Today, Talos is publishing a glimpse into the most prevalent threats we've observed between July 5 and July 12. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org, or ClamAV.net. here that includes the complete list of file hashes, as well as all other IOCs from this post. As always, please remember that all IOCs contained in this document are indicators, and one single IOC does not indicated maliciousness.
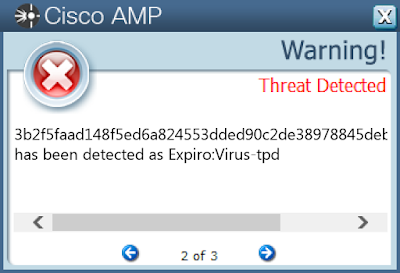
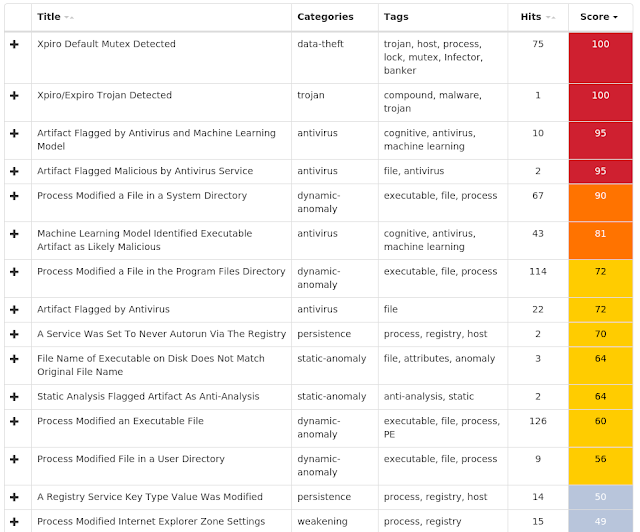
Threat Name Type Description Win.Virus.Expiro-7011826-0
Virus
Expiro is a known file infector and information-stealer that hinders analysis with anti-debugging and anti-analysis tricks.
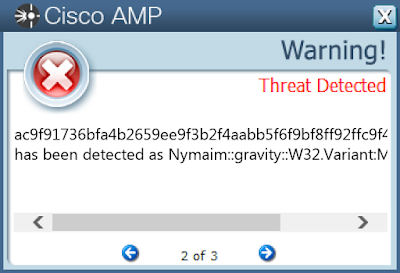
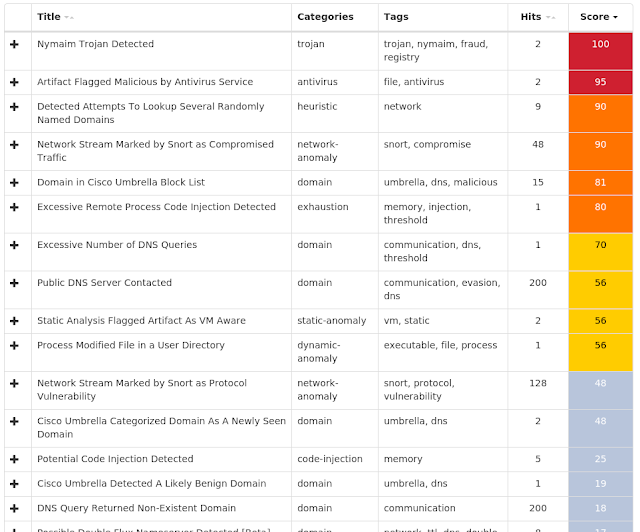
Win.Dropper.Nymaim-7011878-0
Dropper
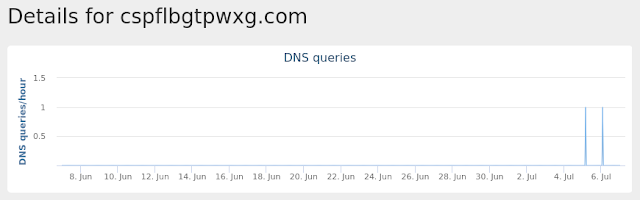
Nymaim is malware that can be used to deliver ransomware and other malicious payloads. It uses a domain generation algorithm to generate potential command and control (C2) domains to connect to additional payloads.
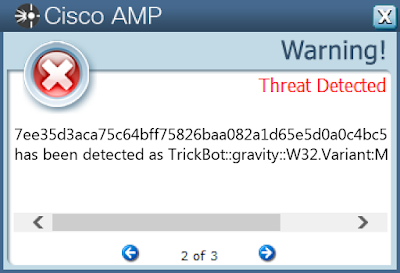
Win.Dropper.TrickBot-7011945-0
Dropper
Trickbot is a banking trojan targeting sensitive information for select financial institutions. This malware is frequently distributed through malicious spam campaigns. Many of these campaigns rely on downloaders for distribution, such as VB Scripts.
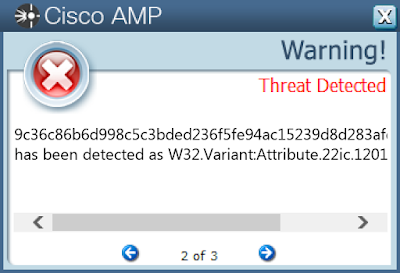
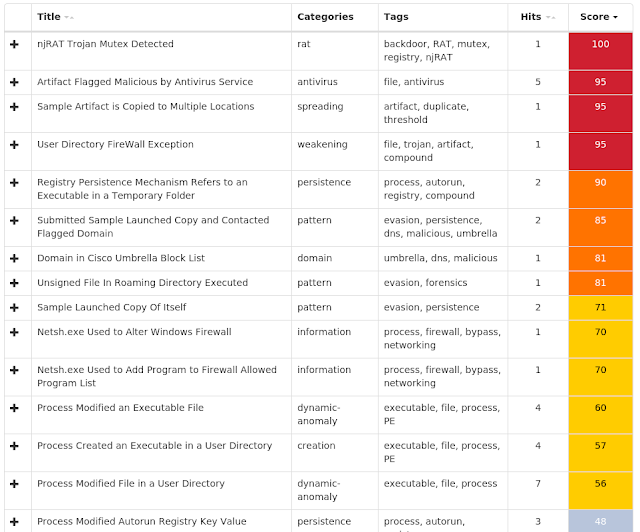
Win.Malware.njRAT-7011967-1
Malware
njRAT, also known as Bladabindi, is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes and remotely turn on the victim's webcam and microphone. njRAT was developed by the Sparclyheason group. Some of the largest attacks using this malware date back to 2014.
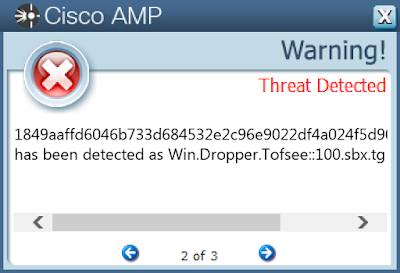
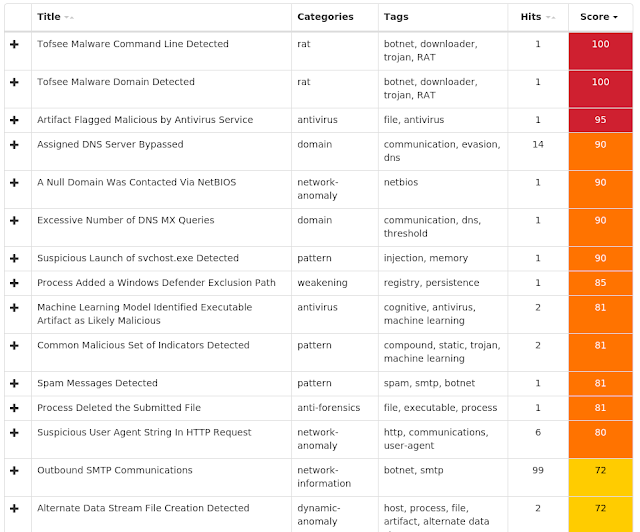
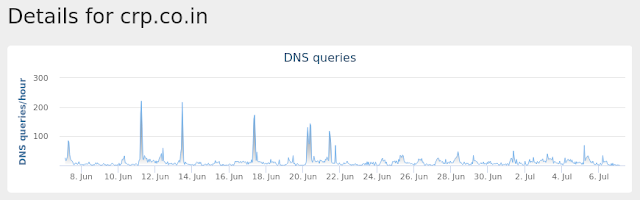
Win.Malware.Tofsee-7012060-0
Malware
Tofsee is multi-purpose malware that features a number of modules used to carry out various activities, such as sending spam messages, conducting click fraud, mining cryptocurrency, and more. Infected systems become part of the Tofsee spam botnet and are used to send large volumes of spam messages in an effort to infect additional systems and increase the overall size of the botnet under the operator’s control.
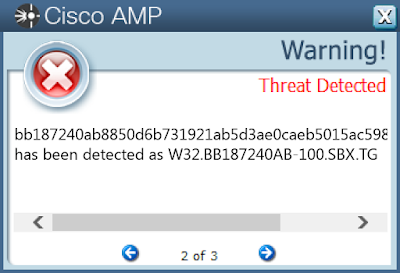
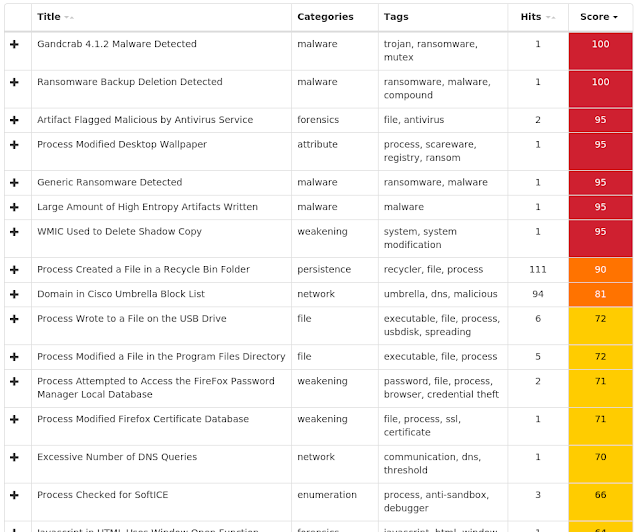
Win.Ransomware.Gandcrab-7012204-0
Ransomware
GandCrab is ransomware that encrypts documents, photos, databases and other important files typically using the file extension ".GDCB", ".CRAB" or ".KRAB." GandCrab is spread through both traditional spam campaigns, as well as multiple exploit kits, including Rig and GrandSoft.
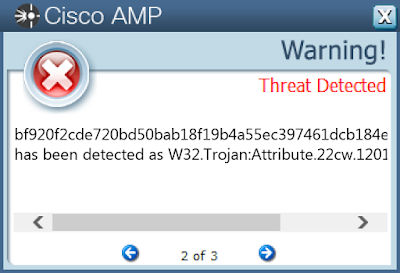
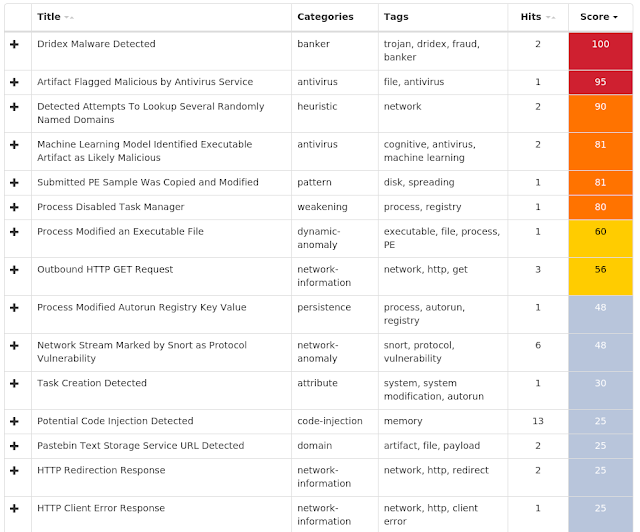
Win.Packed.Xcnfe-7012508-0
Packed
This cluster provides generic detection for the Dridex banking trojan that's downloaded onto a target's machine.
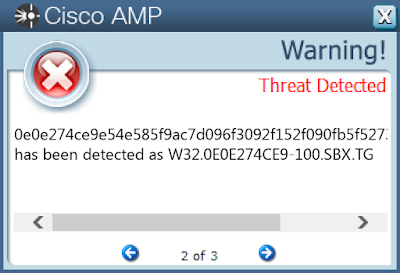
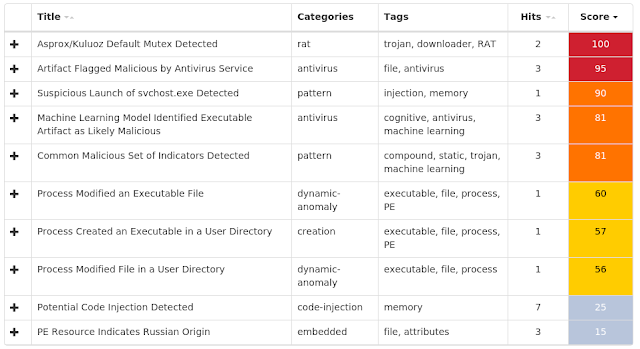
Win.Packed.Kuluoz-7051229-0
Packed
Kuluoz, sometimes known as "Asprox," is a modular remote access trojan that is also known to download and execute follow-on malware, such as fake antivirus software. Kuluoz is often delivered via spam emails pretending to be shipment delivery notifications or flight booking confirmations.
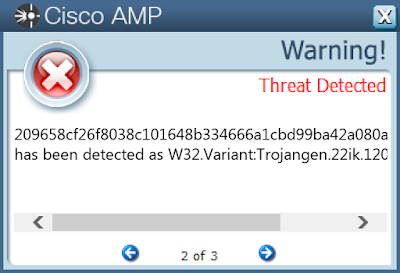
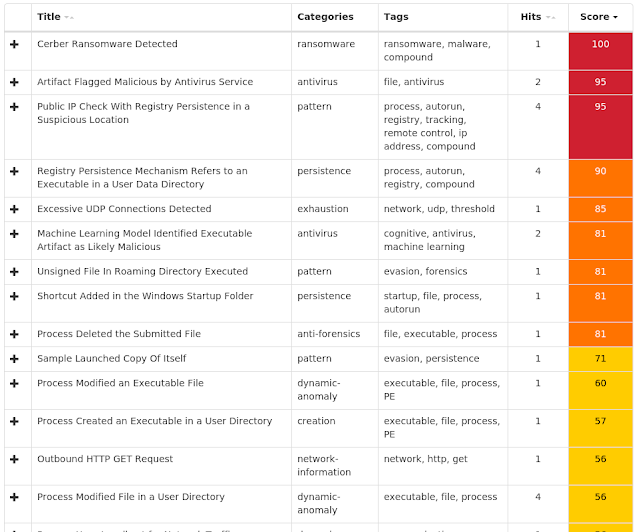
Win.Ransomware.Cerber-7052005-0
Ransomware
Cerber is ransomware that encrypts documents, photos, databases and other important files using the file extension ".cerber."
Threat Breakdown Win.Virus.Expiro-7011826-0 Indicators of Compromise Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WINDEFEND
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V2.0.50727_32
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V2.0.50727_32
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V2.0.50727_64
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V2.0.50727_64
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V4.0.30319_32
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V4.0.30319_32
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V4.0.30319_64
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V4.0.30319_64
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\COMSYSAPP
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\COMSYSAPP
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\IEETWCOLLECTORSERVICE
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\IEETWCOLLECTORSERVICE
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MOZILLAMAINTENANCE
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MOZILLAMAINTENANCE
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSISERVER
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSISERVER
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\OSE
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\OSE
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\UI0DETECT
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\UI0DETECT
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\VDS
Value Name: Type
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\VDS
Value Name: Start
27
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\VSS
Value Name: Type
27
Mutexes Occurrences kkq-vx_mtx1
27
gazavat-svc
27
kkq-vx_mtx64
27
kkq-vx_mtx65
27
kkq-vx_mtx66
27
kkq-vx_mtx67
27
kkq-vx_mtx68
27
kkq-vx_mtx69
27
kkq-vx_mtx70
27
kkq-vx_mtx71
27
kkq-vx_mtx72
27
kkq-vx_mtx73
27
kkq-vx_mtx74
27
kkq-vx_mtx75
27
kkq-vx_mtx76
27
kkq-vx_mtx77
27
kkq-vx_mtx78
27
kkq-vx_mtx79
27
kkq-vx_mtx80
27
kkq-vx_mtx81
27
kkq-vx_mtx82
27
kkq-vx_mtx83
27
kkq-vx_mtx84
27
kkq-vx_mtx85
27
kkq-vx_mtx86
27
*See JSON for more IOCs
Files and or directories created Occurrences \MSOCache\All Users\{90140000-0115-0409-0000-0000000FF1CE}-C\dwtrig20.vir
27
\MSOCache\All Users\{91140000-0011-0000-0000-0000000FF1CE}-C\ose.vir
27
\MSOCache\All Users\{91140000-0011-0000-0000-0000000FF1CE}-C\setup.vir
27
%CommonProgramFiles%\Microsoft Shared\VSTO\10.0\VSTOInstaller.vir
27
%CommonProgramFiles%\Microsoft Shared\ink\ConvertInkStore.vir
27
%CommonProgramFiles%\Microsoft Shared\ink\InputPersonalization.vir
27
%CommonProgramFiles%\Microsoft Shared\ink\ShapeCollector.vir
27
%CommonProgramFiles%\Microsoft Shared\ink\TabTip.vir
27
%CommonProgramFiles%\Microsoft Shared\ink\mip.vir
27
%ProgramFiles%\DVD Maker\DVDMaker.vir
27
%ProgramFiles%\Internet Explorer\ieinstal.vir
27
%ProgramFiles%\Internet Explorer\ielowutil.vir
27
%ProgramFiles%\Internet Explorer\iexplore.vir
27
%ProgramFiles%\Java\jre6\bin\java.vir
27
%ProgramFiles%\Java\jre6\bin\javaw.vir
27
%ProgramFiles%\Java\jre6\bin\javaws.vir
27
%ProgramFiles%\Java\jre6\bin\unpack200.vir
27
%ProgramFiles%\Java\jre7\bin\jabswitch.vir
27
%ProgramFiles%\Java\jre7\bin\java.vir
27
%ProgramFiles%\Java\jre7\bin\javacpl.vir
27
%ProgramFiles%\Java\jre7\bin\javaw.vir
27
%ProgramFiles%\Java\jre7\bin\javaws.vir
27
%ProgramFiles%\Java\jre7\bin\jp2launcher.vir
27
%ProgramFiles%\Java\jre7\bin\ssvagent.vir
27
%ProgramFiles%\Java\jre7\bin\unpack200.vir
27
*See JSON for more IOCs
File Hashes 0f11058b9bb9dce7014b474d85d37f38fef0c65ed40d4cba8045d37728cc3127
12b6dcadcf34533c756995f06ca4c874b355e9fe44fda55f8313e2cfb126b419
1a4c6b55be877c65e946d24812000fb8dfccbdfe19be1b8acc67bce8b4893743
2458be6e8b13f29643ab1bbb040b78d1a94e55e50146eade0a705740eebf054a
26dcb212b2eace9a14bc33b421505143fa0a247df2418b575046df6ef80ee6a9
288fb9363990e5cbbad51e4e0436b4ea69a1cf148dbabae124ffd00151b7bc33
32beb33b4e36b69c79c50928e05d24a8f175d25701bb507e1ad03cdf70b63f3f
3550e5495f8922d17929b8a9bac9c23135d1418356b82576c7dd0a4f15aa95f6
3b2f5faad148f5ed6a824553dded90c2de38978845deb2fbdf99816cabfb8854
4624f0bdb4bb2092cfc73dbd30f7ab61403a0d1c60bef5290c6ed9fe60bff849
47b7d95889199a717407c7a6e8278f5ab9a32c499aabe9930da52f9051304ff2
535bb9df4d41d57fc44572ebc1a535ac726546a41a8b2fcf3b904ed037a96db6
552a987dd3722960cba7fd8c4fc1cd36cc5bf2668c9f0ffe5b452eecdc1824e9
5f998984132fabb1879ddca658baa12d891afbbfd0738d2a2063a491be833a0a
6669a807690556293a60830285c9c2c9ad52842a1c7646e99852724b1b049ab0
67dc0704b4393c6dc523756d107279340eaba04a62d49048588ecd4be5a88aac
6c0f5ca1ab0562b3c285c5556f1a68fbe8a2a5fcec892bbd8333c8a6414c46d8
6cf2f544a52878b86e09d4a6938949fffb1b65c2afae49241c99913e3046baa3
7057f866649141c5f09b96dbece2db447ac2ef1a25ea992d16cc1f44afe9622e
710a3ca2a0030b4b064dc29da045ab7ff61a5f1a5cf11b100ab89a9b1d9ffc83
7327a9114c1facf322d5c31744aa1199a15ba9f57825650b3a548495630c1d63
73aa657a49c7c13b1c0727c05ef7d51fe9fd138862c15fdcc0fd64cdb06ece8d
79732b1aeb27cb1ead7ab37e4681c96d5f97d9e72c6a934b779f05fd82c51473
8de151ef4f21b6e74cc96403debbdd50ecb97299cac0fa7dc988dba68e30c44b
8ef41dc44a6c264c6c475b4d24ad44649a15f4bbbb4e237580621865361b995b*See JSON for more IOCs
Coverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
Wsa
N/A
Screenshots of Detection AMP ThreatGrid Win.Dropper.Nymaim-7011878-0 Indicators of Compromise Registry Keys Occurrences <HKCU>\Software\Microsoft\GOCFK
23
<HKCU>\SOFTWARE\MICROSOFT\GOCFK
Value Name: mbijg
23
Mutexes Occurrences Local\{369514D7-C789-5986-2D19-AB81D1DD3BA1}
23
Local\{D0BDC0D1-57A4-C2CF-6C93-0085B58FFA2A}
23
Local\{F04311D2-A565-19AE-AB73-281BA7FE97B5}
23
Local\{F6F578C7-92FE-B7B1-40CF-049F3710A368}
23
Local\{306BA354-8414-ABA3-77E9-7A7F347C71F4}
23
Local\{F58B5142-BC49-9662-B172-EA3D10CAA47A}
23
Local\{C170B740-57D9-9B0B-7A4E-7D6ABFCDE15D}
23
Local\{B888AC68-15DA-9362-2153-60CCDE3753D5}
23
Local\{2DB629D3-9CAA-6933-9C2E-D40B0ACCAC9E}
23
Domain Names contacted by malware. Does not indicate maliciousness Occurrences xunveu[.]in
22
rerbitzfyff[.]in
22
uwsmf[.]net
22
utgwcrp[.]com
22
xyiubkksjo[.]pw
22
octvwlg[.]net
22
mzutglz[.]com
22
bjgouvf[.]net
22
ulgug[.]in
22
bybxug[.]pw
22
ilqmz[.]com
22
wnckjojra[.]net
22
vncya[.]in
22
mzpgaccm[.]in
22
cspflbgtpwxg[.]com
22
pcarbnracpll[.]in
20
hnmkptaybcf[.]pw
20
ypgfnvixxaw[.]in
20
emuakrgqzg[.]pw
20
ucwwhvxji[.]com
20
rinzevlc[.]net
20
zdlvqrnmf[.]net
20
chavpayztnex[.]net
20
fwceecdhnnph[.]net
20
xlwzoffpooo[.]com
20
*See JSON for more IOCs
Files and or directories created Occurrences %ProgramData%\ph
23
%ProgramData%\ph\fktiipx.ftf
23
%TEMP%\gocf.ksv
23
%ProgramData%\l4szb
23
%LOCALAPPDATA%\15rdg
23
%APPDATA%\4fo
23
%TEMP%\fro.dfx
20
\Documents and Settings\All Users\pxs\pil.ohu
20
%TEMP%\bpnb.skg
10
%TEMP%\wghpl.bqj
1
\Documents and Settings\All Users\akt\aaq.hcr
1
%TEMP%\mfw.cac
1
\Documents and Settings\All Users\yvn\uwawv.hnd
1
File Hashes 21ca501957eb98d23abf16f253027ccf878f8045408dfefe9428df4357d8e4ac
2c7e7c4b50c4eccd7d68eb6aeea2a234a8b6f16cbc82740f85cf950755195aed
2f281ae6cd2f21d87ddd323ea4f1fe37949fd97e9d8fd69019c88754537dbd69
4e242fcebfb964c32ae3d53ac0bb5d85ff940cd58e26733bb677c4fafbd1c7c7
59a7dd286660811bb00e121c3e46c7e591f28e73fffa1d0b2b90eedb8a7824b1
5f4333e507e6d1868060e38423f036facc05cb30b863bef129ecf4db8c45470f
6b21c1f71ee50d296c0ada1d6c8924388b2049556c67966d8a4fcb513ad5afea
829e62346b8b1c58fa10995003137254a9c30f03154875c66b881c9ea6f45e5e
8da1535783ed2194ae6751f2a62964e0969758caa84e24cffaca42dd801e2c11
936179c3eccc864f82de20a7e7620679b78f4439a06b954afea38e81e8dc4597
a1099ca231637ee33617ec9fd3751bc79780a1e4cf5b27a320d8350f83520f86
a3a7b86869d6a01fd9ec3f91b909b40d82e1f970b7d5760c213a6cc7744fc33a
a44b775b0768448ba60a004e452d0b3b36fbd92bf68ad97095a7b2fbad4df0c0
ac9f91736bfa4b2659ee9f3b2f4aabb5f6f9bf8ff92ffc9f4b1eb597c97b7580
b0b4f210c37edf202d27069530d03f808cb72c5103adab2c964d7e35fc372ec0
b516d410b359b11a05a0e94f39cfb7671139899bff1e1aa08dcaf8440c8c5f97
b8d03c79b54cca29f77504b224ec785ca19c735d9137a3c0265066711c6a658e
c33f524a6bbde609dda5ebe36ab56d4c8963a9099446e8da94ea4e48531aa4d8
c50561443829e85ed8477ebab944e1fb44f36d1cf1148f6b1d2c9e4fe95454b1
c855e4b372f4bc3a66c9da5ffa57e39a95fe024bf11d5008097010adcb3a93a1
cd38e469faf445589dd68e69ee193533d86945355019b37f93f1232c0e337b71
f1553bddcfd8a3b662251154296dbac605b1e45e3cdab36af876fb431f0f6c71
f9548073e75760af718afb6466557ef52f84e0f43591b7b44e1f090b590ed6dbCoverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
Wsa
Screenshots of Detection AMP ThreatGrid Umbrella Win.Dropper.TrickBot-7011945-0 Indicators of Compromise Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\AUTHROOT\CERTIFICATES\DAC9024F54D8F6DF94935FB1732638CA6AD77C13
Value Name: Blob
10
<HKLM>\SOFTWARE\Policies\Microsoft\Windows Defender
2
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Users\Administrator\AppData\Roaming\services\
2
<HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Users\Administrator\AppData\Roaming\services\
2
<HKLM>\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions
2
<HKLM>\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Paths
2
Mutexes Occurrences 316D1C7871E00
16
\BaseNamedObjects\785161C887200
9
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 216[.]239[.]34[.]21
4
37[.]230[.]115[.]129
4
78[.]155[.]207[.]143
4
193[.]233[.]62[.]131
4
195[.]133[.]196[.]219
3
200[.]111[.]97[.]235
3
186[.]68[.]120[.]16
3
37[.]230[.]115[.]171
3
37[.]230[.]115[.]133
3
62[.]69[.]241[.]103
3
216[.]239[.]36[.]21
2
23[.]21[.]121[.]219
2
50[.]16[.]229[.]140
2
94[.]103[.]80[.]16
2
216[.]239[.]32[.]21
1
34[.]233[.]102[.]38
1
198[.]27[.]74[.]146
1
104[.]20[.]17[.]242
1
216[.]239[.]38[.]21
1
54[.]235[.]124[.]112
1
52[.]206[.]161[.]133
1
104[.]20[.]16[.]242
1
94[.]127[.]111[.]14
1
184[.]73[.]220[.]206
1
46[.]30[.]45[.]208
1
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences ipecho[.]net
5
elb097307-934924932[.]us-east-1[.]elb[.]amazonaws[.]com
5
myexternalip[.]com
2
checkip[.]amazonaws[.]com
2
api[.]ipify[.]org
2
wtfismyip[.]com
1
ipinfo[.]io
1
icanhazip[.]com
1
Files and or directories created Occurrences Modules
16
client_id
16
group_tag
16
%System32%\Tasks\services update
16
%APPDATA%\localservice\client_id
14
%APPDATA%\localservice\group_tag
14
%APPDATA%\localservice
14
%SystemRoot%\Tasks\services update.job
9
%SystemRoot%\TEMP\~DFDA4328936B46A2E2.TMP
1
%SystemRoot%\TEMP\~DFBEE2068C496B9A0B.TMP
1
%SystemRoot%\TEMP\~DFE4F856122203E5A6.TMP
1
%SystemRoot%\TEMP\~DF95BC682C0250D9D0.TMP
1
%SystemRoot%\TEMP\~DF664B3409FD7DCCB3.TMP
1
%SystemRoot%\TEMP\~DF8B34B44DCAF0FAB3.TMP
1
%SystemRoot%\TEMP\~DFDFC8A9E27AB554F4.TMP
1
%SystemRoot%\TEMP\~DFE798A25A56E126CC.TMP
1
%SystemRoot%\TEMP\~DFCCEBCD519293AB68.TMP
1
%SystemRoot%\TEMP\~DF5DE8F500481F14C0.TMP
1
%SystemRoot%\TEMP\~DFB36F6F7DB9D671D4.TMP
1
%SystemRoot%\TEMP\~DF7A2364BFEF750112.TMP
1
%SystemRoot%\TEMP\~DF604668AE25DEDE76.TMP
1
%APPDATA%\localservice\82b686b66ad703470800edb64763f2b64e1cffaa6830accbe7ff8178e6b48724.exe
1
%SystemRoot%\TEMP\~DF7802BEE615801D53.TMP
1
%SystemRoot%\TEMP\~DF50F658542C3B5672.TMP
1
%SystemRoot%\TEMP\~DF5E22B8EF8D659CE2.TMP
1
*See JSON for more IOCs
File Hashes 008d13100397cf0ce26850e3bcbb5a8c2fc01502d9a2b452439c101aea7d0824
0214625318a30153d364581fb580334f05be63bd5a355cbf86f12be66461716d
11f8a050648d0b8c70d19a99c48aeb9ba0d893d348ee503b96313b4499d96c63
198311c124d55765d5488c44a27d94087c67599f88e7b7afdcce4a1bc936c0c3
36c46dd363ce161955f1fe561791fe7a6f923e8c185b8dd0408211d8001f3515
48994b0e9f9a32783b49759a81e09e818a0faad7b854f349819a0cca9e04ebbb
646d1f9f85c1d2db58748961f9c08147f011434cd79be11cafff4db43a10218a
6c0f7bb7d6d7782d9fbf4b5c9659a8e3502e7ad6ccdb9527311cbd554b716459
71d157b247885a9fac9d5a2de95d62675a2887bd539face9f6d97a749bf368a9
7ee35d3aca75c64bff75826baa082a1d65e5d0a0c4bc5a258d37d22facbaf159
82b686b66ad703470800edb64763f2b64e1cffaa6830accbe7ff8178e6b48724
928e054bade6765803e23936c60ede96cb02603eeecbd98abbef98f88d431c06
98a9522efeef7720f8ba8aad303259eb1e52b35d9b38cc5a44715439d4729b0e
a418ba3cb2818dba4487178db3ac2beabdbd73aec9a5ce38d93d7c3eeb998fba
ebe4c5cdda2437d323417c8d4e43a4fb973665c89a6a7dcf28c2ad0803612f5d
f01e645d797000911da3221face197fd3a6eeb12d2e6acc99b984236530d117bCoverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
Wsa
Screenshots of Detection AMP ThreatGrid Win.Malware.njRAT-7011967-1 Indicators of Compromise Registry Keys Occurrences <HKU>\S-1-5-21-2580483871-590521980-3826313501-500
Value Name: di
26
<HKCU>\ENVIRONMENT
Value Name: SEE_MASK_NOZONECHECKS
26
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON
Value Name: ParseAutoexec
26
<HKLM>\System\CurrentControlSet\Services\NapAgent\Shas
24
<HKLM>\System\CurrentControlSet\Services\NapAgent\Qecs
24
<HKLM>\System\CurrentControlSet\Services\NapAgent\LocalConfig
24
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\NAPAGENT\LOCALCONFIG\Enroll\HcsGroups
24
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\NAPAGENT\LOCALCONFIG\UI
24
<HKCU>\Software\3d115699981cee571b7b4f66ac05e68c
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 3d115699981cee571b7b4f66ac05e68c
7
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 3d115699981cee571b7b4f66ac05e68c
7
<HKCU>\SOFTWARE\3D115699981CEE571B7B4F66AC05E68C
Value Name: [kl]
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: d357c7c29de6f023d943a6a5749259b6
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: d357c7c29de6f023d943a6a5749259b6
1
<HKCU>\SOFTWARE\D357C7C29DE6F023D943A6A5749259B6
Value Name: [kl]
1
<HKCU>\Software\eecedbc08899b6053b2f68175c2ade9d
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: eecedbc08899b6053b2f68175c2ade9d
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: eecedbc08899b6053b2f68175c2ade9d
1
<HKCU>\SOFTWARE\EECEDBC08899B6053B2F68175C2ADE9D
Value Name: [kl]
1
<HKCU>\Software\cee69a9c58a2f342efc10ce9b61baf18
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: cee69a9c58a2f342efc10ce9b61baf18
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: cee69a9c58a2f342efc10ce9b61baf18
1
<HKCU>\SOFTWARE\CEE69A9C58A2F342EFC10CE9B61BAF18
Value Name: [kl]
1
<HKCU>\Software\c89d6f2f51b03aeeb600705006913620
1
<HKCU>\SOFTWARE\C89D6F2F51B03AEEB600705006913620
Value Name: [kl]
1
Mutexes Occurrences Unknown
26
Global\783b85a0-9df2-11e9-a007-00501e3ae7b5
26
3d115699981cee571b7b4f66ac05e68c
7
767e342b9464203399b874be2f756a33
1
88f1bb19962eeb60cb416d731fb26aea
1
e4147808b03abe9f0c3c590c783b5f67
1
cd37f8fb04904790aec64ec6b0296433
1
b2d5379932f9d6eda0b4b4e483e6f706
1
d1c945c77014d102f98a39383a30a06f
1
54652225b66d96cf87694edf842a80cd
1
43ea784f064f564187850c70cfe36c6e
1
d357c7c29de6f023d943a6a5749259b6
1
eecedbc08899b6053b2f68175c2ade9d
1
cee69a9c58a2f342efc10ce9b61baf18
1
c89d6f2f51b03aeeb600705006913620
1
b92cfeca418c2dea22378d2a69b20e0d
1
2fec419046b765ea0c3b4e01c9db47a7
1
853654d9e10653518ce2df77e9edb5a0
1
f6a16052a275bda28850cb9c07e032e6
1
2c19e5532f94fc5804396a44a7b11075
1
bd038787fbc588893c8c348e22ae3557
1
f1d09ec17b6425dd6e0a316aeae5b67e
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 156[.]196[.]135[.]14
4
67[.]214[.]175[.]69
3
159[.]89[.]214[.]31
1
66[.]199[.]229[.]251
1
85[.]17[.]30[.]167
1
154[.]121[.]37[.]5
1
62[.]117[.]61[.]130
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences magichako[.]publicvm[.]com
7
shadowhakar41[.]ddns[.]net
2
AAAA5[.]HOPTO[.]ORG
1
kounan19[.]myq-see[.]com
1
salehboot[.]ddns[.]net
1
updated[.]ddns[.]net
1
blackstrretboy[.]ddns[.]net
1
z12z12[.]hopto[.]org
1
bobaramos[.]ddns[.]net
1
hackerdzarit[.]ddns[.]net
1
hassan1212[.]ddns[.]net
1
rezallta[.]ddns[.]net
1
serveo[.]net
1
android-update[.]servehttp[.]com
1
Files and or directories created Occurrences %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\Mirosoft.js
26
%APPDATA%\Microsoft\Windows\Templates\Windows.Exe
26
%TEMP%\dw.log
24
%TEMP%\73E7.dmp
24
%HOMEPATH%\Start Menu\Programs\Startup\Mirosoft.js
24
%HOMEPATH%\Templates\Windows.Exe
24
%TEMP%\server.exe
13
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\3d115699981cee571b7b4f66ac05e68c.exe
7
%TEMP%\ddn.exe
2
%APPDATA%\explorer.exe
1
%APPDATA%\server.exe
1
%TEMP%\system32.exe
1
%APPDATA%\wininit.exe
1
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\767e342b9464203399b874be2f756a33.exe
1
%TEMP%\syswine.exe
1
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\cd37f8fb04904790aec64ec6b0296433.exe
1
%TEMP%\updated.exe
1
%TEMP%\svchos.exe
1
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\d1c945c77014d102f98a39383a30a06f.exe
1
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\cee69a9c58a2f342efc10ce9b61baf18.exe
1
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\b92cfeca418c2dea22378d2a69b20e0d.exe
1
%TEMP%\windows updates.exe
1
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\f6a16052a275bda28850cb9c07e032e6.exe
1
File Hashes 07ae3ba8b6bb636c3cbc305d25f60d1b8544cbd3932ec60a41979aca444a0c8a
09332d76d630cf20549d849b207a78ac2608d719c7bdfedcf3904d9b07587210
14f0bf6f2bb1706c7c64c42a6dec0d18743ce84455cfa5507671628f09e0056b
29a28ff8074cacda1ee387ea13ea3264fc0819a32ba207002014b69a01e7d20a
2ce9507eca7390d1447568f575a31b3cccc185239956c34df11b8a97d5a41d6f
30ba3ca3f8bfe1be88a41da21b74b442f89ac3b9bc991f1429620cfe43a3d957
3709900a8d262b587769688b9ad51196212647f0c461cfa7c6aa02aad03f4c8e
37cf34ef1a59fa7f2a821d2aea146aa341d56ad8cbe8b60c028218919d9fb65c
3afaa0d40d4d857113aa2211bb268bb71a9f172a66581172c891171f3ec595d1
438a539d7fc684ff23c37d28f6968e16a26361baa95611374e844b527d8348f2
4492ee2ea728db7e9ef4a385f08890082d7754aad197aec3d3ad8a1f1b2e0554
49b6302a30504389f9f9fc0efb48da95aa52053e9c1a1ebcb309dcc0c60c071e
4ff6b9d3c069558001457fef65c1623d05ef503580db96a5b444ccc8dfb58fe8
59c9a7f0f2c8c0abdbe9790fe6d1f4b08dadb7764500fee60fd9782c076cdf40
59e1820154d4a5e6bc42158847a3f82cb25f4e7ac6a89fec036357a5e9ce6342
83e0d7c8af1ab2095ebfd11d195f5b2f1f999d741c0487c97c4f814050d0bb6f
8b9d87a3c7b4a03bf14459e9efdb89b4a73c3ffb006396638163ccd0ac73a72f
8e225d1629cb1c372d096f3d32bb621fadeba5b1c4489b08069ff977130d7bdd
9c36c86b6d998c5c3bded236f5fe94ac15239d8d283afe73acffb35bf45fea39
9cfe4f5840153f5bd81ac360c812854063952cb01fc5f3848fe9d460d84b17d7
9d46831f0a0d012493bde6165661a9af05199aa7451ca4bd89c840546d2c9d0e
a0d93958f9ccada56204fafd970d87ff67d40f78014c65cc3ce063979578aaf7
a1739268211e4f63d1f8d89a897272a945f709e9350a4a8a8f788995b5086c54
b1a0998fd2465208767650c597906941f2c95d9acaa69254238f1923ab6290fb
bc63a9907ef52f5c765a390b140e94b253b97f83aa3959f45c2ee0dcb823e0bb*See JSON for more IOCs
Coverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
Wsa
Screenshots of Detection AMP ThreatGrid Win.Malware.Tofsee-7012060-0 Indicators of Compromise Registry Keys Occurrences <HKLM>\System\CurrentControlSet\Services\NapAgent\Shas
13
<HKLM>\System\CurrentControlSet\Services\NapAgent\Qecs
13
<HKLM>\System\CurrentControlSet\Services\NapAgent\LocalConfig
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\NAPAGENT\LOCALCONFIG\Enroll\HcsGroups
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\NAPAGENT\LOCALCONFIG\UI
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\athnmuap
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: Type
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: Start
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: ErrorControl
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: DisplayName
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: WOW64
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: ObjectName
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: Description
13
<HKU>\.DEFAULT\Control Panel\Buses
12
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config0
12
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config1
12
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config4
10
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config2
10
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config3
10
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\gzntsagv
2
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\athnmuap
2
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\mftzygmb
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFTZYGMB
Value Name: ImagePath
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\GZNTSAGV
Value Name: ImagePath
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\ATHNMUAP
Value Name: ImagePath
2
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 43[.]231[.]4[.]7
13
69[.]55[.]5[.]250
12
239[.]255[.]255[.]250
10
46[.]4[.]52[.]109
10
176[.]111[.]49[.]43
10
85[.]25[.]119[.]25
10
144[.]76[.]199[.]2
10
144[.]76[.]199[.]43
10
98[.]137[.]159[.]27
10
192[.]0[.]47[.]59
10
209[.]85[.]202[.]27
10
168[.]95[.]5[.]114
10
104[.]44[.]194[.]232
9
104[.]44[.]194[.]236
9
94[.]23[.]27[.]38
9
188[.]125[.]73[.]87
8
74[.]6[.]137[.]65
8
65[.]55[.]92[.]184
8
65[.]55[.]33[.]135
8
65[.]55[.]92[.]168
8
65[.]55[.]92[.]152
8
65[.]55[.]37[.]72
8
65[.]54[.]188[.]72
8
104[.]44[.]194[.]231
8
65[.]55[.]37[.]120
8
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences microsoft-com[.]mail[.]protection[.]outlook[.]com
13
250[.]5[.]55[.]69[.]in-addr[.]arpa
12
250[.]5[.]55[.]69[.]zen[.]spamhaus[.]org
10
250[.]5[.]55[.]69[.]cbl[.]abuseat[.]org
10
mta7[.]am0[.]yahoodns[.]net
10
mta5[.]am0[.]yahoodns[.]net
10
mx-eu[.]mail[.]am0[.]yahoodns[.]net
10
250[.]5[.]55[.]69[.]dnsbl[.]sorbs[.]net
10
whois[.]iana[.]org
10
250[.]5[.]55[.]69[.]bl[.]spamcop[.]net
10
whois[.]arin[.]net
10
250[.]5[.]55[.]69[.]sbl-xbl[.]spamhaus[.]org
10
hotmail-com[.]olc[.]protection[.]outlook[.]com
10
mta6[.]am0[.]yahoodns[.]net
10
honeypus[.]rusladies[.]cn
10
marina99[.]ruladies[.]cn
10
coolsex-finders4[.]com
10
sexual-pattern3[.]com
10
msx-smtp-mx1[.]hinet[.]net
9
ipinfo[.]io
8
yahoo[.]fr
6
charter[.]net
6
mx0[.]charter[.]net
6
smtp[.]secureserver[.]net
6
msa[.]hinet[.]net
6
*See JSON for more IOCs
Files and or directories created Occurrences %SystemRoot%\SysWOW64\athnmuap
13
%TEMP%\wmslmukt.exe
13
%SystemRoot%\SysWOW64\config\systemprofile:.repos
12
%SystemRoot%\SysWOW64\config\systemprofile
12
%System32%\antugrwv\nuhhkvni.exe (copy)
10
%HOMEPATH%
9
File Hashes 130c448935b7cda787b3b2c25759959feb78b4da0578993910dea9810ac5d65b
144f230d8ff21cebd98c9baceb3f6bf183cddf3faf499ef998265ce229c6c96f
1849aaffd6046b733d684532e2c96e9022df4a024f5d906f112d1dbe3a8cfe3b
3857377eca60c925c02e5225156497b7e048239b492c2bba6e183ffa11a1fca2
67a3626583d536db9f4e8facf0e2054db1aa5cb3fc0ffc2dd994b6e784aaf0fe
8b5bcebde67ea9f0f71b9dbceff20f719334b364efe2555c0a7faa53c2cccab9
993beed87fcc986b4dacb829f412f3cd0d8d3bd055abf62ad4b2808e308d2a90
ade3682626c6aa2269e28672fe60ebbeafc42a60f5e02922d2506d6bbe8f353c
ae2cc0636044f30a1c0c662699b23bb371584fe4a53cad4ed63f91c25afa5dbb
b1a7847311263f61d845e04d26d4bdb477ebc511e53438ab11408b69f079140c
b2b29afc2cf0d1f3d4d0e29cf102c168d09405d7f1aa98426f1b2f6ae79ca1eb
d63483697d4daef64ece202d8d000b45c5db118d55865b2c981b49dbc2ec80ea
e0def1110bf0854a33f83b38925aee003e3264a35c41df58f39cc6cface46412Coverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
Wsa
Screenshots of Detection AMP
ThreatGrid Umbrella Win.Ransomware.Gandcrab-7012204-0 Indicators of Compromise Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\AUTHROOT\CERTIFICATES\DAC9024F54D8F6DF94935FB1732638CA6AD77C13
Value Name: Blob
15
<HKCU>\SOFTWARE\keys_data\data
10
<HKCU>\SOFTWARE\keys_data
10
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\TASKBAND
Value Name: FavoritesChanges
9
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\TASKBAND
Value Name: FavoritesVersion
9
<HKCU>\Software\EncryptKeys
9
<HKCU>\SOFTWARE\ENCRYPTKEYS
Value Name: local_enc_private_key_len
9
<HKCU>\SOFTWARE\ENCRYPTKEYS
Value Name: local_public_key_len
9
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\TASKBAND
Value Name: FavoritesResolve
9
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\TASKBAND
Value Name: Favorites
9
<HKLM>\SOFTWARE\Wow6432Node\ex_data\data
5
<HKLM>\SOFTWARE\Wow6432Node\keys_data\data
5
Mutexes Occurrences Global\8B5BAAB9E36E4507C5F5.lock
15
BleepingComputer_no_more_ransom
9
Global\XlAKFoxSKGOfSGOoSFOOFNOLPE
5
Global\syncronize_9WATTOA
1
Global\syncronize_9WATTOU
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 213[.]186[.]33[.]5
15
185[.]135[.]88[.]105
13
23[.]236[.]62[.]147
13
217[.]70[.]184[.]50
13
66[.]96[.]147[.]103
13
149[.]56[.]154[.]141
13
199[.]188[.]201[.]218
13
47[.]75[.]206[.]148
13
45[.]118[.]145[.]96
13
69[.]163[.]193[.]127
13
23[.]100[.]15[.]180
13
142[.]93[.]6[.]249
13
62[.]210[.]24[.]116
13
104[.]31[.]75[.]227
10
104[.]27[.]162[.]241
9
104[.]28[.]31[.]160
8
104[.]24[.]103[.]153
7
45[.]33[.]91[.]79
6
104[.]24[.]102[.]153
6
194[.]154[.]192[.]67
6
186[.]202[.]153[.]95
6
217[.]160[.]0[.]27
5
209[.]182[.]208[.]245
5
94[.]73[.]148[.]18
5
213[.]186[.]33[.]3
5
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences www[.]cyclevegas[.]com
13
img[.]maokeyang[.]cn
13
himmerlandgolfogsparesort[.]dk
13
www[.]casegranmoun[.]com
13
acbt[.]fr
5
www[.]billerimpex[.]com
5
asl-company[.]ru
5
www[.]macartegrise[.]eu
5
oceanlinen[.]com
5
nesten[.]dk
5
perovaphoto[.]ru
5
koloritplus[.]ru
5
pp-panda74[.]ru
5
dna-cp[.]com
5
boatshowradio[.]com
5
www[.]mimid[.]cz
5
tommarmores[.]com[.]br
5
cevent[.]net
5
poketeg[.]com
5
alem[.]be
5
h5s[.]vn
5
wpakademi[.]com
5
www[.]fabbfoundation[.]gm
5
6chen[.]cn
5
zaeba[.]co[.]uk
5
*See JSON for more IOCs
Files and or directories created Occurrences %APPDATA%\Microsoft\Templates\LiveContent\Managed\SmartArt Graphics\1033\TM02660319[[fn=Tab List]].glox
23
%HOMEPATH%
20
%HOMEPATH%\ntuser.ini
15
%HOMEPATH%\98b689da98b68e3d7f.lock
14
%HOMEPATH%\AppData\98b689da98b68e3d7f.lock
14
%APPDATA%\98b689da98b68e3d7f.lock
14
%APPDATA%\Media Center Programs\98b689da98b68e3d7f.lock
14
%APPDATA%\Microsoft\98b689da98b68e3d7f.lock
14
%APPDATA%\Microsoft\Internet Explorer\98b689da98b68e3d7f.lock
14
%APPDATA%\Microsoft\Internet Explorer\Quick Launch\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Cookies\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Desktop\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Documents\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Documents\My Music\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Documents\My Pictures\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Documents\My Videos\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Downloads\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Favorites\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Links\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Music\98b689da98b68e3d7f.lock
14
%HOMEPATH%\My Documents\98b689da98b68e3d7f.lock
14
%HOMEPATH%\NetHood\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Pictures\98b689da98b68e3d7f.lock
14
%HOMEPATH%\PrintHood\98b689da98b68e3d7f.lock
14
%HOMEPATH%\Recent\98b689da98b68e3d7f.lock
14
*See JSON for more IOCs
File Hashes 0341bda36f866ba3f1577ff22863cc98f3db2eb576f9ddba0efd72226362fc43
0420cacdcaf5e4dea7eacab7a960a18bc6037a88b87c1965636e70a1c3227721
11f5d5328ee2f9cef980dcfbb30621c0310eda7a6d7827c5781b32dd0d15ec22
3cb3e5d46cfbd6e6f7e1cb2398df4ff36d615657e9156bd5381564e283ce58a8
4229d9cbca43732abbe849cf9b41cb92e62702a9716a36040a51ae4ae53b4035
4844c20d9a7b7f968d0dc2a2155abb371b53098f17c14d02eca4c3e318532d59
4ce34bd577092109a075a1889b0a7de35348d6e1c5055e8fed4c78f1deed3ffe
4eb064297e7f7c2353d9a6838527168e38765163f252277049fa55eab0adc8d7
567c39590d4590c201b42384e0188ce2e621613444da676c5a4a5010fd27e4a8
5c9db3e49d5f7633752a11bf74e9d11140ddfab0957bbdabd6c55eadaa9b87f9
68ae6904af508a6fdd6cb66f8db5ddb8fc1d3da7c97241ffe31a818fa0e8ed72
720b56fd906ba499f031c7747f630fec03bec5c0bcd4a48751783550fb089df5
7662ed6be2dda454c3660d65db1a0c4d67af16a563a0c128bcf6d8a498526c7a
87b9a389d2797a074483d4147805e82f225702363afe8d1f95416cdc6dc77678
8c099167fbe1897dc8390979486353371194c2cfcb8095b6542f13670c75cab4
9c0e9a4eadea6cab1ec7faf191e77e77b91e709d8222b5c2a1d30059d026f266
a0c0eab3ce2d8be0e79d2f45b106095912f28f3f55e179cb376d7c71323146f6
a159c38828b48df7f02089b7e69e18e154054c45aa056cb9a6cefe47cd1dda47
b00ff6be8bc64d83f2d33042b9bc17110e03acc140dc3a26aa777767f210bd1e
b423e1d48c0278c2844858deff96748e9d28e8fb076990a57de6b85d8beacb03
bb187240ab8850d6b731921ab5d3ae0caeb5015ac5986af51af789ea75a3ef71
c6b096d8100033e510406c7d3f5ae5e16c8d3fb976509dacbc435c0bd0e3a118
c992d5faf5fc1cbafaf5e40e3fcfc0daad218bda2768b3640a97ed5185f91627
d88411b37cb58467d6f6050675757d8ec5cb7dfa1bbb9804f898010d4611eac6
ddee26d282c0eac34452e28c3295638fc9c887ee8f5750913f7de255b929b493*See JSON for more IOCs
Coverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
Wsa
Screenshots of Detection AMP ThreatGrid Umbrella Win.Packed.Xcnfe-7012508-0 Indicators of Compromise Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
Value Name: trkcore
25
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\SYSTEM
Value Name: DisableTaskMgr
25
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.CHECK.0
Value Name: CheckSetting
25
Mutexes Occurrences 47DjnezoRe
2
IXK1mBzkeB
2
RkTC1Yz5Uz
2
TmvHGtjMMV
2
gTBa3BMJg6
2
mssh1fu7QG
2
pyG6EAoW3D
2
rPy4lSuqRA
2
ii60Bmwus7
1
vKukwxgBam
1
CUDKUvauMV
1
KCeMGJgXYT
1
SFxcCQUOXu
1
SUC2X0PwVg
1
X3ENRc03mQ
1
YWuTH3ehY0
1
nVz9jsXjUw
1
oFYy6Mcbck
1
0CNHUsuQfc
1
2rTNQbESAE
1
PbFIJDskBy
1
R5aLQD5OQO
1
rrQXp0Shel
1
9ykplVD3nO
1
sKcAQgjpGg
1
*See JSON for more IOCs
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 172[.]217[.]12[.]142
25
104[.]20[.]209[.]21
13
104[.]20[.]208[.]21
12
Domain Names contacted by malware. Does not indicate maliciousness Occurrences pastebin[.]com
25
www[.]fvtbhlnxj0[.]com
2
www[.]fynzp0oht8[.]com
2
www[.]in4lprxgui[.]com
2
www[.]ct1wlbyjzx[.]com
2
www[.]uttn4zziks[.]com
2
www[.]lrv8bvrmhq[.]com
2
www[.]rm1cbe2kvb[.]com
2
www[.]tcp1twzitf[.]com
2
www[.]gzw0bfzxhb[.]com
1
www[.]glixbn9lnj[.]com
1
www[.]coxymk80cd[.]com
1
www[.]exgk5nzv7m[.]com
1
www[.]c62yc6xsm1[.]com
1
www[.]hludxizrvf[.]com
1
www[.]huga7gshpk[.]com
1
www[.]rjhw2tvcvh[.]com
1
www[.]5twtwy19pp[.]com
1
www[.]fwn4l9u2gb[.]com
1
www[.]xpqvri1vhh[.]com
1
www[.]seqamoa4jp[.]com
1
www[.]b7qxyidhg5[.]com
1
www[.]porsukgrlq[.]com
1
www[.]lqdu4kraxu[.]com
1
www[.]t0uetiplqk[.]com
1
*See JSON for more IOCs
File Hashes 071530d5d5e7021d1138953c314be94b1808f172e46e2e6e2b28d97ffbf2c0b1
178f3b0fc03659a616e12f423e870ab1aab778b44bd82cbc06e2c485f04bf8c3
1d987ccce04b8ba41261670691d44983a11ec2518098b312be88cb71beffa897
381a0476632ef5d0ebccd2ab242efc6a83a2e4834f2cb1fa3fa67f8fb4c09972
39c3b3c78175e68a946f81d3f5e5b2e4e45d2575387e0ab49324832fe1f47452
45103c6e8ccfda4b3f15ce4b2f3ecfdd44e1d335206f75b9a43665d35f0da2ee
486e2ea46a4e4d0e0392cb35c2e81ec465a0f89908f67a029c67c31a6178c20b
4c148b99dedd40de86d9fa90aeffae2615d465cef96547e32e2f76719f85cb26
6becb03594eaa1591c61343ba50e39df29ae01499aae44edf98a403970b0c8ac
73508f028e327bb43f8881d00a1067b5566e62b83ea5f98167a4a1947c24805a
7b89b754f7a6874a3273eedae6002a97d6ad2fab6be330207454f1ab403d38cc
8110313cc103989b2cf33894381e8715214e9003cde31d6fdf1bc8c5b49a4e89
82f1226d731f6f3c27911079d760b544b88da1e8eb5f61f4071d1d50aff37702
9915365d2bea4cd179b535b6591443ed07206dcdeb76f07dcfb9a0858e53be5b
a1e834564e9e46ee8ee26b853b4341de9909840cb82357e5ceca6cceb5346733
a5922d0eb96861fa4d6354ea66b4cb3adca32c2767de523becd1f27c7fc3cd22
b17f763211175ee8f0cbe6aec43037fb299122dcd57367b7723dd27522934365
b7c692bea525a7f6fbde41f5f85212ca38495b23795efe801246ce061ae0d6d6
bf920f2cde720bd50bab18f19b4a55ec397461dcb184e46b51884294030311a9
c80454dfd900f67cb0e22b653c5dd0b3b45cb5ac2bdf8c47c45e3ba82fb36e79
c92b1407e77bcfeb097fbe7e03c22d5adad5e437522c2bcecaa3005973817d45
dd07a463b6a9f7405660ce8ae71307e044ec17a17d9dd06cbd456cf716d51a11
f745b8cf0c6e0c86f647613e3ee3557f471bf5f4ab5b7b37565881d6d1b83838
faee0cb6a7535b30312dfb855a1c59a24dc533564ff1aa5405f351a4748b6464
fdca740263e4d6dd9d71bacb869b3792010c9e427216e54c72edfc9acfe584d7Coverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
Wsa
N/A
Screenshots of Detection AMP ThreatGrid Win.Packed.Kuluoz-7051229-0 Indicators of Compromise Mutexes Occurrences 2GVWNQJz1
26
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 178[.]63[.]193[.]60
17
74[.]208[.]246[.]250
16
37[.]26[.]108[.]41
14
133[.]242[.]134[.]76
14
62[.]75[.]143[.]211
13
78[.]47[.]145[.]72
13
77[.]72[.]26[.]97
8
Files and or directories created Occurrences %LOCALAPPDATA%\hcxlrall.exe
2
%LOCALAPPDATA%\nxeeoucb.exe
2
%HOMEPATH%\Local Settings\Application Data\rbgruqii.exe
2
%HOMEPATH%\Local Settings\Application Data\leqahubc.exe
1
%HOMEPATH%\Local Settings\Application Data\kwoisujq.exe
1
%HOMEPATH%\Local Settings\Application Data\qoqjntog.exe
1
%HOMEPATH%\Local Settings\Application Data\pegwmgts.exe
1
%HOMEPATH%\Local Settings\Application Data\oubnlaau.exe
1
%LOCALAPPDATA%\bufneahr.exe
1
%LOCALAPPDATA%\ixhcodud.exe
1
%LOCALAPPDATA%\esnbtcpu.exe
1
%LOCALAPPDATA%\qphrcdrs.exe
1
%LOCALAPPDATA%\gamnsluq.exe
1
%LOCALAPPDATA%\qakojkqh.exe
1
%LOCALAPPDATA%\tachgniq.exe
1
%LOCALAPPDATA%\wcsmjqql.exe
1
%LOCALAPPDATA%\akkqeuve.exe
1
%LOCALAPPDATA%\huhqpcvi.exe
1
%LOCALAPPDATA%\bxqfccqi.exe
1
%LOCALAPPDATA%\jbsxvqlw.exe
1
%LOCALAPPDATA%\gjqfijgu.exe
1
%LOCALAPPDATA%\qxvxkxtb.exe
1
%LOCALAPPDATA%\nsahkntd.exe
1
%LOCALAPPDATA%\ptlqijon.exe
1
%LOCALAPPDATA%\saxrgecs.exe
1
*See JSON for more IOCs
File Hashes 00722db9477ac36de1c2862fc9f35cafc7a01347110d29102dce98cdf72155bc
012ab737e3a2128c76e48db7bef2768bdd57778e4af397ec133c6079c42411c5
012c77f8b7c99a1d27823d452e130abc5cac6f000adf05d56c7f2ae47a9d72bf
0146c339fb7ec7f1284c123da8e8a4d4faf8c52301949b1da482696a054c87d1
01afc54230a064be47e8948f41b699a33ed1fef92eada1fbab8cde2ab0655d03
02494b4c16f22b6d4f92ce1eef08a661cea52f673c7eb0289579290d46717898
03c783b4a26b0d890a71bdf0a643bdb96de4818898177a4716333b435ca1cd28
04a85f4471adefcba2b10c0e32a2fe12ff81b804205730f3cc21f3db4bc49b7c
04b02fc83ba2785e3216acccb81490bb1db3807bc2a2a255a193313ed90717fd
04f45879c4e79a6bea82e39aea468d8e1f8e55f13c8dbde1e4855141b19b26e6
0522ba3cf1a33345ee6bffade7ff3f73d8d3d018994f08e1a9d36df93efa9299
06370b03ef47ca5e5547d750f49034fbeb3782c201e36921c2577f074123ccb8
069df491cffe2a3fe59b8e85dce0e6520b61c2a8d9fd164277ee0f9a254354d0
06bc29e3a3c0cdc268fca231cb64458228d9d11b5f72cb6416321c986832aaf8
07067626f964e49a6efde18624deed513c1a53f5ac096e2bc422fdf23d70dedf
0763b04d0acac49c55a7fec6f47169e7567ccd9c0ed9264ddadd848bb08b7b65
08f908d9480fc99e75ba466f9fa113495db64e6decf5d26ced63a24a9c240caa
091fabce8131379f261ab41ade48b8b5ffb939f66e0219cc5083c85346d99661
0a579fd78803ea10efd73e5e1a36986f5a4f1caba4fecb0774d918ba578818de
0ae4096d1264141e9714700691f6fcad18b1ccac36f73d9e580a652b6b9e2743
0b7adc1b0cfd8e7b0b24f98a7ff788ef6ce9f361f09b286bee4d99ec5bd2c0ac
0c042729532173d9c64ab369c0710861299ed553b201c218a1453c52d967032c
0e0e274ce9e54e585f9ac7d096f3092f152f090fb5f5273d6086270f2b8da40d
0eacc634900f97e7c7b7e421db1f38c40e869dc86e79c0f490b71572510e6085
0ef4c5d715006cba42eb775a72e285c59c7ccf64082dcc85e3ed2843b1fc1be7*See JSON for more IOCs
Coverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
Wsa
N/A
Screenshots of Detection AMP ThreatGrid Win.Ransomware.Cerber-7052005-0 Indicators of Compromise Registry Keys Occurrences <HKCU>\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
18
<HKCU>\Printers\Defaults\{21A3D5EE-E123-244A-98A1-8E36C26EFF6D}
18
<HKCU>\PRINTERS\Defaults
18
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER
Value Name: Run
18
<HKCU>\SOFTWARE\MICROSOFT\COMMAND PROCESSOR
Value Name: AutoRun
18
<HKCU>\CONTROL PANEL\DESKTOP
Value Name: SCRNSAVE.EXE
18
<HKCU>\PRINTERS\DEFAULTS\{21A3D5EE-E123-244A-98A1-8E36C26EFF6D}
Value Name: Installed
12
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER
Value Name: CleanShutdown
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{509D0DCA-5840-11E6-A51E-806E6F6E6963}
Value Name: Generation
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{6DD1DC5F-5840-11E6-B80E-00501E3AE7B5}
Value Name: Data
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{6DD1DC5F-5840-11E6-B80E-00501E3AE7B5}
Value Name: Generation
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{3F37BA63-EF5C-11E4-BB8D-806E6F6E6963}
Value Name: Data
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{3F37BA63-EF5C-11E4-BB8D-806E6F6E6963}
Value Name: Generation
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{3F37BA64-EF5C-11E4-BB8D-806E6F6E6963}
Value Name: Data
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\MOUNTPOINTS2\CPC\VOLUME\{3F37BA64-EF5C-11E4-BB8D-806E6F6E6963}
Value Name: Generation
7
<HKLM>\SYSTEM\CONTROLSET001\ENUM\PCIIDE\IDECHANNEL\4&A27250A&0&2
Value Name: CustomPropertyHwIdKey
7
<HKLM>\SYSTEM\CONTROLSET001\ENUM\USB\VID_46F4&PID_0001\1-0000:00:1D.7-2
Value Name: CustomPropertyHwIdKey
7
<HKLM>\SYSTEM\CONTROLSET001\ENUM\PCI\VEN_1AF4&DEV_1001&SUBSYS_00021AF4&REV_00\3&2411E6FE&2&18
Value Name: CustomPropertyHwIdKey
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: winrs
2
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: rasautou
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
Value Name: rasautou
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: getmac
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
Value Name: getmac
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Utilman
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
Value Name: Utilman
1
Mutexes Occurrences shell.{381828AA-8B28-3374-1B67-35680555C5EF}
18
\BaseNamedObjects\shell.{573F0F01-C284-E3E4-B166-E3C39544ED56}
17
cversions.1.m
12
GeneratingSchemaGlobalMapping
12
cversions.2.m
12
Local\ExplorerIsShellMutex
8
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 31[.]184[.]235[.]224
18
31[.]184[.]234[.]128
18
31[.]184[.]234[.]0
18
31[.]184[.]235[.]252
18
31[.]184[.]235[.]254
18
31[.]184[.]235[.]248
18
31[.]184[.]235[.]128
18
31[.]184[.]234[.]224
18
31[.]184[.]234[.]192
18
31[.]184[.]235[.]192
18
31[.]184[.]234[.]252
18
31[.]184[.]234[.]254
18
31[.]184[.]234[.]248
18
31[.]184[.]235[.]0
18
31[.]184[.]235[.]240
18
31[.]184[.]234[.]240
18
216[.]239[.]32[.]21
8
216[.]239[.]34[.]21
7
216[.]239[.]38[.]21
7
216[.]239[.]36[.]21
7
104[.]26[.]15[.]73
6
147[.]135[.]15[.]186
5
104[.]26[.]14[.]73
5
185[.]100[.]85[.]150
1
54[.]84[.]252[.]139
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences ipinfo[.]io
18
en[.]wikipedia[.]org
8
www[.]collectionscanada[.]ca
8
alpha3[.]suffolk[.]lib[.]ny[.]us
8
www[.]archives[.]gov
8
www[.]vitalrec[.]com
8
www[.]cdc[.]gov
8
freegeoip[.]net
6
ip-api[.]com
5
52uo5k3t73ypjije[.]hlu8yz[.]top
2
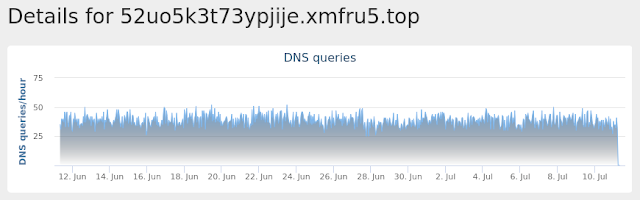
52uo5k3t73ypjije[.]xmfru5[.]top
2
onion[.]to
1
cerberhhyed5frqa[.]onion[.]to
1
52uo5k3t73ypjije[.]zclw5i[.]top
1
52uo5k3t73ypjije[.]ujtwhg[.]top
1
52uo5k3t73ypjije[.]ka0te8[.]top
1
52uo5k3t73ypjije[.]j92msu[.]top
1
52uo5k3t73ypjije[.]nameuser[.]site
1
52uo5k3t73ypjije[.]b7mciu[.]top
1
52uo5k3t73ypjije[.]marksgain[.]kim
1
52uo5k3t73ypjije[.]moonsides[.]faith
1
52uo5k3t73ypjije[.]bigfooters[.]loan
1
52uo5k3t73ypjije[.]poplenjohs[.]review
1
Files and or directories created Occurrences %APPDATA%\Adobe\Acrobat\9.0\# DECRYPT MY FILES #.html
17
%APPDATA%\Adobe\Acrobat\9.0\# DECRYPT MY FILES #.txt
17
%APPDATA%\Adobe\Acrobat\9.0\# DECRYPT MY FILES #.url
17
%APPDATA%\Adobe\Acrobat\9.0\# DECRYPT MY FILES #.vbs
17
%APPDATA%\Adobe\Acrobat\9.0\JavaScripts\# DECRYPT MY FILES #.url
17
%APPDATA%\Microsoft\Office\Recent\# DECRYPT MY FILES #.html
17
%APPDATA%\Microsoft\Office\Recent\# DECRYPT MY FILES #.txt
17
%APPDATA%\Microsoft\Office\Recent\# DECRYPT MY FILES #.url
17
%APPDATA%\Microsoft\Office\Recent\# DECRYPT MY FILES #.vbs
17
\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.html
17
\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.txt
17
\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.url
17
\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.vbs
17
\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.html
17
\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.txt
17
\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.url
17
\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.vbs
17
\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.html
17
\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.txt
17
\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.url
17
\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.vbs
17
\MSOCache\All Users\{90140000-001A-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.html
17
\MSOCache\All Users\{90140000-001A-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.txt
17
\MSOCache\All Users\{90140000-001A-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.vbs
17
\MSOCache\All Users\{90140000-001B-0409-0000-0000000FF1CE}-C\# DECRYPT MY FILES #.html
17
*See JSON for more IOCs
File Hashes 209658cf26f8038c101648b334666a1cbd99ba42a080a43876e8029213fd405b
274afa596526d108c10f535087a70a4fa67b6f1fd104d21e3c8674af03f7adfe
39c03cb39ccac093652c84050ce94ee6369a61bc8a1ca6a29da77e29085b2911
5a7a2465a741812bb9f5f6d203600e190db972f3e04dba331af035ccb27c61fb
70ee34b58fdfb524314767a6054328bd22fe04b57d6ac91e4509ec4ca11255ea
7fe89fee44b718691ba4af29f533b375ad78bdee6660a89071f80f8b12c58295
84237ea2516de3f238fbcc495a5c50b3c2ef72001b0afc14d0939a984d1dbf22
934861f1991b586ea681132cf93cc5a3d0892158ffa310ac55691c996e6bec19
9bf0aa931cd9e7faf11a6b17ead1493b98dae3155d948eb648d2b797e301a2cc
ad93c9f4410bb99238320518457308695053b36d9034ba6a3720a9294b6b4c4f
b52f586b1d185c332aa2c8ec7e196747b817344e508896bb24996c607cbd4581
b8148a65912385e4ce63f6ea7bb78b30479dddbc84d2bd6cbe9fa1a3425c27a3
d41538fe9d4c4edb975df9af8850749b9db89cd470139b0a58ff8d68e5b6240f
eaf534a49e96dcbd62b64e4ca52c2aa087f554eec76d40760393841f4440f451
ec3b5abf71ccbe9986bf6033ab48cb2f616519825047dbdf7668f7fea8bcebeb
eefe9124619775ab69b2cd620988245f928a8bb9c988298b9340f82cdf0187a7
f65d7ea6666e7aa4d3bac195a0493c4b736c995d36118915a1d10567a2b31b3f
f8c55ef8913ff76ec97e8d226fdbe88c82a2ccaab4662fd6859585f3db946d6dCoverage Product Protection Amp
Cloudlock
N/A
Cws
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
Wsa
Screenshots of Detection AMP ThreatGrid Umbrella Exploit Prevention Cisco AMP for Endpoints protects users from a variety of malware functions with exploit prevention. Exploit prevention helps users defend endpoints from memory attacks commonly used by obfuscated malware and exploits. These exploits use certain features to bypass typical anti-virus software, but were blocked by AMP thanks to its advanced scanning capabilities, even protecting against zero-day vulnerabilities. Madshi injection detected - (1969)
Madshi is a code injection framework that uses process injection to start a new thread if other methods to start a thread within a process fail. This framework is used by a number of security solutions. It is also possible for malware to use this technique.
Kovter injection detected - (1195)
A process was injected into, most likely by an existing Kovter infection. Kovter is a click fraud Trojan that can also act as an information stealer. Kovter is also file-less malware meaning the malicious DLL is stored inside Windows registry and injected directly into memory using PowerShell. It can detect and report the usage of monitoring software such as wireshark and sandboxes to its C2. It spreads through malicious advertising and spam campaigns.
Process hollowing detected - (792)
Process hollowing is a technique used by some programs to avoid static analysis. In typical usage, a process is started and its obfuscated or encrypted contents are unpacked into memory. The parent then manually sets up the first stages of launching a child process, but before launching it, the memory is cleared and filled in with the memory from the parent instead.
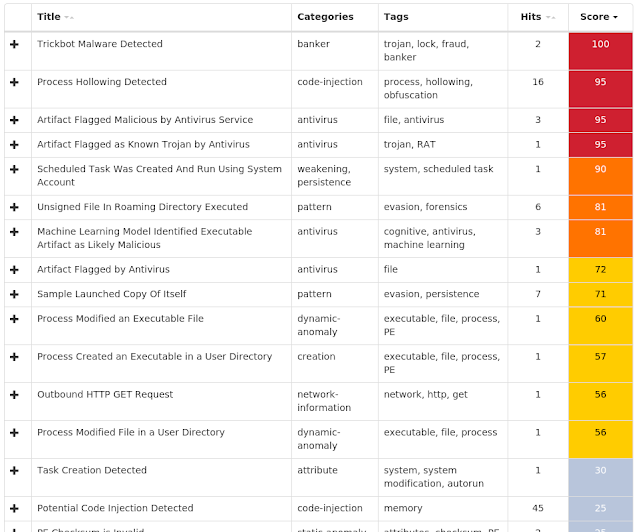
Trickbot malware detected - (714)
Trickbot is a banking Trojan which appeared in late 2016. Due to the similarities between Trickbot and Dyre, it is suspected some of the individuals responsible for Dyre are now responsible for Trickbot. Trickbot has been rapidly evolving over the months since it has appeared. However, Trickbot is still missing some of the capabilities Dyre possessed. Its current modules include DLL injection, system information gathering, and email searching.
Dealply adware detected - (468)
DealPly is adware, which claims to improve your online shopping experience. It is often bundled into other legitimate installers and is difficult to uninstall. It creates pop-up advertisements and injects advertisements on webpages. Adware has also been known to download and install malware.
Gamarue malware detected - (125)
Gamarue is a family of malware that can download files and steal information from an infected system. Worm variants of the Gamarue family may spread by infecting USB drives or portable hard disks that have been plugged into a compromised system.
Atom Bombing code injection technique detected - (61)
A process created a suspicious Atom, which is indicative of a known process injection technique called Atom Bombing. Atoms are Windows identifiers that associate a string with a 16-bit integer. These Atoms are accessible across processes when placed in the global Atom table. Malware exploits this by placing shell code as a global Atom, then accessing it through an Asynchronous Process Call (APC). A target process runs the APC function, which loads and runs the shellcode. The
malware family Dridex is known to use Atom Bombing, but other threats may leverage it as well.
PowerShell file-less infection detected - (42)
A PowerShell command was stored in an environment variable and run. The environment variable is commonly set by a previously run script and is used as a means of evasion. This behavior is a known tactic of the Kovter and Poweliks malware families.
Installcore adware detected - (38)
Install core is an installer which bundles legitimate applications with offers for additional third-party applications that may be unwanted. The unwanted applications are often adware that display advertising in the form of popups or by injecting into browsers and adding or altering advertisements on webpages. Adware is known to sometimes download and install malware.
Excessively long PowerShell command detected - (37)
A PowerShell command with a very long command line argument that may indicate an obfuscated script has been detected. PowerShell is an extensible Windows scripting language present on all versions of Windows. Malware authors use PowerShell in an attempt to evade security software or other monitoring that is not tuned to detect PowerShell based threats.