Today, Talos is publishing a glimpse into the most prevalent threats we've observed between June 19 and June 26. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org , or ClamAV.net .
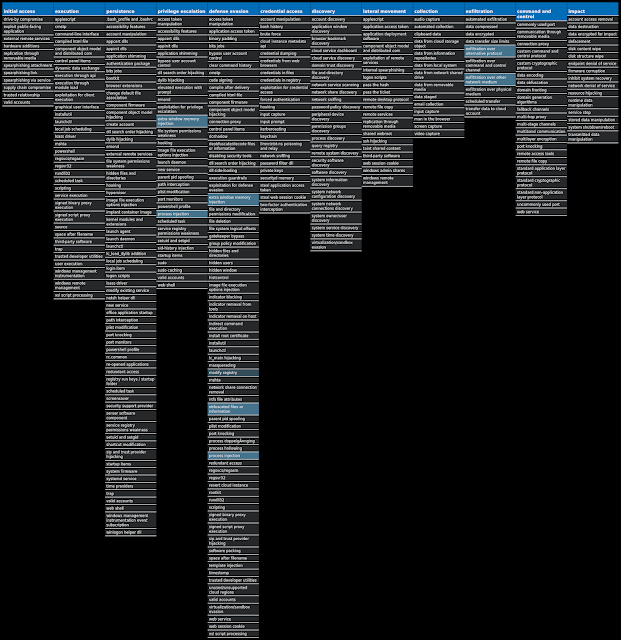
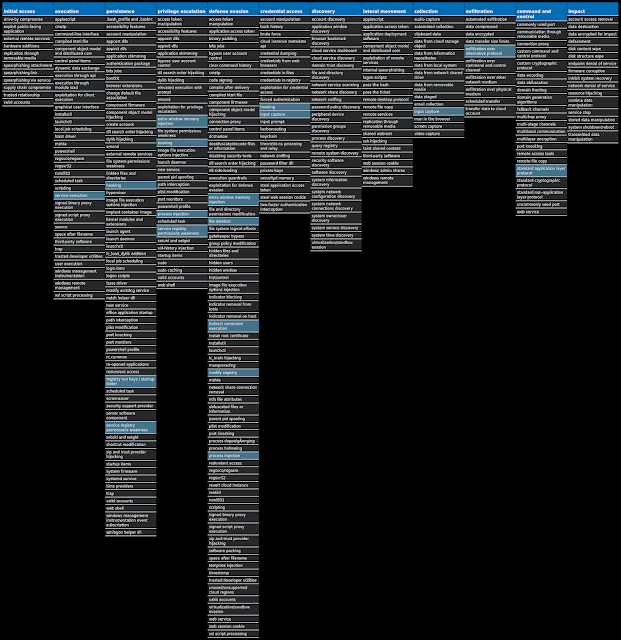
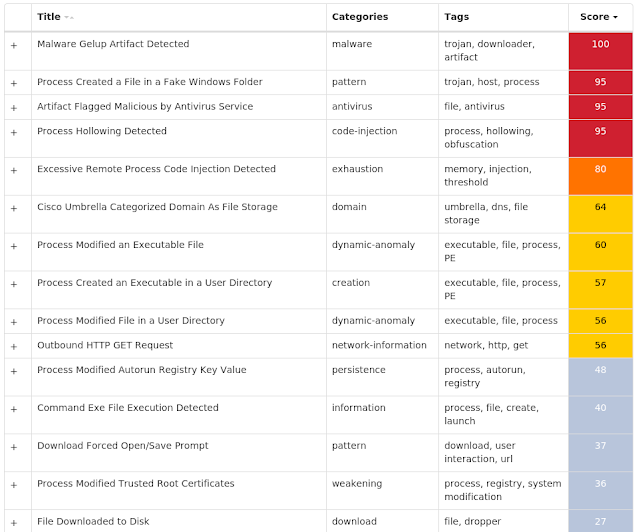
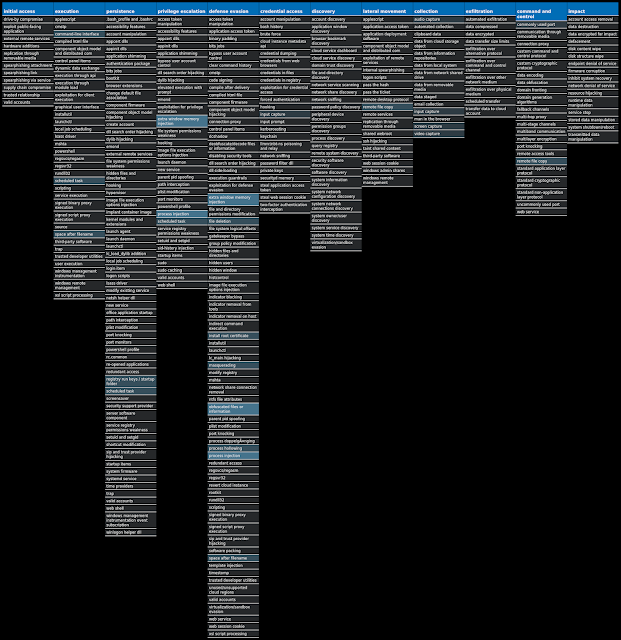
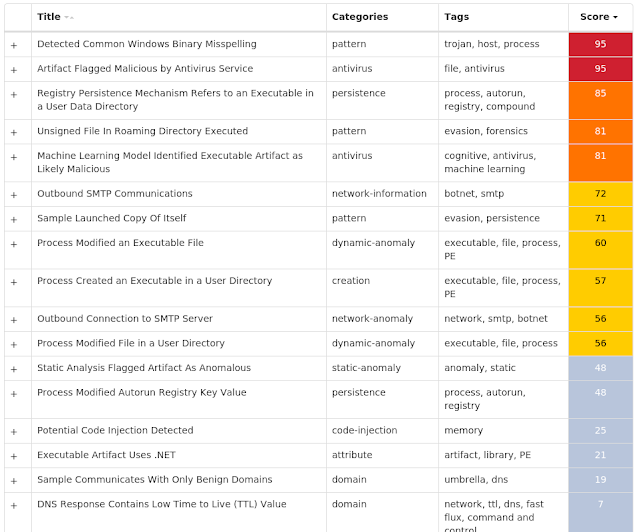
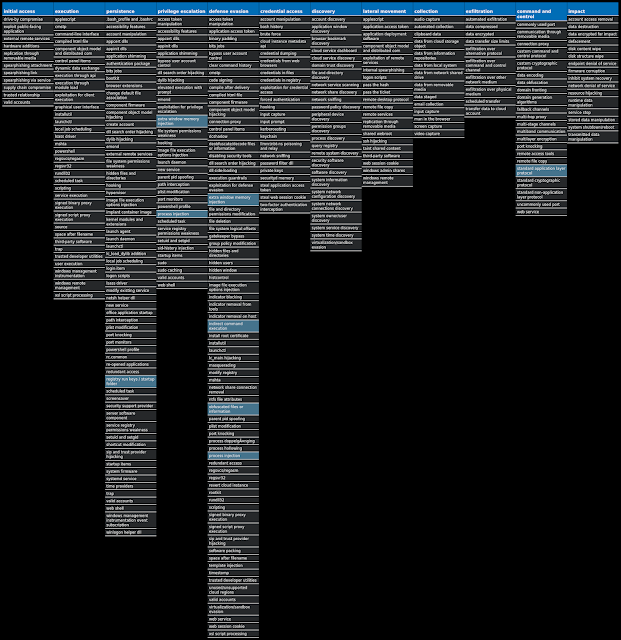
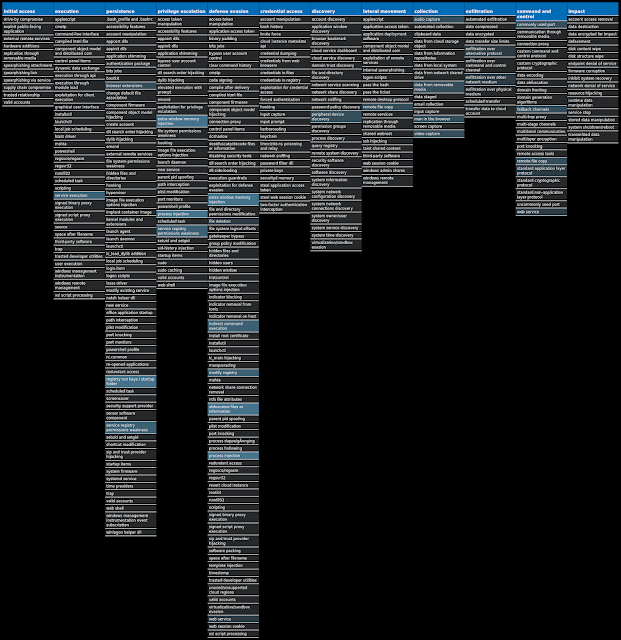
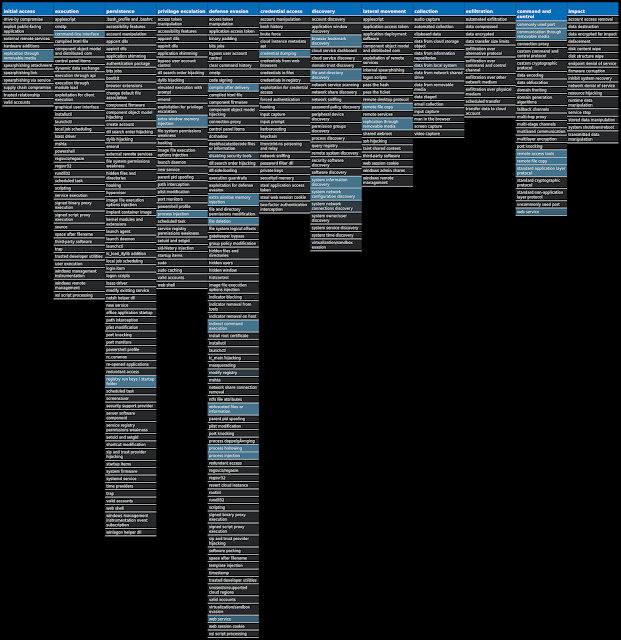
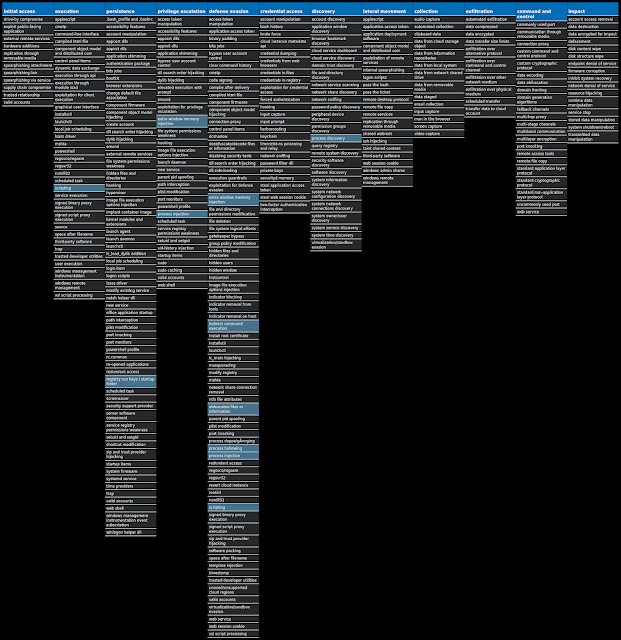
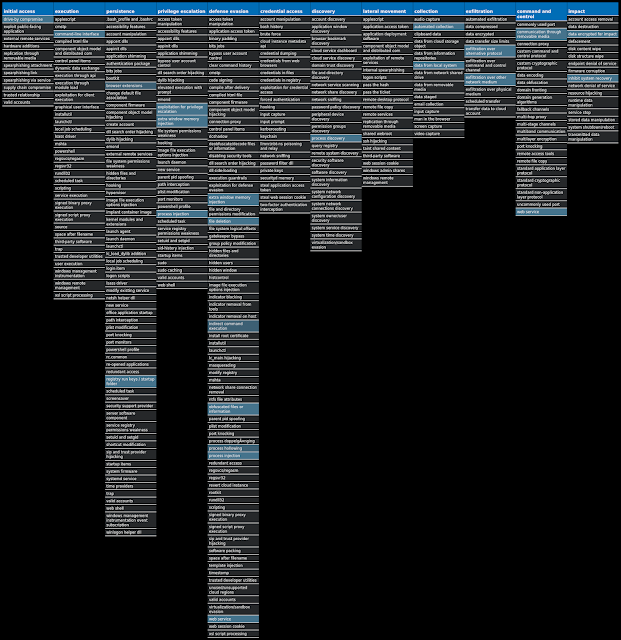
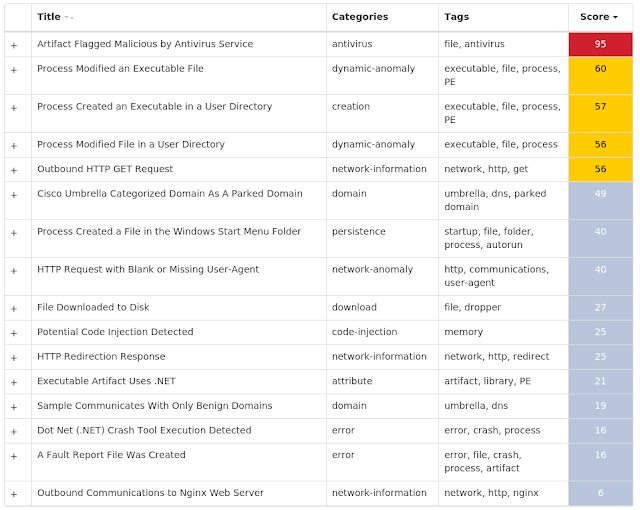
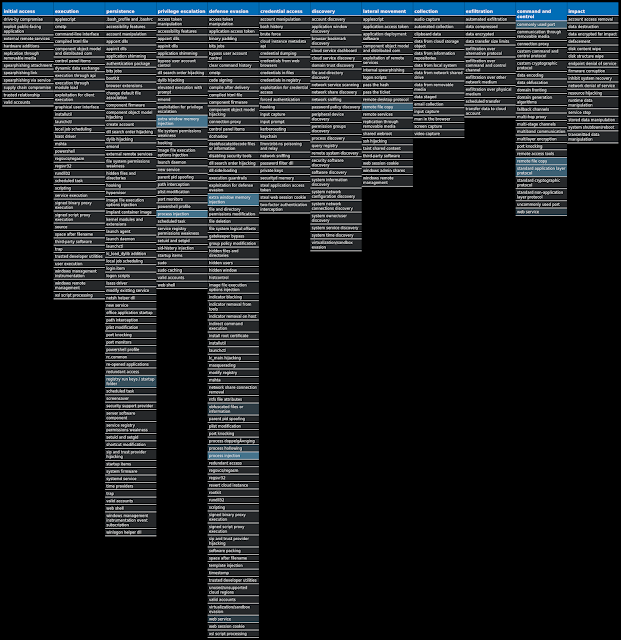
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found here that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name Type Description Win.Downloader.Nymaim-8076820-0
Downloader
Nymaim is malware that can be used to deliver ransomware and other malicious payloads. It uses a domain generation algorithm to generate potential command and control (C2) domains to connect to additional payloads.
Win.Packed.Emotet-8082161-0
Packed
Emotet is one of the most widely distributed and active malware families today. It is a highly modular threat that can deliver a wide variety of payloads. Emotet is commonly delivered via Microsoft Office documents with macros, sent as attachments on malicious emails.
Win.Trojan.Remcos-8176626-0
Trojan
Remcos is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes, interact with a webcam, and capture screenshots. This malware is commonly delivered through Microsoft Office documents with macros, sent as attachments on malicious emails.
Win.Packed.Zbot-8176461-0
Packed
Zbot, also known as Zeus, is a trojan that steals information, such as banking credentials, using methods such as key-logging and form-grabbing.
Win.Dropper.Ramnit-8176536-0
Dropper
Ramnit is a banking trojan that monitors web browser activity on an infected machine and collects login information from financial websites. It also has the ability to steal browser cookies and attempts to hide from popular antivirus software.
Win.Dropper.HawkEye-8176602-0
Dropper
HawkEye is an information stealing malware that specifically targets usernames and passwords stored by web browsers and mail clients on an infected machine. It is commonly spread via email and can also propagate through removable media.
Win.Dropper.NetWire-8176767-1
Dropper
NetWire is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes, interact with a webcam, remote desktop, and read data from connected USB devices. NetWire is commonly delivered through Microsoft Office documents with macros, sent as attachments on malicious emails.
Win.Ransomware.TeslaCrypt-8182300-0
Ransomware
TeslaCrypt is a well-known ransomware family that encrypts a user's files with strong encryption and demands Bitcoin in exchange for a file decryption service. A flaw in the encryption algorithm was discovered that allowed files to be decrypted without paying the ransomware, and eventually, the malware developers released the master key allowing all encrypted files to be recovered easily.
Win.Packed.Zusy-8182349-0
Packed
Zusy, also known as TinyBanker or Tinba, is a trojan that uses man-in-the-middle attacks to steal banking information. When executed, it injects itself into legitimate Windows processes such as "explorer.exe" and "winver.exe". When the user accesses a banking website, it displays a form to trick the user into submitting personal information.
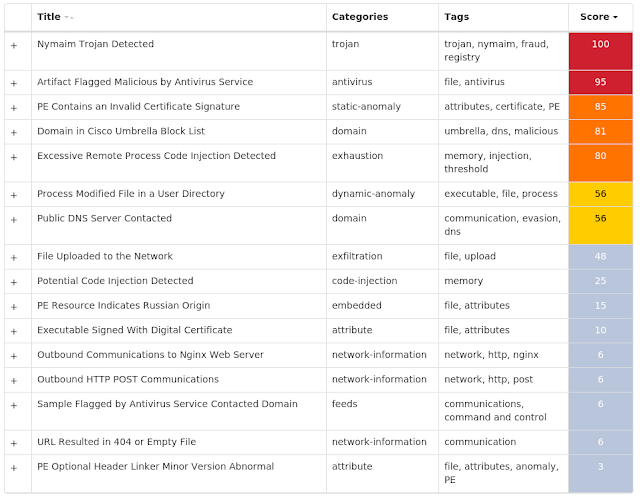
Threat Breakdown Win.Downloader.Nymaim-8076820-0 Indicators of Compromise IOCs collected from dynamic analysis of 16 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\GOCFK
16
<HKCU>\SOFTWARE\MICROSOFT\GOCFK
Value Name: mbijg
16
Mutexes Occurrences Local\{369514D7-C789-5986-2D19-AB81D1DD3BA1}
16
Local\{D0BDC0D1-57A4-C2CF-6C93-0085B58FFA2A}
16
Local\{F04311D2-A565-19AE-AB73-281BA7FE97B5}
16
Local\{F6F578C7-92FE-B7B1-40CF-049F3710A368}
16
Local\{306BA354-8414-ABA3-77E9-7A7F347C71F4}
16
Local\{F58B5142-BC49-9662-B172-EA3D10CAA47A}
16
Local\{C170B740-57D9-9B0B-7A4E-7D6ABFCDE15D}
16
Local\{B123E21A-671F-AA5F-2286-F31181A381CF}
16
Local\{85785183-F382-5EB6-2795-711B10C1720E}
16
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 66[.]220[.]23[.]114
16
64[.]71[.]188[.]178
16
184[.]105[.]76[.]250
16
Domain Names contacted by malware. Does not indicate maliciousness Occurrences nvwzxhhhdv[.]com
14
wpbzgw[.]com
6
qggkh[.]com
1
bwsmfrjorlq[.]net
1
bwdeplfczh[.]in
1
wjosmgsktip[.]pw
1
cfznbpxyryk[.]net
1
jocgylyymc[.]net
1
wfruicutcyrs[.]net
1
fhudalgggjg[.]in
1
lupedxkaibo[.]com
1
kzaymlrch[.]net
1
aycxogx[.]com
1
mwuylejzv[.]net
1
oxoftcpn[.]com
1
zhdmdivvz[.]in
1
senfukvb[.]com
1
ssdodwxhnd[.]com
1
scqbxsagu[.]net
1
Files and or directories created Occurrences %ProgramData%\ph
16
%ProgramData%\ph\fktiipx.ftf
16
%TEMP%\gocf.ksv
16
%ProgramData%\<random, matching '[a-z0-9]{3,7}'>
16
%APPDATA%\<random, matching '[a-z0-9]{3,7}'>
16
%LOCALAPPDATA%\<random, matching '[a-z0-9]{3,7}'>
16
%TEMP%\fro.dfx
15
\Documents and Settings\All Users\pxs\pil.ohu
15
%TEMP%\bpnb.skg
2
%TEMP%\yvthfwu.dke
1
\Documents and Settings\All Users\tjl\wknj.wwy
1
File Hashes 0b8b92c84b42245d75835c5c08207c58afa5b2c713a73b63b12893ce2b55fcab
1073e4d929967870bc85a70610a16ffea79abdd4e0458e97f9ccf494a02ccaff
467c064eeabc29668178ddbefc466f856672291347abfe3cd8290c0223976fda
59efdf5c8785c716a263f09c146de00bce00590df67a8b4ccf3d316780dc681a
6a0953a33920722f1c8a06b4e4bbe428ced81fb840422b18b86b293284325aef
6a41f990066df75b6d2bed50ca401a89f2c35c1d6683f861938831f5c61e937f
6b4aa0bbc515677549a3b6f33cc762032e151a5da40f127323bbcb7dba3ab979
7dd3a949f6e6b6dab8352fdc1d917f07697f9dc0b2dbb5d35d1539be1c56e15d
8f8f122da6336a028e636218b57ba9e8abaffdf934977c7cb55ba376c76f529c
a568133513b2f1520e8b45494bbbbb4b5b40bb29c21271ae5d51514be907b1f5
a7573193ade3d217c745d948238d61c8ec0356bfe8e0623bdfbf81c4566a0f28
b0a0f7b7c6f7902facf84acd566afaf32ead8ec9c437722b584f7a927035c38a
c58e14431f9d6dd30c6437e7ffcd146cd86de44e48298aab6fe45296685ba3ec
cf0b258853687bbb2b02617ed5b627f7a67f354efc597f0ac222708106094ed2
dc5146d83c233077ae27dbffc23b7aa7fae1ac3068785e96d88995299b3d7351
eabd9c9a0b18c1c85f7a306f7f3075425b4cddafebb2acd2b6e5adfdd8064ef0Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
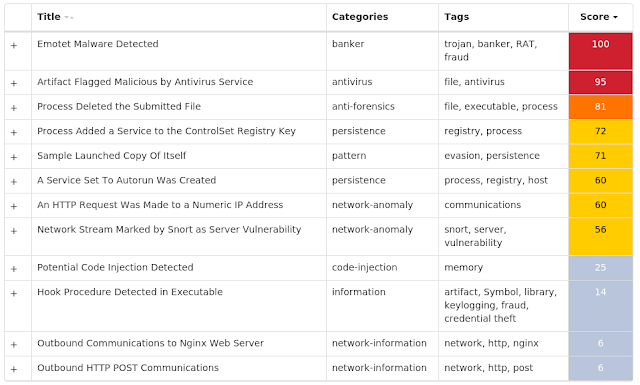
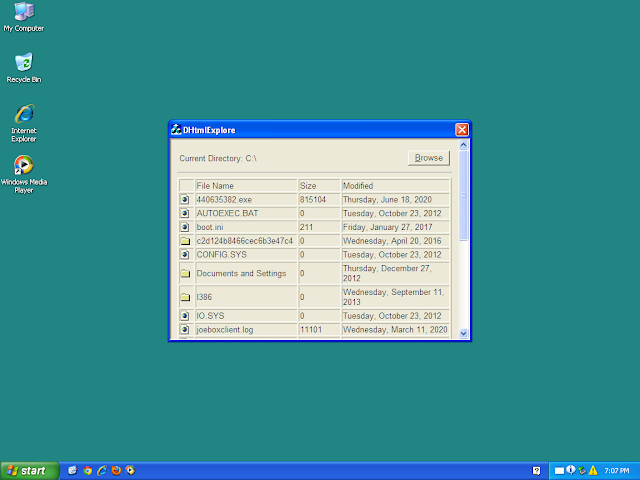
Screenshots of Detection ThreatGrid MITRE ATT&CK Win.Packed.Emotet-8082161-0 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER
Value Name: 98b68e3c
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Type
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Start
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ErrorControl
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ImagePath
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: DisplayName
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: WOW64
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ObjectName
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Description
6
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: Type
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: Start
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: ErrorControl
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: DisplayName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: WOW64
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: ObjectName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MFC100
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSHTML
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSHTML
Value Name: Type
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSHTML
Value Name: Start
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSHTML
Value Name: ErrorControl
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\EHSTORAPI
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSHTML
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSHTML
Value Name: DisplayName
1
Mutexes Occurrences Global\I98B68E3C
7
Global\M98B68E3C
7
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 190[.]144[.]18[.]198
8
87[.]106[.]136[.]232
5
87[.]106[.]139[.]101
5
80[.]11[.]158[.]65
5
37[.]187[.]72[.]193
5
79[.]143[.]178[.]194
5
91[.]236[.]4[.]234
3
190[.]19[.]169[.]69
2
Files and or directories created Occurrences %SystemRoot%\SysWOW64\NlsData0027
1
%SystemRoot%\SysWOW64\appidapi
1
%SystemRoot%\SysWOW64\cmstplua
1
%SystemRoot%\SysWOW64\EhStorAPI
1
%SystemRoot%\SysWOW64\NlsLexicons002a
1
%SystemRoot%\SysWOW64\whealogr
1
%SystemRoot%\SysWOW64\w32tm
1
%SystemRoot%\SysWOW64\lz32
1
%SystemRoot%\SysWOW64\wmdrmdev
1
%SystemRoot%\SysWOW64\PSHED
1
%SystemRoot%\SysWOW64\CertEnrollCtrl
1
%SystemRoot%\SysWOW64\msfeedsbs
1
%SystemRoot%\SysWOW64\extrac32
1
%SystemRoot%\SysWOW64\api-ms-win-core-libraryloader-l1-1-0
1
%SystemRoot%\SysWOW64\cmdl32
1
File Hashes 28f45c3bdef40c864939b203fe42b97691e96cc1a26786f542a21238452bb45b
626a83472418cc757d05ec3a1c2a2f73ba0dd90851c8c16806ce7557a979d879
806ab67b3aec3028f4132ae8b0cde816da09e337bd6380dea77b2e6cae261e23
88e3109eaa7fd6de65470cdc84618564f98fd5d2777837be6205c441f1b8a292
8bf76f5f209639df749a91a2865cf25e066f4652f5f9d791593c2e07b75299f3
922e78c72fb593a1da98c7792472c103c5af35090ad6e121fe5acedde7112892
92c7526ada570a46f13b920b071915b2efd3bb7e025d18f290c808a5b8da97a2
961915c930315db7aad15906772b8f4ef0411b5c8c3c936c6d3be550fd7656e1
b157599051151586660a5e78a98ea1bfd2ec49fdd6f133780f7acfe26ed76ba5
d161f02bf8469bba4fe10eb747e06583f4bf3d03c8cb7526e817deb21c331744
d27319306e9f21f4509ae9eb09468e71fcaf2a5dada91ae090b10291dc23f57c
d6a3e6dc6c122c4c2c7d7f3818d2de684397a38ed08022dd12905c7914366499
ea60bd0c480e51e2e5fee1aa947f06988d99db5906ba0f637de906e5b7d9ed0a
ee90f1631dfec6fcd075b687a0538a0203ae94e6dcb06c553e4dd4e1233bed34
fe5c2dace461fee5760c04d3aff6a2ecf246687c9d4b74bde795809d60b59abfCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
Screenshots of Detection ThreatGrid Malware MITRE ATT&CK Win.Trojan.Remcos-8176626-0 Indicators of Compromise IOCs collected from dynamic analysis of 20 samples Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\AUTHROOT\CERTIFICATES\75E0ABB6138512271C04F85FDDDE38E4B7242EFE
Value Name: Blob
7
<HKCU>\ENVIRONMENT
Value Name: windir
7
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNONCE
Value Name: Puzv
7
<HKCU>\SOFTWARE\REMCOS_NQTJIDYSXC
3
<HKCU>\SOFTWARE\REMCOS_NQTJIDYSXC
Value Name: EXEpath
3
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: LanguageList
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\system32\p2pcollab.dll,-8042
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\system32\qagentrt.dll,-10
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\system32\dnsapi.dll,-103
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\System32\fveui.dll,-843
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\System32\fveui.dll,-844
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\System32\wuaueng.dll,-400
1
<HKU>\.DEFAULT\SOFTWARE\CLASSES\LOCAL SETTINGS\MUICACHE\\52C64B7E
Value Name: @%SystemRoot%\system32\WindowsPowerShell\v1.0\powershell.exe,-124
1
Mutexes Occurrences Global\<random guid>
6
Remcos_Mutex_Inj
3
remcos_nqtjidysxc
3
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 172[.]217[.]164[.]142
7
172[.]253[.]122[.]132
7
172[.]217[.]197[.]102
3
194[.]5[.]99[.]132
3
172[.]217[.]197[.]101
2
172[.]217[.]197[.]138
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences doc-08-0s-docs[.]googleusercontent[.]com
7
site[.]ptbagasps[.]co[.]id
3
Files and or directories created Occurrences %TEMP%\<random, matching '[a-f0-9]{3,5}'>_appcompat.txt
9
%TEMP%\<random, matching '[A-F0-9]{4,5}'>.dmp
9
%System32%\winevt\Logs\Microsoft-Windows-CodeIntegrity%4Operational.evtx
7
%PUBLIC%\Natso.bat
7
%PUBLIC%\Runex.bat
7
%PUBLIC%\fodhelper.exe
7
%PUBLIC%\propsys.dll
7
%PUBLIC%\x.bat
7
%SystemRoot%
7
%SystemRoot% \System32
7
%SystemRoot% \System32\fodhelper.exe
7
%SystemRoot% \System32\propsys.dll
7
%PUBLIC%\cde.bat
7
%PUBLIC%\x.vbs
7
%LOCALAPPDATA%\Puzv
7
%LOCALAPPDATA%\Puzv\Muck
7
%LOCALAPPDATA%\Puzv\Puzv.hta
7
%LOCALAPPDATA%\Puzv\Puzvset.exe
7
%APPDATA%\winos
3
%APPDATA%\winos\logs.dat
3
File Hashes 2074bbaf53f1dc7f45efcf3b765e68bdb14f50a3ae1f12e8e490a6bbd81e70c9
24402c40c09ccff0f631c7aa3b43a19765dc67b486ee7e2330fd48c9b469acc0
2ee32bc032964be40559a82604a4941d7e38566e910e647e3a956ce9b07cec5c
3849ddf6618006df9e07ac84e5d5ba711c4e1c766595c08d49d0af760e5fc458
3a85dd98bc3baeee41e8bc0d121c35e792357dc5ca9518156fac2427d8e65bf3
45e4fa6c2020b4540dab321dc6f7bc98c64167127e9d9eb9bcd4e3d75b035cbb
5e0659df78b4ff35f5e0d41eb0c44758a88c78c0534152773f56c00aaf6f6437
6ecc2adaff1e68943661c5a3fd4592469151b20300ba6f0a4823066d96ae850e
85919307d926304aeff6e1dda3057238653fc6e4b62fe6a51e2fce07c44eb6cc
86fbb94d98b26ec6c8641aa5c93edc2902e755fa02863034a3c3eb33666e9fd7
8aa9dd9f443ef012e4f3a62f8cb33258b241575801742dab834e6d93a2acbf6d
8da905d01a4de39de8b8d86ab3e949736742c0c78951d754382e1c58403a5228
ae313916e1f6d6de3ec204282d3ede5b4111d8470ea2609be38891f51da7ed0e
b1d078e0b4a3026eef276cefd0ca2882992e2f64d88094e998315d390c6e5287
caabcb165ac93385c30ff79a9a2a4e862c660576e541dc34d3d9d9772e81d1fa
d783113e535cc176b515bb7697eb4b5356a387acdbd65ab70b3648856318b6fc
d8207bb056770482d0d3c289a87486a3e1c8d6038d80f56bac1b6b487b9b78ea
eaa443151a4ffca8d611d73084109b43c549ba2705f0f94fd59652e0c4809373
f168ed4028b0173b0372db15afda4fcb7cdeb7deccaad5c66ca81d578b3cfff3
fdd6591b6783f815a2ebc5cd6d5651f0e741a3dd30d256caf16defa37ef4cceeCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
Screenshots of Detection ThreatGrid MITRE ATT&CK Win.Packed.Zbot-8176461-0 Indicators of Compromise IOCs collected from dynamic analysis of 11 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
11
Mutexes Occurrences pZWQigDYwD
1
UQFZPGUeNN
1
PLzULCPZII
1
iBVoiYENNM
1
lgVpgXkved
1
CUoICrXggf
1
MBxrKHdzYe
1
zujEulyKsr
1
aMFMpDCSWZ
1
wsgBriwHpo
1
BaphSzCWyE
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 142[.]250[.]31[.]108/31
7
173[.]194[.]175[.]108/31
6
52[.]96[.]15[.]178
1
52[.]96[.]9[.]2
1
52[.]96[.]88[.]50
1
52[.]96[.]88[.]66
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences mnz-efz[.]ms-acdc[.]office[.]com
1
Files and or directories created Occurrences %APPDATA%\iexplorer.exe
7
%TEMP%\PC - 6-23-2020-9.13.28-AM.gif
4
%TEMP%\PC - 6-23-2020-9.10.28-AM.gif
3
%TEMP%\PC - 6-23-2020-9.12.28-AM.gif
3
%TEMP%\PC - 6-23-2020-9.11.29-AM.gif
2
%TEMP%\PC - 6-23-2020-9.11.27-AM.gif
2
%System32%\iexplorer.exe
2
%TEMP%\116938 - 6-23-2020-9.10.55-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.10.56-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.10.58-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.10.59-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.00-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.01-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.02-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.03-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.04-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.06-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.08-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.10-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.11-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.12-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.13-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.15-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.16-AM.gif
2
%TEMP%\116938 - 6-23-2020-9.11.17-AM.gif
2
*See JSON for more IOCs
File Hashes 2fd57d79186295b19653f2a83d099a20c5d04fbe194893aed69aa1d376046492
3afef4e594621bc5a71ba9cbf05f9d6ee55102620f3f3719bc79ae8426526405
968c9503eb535de384a86714f2e24cec5bad278bbde0ca1160583ba3c8d389b5
9725a8b3416a0cb897ea3c8482533e73a466bfd2c1a29a8b43a278dbcd231108
9817508dcfc3047752d43444f7903d7d1e8e3cd6e814e43f4fd53ea920598253
9c15c96132e2fd335dd7f5a1abefc6e408b64ff943ffd412a1fb5c5d715266f5
bd11e0fe4f8c927bde8aa40dabfc9b6d63f761618819a44e0689f23180c1be10
bffccc4ae3a7608667c043eb628cffc03b2aefb60a6258b68753a65a3dbf5088
c0529c07e87a56ca97d28d129d8d247e2af10fcf35d10f274769e6a24c09c476
c8763262a4a6edffb4338752730ec703ddd0f6a37b4dd15e2bfdeb4c93be72bb
d9c551668bcc65e80b5ded0eea293303df7d0c74b24501e836fe62c54c832278Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
Screenshots of Detection ThreatGrid MITRE ATT&CK Win.Dropper.Ramnit-8176536-0 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: ConnectGroup
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: MarkTime
13
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: Type
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: Start
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: ErrorControl
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: ImagePath
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: DisplayName
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: WOW64
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: ObjectName
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: Description
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\RS<random, matching '[A-Z]{4} [A-Z]{8}'>
Value Name: FailureActions
7
Mutexes Occurrences KyUffThOkYwRRtgPP
11
{79345B6A-421F-2958-EA08-07396ADB9E27}
8
{<random GUID>}
8
Global\KFIFavorites
6
HistoryUpgradeExecuting
6
Local\MSCTF.Asm.MutexDefault0
6
127.0.0.1:8000:Rsiggc qsmiccmq
2
47.96.133.212:8000:Rsgkgu qkqikqqa
1
121.89.216.126:9000:Rsseew icoyckqy
1
c4.ak47a.cn:1747:Superdy360
1
ljl1995.com:1747:Rskepv beokccpx
1
namenamename258123.zhuanbaoba.com:63333:Rskmms wkgyqyqo
1
127.0.0.1:8000:Rssomw iywwkoma
1
127.0.0.1:8000:Rskwsc iwwamgma
1
127.0.0.1:8000:Rsvgpp nntuecwq
1
127.0.0.1:8000:Rspgtt vvxqmgic
1
117.152.196.111:8000:Rsuogk qiewiiqs
1
notfpsever.e1.luyouxia.net:26972:26972:Rskmgq oegwyqyu
1
4562.f3322.net:9000:Rssbge pfixdvkq
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 204[.]79[.]197[.]200
11
13[.]107[.]21[.]200
9
72[.]26[.]218[.]70
9
204[.]79[.]197[.]203
6
82[.]112[.]184[.]197
6
192[.]229[.]211[.]36
6
45[.]55[.]36[.]236
6
52[.]16[.]225[.]15
6
23[.]5[.]230[.]228
6
172[.]217[.]7[.]174
6
112[.]3[.]25[.]143
6
104[.]129[.]67[.]136/31
6
172[.]217[.]197[.]113
5
65[.]55[.]44[.]109
5
20[.]36[.]253[.]92
5
23[.]218[.]116[.]185
5
23[.]13[.]208[.]102
5
172[.]217[.]197[.]138/31
5
172[.]217[.]197[.]100/31
5
172[.]217[.]197[.]102
4
104[.]129[.]67[.]138
4
76[.]13[.]32[.]147
4
152[.]195[.]14[.]41
4
23[.]196[.]52[.]77
4
108[.]174[.]10[.]14
3
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences fget-career[.]com
9
outlook[.]com
6
rover[.]ebay[.]com
6
www[.]onenote[.]com
6
www[.]msn[.]com
6
itunes[.]apple[.]com
6
contextual[.]media[.]net
6
img-s-msn-com[.]akamaized[.]net
6
www[.]autotrader[.]com
6
flights[.]msn[.]com
6
linkmaker[.]itunes[.]apple[.]com
6
carrentals[.]msn[.]com
6
static-global-s-msn-com[.]akamaized[.]net
6
www[.]skype[.]com
6
msn[.]benevity[.]org
6
www[.]fool[.]com
6
o[.]aolcdn[.]com
6
tvrstrynyvwstrtve[.]com
6
rtvwerjyuver[.]com
6
supnewdmn[.]com
6
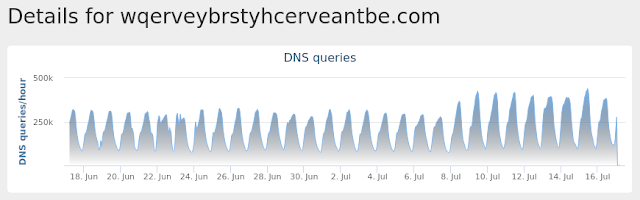
wqerveybrstyhcerveantbe[.]com
6
msn[.]lockerdome[.]com
6
blogs[.]msn[.]com
6
www[.]fubo[.]tv
6
disneyplus[.]bn5x[.]net
6
*See JSON for more IOCs
Files and or directories created Occurrences %ProgramFiles(x86)%\Microsoft
11
%ProgramFiles%\Internet Explorer\dmlconf.dat
10
%ProgramFiles%\Microsoft\DesktopLayer.exe
10
File Hashes 0163f48d0e9dcd3111e691eb8923057233cdd84106ddcbd62cb7ee52e02fc5c8
0379257b7c1fa96696b842170370125ef091fa653555d819e994143e0f4be28b
1082f4d8395dea2ea032c82befbb5fdf0de525c2fdf255b8e04196d40be25973
1f22e6aabcba1a3ee7f960ad16265a90f36c858b932d067dadb87ce24a67f3bd
24ddfaa49d23ff1c2e77fdb1fbcc08a221ea232c19910a7c42a6b1bf7bd32902
2922eaba0ab9dab526a73d0834960c8cb32d42b0d865cd73bee9b5eb27981157
3449f9c3fa8303e67b696c14696bb941c99c3bea413c3fcd2a247971e65808a9
3781c206be1febbf071c2a76203f0fc0ff5547ffef254d88d7da21c35f9bdfe5
4314d4b67eafc3db322f32601947f490bcc7dcec93cbfab5a753fc4806ca4b93
4809d4f44c7c9b6c5f03bbd35c0414fd82f62ebcb0fa1c27794797c24be26718
575edb997832ea7029b04116b8c7643871a28b03531630084adf6563afa5c249
7cbf99304ec79cd0d5a856c292ec3279e0529505b2cdd52a5e04e193448d9e90
990b55a5c7fae21e5dc71d17024c7a2ec47b4d7a7fcf3cb550bca73163805a23
a37e605ee3a952abc0c06a5a294acfc00b406d62db1b9c296ca08f4b6b5a0285
d7c27b39f146f14514eeeb013e02820de37c0ba691d082169f8ef3b4c6347b5fCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
Screenshots of Detection ThreatGrid Umbrella MITRE ATT&CK Win.Dropper.HawkEye-8176602-0 Indicators of Compromise IOCs collected from dynamic analysis of 24 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\ADVANCED
Value Name: Hidden
22
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Windows Update
20
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: iTunes
9
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Adobe
8
<HKLM>\SYSTEM\CONTROLSET001\CONTROL\SESSION MANAGER
2
<HKLM>\SYSTEM\CONTROLSET001\CONTROL\SESSION MANAGER
Value Name: PendingFileRenameOperations
2
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: AdobeR
2
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: AdobeX
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: AdoR
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: VideoGames
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Media Player
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON
Value Name: shell
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 104[.]16[.]155[.]36
12
104[.]16[.]154[.]36
10
18[.]211[.]9[.]206
4
195[.]20[.]55[.]174
3
1[.]1[.]1[.]1
2
195[.]20[.]46[.]254
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences whatismyipaddress[.]com
22
ftp[.]banclays[.]com
4
ftp[.]rbsb-uk[.]com
4
ftp[.]monocool[.]pk
4
ftp[.]eurotek[.]ga
3
hdredirect-lb6-54290b28133ca5af[.]elb[.]us-east-1[.]amazonaws[.]com
1
78[.]210[.]14[.]0[.]in-addr[.]arpa
1
169[.]241[.]9[.]0[.]in-addr[.]arpa
1
231[.]29[.]2[.]0[.]in-addr[.]arpa
1
251[.]111[.]0[.]0[.]in-addr[.]arpa
1
101[.]37[.]7[.]0[.]in-addr[.]arpa
1
mail[.]rbsb-uk[.]com
1
mail[.]prizemug[.]com
1
ftp[.]empiredecor[.]tk
1
ftp[.]eurotek[.]tk
1
ftp[.]prizemug[.]com
1
Files and or directories created Occurrences %APPDATA%\pid.txt
24
%APPDATA%\pidloc.txt
24
%TEMP%\RES<random, matching '[A-F0-9]{3,4}'>.tmp
24
%TEMP%\tmp<random, matching [A-F0-9]{1,4}>.tmp
24
%TEMP%\<random, matching '[a-z]{3}[A-F0-9]{3,4}'>.tmp
24
%TEMP%\<random, matching '[a-z]{8}'>.exe
22
%TEMP%\<random, matching '[a-z0-9]{8}'>.dll
22
%TEMP%\<random, matching '[a-z0-9]{8}'>.out
22
%TEMP%\<random, matching '[a-z0-9]{8}'>.cmdline
22
%TEMP%\holdermail.txt
20
%TEMP%\holderwb.txt
20
%APPDATA%\WindowsUpdate.exe
20
\Sys.exe
18
\autorun.inf
18
E:\Sys.exe
18
E:\autorun.inf
17
%TEMP%\SysInfo.txt
13
%APPDATA%\Windows Update.exe
13
%System32%\wbem\Logs\wbemprox.log
10
%TEMP%\RES3.tmp
10
%TEMP%\CSC2.tmp
10
%TEMP%\tmp1.tmp.txt
10
%TEMP%\dw.log
8
%TEMP%\<random, matching '[A-F0-9]{4,5}'>.dmp
8
%TEMP%\RES6.tmp
6
*See JSON for more IOCs
File Hashes 1117fdfd868cc15b5787f6ff98c0a2e9329093e91d6d352e14a9c351b1991fdb
13746e220644a60271db265fae26a592f7d49901bdb824c4f968a0fbef23b983
18d912ab6ca9ce6253d820bebb665472b5431ead7ae1dd5362c59ec8c7e1fc40
1b3715036d976877787e3213634de9928113a39733452618e2e967fb04561d91
312e4eec7cdd913b12a2988ce18e97572c2a85ab9afde72ac5b50da68fbc8f08
3c839d7f8b8770d07ddb6b5fa16d11a8024b71bdbd6dadd6ee5461fb5de59fb3
46abf2a6105b05f3c840fd95c2c3c15e03c8bafa395fa26ac8442cdcaee395d0
4770663aaa81d04a4567cca33248f1179725e09dfc69e785b4b1fd6ce706d7c7
55f9caabd50f44c66614d46da0613c6800190961288372883447a49400526c0d
7f2cf02f9b738ef140ae1e90af713c6c4b7d290f06e18b5a9e7616f4eb10a369
802ca590b720174ce7a9fff3526577a826ad81ef4d1724b5e01c93224f07fa75
8fbc3e07630dd54fafdd190e13017d4686f9f70b2c634ca073b2a369a4188032
9f3a6dae7b4601f5d8a4d4da23f4fb0111312a257d0c6a582501c8287c86e5fa
a14e5e9e6ab512d73cb755712319336f76c67ae3a3be992f5ce2b48cd131cbeb
a47f9735843f36b347871b51b03b87004efed2049cb5610f072015de56468cd8
aee6b4a83a725982dace7285dd265c695518c8253c718c8240fad5bb5a1a3b58
b52d96f54c5fecd727d4e5f1c2cccf43f0e8f606ffcb6b7729948bc109874b29
b63f7c15d2ede3088b030278456bfad6f3bd7a9e07ffd135d816704973dd7a89
bfd5efba6b056de7d35a470d2185b52ff02ada956c696de15e1f4f9b2ebefd67
c375a52fdf14b9e0ec1d3aa757f2ab4c49a6c4f5ceba7db22ca0a443e29de2f5
cea5084a781e34efd60a8736b2b2f26c2237017dabfecfae1ff2fe0c58d19f20
d5ba22a7361f2ff31855e21d2faa60449091dfd1a27103ec1a253e39d81ad3f1
ece559cc33b18ad5413ae1440b1f32d21e4f1fc88d0457eb4ee1e2874eea3b11
ed09e114587fdabe6c94919a268c6532d55241f32d43a0e06b3c0ac04a15201bCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
Screenshots of Detection ThreatGrid MITRE ATT&CK Win.Dropper.NetWire-8176767-1 Indicators of Compromise IOCs collected from dynamic analysis of 27 samples Registry Keys Occurrences <HKLM>\SOFTWARE\Wow6432Node\Microsoft\Active Setup\Installed Components\{2R7E0MB5-3C78-015R-5PA4-2N217P65OAC6}
27
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{2R7E0MB5-3C78-015R-5PA4-2N217P65OAC6}
Value Name: StubPath
27
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 66[.]154[.]113[.]239
27
Files and or directories created Occurrences %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\asferror.url
27
%APPDATA%\asferror.vbs
27
%APPDATA%\mirco
27
%HOMEPATH%\Start Menu\Programs\Startup\asferror.url
27
File Hashes 04847008b010424609cd580987144a2b9677bfe39e89209d8fcbab8d8d2f7698
09919052f61ac1660c86c85b46c21d22f62121ad61d8ac7b14d8bf27cfd5308a
0bd7a9cb935a1a2692cb120f88b0f8a4cb8042746834a023d8ae216582495e9e
11c8cd80992992b1c181e939b5622f34e5b0f3af5ab5d29f57958e7a64d4aad9
134a537201d2569aa5784c2ebdb826d42185ea1fcc24668f92fbb163b77186a8
14352e9647cf27ffb8de0c52f3d2095283deabc1b2825bf4e49bf27da8b4b531
22a45e245fe93a4b04c80bbec0ea5451f10d2dacae1aafd8fb8594a881f7cca2
2795051768e00fdd656142d08ee702a65c3b469e5f7a14a2d40f30e08ede345a
2a3c5d8da5fe94a58d673eb10f830b3932a51a70b59862abf4ff07dfd1ae2dd2
32fbb4bcd22521d42f106ffa3ee75bda96e90ea99e1208a6324e8281b86c58bb
339e5855335cd1530550ce94570da90a6db5422a4a8aae169f1dd23fda65ce04
4d950ff6aa9ba6f447001fa25b355cad5bf610410c9706e3a19222ccd924d1e0
542571f351908e93395402cfc3feba38d4f09d3c57fec1edc008d44576a7c9ad
5a6575cb82ed9dad3bd706d944461246af214677917aa1e9af1d01b59580232a
5ec67cee06f6192e9514bd730c71bc2b5c79f0b7120fcb4958aa674b15b12cde
65fe4e2908ca3ebea0d3e697e3c3e686e171e27ec2f62ebdb9f36ed90db47d74
6d159c2f3b6f1fd253503f7ee0d883f0e8cb4ae02ca14e92e96c6546b14b03d5
6fdfb8c930755351f594cf9ef176208464708d121e6893cf6204bb7e13b62a69
79581bda91ef8fb31f72d8c5615c2f4963aeec56360dafb03ff6c67d1f489e56
85b4e1882607f4faa02a6eb9e50be0baeefbcfd8b271ee277fc5a7eb578285c1
89541dbe2042acee8e94d6e65a77ad2ea66a9645a00a879ab00d9bd719e7ea84
8db080f182124b049405bda1d07d9d9dd0a2aecc19fed8edbcfc40f4dbc0dbb0
9452a2f66b89a471be96088bf8a42d2d6fcd411502280b6b0bddd010d1ea480c
9eb9fa01d1858d378bc391d1ea73e53d18eb8be04dea25b97be302f0cc5f2891
af61ecaffad4e441df4726871261a738eed18b62ff72ee015e61d8d362b6dc17*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
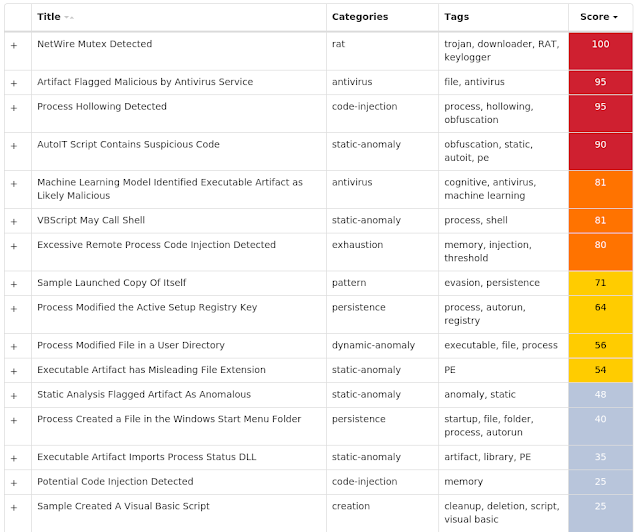
Screenshots of Detection ThreatGrid MITRE ATT&CK Win.Ransomware.TeslaCrypt-8182300-0 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000009
Value Name: Element
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\250000E0
Value Name: Element
15
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\SYSTEM
Value Name: EnableLinkedConnections
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000041
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000041
Value Name: Element
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000020
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000020
Value Name: Element
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000040
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\16000040
Value Name: Element
15
<HKLM>\BCD00000000\OBJECTS\{926583E4-EF64-11E4-BEED-D6738078AD98}\ELEMENTS\250000E0
15
<HKCU>\SOFTWARE\XXXSYS
15
<HKCU>\SOFTWARE\XXXSYS
Value Name: ID
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: gatert-12010
15
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: gatert-12010
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.CHECK.0
Value Name: CheckSetting
15
<HKCU>\Software\<random, matching '[A-Z0-9]{14,16}'>
15
<HKCU>\Software\<random, matching '[A-Z0-9]{14,16}'>
Value Name: data
15
Mutexes Occurrences __sys_234238233295
15
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 176[.]74[.]179[.]58
15
209[.]127[.]83[.]225
15
104[.]247[.]82[.]14
15
Domain Names contacted by malware. Does not indicate maliciousness Occurrences en[.]wikipedia[.]org
15
www[.]torproject[.]org
15
www[.]sedo[.]com
15
southinstrument[.]org
15
grant-pro[.]com
15
iicsdrd[.]com
15
bddadmin[.]desjardins[.]fr
15
dunyamuzelerimuzesi[.]com
15
educarpetas[.]com
15
83gd65jfh24jbrwke43[.]brocksard[.]su
15
pp4dehh5nlkcs[.]pesslaugh[.]com
15
ss7fh33dfnourebfle[.]geckoyao[.]com
15
Files and or directories created Occurrences \$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I478AKJ.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4FI238.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4FKVBH.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I4QK3KJ.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I5QX7W9.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I77RW1L.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I7J37KF.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$I9NSD58.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IANXEE8.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IC5NB1M.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$ID60W3E.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IIUTK07.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IJE160U.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IKAVPAE.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IL2NS3P.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$INKC8CM.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IP8M1EE.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IPDP9E0.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$ISIYA4I.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IV54ALI.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IWK2JPN.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IWYYKMD.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IXC3P46.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$IZ7KADN.txt
15
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$R0Y9SM6.txt
15
*See JSON for more IOCs
File Hashes 033359631f6cd3edd2d33980eda34911b7ec5857c895752f9bf6b888da87b45f
1e11feb89090e04c3e359f608e27c3cfa3e627eb1884f2318a95d94a472bb979
2871505f0d7b54a5880b981e1602eef2e67f7bab5546bf435eb94313164112f4
3b66c9c5140bb7a390f6c239baf060360aa5139219c54cb8b219e752801165e2
47e6de6c9574a2c98e595f58c0b7e89363c15761b67a867e85e25916df79a92b
618d6d2dd1b6a5eebc0551477efaf32c62777ffc7a5092c5852844ea8783a4cd
8824cfb7139627c0620b6304bbc53dff98b690dd40ab572e3ae28854a46e632c
9a429001603d1bbea797bd12761f4ad31aafb08991c27628148dccc5e00f640f
ac1c35ee74304f857fe579be4546b404ac0f34f02a21566a87eaac032efdeef7
bbb6334d2105694a7f191109e1176a329915e0a8587be2fed74855f757b5331e
d8c984fabf9b08bed720685edbdd284f55dc782ff126d82d285be9a96976e236
e6572ba93fc9fedcbd7d60eaf9c1076f46f913b8549c74077b889566cd6ebcc7
ec45bb7d7c6dec2afc90f72200b28b01e2d6c6c2e1011cef99c08f402118dd8b
ee97c569b2f0951b5b3ef9f1c9cd8e5190a871f694e9631cfd4e3e52f5b6e35b
f13e919456801f63622955376055f9a1ae183ceacaeeaa630041c332f98cc83aCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
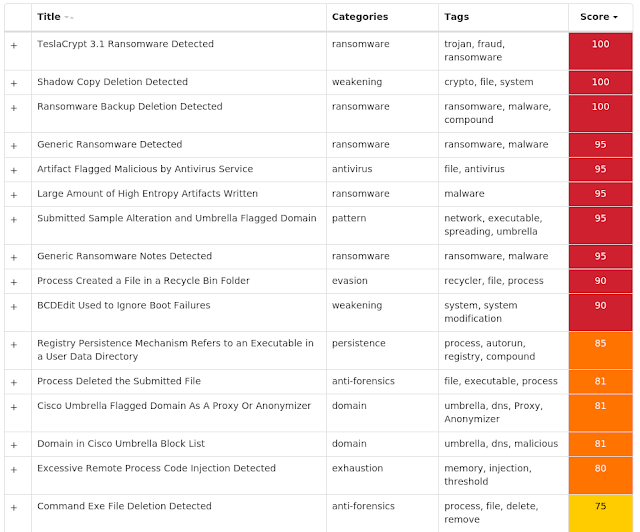
Screenshots of Detection ThreatGrid MITRE ATT&CK Win.Packed.Zusy-8182349-0 Indicators of Compromise IOCs collected from dynamic analysis of 19 samples Registry Keys Occurrences <HKCU>\SOFTWARE\XTREMERAT
1
<HKCU>\SOFTWARE\XTREMERAT
Value Name: Mutex
1
Mutexes Occurrences Global\<random guid>
16
ZHC43hxiAT
1
ZHC43hxiATPERSIST
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 162[.]125[.]8[.]15
5
204[.]74[.]99[.]100
3
138[.]201[.]21[.]203
2
104[.]27[.]162[.]117
2
96[.]47[.]230[.]69
1
104[.]23[.]98[.]190
1
199[.]91[.]152[.]154
1
104[.]27[.]163[.]117
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences dl[.]dropboxusercontent[.]com
5
www[.]site[.]com
3
rghost[.]net
3
ar[.]rghost[.]net
2
pastebin[.]com
1
directxex[.]com
1
dc203[.]gulfup[.]com
1
download1654[.]mediafire[.]com
1
Files and or directories created Occurrences %TEMP%\dw.log
18
%TEMP%\<random, matching '[A-F0-9]{4,5}'>.dmp
18
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\Server.exe
16
%TEMP%\x.html
1
%APPDATA%\Microsoft\Windows\Templates\Camfrog.exe
1
File Hashes 0acd6d045bb4f7453cb2348cb5687cd6213c04fa1a2c354cfad213b6eba5f4ec
1fdea5b9d89ab62a297e9eb2101389b21b0cb110f0efef07b9e86cd940d671cd
2b6d1b96124cfee83314000e9bc54c18c5654ca04eaa839ec3c23834a101ebd9
2f86060cc9aa517691719c349bcdd5f0fdf2800044566ef42f0ce7a94156f8e1
3da92815d869ae0faf1c54d2370aee6b3008e1e4d9f09520d71d3b4476755ad1
427f511ed3def0ec25925ffc6826a1041d4cafd96c83608ac493653f7525274e
5a08360182282a60da516c1bdc150ab368684075f5a84ce7d24ad2ff0400ce2b
625f656a9964d748c3ab929defaef51b4c0c123b2527db44c7f0eccb0c490c5b
77093ad246b7f6a7731f5ae14bfbcc151f730dbbee655f6141237f3330427a0d
9bb6bfbf0b481a98853e8e381a2353733f6514623cce14b1fd37bd24a65e45b8
a0d08aaacf4f3f35d1833179bd75e271de1fda2a2191706e1c0157c30c3704cd
b22547c35a9a810aaff8c400e655362666d12fed13ed408df9a4e86ddb8fa55d
d0978379503a84d85b44dfbe5aed24553b414828417f04acc0104bbf2b2f34b5
e0e5b59eaf6601af850145bb7538e7b71bd577965059cb2ee0fe0c8c1e1d722f
ec9fa20e89ad21b091880dc2d7c531eddfb198a1779012fbf064ddc3e1cf36d5
f09ee6861b15d573c9ec764fb5d7c6e1b0f1110bc612573143b3db9ca12711b7
f5e881fddbcf08ad2c8644529a0a9c311cd6a7b20cf6b594214abfbc7193f9d0
fa4c8f09999b3a0613a83827d3441858c5bf2373a10be72dc8c0ae886d199aff
fff878c113c7d539047c164419fbca2b429b53e3584fae1d2aa1e7b27ffc1a6eCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
Screenshots of Detection ThreatGrid MITRE ATT&CK Exploit Prevention Cisco AMP for Endpoints protects users from a variety of malware functions with exploit prevention. Exploit prevention helps users defend endpoints from memory attacks commonly used by obfuscated malware and exploits. These exploits use certain features to bypass typical anti-virus software, but were blocked by AMP thanks to its advanced scanning capabilities, even protecting against zero-day vulnerabilities. Dealply adware detected - (15707)
DealPly is adware, which claims to improve your online shopping experience. It is often bundled into other legitimate installers and is difficult to uninstall. It creates pop-up advertisements and injects advertisements on webpages. Adware has also been known to download and install malware.
CVE-2019-0708 detected - (3359)
An attempt to exploit CVE-2019-0708 has been detected. The vulnerability, dubbed BlueKeep, is a heap memory corruption which can be triggered by sending a specially crafted Remote Desktop Protocol (RDP) request. Since this vulnerability can be triggered without authentication and allows remote code execution, it can be used by worms to spread automatically without human interaction.
Installcore adware detected - (1928)
Install core is an installer which bundles legitimate applications with offers for additional third-party applications that may be unwanted. The unwanted applications are often adware that display advertising in the form of popups or by injecting into browsers and adding or altering advertisements on webpages. Adware is known to sometimes download and install malware.
Process hollowing detected - (1589)
Process hollowing is a technique used by some programs to avoid static analysis. In typical usage, a process is started and its obfuscated or encrypted contents are unpacked into memory. The parent then manually sets up the first stages of launching a child process, but before launching it, the memory is cleared and filled in with the memory from the parent instead.
Excessively long PowerShell command detected - (1490)
A PowerShell command with a very long command line argument that may indicate an obfuscated script has been detected. PowerShell is an extensible Windows scripting language present on all versions of Windows. Malware authors use PowerShell in an attempt to evade security software or other monitoring that is not tuned to detect PowerShell based threats.
Squiblydoo application whitelist bypass attempt detected. - (884)
An attempt to bypass application whitelisting via the "Squiblydoo" technique has been detected. This typically involves using regsvr32.exe to execute script content hosted on an attacker controlled server.
Gamarue malware detected - (535)
Gamarue is a family of malware that can download files and steal information from an infected system. Worm variants of the Gamarue family may spread by infecting USB drives or portable hard disks that have been plugged into a compromised system.
Bluestacks adware detected - (482)
Bluestacks adware displays unwanted advertising in the form of popups or by injecting into browsers and altering advertisements on webpages. Adware has also been known to download and install malware.
Palikan browser hijacker detected - (358)
Palikan is a potentially unwanted application (PUA), browser hijacker, a type of malware that most of the time does not explicitly or completely state its function or purpose. When is present on the system, it may change the default homepage, change the search engine, redirect traffic to malicious sites, install add-ons, extensions, or plug-ins, open unwanted windows or show advertising. Palikan commonly arrives as a file dropped by other malware or as a file downloaded
unknowingly from a malicious site. It has also been closely associated with DealPly.
Kovter injection detected - (192)
A process was injected into, most likely by an existing Kovter infection. Kovter is a click fraud Trojan that can also act as an information stealer. Kovter is also file-less malware meaning the malicious DLL is stored inside Windows registry and injected directly into memory using PowerShell. It can detect and report the usage of monitoring software such as wireshark and sandboxes to its C2. It spreads through malicious advertising and spam campaigns.