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{5BA6AC36-8FC9-4BF2-8699-D1C5E4B53ED2}
- Value Name: Triggers
- <HKLM>\Software\Wow6432Node\Microsoft\Windows Script Host\Settings
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
- Value Name: calenderfile
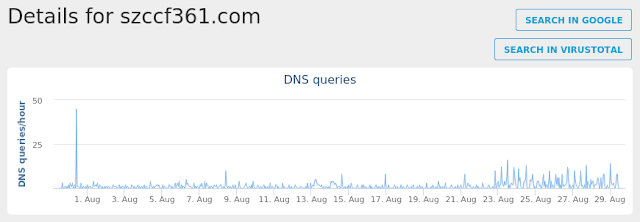
- <HKLM>\http://szccf361.com//trqcer/xx/les/fre.php Mutexes
- 3749282D282E1E80C56CAE5A
- CKVXlxMv IP Addresses
- 185[.]148[.]241[.]42 Domain Names
- szccf361[.]com Files and or directories created
- %LocalAppData%\Temp\subfolder
- %LocalAppData%\Temp\subfolder\calenderfile.scr
- %ProgramFiles% (x86)\AGP Manager
- %LocalAppData%\Temp\subfolder\calenderfile.vbs
- %ProgramFiles% (x86)\AGP Manager\agpmgr.exe
- %AppData%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5
- %AppData%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\Logs
- %AppData%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\Logs\Administrator
- %AppData%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\run.dat
- %System32%\Tasks\AGP Manager
- %System32%\Tasks\AGP Manager Task
- %AppData%\D282E1
- %AppData%\D282E1\1E80C5.lck
- %LocalAppData%\Temp\tmpA720.tmp
- %AppData%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\task.dat
- %LocalAppData%\Temp\subfolder\.IgHiJkLiO
- %LocalAppData%\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28\Policy.vpol
- \PC*\MAILSLOT\NET\NETLOGON File Hashes
- 36d338d4e27b80b605a8f41e6d5466c6c091f850460ad3438307fa310fee6124
- 37b97f4b355b4d5b8515afaac65be8d472739af29b0ae710af1cd7f3c72ada90
- 3db230f77666811830da80b685fce292b9f193e022dce1d4038cc8b9589ce9ea
- 4dc0fcb41a2337adf6ae7298d7c3d149690c424405da81691847d7a9dcfe0cd2
- 5b35f219098af55485f255877b0e00625ead753d08242496e74ca65d544ff32a
- 68dea7453ba1ffd5706fe544c18c0a74b6ed307b02591a5b12e9029ce0673cd6
- 7128acdf0af3ca1168c44a3440992dc118acaf21fa9e4fa7e9a49a22a87d8cd6
- 741d126dae4e162b0108c30336b9a2e85c3260b321e027f02150fe8c29a54e42
- 7ebb784df21a85f511a70c9914e42cca0f1634bbb54d83214719eba28d25076b
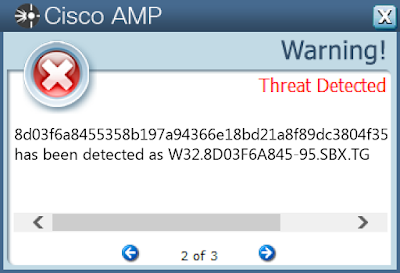
- 8d03f6a8455358b197a94366e18bd21a8f89dc3804f35b7c065b6fe3b28fdd44
- d6fd60308a1c812fae450e731dd184e33ed0d0a3c73fb7b99c35edfa174e22ac
- e3cb0f6d1f1d9dca58775aa58add608f67e32195bd53e9e9c00f720909ed80a1
- f793a85bfb4cd6ea3d8928d12ce678250a69bb210880901417508d52cca7cc75
- feee147fb9042914d58c0bdade8a314bb89e710b78cb6d3a9d4511e033e544e0
Coverage

Screenshots of Detection AMP
ThreatGrid
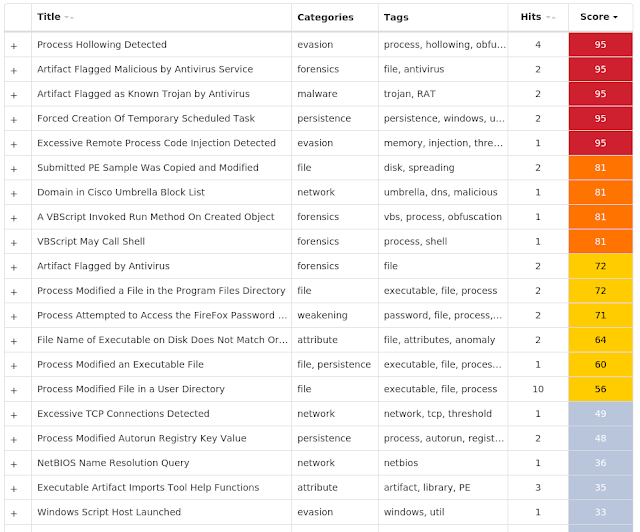
Umbrella
Win.Malware.Generic-6664552-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
- Value Name: Registry Key Name
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\ADVANCED
- Value Name: Hidden
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: Windows Update
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: Microsoft HD Video Card Mutexes
- Remcos_Mutex_Inj
- remcos_fpvcewmpthnemuo IP Addresses
- 104[.]16[.]16[.]96
- 77[.]79[.]239[.]196 Domain Names
- whatismyipaddress[.]com
- mail[.]alltracklogistic[.]com Files and or directories created
- %LocalAppData%\Temp\subfolder
- %LocalAppData%\Temp\subfolder\filename.exe
- %LocalAppData%\Temp\holderwb.txt
- %AppData%\WindowsUpdate.exe
- %AppData%\pid.txt
- %AppData%\pidloc.txt
- %AppData%\Microsoft\Vault
- %LocalAppData%\Temp\~DFDC33AF0144AFBF01.TMP
- %LocalAppData%\Temp\subfolder\filename.vbs
- %LocalAppData%\Temp\~DF3457B4150AFB88CA.TMP
- %LocalAppData%\Temp\~DF72CB1D21ECC44F9B.TMP
- %LocalAppData%\Temp\hkj.exe
- %LocalAppData%\Temp\~DF0A22527376F8AA09.TMP
- %LocalAppData%\Temp\install.bat
- %AppData%\Microsoft HD Video Card\Microsoft HD Video Card.exe
- %LocalAppData%\Temp\bhv11EA.tmp File Hashes
- 051b5663a5fd0aa611ccbbb92e385264b59e9495441b9412edc34ab6903f5177
- 0a13fbebefbb460de7565dfc7fd6b86674daecd42cfed4626ddcfe303d2b9670
- 237d9e85b5ebcacc0548757b50563c88e48495c942ecc34ae4dc70fd17f0e56c
- 43ff3bcd5e6161b482ebe381ccfdd5f25ad22e193172b4fbd2b42848e66fcc84
- 46fc6e30280595dae36c09e87be036859c91a75ea2cb7b30af667513754b4d61
- 52b3c994dd4e7d96b1806757af2ffae399559d2d4602facffbe5c20646a5d280
- 5693932850faa2d97f61a24c1dbf519fc44cc911b148a786a7b322c5d05d3cde
- 63abb6b27f686a6daf0efbb37ee8a881c70c4a786e69a18761c6aa69be026757
- 6d32d47f05162c9da374f9d5c1c003022b667a26bc130154fd2e8e785b499b39
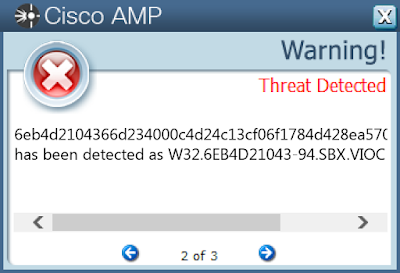
- 6eb4d2104366d234000c4d24c13cf06f1784d428ea5700ab9a3171fb1d2499e1
- 8af8918383a6e8ae0426630aaafbdccb248d4661e392f0504bbc0dc3d942604c
- 8c966864d1115d71e2b6e96bb967ab849f6610f338e6fd3022c51fcf897dcd1f
- 9128bbb89e8497bff023af7f28187e5a9e98ff16534dbd3bbdcc2d5bbfcc66c9
- b070efa747e400efbf06aae4cc012e7793ca2773827207a773b6406eb5c09212
- ba06d969cfcc69452153a2f453520cc981680b79402419b018bf97552d1be97a
- c60c3ac771ccb72ba788e04d4add83786e26dfc54720c5270654b9215acbe0c0
- dbb9c698f74f9f113a444fba6e17e5c4931f6eebd1739465ea308d74ba827645
- e5156c3d6ea2b87371fe57aae68d5cc4b63dd0c8f6bcf651c56a2f6906d9f996
- ed12f4bb9e9157815266d0f14f707d72f72894043bef1116704e7b45e5704a2c
- f1d8d1363534e62e43213a0b625507aeb24f669ff65efdd6f414f769336b4841
- f2cdc306085686d1e8f38234f6a8a0ec9cfcc0f00dbcb81106b20807bd1ab5d3
- fdbb0b36d904b56348382ae39d2ca39347485f1ca6365c87b1b54bb6ea0dbc41
Coverage
Screenshots of Detection AMP
ThreatGrid
Win.Dropper.Llac-6664551-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKLM>\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN
- Value Name: Policies
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: HKLM
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{537S174K-BM25-YPUH-7HFF-B4DP4K21I7TL}
- Value Name: StubPath
- <HKCU>\SOFTWARE\DREGRESS@HOTMAIL.COM
- Value Name: FirstExecution
- <HKCU>\SOFTWARE\DREGRESS@HOTMAIL.COM
- Value Name: NewIdentification
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\EXPLORER_RASAPI32
- Value Name: EnableFileTracing Mutexes
- _SHuassist.mtx
- WlekOENFlw
- WlekOENFlw_PERSIST
- _x_X_BLOCKMOUSE_X_x_
- _x_X_PASSWORDLIST_X_x_
- _x_X_UPDATE_X_x_
- WlekOENFlw_SAIR IP Addresses
- N/A Domain Names
- dregress[.]no-ip[.]biz Files and or directories created
- %LocalAppData%\Temp\XX--XX--XX.txt
- %AppData%\system32\
- %AppData%\system32\explorer.exe
- %LocalAppData%\Temp\UuU.uUu
- %LocalAppData%\Temp\XxX.xXx
- %AppData%\logs.dat File Hashes
- 5d3e533eddbec63bf8a4e4f55c2c92fdcaf55c48c8ced978fe9b2120ba8c978b
- 640f20202437cfda4b49cdf95dd3760ec3d76f23e5c473c568835c5e5b5ae721
- 67d07d8a0a78428347447f235a18804a9d9d814066c9dc4116d1581c2000d5ae
- 7c86998390a89147d142c1a3914d80cd648bbba9c07dc10a4fb6deee6b81b720
- 97fabe289c0d778fee300c7b52ad5013ac85bd2a39c3f724d458f4e9268738c6
- 9817dbfcf5e3136708c26171089ce0b55304a3b2165ddd85d02ee5188de05d41
- c070bcdf59f548025ad1b12dc1c33699a24963ef7bd4bc88bf29322551dbc440
- c76f9440d9f992954629a87620da8ef23f2a565870483242cb988eb0aa147743
- c86b94bcf90b4bb6a6318c22c1eaec125b7329e988fa20bc76e02f072806c288
- c8e13a8e304358e9b3b337c6a0dd8c8ade371078f153130474f83af7917e845d
- d90c74e44e999784659ae92d5b4a71095f66eb2a8a750f6fda17976ead3e0658
- e4cdc7979e494ebd9d7de24955064272bdce61a711f70ff32925b4b47c9320e9
Coverage
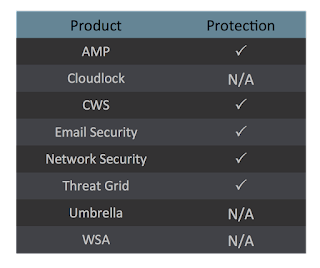
Screenshots of Detection AMP
ThreatGrid
Win.Dropper.Weecnaw-6649176-0
Indicators of Compromise
Registry Keys
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: internat.exe
- <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
- Value Name: Avast
- <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{I8877104-6125-5WU7-VAYG-S5K3CM2I1XV8}
- Value Name: StubPathMutexes
- iTCUfMuY IP Addresses
- 91[.]192[.]100[.]3 Domain Names
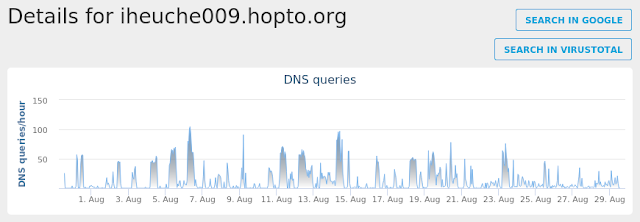
- iheuche009[.]hopto[.]org Files and or directories created
- %AppData%\Install
- %AppData%\Install\Host.exe File Hashes
- 00e3f5ffeb38495cefce0f1c9522743764adf1ee6ce51b91c9c4726726562a12
- 01a7bdfdc6502db6bd237fcbc64596d8f76052e942c2c87e897f1ae786b7cac2
- 02c5fa1012b9cf0d46801cadcc4fe6814b4f75d50104e948031d00ff3ca7b93c
- 035f91568ca2bad43ce3fde98a2ae0418821e5f558c62b919c786c3b07bc0fe2
- 03970d185025e7e226c704b5bcd13de89730677345d3d57081d07895966567d4
- 055865fb005e3969e6d9e7feba2e81a8bedbe3048bf2a9cd3a9fbfe8ea6076e5
- 063e213ee0ecae95132a3cea557203b782de3c63b753fbd405ed670e83fbf573
- 081fbe8f1c01676f9765ff7742b5d348433e2fd073136355100fe9f054140e6a
- 08c257d2e5938dc6539b463ba0689982b79c112c8ad0aaf1be247726622ea487
- 09c9b81d40f3c97876eaad0f29d7e9694c58c9a9cc4dc38b167611ecfbda3d75
- 0a032738a8ffc58b6cdce62ef209b247e008f597b6955d87da71e1654da970ef
- 0afde5386ca8587bca67577727f02c3e71b883b7b5fc72e25a0d542f6c5819c8
- 0f4fc18209bbb1d979cb504b807142e1a24aa8ee831e33ce8825a5bd350096fa
- 10427e9a0ee1b4e3d349d61839e1f09cb86b2a68d23e41933127dd5ce2da0134
- 1343648c8b4748294191cfdca4b4881a57cee96db4051530c514e7c56e1152e3
- 17983b493cd46b604ef3846516da1cda1628ec855b896be8b54a9558ae83058c
- 1bb84d812e0863ce21398678bf8facfe6864a33237d67d3416fbcab73226bdbe
- 1cb1870d583bef0aa1dbb99b30f0819b7490855786a85c5969be925b2719c6be
- 1fbac835a770d9b309ed87d3df0746bd28f1033f366ab35cde9e165f2b069388
- 260eaee5c9e8a7effb1698f670464e9b6aad29244dcb16434af489e65adc6d6c
- 2af2ef163e2035d3503ac8af23ffe8be8ca286dbf9c96aac6c8cebb61e9551c1
- 2b65d21294f9a06d570811d2e7aeec7ab4785e8840d79e8083791cc3684e4a92
- 2e7e5b2ac10a3591ab570028b6a230d51f117e1842b6d11f56499785c6faa1c6
- 2f0184defca0e2583f65e1e6d244a9e3cef8e3c83d02282ef797d97ee784869d
- 3276ac34b3c9f03cb9f1a259ed09043083e3adeaa82a41fc2dccfc51f20570c7
Coverage

Screenshots of DetectionAMP
ThreatGrid
Umbrella