By Matthew Valites with contributions by Joanne Kim and Edmund Brumaghin.
Executive summary
Mobile stalkerware has all sorts of wide-ranging consequences. The creators of these types of apps can track user's locations, see their social media usage and more. And they certainly open the door for abuse by governments hoping to spy on their citizens, parents looking to track their children or controlling spouses hoping to track every move their partners make. This class of software exists to surreptitiously get and provide this personal information, sometimes in real time.
Cisco Talos recently spotted a wave of vendors hawking this software, designed to spy on unsuspecting users. We observed apps across the globe — including activities in countries that have some of the worst human rights records — with vendors offering language- and country-specific services. In all, there were 87 vendors we discovered as part of our research, which we believes poses a serious threat to at-risk individuals. The stalkerware space is completely unregulated, and these apps are allowed to exist on many app stores for extended periods of time, with their creators even offering easy to follow tutorials online as to how to trick users into downloading these apps. This is an easily accessible, yet volatile, market.
Previous research by Talos shows adversaries, including nation-state level actors, using open-source mobile device management (MDM) software and fake apps to surreptitiously control compromised devices and exfiltrate sensitive data. Leaked data shows that five to 10 years ago, this capability would cost an adversary a significant amount of money. Today, anyone with an internet connection can choose from a range of commercial vendors providing identical capabilities for anywhere from free to $80 per month. It's even got to the point that prominent government vendors are reselling off-the-shelf "toy" software to track "unfaithful spouses," according to leaked emails. A flourishing marketplace exists for these dual-use applications that provide tracking, remote control, and interception capabilities. Operating on the internet with impunity, some of the most intrusive applications include the ability to covertly listen to active phone calls and enable the camera or microphone.
The basics
Most commercially available stalkerware applications are sold and distributed directly through vendor sites. Some vendors host their applications for download without authentication while others require signing up and paying for the service. Of the vendors selling or reselling spy software that we identified, only two were available through the Google Play store.
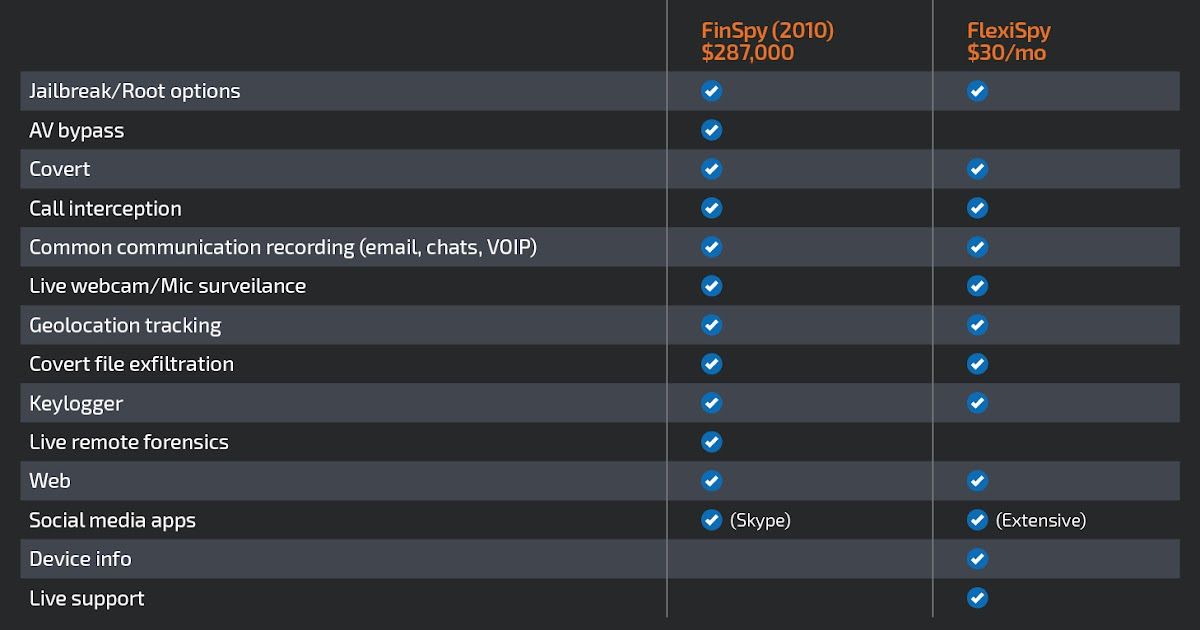
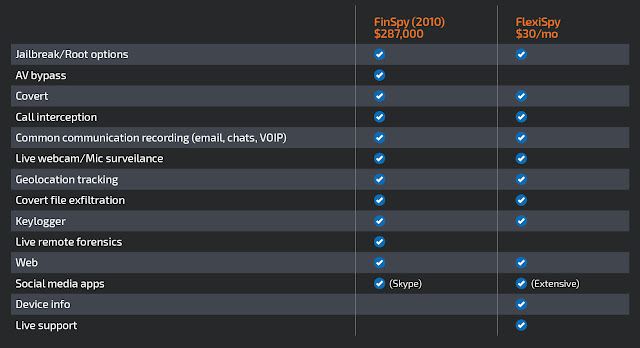
Nearly all vendors offer varying capabilities, some dependent on whether the target devices are rooted or jailbroken. In the table below, we compare a popular commercial stalkerware vendor called "FlexiSpy" with a government-level offering called "FinSpy." Most capabilities present within nation-state level software are comparable to those present within the most popular consumer-level stalkerware applications that we identified. Where the government options differ is in their live remote forensics and anti-virus avoidance. While Flexispy provides call interception, most vendors only provided call metadata. In 2014, the United States Federal Trade Commission (FTC) fined StealthGenie $500,000 for violating the Wiretap Act by selling an interception device. While live intercept may be too risky of a capability for most vendors to offer, geolocation tracking is a standard offering.
Some vendors provide premium multilingual installation support services to assist consumers with installing the software on the device. The screenshot below shows an example of an Mspy reseller offering a Spanish chat service. The ad states, "Spanish support, free consultation through chat." While presumably there to offer legitimate technical support, previous reports have shown the support staff often acts inappropriately.

How widespread of a problem is this?
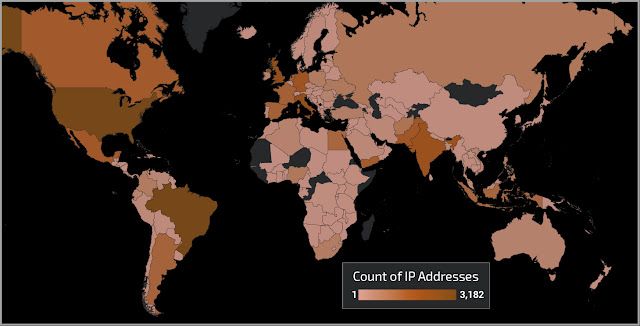
Using passive DNS telemetry, we observed activity to these domains from 171 different countries in a single day. The darker the country in the map below, the higher number of unique remote IP addresses we observed. What's most immediately apparent is how global these applications are used. Brazil and the United States combined account for nearly 50 percent of the observed queries. Italy, the United Kingdom, and India round out the top five with less than 4 percent of the total queries coming from each country. Spying capabilities once restricted to certain nation-states have been democratized and are being used all over the world.
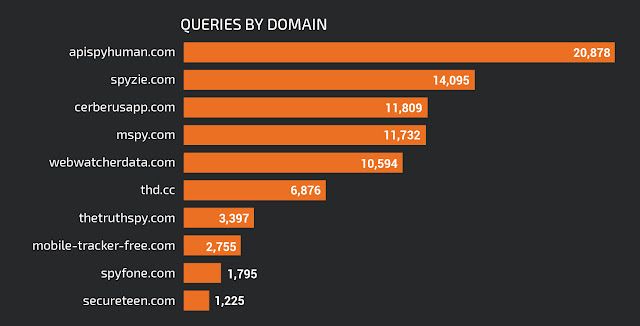
The next table shows the most queried domains from our sample data. The top domain is the API endpoint for an application owned by a vendor called spyhuman[.]com, who provides a free offering that includes geolocation capabilities. This application is supported on only six vendors' devices, yet claims the top spot for most-queried domain, and was observed primarily in the Middle East and Northern Africa. The third domain is for Cerberus security, which for five Euros per device per year, offers supposed anti-theft geolocation services for Android devices, including on Android Wear smartwatch devices. Also included in the top 10 most-queried domains is thd[.]cc, the domain hosting applications for another stalkerware app called mspy[.]com.
Spyhuman was the victim of an attack in 2018 that exposed collected metadata from remote devices. Be it the shaky moral ground of the businesses, or the sensitive data they contain, spyware providers have found themselves the targets of hackers. Four other businesses, including a parent company that owns multiple spyware companies are known to have been successfully breached. One of those companies admitted to a breach of photographic material (presumably acquired from targets by customers) that ultimately and indefinitely halted its spyware products.
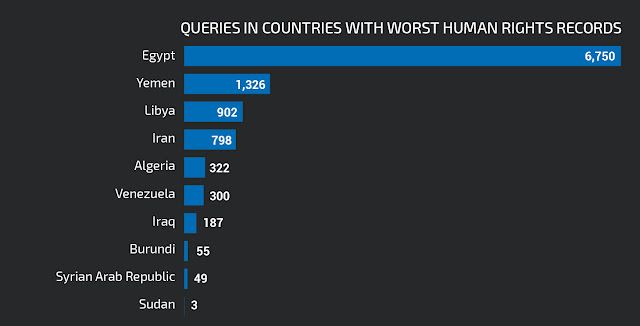
Cross-referencing DNS data with data from the CATO Institute's Human Freedom Index, which attempts to quantify the state of global human freedom, we can see query activity to spy domains from the 10 lowest-ranked countries on the index. Egypt has the most number of queries at 6,750 from 179 unique requestor IPs, whereas Yemen has the most unique requestor IPs at 224 with 1,326 queries. We observed queries to stalkerware backend API infrastructure in each of these countries, indicating not just web browsing activity, but active use of these applications. That these businesses sell their wares in countries with known poor human rights records calls into question the morality of their operations.
What can be done?
Many of the vendors Talos researched publicly advertise their services toward parents monitoring the safety of their children, consumers who want to prepare themselves in the event of the theft of the device, or businesses monitoring employees' devices. And our research shows evidence of the latter. We see businesses intentionally whitelisting domains belonging to some of these vendors, ostensibly to ensure service availability when using the applications legitimately for enterprise device management. However, some sites overtly display suggestive marketing material that indicates a more nefarious use-case for the software, as can be seen in the image below. No longer solely in the realm of nation-states, anyone with intent and device access can afford to use these spy-like capabilities.

Detecting whether a covert spy application is installed on a device is, by intention, difficult. Additionally, at-risk individuals can leak metadata to adversaries even without these apps installed. With access to individual accounts, such as Facebook and iCloud backups, abusers can get sensitive information without installing spyware. The Federal Trade Commission has information for stalking victims on their site. Additionally, users who suspect they may be the victim of spyware can check a few things:
- Rotate and use unique passwords for sensitive accounts, and use multi-factor authentication where possible.
- Many social media services show account logins by device. Check for unauthorized devices.
- Disable geolocation permissions on applications and devices as much as possible.
- Keep devices and apps patched to prevent possible vulnerability exploitation.
- Conduct sensitive conversations in person or use a new phone.
- Protect your devices with a strong password/pin.
- Use only official application stores to install software.
- Factory reset or wipe the device.
- Use stalkerware installation guides to determine if your devices has signs of being configured to allow installation of these applications.
Be mindful that this software can exfiltrate dialed phone numbers, application chats and SMS. If you fear you're at risk and must seek help, try to use a known secure phone.