Today, Talos is publishing a glimpse into the most prevalent threats we've observed between Nov. 27 and Dec. 4. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org , or ClamAV.net .
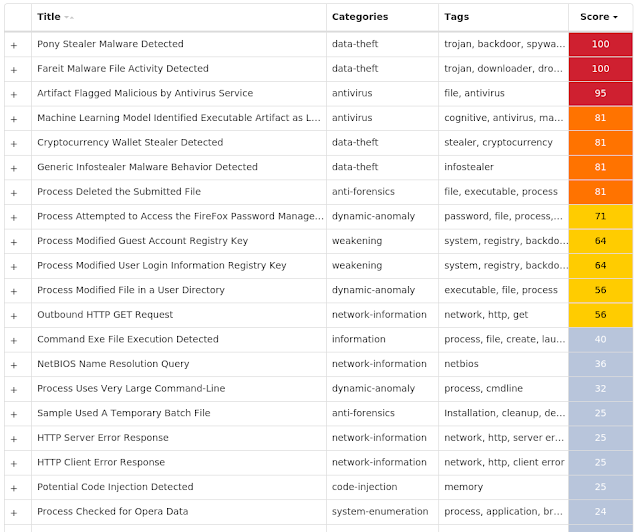
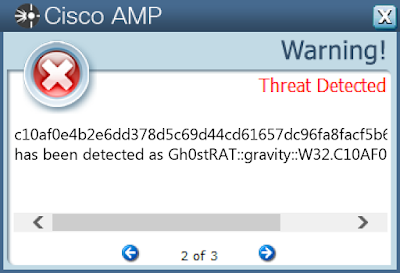
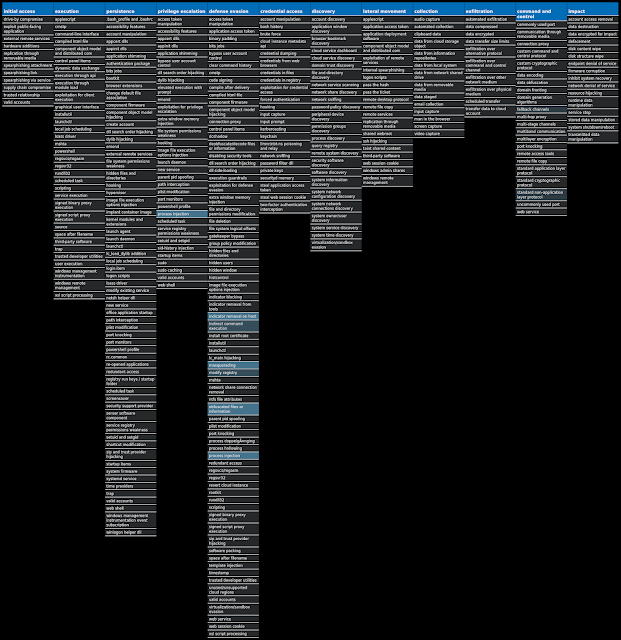
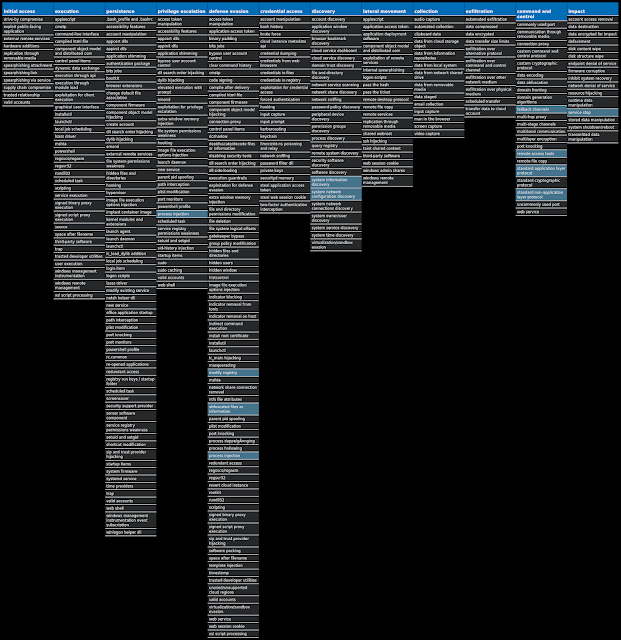
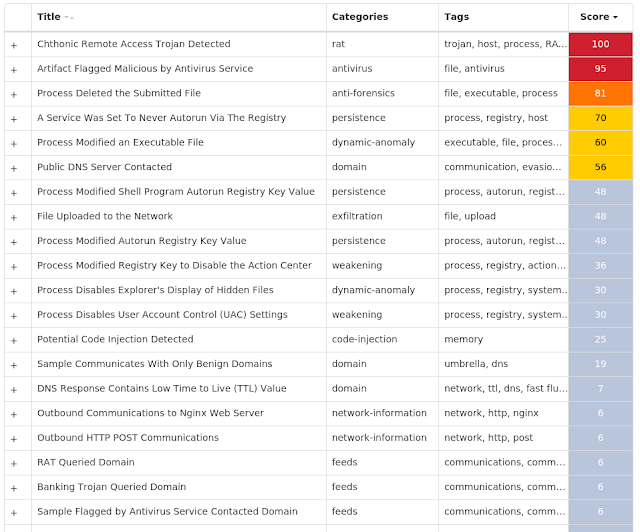
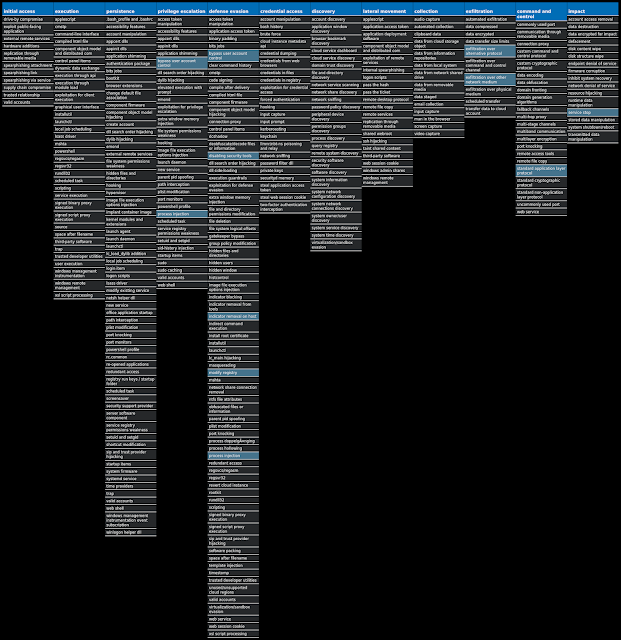
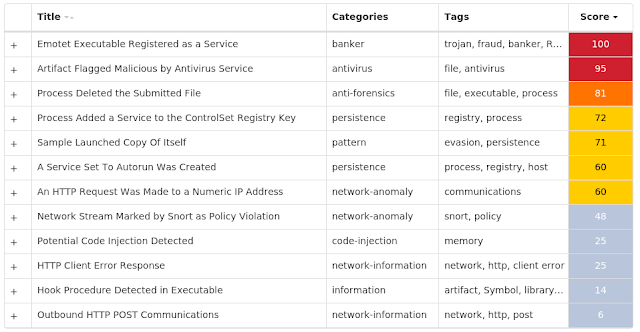
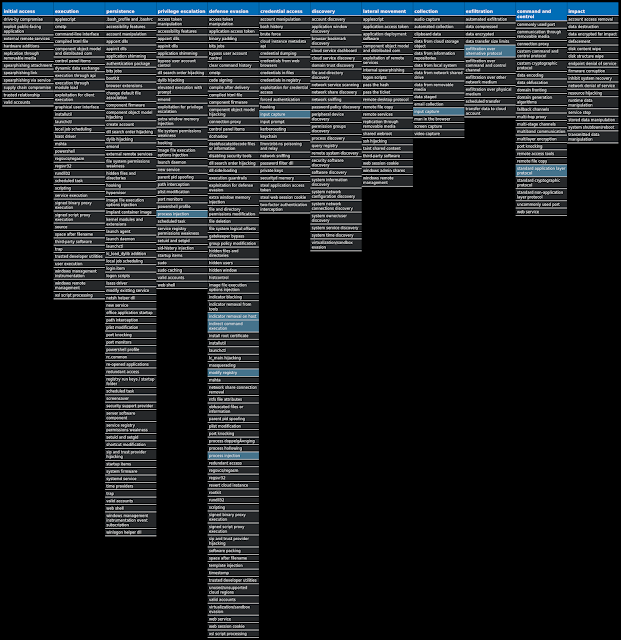
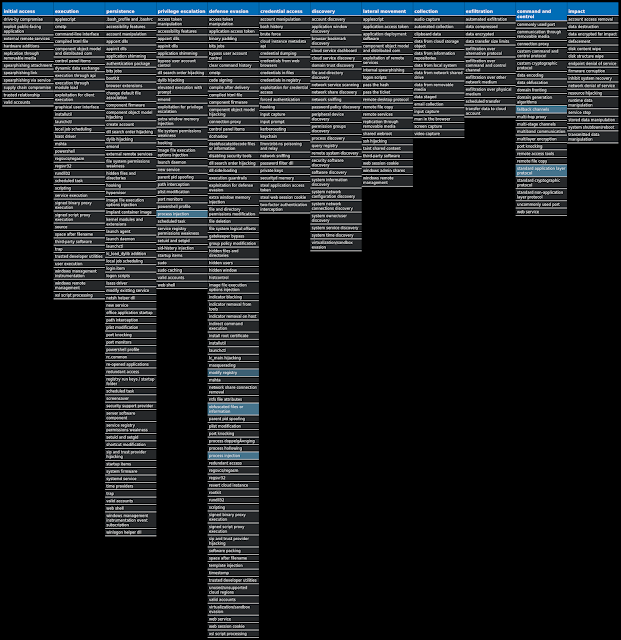
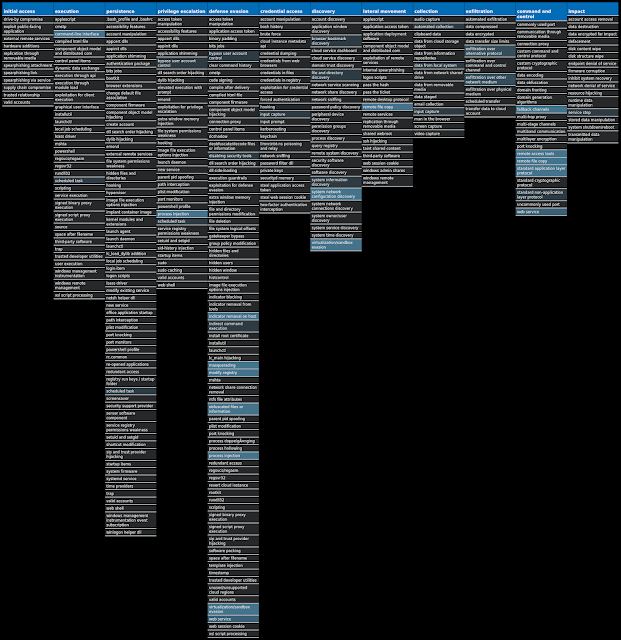
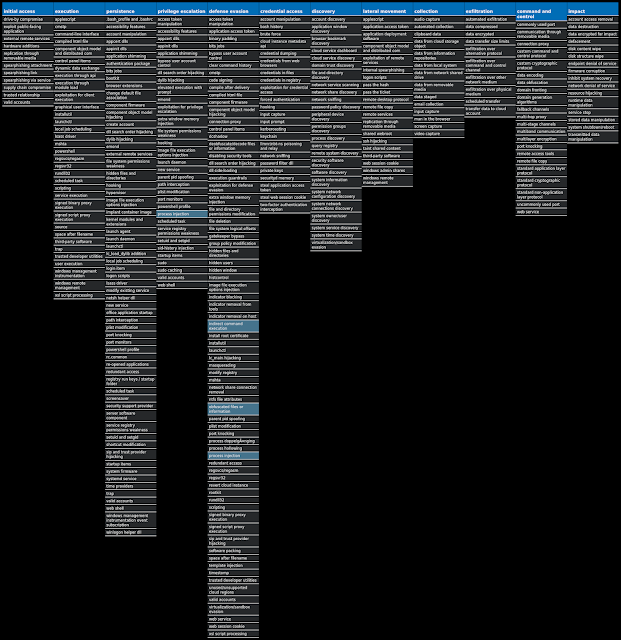
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found here that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name Type Description Win.Packed.Fareit-9801148-0
Packed
The Fareit trojan is primarily an information stealer that can also download and install other malware.
Win.Dropper.Gh0stRAT-9800485-0
Dropper
Gh0stRAT is a well-known family of remote access trojans designed to provide an attacker with complete control over an infected system. Capabilities include monitoring keystrokes, collecting video footage from the webcam, and uploading/executing follow-on malware. The source code for Gh0stRAT has been publicly available on the internet for years, significantly lowering the barrier for actors to modify and reuse the code in new attacks.
Win.Packed.ZeroAccess-9800486-1
Packed
ZeroAccess is a trojan that infects Windows systems, installing a rootkit to hide its presence on the affected machine and serves as a platform for conducting click-fraud campaigns.
Win.Trojan.Chthonic-9800490-1
Trojan
Chthonic is a banking trojan derived from the Zeus family of banking malware. It is typically spread via phishing emails and attempts to steal sensitive information from an infected machine. Chthonic has also been observed downloading follow-on malware such as Azorult, another information stealer.
Win.Dropper.Emotet-9800496-0
Dropper
Emotet is one of the most widely distributed and active malware families today. It is a highly modular threat that can deliver a variety of payloads. Emotet is commonly delivered via Microsoft Office documents with macros, sent as attachments on malicious emails.
Win.Packed.Nymaim-9800769-1
Packed
Nymaim is malware that can be used to deliver ransomware and other malicious payloads. It uses a domain generation algorithm to generate potential command and control (C2) domains to connect to additional payloads.
Win.Dropper.Tofsee-9800794-0
Dropper
Tofsee is multi-purpose malware that features a number of modules used to carry out various activities such as sending spam messages, conducting click fraud, mining cryptocurrency, and more. Infected systems become part of the Tofsee spam botnet and are used to send large volumes of spam messages in an effort to infect additional systems and increase the overall size of the botnet under the operator's control.
Win.Trojan.Barys-9800808-0
Trojan
This is a trojan and downloader that allows malicious actors to upload files to a victim's computer.
Threat Breakdown Win.Packed.Fareit-9801148-0 Indicators of Compromise IOCs collected from dynamic analysis of 27 samples Registry Keys Occurrences <HKCU>\SOFTWARE\WINRAR
27
<HKCU>\SOFTWARE\WINRAR
Value Name: HWID
27
<HKLM>\SAM\SAM\DOMAINS\ACCOUNT\USERS\000003E9
Value Name: F
27
<HKLM>\SAM\SAM\DOMAINS\ACCOUNT\USERS\000001F5
Value Name: F
27
<HKLM>\SAM\SAM\DOMAINS\ACCOUNT\USERS\000003EC
Value Name: F
27
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 103[.]91[.]189[.]178
27
104[.]31[.]88[.]140
9
104[.]31[.]89[.]140
9
172[.]67[.]192[.]156
9
204[.]79[.]197[.]200
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences dr-sea[.]by
27
dreamsmile[.]24host[.]lt
27
kuiwit[.]ac[.]th
27
skopych[.]kiev[.]ua
27
somad[.]md
27
Files and or directories created Occurrences %TEMP%\-<random, matching '[0-9]{9}'>.bat
26
%TEMP%\<random, matching '[0-9]{5,6}'>.bat
22
%TEMP%\-1472438118.bat
1
File Hashes 00b74cf7e45b094f738e7265d7ab1809b6bae393354da7d3aa68e0cdfed0f7ab
01c97be416800ddfda585e8378c4c481dfae942c4eea7d114a665435e8c0777e
0314b86123be26d9572f9fe84476eb65c5e592d111f57aa810c56c483f022561
0504e4a93be7f4766e781c719ff10ed1b90c3238443a2267a310e4c5208e4d9d
06e811d7b34b46515a450d1536aa9c35b70e92224a73ea17f8ff3653f7c4a0cb
107d0d11eb9afc78c42ac5d2ba39de6d25f4e353bdd160359170e68d52eda5cb
14d6d71aed6b63c6749eb4555036edb62c65961dd19b3b03db80bf94f070256e
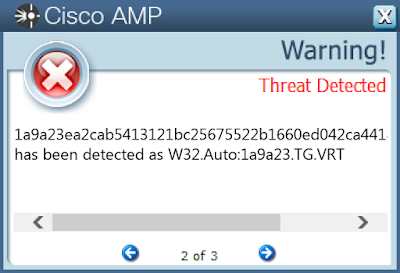
1a9a23ea2cab5413121bc25675522b1660ed042ca4418586aeaefeb939017b2d
1dd5adcd80870ad36c47180a3db8c26d54b80bc3c958581bb0d028fa026eafc6
1e8c220698b84baadf367125e8c6fdb43f29bb820fc0275c01889d104d63ef55
1ef9937d2da36f2f5cf12d2fd0a39c46b5b8b319da9e4c99ae111cc8b3e65918
2756502f16562c6f0bd8e8830d3d278c6b2cb16c3151cf2e116da4113d8444de
3b0bd8920edabf76b82784be366e2ab1f9194a6fc4d69de2925ae82fcd4ff59f
3e94c3c396f21b930cbadea8deab10c67dd8d0c27e4dc29de7dd91208151f462
4440c90bed32987322b58886b56a44ad96050b3c1c26d310da66ba6e85ce6941
50eb6d588f1a98faa048b20a3b85cf878b8d9bdbaf556334a42f37123968d3f7
54df0a7441a3ada52cc06037505ef6619b746bad099fe72349d5b19907ef788a
5f7d7f696fdf5268bad6a09d819ef50ae73a524497212ee7634f49f0542dcd92
733de435b15d88f421201530513eb56c350aba2fb13a93254f7c7680a205a471
87998a1040645b873a58da92ca71a192ccfe8a019fd7801803813660de0c6c99
9d4c3523170149ebacdca720f1937d52176c28d8df6918bed9b9d2f8b52bf64f
9d8e3ffe49efba880fe1c37a90d85ed6b74032e283d30dcef3ba2e1b0160d2c4
aaff6d8ecee652a27c5e643e7621508d4e670ac8f98131d9cccbd3a969273c9a
acf3317a4d4372b38eff343cd2695faabfe77898a9e5ce997af3564d8f7abcc0
ae2685a9016129d92fd8adddfd96376aa986e87851d83470d1ec36b8228163ef*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Dropper.Gh0stRAT-9800485-0 Indicators of Compromise IOCs collected from dynamic analysis of 26 samples Registry Keys Occurrences <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Lostlove_K
7
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: Description
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: Start
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: ErrorControl
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: DisplayName
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: WOW64
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: ObjectName
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: Type
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\STUVWX ABCDEFGH JKL
Value Name: ImagePath
2
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
Value Name: DisplayName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
Value Name: WOW64
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
Value Name: ObjectName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\KLMNOP RSTUVWXY BCD
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\KLMNOP RSTUVWXY BCD
Value Name: Start
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\KLMNOP RSTUVWXY BCD
Value Name: DisplayName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\KLMNOP RSTUVWXY BCD
Value Name: WOW64
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\KLMNOP RSTUVWXY BCD
Value Name: ObjectName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\KLMNOP RSTUVWXY BCD
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\GHIJKL NOPQRSTU WXY
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
Value Name: Type
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
Value Name: ErrorControl
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\QRSTUV XYABCDEF HIJ
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\HIJKLM OPQRSTUV XYA
1
Mutexes Occurrences 127.0.0.1
6
mingyemo.3322.org
4
www.baidu.com
3
103.248.220.13
2
seo.kfj.cc
1
118.25.217.14
1
111.67.192.136
1
116.6.103.201
1
122.112.229.41
1
53074960.nat123.cc
1
192.168.1.138
1
lht1361828085.3322.org
1
bqcyyx.com
1
27.154.146.235
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 204[.]79[.]197[.]200
5
61[.]157[.]95[.]47
4
103[.]248[.]220[.]13
2
118[.]25[.]217[.]14
1
107[.]175[.]137[.]138
1
119[.]28[.]51[.]44
1
111[.]67[.]192[.]136
1
122[.]112[.]229[.]41
1
116[.]6[.]103[.]201
1
113[.]17[.]12[.]40
1
27[.]154[.]146[.]235
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences mingyemo[.]3322[.]org
4
www[.]wshifen[.]com
2
seo[.]kfj[.]cc
1
53074960[.]nat123[.]cc
1
bqcyyx[.]com
1
lht1361828085[.]3322[.]org
1
File Hashes 031069be38b4c5120842116f7c00748dced396e88fc1e564e459c241d0127886
21622a4f36b8eaf2017cadc325b6b5febb83ff9bd284c6c125d67b7e2b813d03
218515dcf5a4d4701a4699220f29c31c7843d7d06e9d42cc9d61a65352bbf10e
2ad783cf145223a770a12e9f3028e8da8afafdbebee44666f20d53e57f32260a
381f9d6dddaa1968146d70d77b2246e2e12b55087fb0633fbd1cd53b55296419
4ba316423956b8f15f2350a31fe422d0c94bae203f9661590a4e39f45b28f1f8
535a8d411eb40388d47006f6287daffad76bb8fd4be9b084035dfdeacabafb2c
54723ed987c1551700d3df12044781debe94745f4f05fa7dd39b903f93bf6ae4
554de32c75c02cf3df0d720320621b8d47ba442577813c0446b0e82bfd7b35c9
564f404f75de771978522db628f91eaed327de25812cf1206956f79863e76532
82059a5ab0006a6051c58411f88ef73867144e56302f1aa2bfc29276dbc9b0b8
8db50612c42f4950dcce5fa30b8fa21e98afa31b9952ca89bd09802b19e1f5c6
98df522c95adac50f1a84a93fdd1816b9510512df42e5474f1fa8bf19aef5763
99b4527c96768e0ea55140e46f214ccd2dfa0323ccca1e6a6018dad0fb87f2c3
9d6168140797749561d9ecaaace37e4321a1f8ecb80891246669d666bbf39b06
a6ec5317c5de2bf66d0746ca8623f965cb8e077ca8619a6173cddde4cf825380
a7413a49303175bce76671764e4e508b77d64cc9425be99df7dded791cb9a238
ab3c2fd2dcae843ed7d74651f7f8a912a365f43b33deae0013de94d2af2270d5
acc6c7612ffb27fd98753d8c58ea3efe4e38c5c8b57e5424f1827e829d585013
ad85f99b2d8de491c472aa7526dd02c4e788c2c7fbda519eb2e967c1419d3ec9
ae333c03347a1d420b46ed6bb66d8faca475e35bd1b01a9d46145a2d9d90bae4
b2bf5993d399a91c2ef2d3629a201c8f97702b9359c0bef119e3391eaf47acab
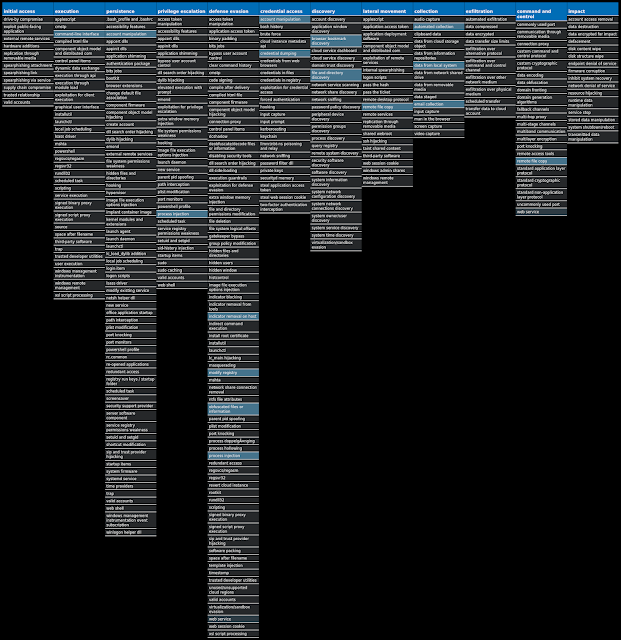
c10af0e4b2e6dd378d5c69d44cd61657dc96fa8facf5b61f45c9b49071208811
c1fa3255fb4d6182228812ce93877693494c308fae7ff5810c137625aaee3d76
cfbdaf22a60c8a45f95e30e6d95232187d0b68a4d0ce24988d8909aa1e8d1625*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
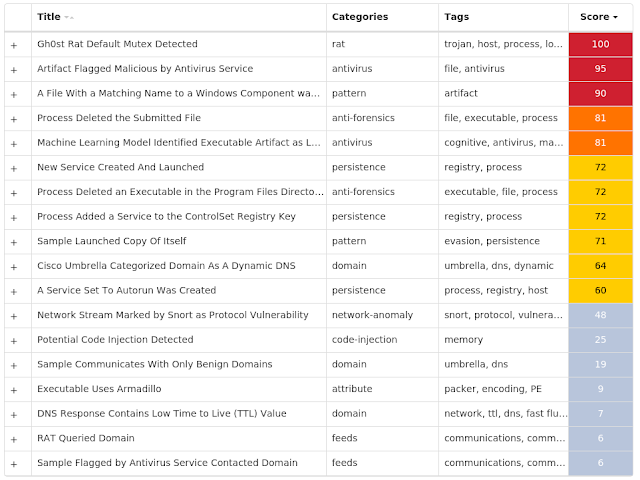
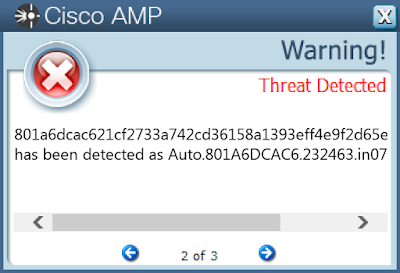
Screenshots of Detection AMP
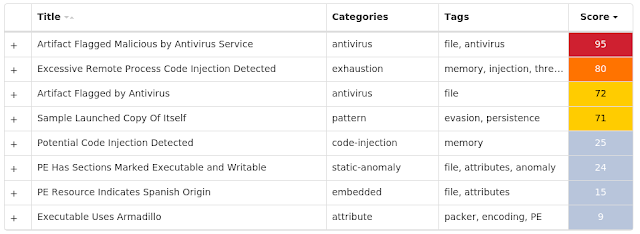
ThreatGrid
MITRE ATT&CK Win.Packed.ZeroAccess-9800486-1 Indicators of Compromise IOCs collected from dynamic analysis of 16 samples Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: Start
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS
Value Name: Start
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC
Value Name: Start
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\IPHLPSVC
Value Name: Start
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS
Value Name: DeleteFlag
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC
Value Name: DeleteFlag
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: DeleteFlag
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\BROWSER
Value Name: Start
16
<HKCR>\CLSID\{FBEB8A05-BEEE-4442-804E-409D6C4515E9}\INPROCSERVER32
Value Name: ThreadingModel
16
<HKCR>\CLSID\{FBEB8A05-BEEE-4442-804E-409D6C4515E9}\INPROCSERVER32
16
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Windows Defender
16
<HKLM>\SOFTWARE\CLASSES\CLSID\{5839FCA9-774D-42A1-ACDA-D6A79037F57F}\INPROCSERVER32
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS
Value Name: Type
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS
Value Name: ErrorControl
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\IPHLPSVC
Value Name: Type
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\IPHLPSVC
Value Name: ErrorControl
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\IPHLPSVC
Value Name: DeleteFlag
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: Type
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: ErrorControl
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC
Value Name: Type
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC
Value Name: ErrorControl
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\BFE
Value Name: Type
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\BFE
Value Name: Start
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\BFE
Value Name: ErrorControl
16
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\BFE
Value Name: DeleteFlag
16
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 209[.]68[.]32[.]176
16
114[.]140[.]13[.]110
16
64[.]184[.]203[.]87
16
66[.]74[.]65[.]21
16
75[.]69[.]92[.]137
16
173[.]161[.]53[.]61
16
67[.]82[.]249[.]90
16
71[.]87[.]111[.]92
16
75[.]64[.]22[.]81
16
181[.]47[.]5[.]125
16
95[.]111[.]225[.]124
16
181[.]165[.]92[.]121
16
118[.]168[.]183[.]114
16
125[.]58[.]66[.]125
16
61[.]227[.]47[.]110
16
24[.]166[.]59[.]97
16
71[.]97[.]99[.]170
16
1[.]160[.]225[.]1
16
68[.]230[.]236[.]85
16
97[.]104[.]42[.]173
16
111[.]248[.]215[.]43
16
178[.]158[.]65[.]14
16
114[.]162[.]146[.]65
16
190[.]181[.]207[.]76
16
24[.]181[.]13[.]254
16
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences j[.]maxmind[.]com
16
Files and or directories created Occurrences %System32%\LogFiles\Scm\e22a8667-f75b-4ba9-ba46-067ed4429de8
16
\$Recycle.Bin\S-1-5-18
16
\$Recycle.Bin\S-1-5-18\$0f210b532df043a6b654d5b43088f74f
16
\$Recycle.Bin\S-1-5-18\$0f210b532df043a6b654d5b43088f74f\@
16
\$Recycle.Bin\S-1-5-18\$0f210b532df043a6b654d5b43088f74f\L
16
\$Recycle.Bin\S-1-5-18\$0f210b532df043a6b654d5b43088f74f\U
16
\$Recycle.Bin\S-1-5-18\$0f210b532df043a6b654d5b43088f74f\n
16
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$0f210b532df043a6b654d5b43088f74f
16
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$0f210b532df043a6b654d5b43088f74f\@
16
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$0f210b532df043a6b654d5b43088f74f\L
16
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$0f210b532df043a6b654d5b43088f74f\U
16
\$Recycle.Bin\S-1-5-21-2580483871-590521980-3826313501-500\$0f210b532df043a6b654d5b43088f74f\n
16
%ProgramFiles%\Windows Defender\MSASCui.exe:!
16
%ProgramFiles%\Windows Defender\MpAsDesc.dll:!
16
%ProgramFiles%\Windows Defender\MpClient.dll:!
16
%ProgramFiles%\Windows Defender\MpCmdRun.exe:!
16
%ProgramFiles%\Windows Defender\MpCommu.dll:!
16
%ProgramFiles%\Windows Defender\MpEvMsg.dll:!
16
%ProgramFiles%\Windows Defender\MpOAV.dll:!
16
%ProgramFiles%\Windows Defender\MpRTP.dll:!
16
%ProgramFiles%\Windows Defender\MpSvc.dll:!
16
%ProgramFiles%\Windows Defender\MsMpCom.dll:!
16
%ProgramFiles%\Windows Defender\MsMpLics.dll:!
16
%ProgramFiles%\Windows Defender\MsMpRes.dll:!
16
%ProgramFiles%\Windows Defender\en-US:!
16
*See JSON for more IOCs
File Hashes 207793677b889bf22c8f28120df0ab1cca69e23eb5213bfda5b474a0472f3fff
2263c1eb4d302492f261a35f02ac9257baaa1a1d8f0c0025459aef18dfde14e9
34d6f25484edc517676af1b474d0dcc9fdf8277585206f3dfe1b9dc41a8e1d30
52818de60a1238d208ec65ca00ae14d152ce2707104b02b9bb662533c33f9b80
5d7810ab55189a068ae5ceef92f5d95ea105716f7abb7fdaa8db368bcc997c04
8f5c02d7501229d5a06f864a936a76552fa03688860533ac46de9b1a881599db
9fdd46b8fac611813d0610ddc9a74be2534552f84037a021f2111f8cfcd02669
c702947e68cebfde3eafa8b78711ba0c536e44912d7b4984a9055aa22d7ccedf
ca72d0ae5eb6e9e50fad7cea56c5048dc738024ed13750da83040fe0a5984101
cb01f4749caef72ea8aaf8c166aa5b572f8bd5295779500cb0e5e8f1a2c38dc9
cd669d8bc591e23169c703f49a20d7446a8a6db51c959334e9a5a6650882703e
d8b62bc60696d110df3d97c4ebcb5d2bd0a0c0445ce4a86a5a86c7e494f4c8d0
e0d5bc01f2e3465b7dce3eb791b7e455a7bbd2c109a604312384d99e93f9b6b4
ef804ddc84810a362e4c70f3bc1eb1650254acaabe33ffe9e1ed65a6ddd82067
f023618b0b87c2b9c5115bfd3342c694564219757c1b5125c042f5a0f17ae682
f8c1f6de0ec2d17ad26aae9fa2c5a33a9105cda60251cc388bd4c2c624d738e4Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
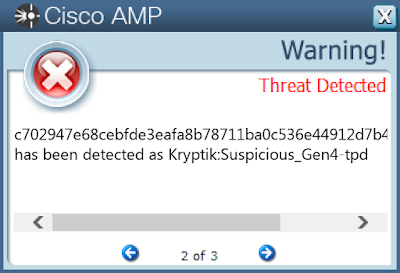
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Trojan.Chthonic-9800490-1 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\ADVANCED
Value Name: Hidden
15
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\SYSTEM
Value Name: EnableLUA
15
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: Start
15
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WINDEFEND
Value Name: Start
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\ADVANCED
Value Name: ShowSuperHidden
15
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC
Value Name: Start
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER
Value Name: HideSCAHealth
15
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER
Value Name: HideSCAHealth
15
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WUAUSERV
Value Name: Start
15
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER
Value Name: TaskbarNoNotification
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER
Value Name: TaskbarNoNotification
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWS
Value Name: Load
15
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 1081297374
15
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN
Value Name: 1081297374
15
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN
15
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 40[.]70[.]224[.]146
15
104[.]42[.]225[.]122
11
62[.]168[.]65[.]36
2
78[.]156[.]103[.]10
2
204[.]79[.]197[.]200
1
13[.]107[.]21[.]200
1
91[.]189[.]182[.]32
1
195[.]113[.]20[.]2
1
92[.]243[.]6[.]5
1
80[.]151[.]186[.]5
1
192[.]36[.]143[.]130
1
185[.]255[.]55[.]20
1
130[.]60[.]204[.]10
1
92[.]246[.]24[.]228
1
20[.]36[.]253[.]92
1
152[.]199[.]4[.]33
1
35[.]244[.]181[.]201
1
34[.]107[.]221[.]82
1
5[.]39[.]81[.]111
1
204[.]2[.]134[.]164
1
193[.]182[.]111[.]12
1
46[.]17[.]46[.]226
1
13[.]107[.]246[.]13
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences europe[.]pool[.]ntp[.]org
15
eur06[.]com
11
cny06[.]com
2
usd04[.]com
2
north-america[.]pool[.]ntp[.]org
1
Files and or directories created Occurrences %ProgramData%\msodtyzm.exe
15
%ProgramData%\~
15
File Hashes 1903668f3f1d9d84b4a98b8f19c334a901e798c1e397ffd8ce5fefcc30dc3788
316c6c83259094143e0ac5dd0468e63fecdfd92a35323845f0128d493fb606a9
4aa327716f1698091b45061cea055c04a3cb9ab00b62b901caec4bf66dc0b3b0
57566f59882b0923821cc2df7039e25686e9b7359ad3a9ab22543532e0ccaa16
66619f03c099416b9965ad05f78c575bb07f6e2f42c8fbf811d1c8d05750e59a
66827edc7665b94304e9bd957db45299e0de78e699750160f229a284e371d21d
702ab736a3af37714ab7a587c58ae08af53c4e4e6d0c721622274edff15021a8
71206878d56965dc697e6be9043787c32de1f190d4c3b9f0d25af540dca1f606
886948c601381b6091bf5a62d94536f045682101f1d000330ff76b0981dbf595
8959e806580edfe4d5bd8fecf75542ca09636afcb07e7f7dc762c92e1fbe5b36
8a193d26681244b9076cd1852a8d94d8f8db925d28aeae621618e1b3e0932e7b
9ee4104daff790ac22ba53d54af822f900e37c8cdf2f8ccfe8347ada667bcb83
ae2261cf8620e125ea3f5ca178ed304858db9aba288d8db81c066ba3e9b6b470
d5ed9e42ec45ed31455433272ab28baa6392ffbca83d787b272aae011ef5db13
d999dc87b0d9c537f3182f9ec8b1b2e781f1690f08ab69be141404f9ee9b1ce3Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
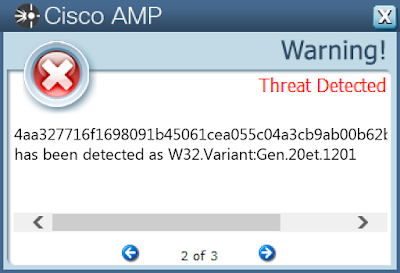
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Dropper.Emotet-9800496-0 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\MCTRES
Value Name: DisplayName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MCTRES
Value Name: WOW64
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MCTRES
Value Name: ObjectName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SXSSTORE
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: Type
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: Start
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: ErrorControl
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: DisplayName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: WOW64
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: ObjectName
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\COMPSTUI
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\NDPROXYSTUB
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MCTRES
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SETX
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SYNCINFRASTRUCTUREPS
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSV1_0
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MOBSYNC
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SETX
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSDART
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\CABINET
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MCTRES
Value Name: Description
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\COMPSTUI
Value Name: ImagePath
1
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\NDPROXYSTUB
Value Name: Description
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 46[.]105[.]131[.]87
15
87[.]106[.]139[.]101
15
50[.]116[.]86[.]205
15
178[.]20[.]74[.]212
15
58[.]171[.]38[.]26
15
110[.]145[.]77[.]103
15
169[.]239[.]182[.]217
15
41[.]203[.]62[.]170
15
153[.]126[.]210[.]205
15
142[.]105[.]151[.]124
14
93[.]51[.]50[.]171
5
Files and or directories created Occurrences %SystemRoot%\SysWOW64\NAPCRYPT
1
%SystemRoot%\SysWOW64\mfc100cht
1
%SystemRoot%\SysWOW64\uniplat
1
%SystemRoot%\SysWOW64\lz32
1
%SystemRoot%\SysWOW64\MSAC3ENC
1
%SystemRoot%\SysWOW64\d3d11
1
%SystemRoot%\SysWOW64\fdSSDP
1
%SystemRoot%\SysWOW64\LocationApi
1
%SystemRoot%\SysWOW64\netid
1
%SystemRoot%\SysWOW64\filemgmt
1
%SystemRoot%\SysWOW64\inetcomm
1
%SystemRoot%\SysWOW64\extrac32
1
%SystemRoot%\SysWOW64\api-ms-win-core-localization-l1-1-0
1
%SystemRoot%\SysWOW64\imagesp1
1
%SystemRoot%\SysWOW64\NlsLexicons0026
1
File Hashes 1ef6a2b97efef7c620cdb5d2e928ddf7d76ba3e2b2a8462654bfeb17ecbfc96c
301529f7fe85997628ad9c39bd016647d4e05deba178b0f0fe444e5c267090f7
3b5297a15d85364dfae055d572152e2d1ccde70dcd59aaf9d35487d99d4de242
546be3a16673f743aea1300b0d5699cf8f06efb5e15d0483827e04fb5f2e4d28
575cfb6da9c9bab3a659d4a624a19d42fe9a176750d6468c8f056daea2f044e5
58d9a58907eb0636706398b3862e251e807c698fa4bd43695f9e585441f7a6c7
5e45ce9469971c0f8c3998f03ad58b76cd85ee4fc06d7e04d928fb8fc01f0348
5f6ac0128dd0a4cee7cb554d5024635939ed7ade06ee199a178a1cd9f18d4584
78c73b757152c1579468c5b112795b0f20480a2598e3a7a9da088606b4437e96
a58d1c6c7e09c0b0b35b091fac8ac7f8446fc98ce367a40753522de667bb5143
a7072679b5c534be741f8bab3835cfd4235c15941c1557a9fcc0ee121f05bcca
b9519963dbf13e668de9e38d46f2a8233a9da22527695176d0c01da342c72350
ca8634fbe7c59c42dc8377d9601768971b62dc7ce7ee2c901bdec0ee04f146fe
cc305939189e309207fb46e48a9bae69ba9b97d5eebdb3aeee98ce8b166dab05
effbb0d1b4406f9a4d56612dfd027865a91873060d6afe19e88507ac365faf96Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
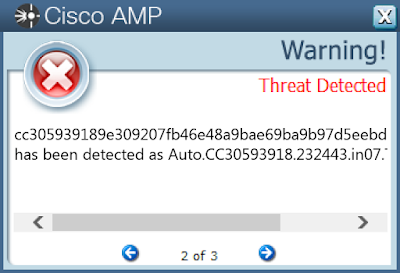
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Packed.Nymaim-9800769-1 Indicators of Compromise IOCs collected from dynamic analysis of 20 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\GOCFK
20
<HKCU>\SOFTWARE\MICROSOFT\GOCFK
Value Name: mbijg
20
Mutexes Occurrences Local\{0CCE1A6D-10E1-4330-6D33-59F9418C9024}
20
Local\{1181F583-B634-69BF-E703-D4756599024F}
20
Local\{180BBEAD-0447-044A-68BD-247EB6D0E352}
20
Local\{18DD7903-1E96-FEAF-92BF-014008A1248C}
20
Local\{65E26329-DE88-D536-CB3A-203091D3DF68}
20
Local\{92502033-C012-7F46-D6A8-0AC972DF6662}
20
Local\{25754F3F-7A37-56CA-31BB-3C9D33DA226B}
20
Local\{8B75523D-CAF4-D06B-A2AD-13EEF593AC52}
20
Local\{D2CC4CCA-CB77-CF10-8293-17C78DEC853F}
20
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 8[.]253[.]132[.]120
1
8[.]253[.]131[.]120
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences avrorcxzym[.]com
19
crhecbeaw[.]com
19
fytvfeseoxi[.]com
19
gktrgoolwdhh[.]net
19
gqpazmml[.]pw
19
jmzkplg[.]in
19
josdjhjzv[.]net
19
nhjtwfy[.]pw
19
nioxrmocwnar[.]com
19
pbjqn[.]com
19
rbxbkz[.]pw
19
rnbwbb[.]pw
19
rxxbrghmrnts[.]in
19
wvrpfnjpcxee[.]in
19
zpriveljzsge[.]com
19
dljaw[.]com
1
ebanqeg[.]com
1
erewkzl[.]net
1
fllbvddhachj[.]pw
1
ggybj[.]in
1
hdkearo[.]com
1
jbwyh[.]com
1
juqnnxinzqn[.]in
1
kzkhxc[.]in
1
njwkcve[.]net
1
*See JSON for more IOCs
Files and or directories created Occurrences %ProgramData%\ph
20
%ProgramData%\ph\fktiipx.ftf
20
%TEMP%\gocf.ksv
20
%ProgramData%\jzk\icolry.ylg
20
%TEMP%\qnvgtx.eww
20
%ProgramData%\<random, matching '[a-z0-9]{3,7}'>
20
%APPDATA%\<random, matching '[a-z0-9]{3,7}'>
20
%LOCALAPPDATA%\<random, matching '[a-z0-9]{3,7}'>
20
File Hashes 01bd3ce3ee770397df390ff566cd7e5fd0b4e61d36cc67abe1023f5a6ee98fd1
06df437bcebdd97f0f29e184980a0e9589e5190a099c6194df56c9d150ec41de
1ca064cd043f3d02315bacfa884a8b35c70034606f9d5f8a321522a38099e11a
205cf2569d58bc3b8d458242009a5a287d3e36b9dd1d93a735b2cc341346f93b
2cc606171b271d42e7feb5a486d1039e66074abf630b4b44903bb24da9b056d7
581433592a45ad8341b70c4a3e63a3f74dfc74cfd8836188acb35c2e559a9a9f
62d42edc6e74c6e39ffe233562bb624ea1f960f2a72e385f751e7f37961b0f54
634b468ba7756c56a08c3bc5a745aad968e50e0e0b58bc15ddc655bad71e853f
65aaabd043d30f67209b3b3e5db858e3ae0122e4d8802fa41b74b7bb1a638bf3
6ed3bec0e26719061853bb59bce715ff968bf04e88bb169ed0e035205336e344
7762067d6dcf85c239100982971ca1841f8248f05d72f55e2ad7801d19cb2ffc
92d5d9bec2fcdde14cf57b0b50ce736d46937482d63e74a3f61807187956f7bb
955cc0ab3749fda06cf71e2e1c8ee5ecc888cb92141f0896efeea59a33427719
9e2a194442ed2cd6d0513ae7863cd3eae2e6d2ad242e69ba98b4928afbfbd236
a33d51c1849c2738ca36073df69a6322f5d8db99d100339a2e4287eb41a9ccb4
a47a1d69455168e80aa5a467cfbaf08505f331521b1477315af334b9f7a13ca7
a62481e7259fa0bdd72210b8e3887cf2f194b87b4750f52f0e60ebd66a995ee6
bf5e2c1dbaad425b603fb6e9dd00727a71d026ef92b16caa3a294e1b7151238a
dc7749e6d1fc95d7d9f8ea94efd6531e0c1a5a90ed60df2bbb260ad0f44f4d6d
e12749d1cac502ef03581642a99c3e109e71e9ca7d8271a16405fd29737be0b7Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
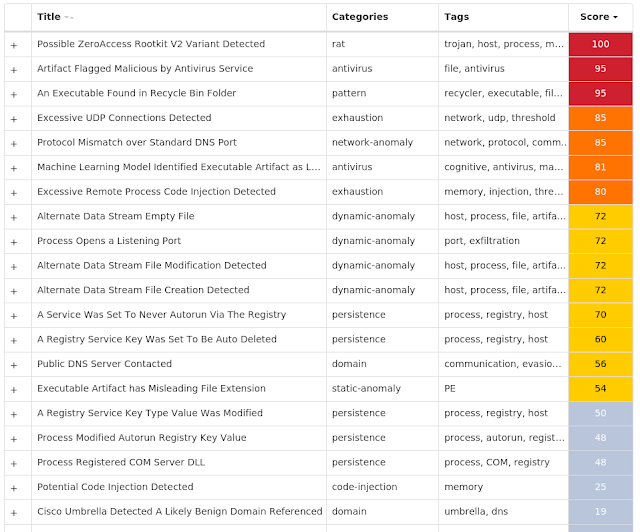
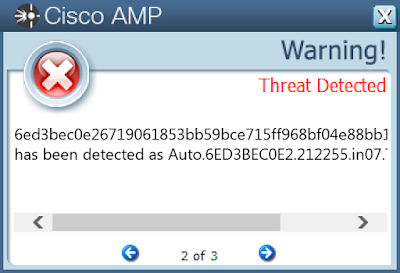
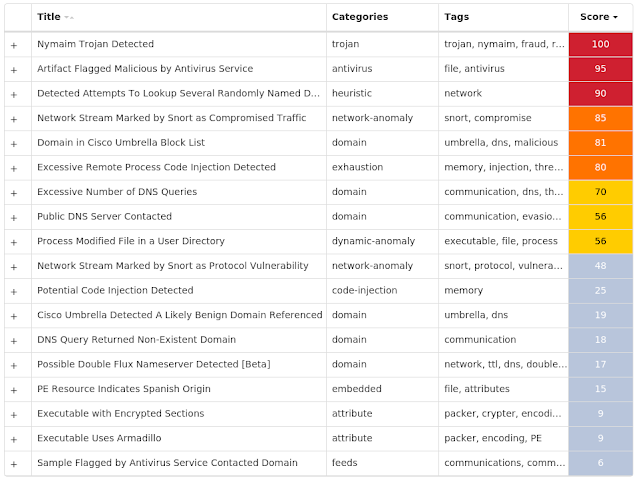
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Dropper.Tofsee-9800794-0 Indicators of Compromise IOCs collected from dynamic analysis of 79 samples Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Start
72
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Type
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ErrorControl
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: DisplayName
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: WOW64
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ObjectName
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Description
70
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
70
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config2
70
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ImagePath
46
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\dwkqpxds
6
<HKCU>\Software\Microsoft\<random, matching '[A-Z][a-z]{3,11}'>
6
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\qjxdckqf
5
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\unbhgouj
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\exlrqyet
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\jcqwvdjy
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\piwcbjpe
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\buionvbq
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\vocihpvk
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\mftzygmb
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\zsgmltzo
3
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\lesyxfla
3
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\slzfemsh
3
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\yrflksyn
3
Mutexes Occurrences Frz_State
6
Sandboxie_SingleInstanceMutex_Control
6
071A6ACE949624B9697446FFCCE6F0F1
6
6166662618921DF92B97CE8795B490AA
6
B0CEAFE74F56E112072FA8DE0DF2DDDC
6
<32 random hex characters>
6
{7930D12C-1D38-EB63-89CF-4C8161B79ED4}
2
tiqjngkbukjgtggd
2
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 239[.]255[.]255[.]250
70
69[.]55[.]5[.]249
70
43[.]231[.]4[.]6/31
70
85[.]114[.]134[.]88
70
217[.]172[.]179[.]54
70
5[.]9[.]72[.]48
70
130[.]0[.]232[.]208
70
144[.]76[.]108[.]82
70
185[.]253[.]217[.]20
70
45[.]90[.]34[.]87
70
172[.]217[.]10[.]132
69
157[.]240[.]18[.]174
67
104[.]47[.]54[.]36
46
23[.]5[.]238[.]97
39
69[.]31[.]136[.]5
35
216[.]239[.]32[.]21
34
157[.]240[.]20[.]63
32
157[.]240[.]20[.]174
30
87[.]250[.]250[.]22
26
85[.]25[.]185[.]229
26
216[.]239[.]38[.]21
24
104[.]47[.]53[.]36
24
160[.]72[.]43[.]232/31
23
163[.]172[.]32[.]74
21
172[.]217[.]10[.]227
20
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences schema[.]org
70
microsoft-com[.]mail[.]protection[.]outlook[.]com
70
249[.]5[.]55[.]69[.]bl[.]spamcop[.]net
70
249[.]5[.]55[.]69[.]cbl[.]abuseat[.]org
70
249[.]5[.]55[.]69[.]dnsbl[.]sorbs[.]net
70
249[.]5[.]55[.]69[.]in-addr[.]arpa
70
249[.]5[.]55[.]69[.]sbl-xbl[.]spamhaus[.]org
70
249[.]5[.]55[.]69[.]zen[.]spamhaus[.]org
70
www[.]tiktok[.]com
44
native-vita[.]np[.]ac[.]playstation[.]net
39
api[.]sendspace[.]com
35
market[.]yandex[.]ru
26
ip[.]pr-cy[.]hacklix[.]com
21
video-weaver[.]waw01[.]hls[.]ttvnw[.]net
20
www[.]google[.]co[.]uk
19
hotmail-com[.]olc[.]protection[.]outlook[.]com
19
accounts[.]ea[.]com
17
signin[.]ea[.]com
17
mta5[.]am0[.]yahoodns[.]net
17
mta6[.]am0[.]yahoodns[.]net
16
115[.]151[.]167[.]12[.]in-addr[.]arpa
16
ip02[.]gntl[.]co[.]uk
16
msr[.]pool[.]gntl[.]co[.]uk
16
work[.]a-poster[.]info
15
mta7[.]am0[.]yahoodns[.]net
15
*See JSON for more IOCs
Files and or directories created Occurrences %SystemRoot%\SysWOW64\config\systemprofile
70
%SystemRoot%\SysWOW64\config\systemprofile:.repos
70
%SystemRoot%\SysWOW64\<random, matching '[a-z]{8}'>
70
%TEMP%\<random, matching '[a-z]{8}'>.exe
70
%System32%\<random, matching '[a-z]{8}\[a-z]{6,8}'>.exe (copy)
47
\Documents and Settings\LocalService:.repos
30
\Device\ConDrv
16
%System32%\config\systemprofile:.repos
16
%TEMP%\<random, matching '[a-z]{4,9}'>.exe
9
%APPDATA%\Mozilla\Firefox\Profiles\<profile ID>.default\prefs.js
5
%LOCALAPPDATA%\bolpidti
2
%LOCALAPPDATA%\bolpidti\judcsgdy.exe
2
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\judcsgdy.exe
2
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\RGIE4AB.exe
2
%TEMP%\upd50c4494d.bat
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\RGIE4AB.zit
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\proofing-en-us_MSPLOG.exe
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\uxeventlog.iqp
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\~DF1B7CEAACC0AD00E7.rao
1
%TEMP%\upd990c4293.bat
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\RDFBE4.ake
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\firstrun.exe
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\proof-lt-lt.ona
1
%LOCALAPPDATA%\Adobe\Acrobat\9.0\Cache\proof-te-in.uxu
1
%TEMP%\updc86f8d77.bat
1
*See JSON for more IOCs
File Hashes 01647ee4a8e721c131100a94fd3c069d00621b8aefd67d3fdaaaeb3e8f0e6ce1
035796e758b1256f6c37ad0e2ece9ebc812a5fcafc6fca0f60a0d5f65bb20c1d
07f9119c40aa6836350a8f297bd1b9936598bdf1d23ed43a58f78bb082286e1d
086b7dc49c88d54e0895e4dc82ba7fadf1af2bea6dcc1964b2f347ae15b6213a
08978cfa4113fe9262190b3f857ea9eb0f9fcd7e410c61f7c02d3564d52c86b2
0a5e0ed9eb04577f7485d69804362046ddcf809fe0c6544e71f7d85f97cc8b69
0bae47b829cabfddeb204290b8386c971cbf9d9000d3eb9bb1b56227000b655a
0d839a6577d8a3619d22a0cd2b44798f1306f676de108ece2c82f701bf785f71
14919491cd4d8d29d777177c7b4f7af301fb5d9688e9bb8f9dc945d415caab1e
17f2b5420d59304ccb4febbe1ac1fb14eba31243f62c884305b6c50feb36199d
18379944d8d01fc8b732296453a7ed7f50ce8cf7c04be6d88767ccdd486fe87b
1b25f7a819829ffa241ca1399a75c7e489297e1bbb7cc0f4fc74f22075c9f879
1c8129bc114462c611a529cd73eeb6986a374fd407b1d98aa8748d169e703b58
1cf6145d0f9269122c7d00269fa889e03be2259a184fd60f6feba550ab8ae499
207aea8ee73bbe3fac17a177f25a82faa8ea94e6e40ac9c4a5a92db10daa99e2
235ac45639a88c378655372d62df0ee996a14f18962a3912634aca60f5e7202c
26e8cc645804caa970ea159aa9dae0d86783bf5eb4d2197616ac67cc254f8f22
28aafc4ad322a36d00ab3526542137759cd0254ebeb5fdbaae236273e9af6725
31aa06097b0be75f6e539c36ccb103c9a4e39a1897ba7809f54673a522a7e0a9
344457d11ca5807dd035c4cbcc5ff200c99a500a1e4506b057e338884df9288a
34c09d333b85e650520c34052ad3e93cafe3ec8728c2658bf1eacc8c0daf2da4
38043bce36379d6695b0835e291e9a80c0b27916f2eae4acfe2f9672c1da0b9c
3884ac38d38ecd5f6f72b8874aad88279771fa02935f78af08a27f2a62d737ee
3a8039d7347aa39e78e2f2930dbdd83de7143c49fa2c27b1c67cc0c252d8d6f4
411ce6221c8cd447e7217c75c8b0b688c20fd804b63ae7bbdf46c07ecdd1b937*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
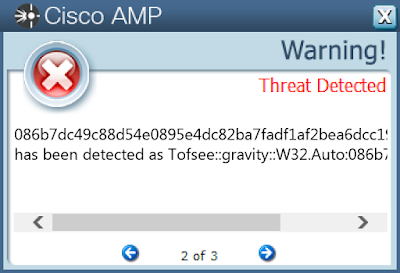
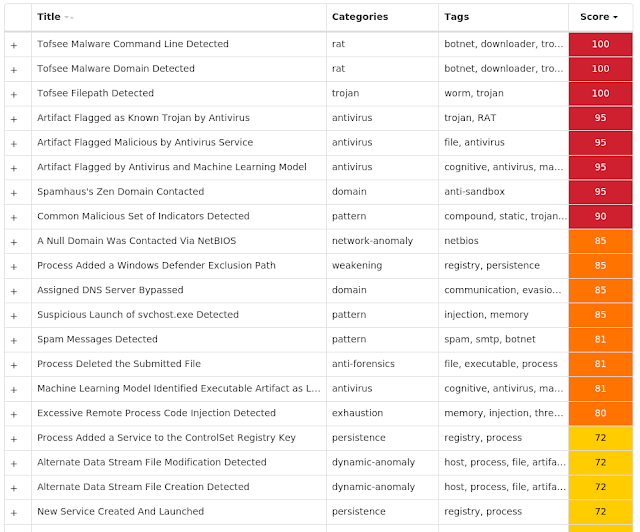
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Trojan.Barys-9800808-0 Indicators of Compromise IOCs collected from dynamic analysis of 13 samples Registry Keys Occurrences <HKCU>\SOFTWARE\LOCAL APPWIZARD-GENERATED APPLICATIONS
10
<HKCU>\SOFTWARE\LOCAL APPWIZARD-GENERATED APPLICATIONS\
10
<HKCU>\SOFTWARE\LOCAL APPWIZARD-GENERATED APPLICATIONS\ \RECENT FILE LIST
10
<HKCU>\SOFTWARE\LOCAL APPWIZARD-GENERATED APPLICATIONS\ \SETTINGS
10
<HKCU>\SOFTWARE\
2
<HKCU>\SOFTWARE\ \RECENT FILE LIST
2
<HKCU>\SOFTWARE\ \SETTINGS
2
Mutexes Occurrences K^DJA^#FE
10
SDK&#AD
1
DJ^#JASF
1
%^123nv22
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 58[.]158[.]177[.]102
1
221[.]130[.]179[.]36
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences tw[.]2012yearleft[.]com
1
meibubaker[.]3322[.]org
1
Files and or directories created Occurrences %SystemRoot%\System32:mssendfull.exe
5
%SystemRoot%\system32:mstankers.exe
1
%SystemRoot%\System32:msFartiTs.exe
1
File Hashes 21b717aec3c02bc57adb465aae610e9a7fe1b889321b373c2808187eade50397
243cf03be11f0dd442a8d5e3ad16b07c36425af539a4d136fd73cbcbc0bcb25f
46672b5570794513e4df7bb9b5f7dd08469f15ee0875cb48319350aab3d1c410
57e1837a161e003140706f792ca3ab54232581aae26d548f14b94db076ff2e08
61289f2bc4a3b72465ac711178831abd65ed9c0ee83ce1a1d1e20b67d3912b71
65caad9e8a736986f8995f5621ce3eec52738f2e6e083290c0eeaef39eda87d2
67a5c87246cfd48919719147a23f5fc9d673eda0f0a860612bfa8a94d692a061
70ffe23105998277230ab194779633cc8f7ed092532f9e40fe519e1e72156678
801a6dcac621cf2733a742cd36158a1393eff4e9f2d65ea151385d80c10d71c9
80df035a361780c2a8b567d08a0cd161015ba37b1b4479085886e379b5ab54ac
a404215539b7bc308e112222493ba4d59a41adeb5204e59ad14cd7836dd6a545
a98b443dab1373415ceefacf3be09bb209377827785a02e5f7d4a20c3badc01c
c88f7682caa26ce756341a27d45f3c6507641249b3b26e2381decf768930e43fCoverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Exploit Prevention Cisco AMP for Endpoints protects users from a variety of malware functions with exploit prevention. Exploit prevention helps users defend endpoints from memory attacks commonly used by obfuscated malware and exploits. These exploits use certain features to bypass typical anti-virus software, but were blocked by AMP thanks to its advanced scanning capabilities, even protecting against zero-day vulnerabilities.
Process hollowing detected - (3514)
Process hollowing is a technique used by some programs to avoid static analysis. In typical usage, a process is started and its obfuscated or encrypted contents are unpacked into memory. The parent then manually sets up the first stages of launching a child process, but before launching it, the memory is cleared and filled in with the memory from the parent instead.
Smoke Loader detected - (2119)
Smoke Loader has been detected. Smokeloader is used mainly to execute other malicious software, like ransomware or cryptocurrency miners. Its initial infection vector is usually an email with a malicious Microsoft Word document or delivered through an exploit kit. Smokeloader uses various plugins designed to steal data from its victims, particularly credentials stored on the system or transfered over HTTP, HTTPS, FTP, SMTP, POP3 or IMAP.
Dealply adware detected - (1790)
DealPly is adware, which claims to improve your online shopping experience. It is often bundled into other legitimate installers and is difficult to uninstall. It creates pop-up advertisements and injects advertisements on webpages. Adware has also been known to download and install malware.
CVE-2019-0708 detected - (1585)
An attempt to exploit CVE-2019-0708 has been detected. The vulnerability, dubbed BlueKeep, is a heap memory corruption which can be triggered by sending a specially crafted Remote Desktop Protocol (RDP) request. Since this vulnerability can be triggered without authentication and allows remote code execution, it can be used by worms to spread automatically without human interaction.
Crystalbit-Apple DLL double hijack detected - (1514)
Crystalbit-Apple DLL double hijack was detected. During this attack, the adversary abuses two legitimate vendor applications, such as CrystalBit and Apple, as part of a dll double hijack attack chain that starts with a fraudulent software bundle and eventually leads to a persistent miner and in some cases spyware deployment.
Excessively long PowerShell command detected - (576)
A PowerShell command with a very long command line argument that may indicate an obfuscated script has been detected. PowerShell is an extensible Windows scripting language present on all versions of Windows. Malware authors use PowerShell in an attempt to evade security software or other monitoring that is not tuned to detect PowerShell based threats.
Squiblydoo application whitelist bypass attempt detected. - (376)
An attempt to bypass application whitelisting via the "Squiblydoo" technique has been detected. This typically involves using regsvr32.exe to execute script content hosted on an attacker controlled server.
Certutil.exe is downloading a file - (372)
The certutil.exe utility has been detected downloading and executing a file. Upon execution, the downloaded file behaved suspiciously. The normal usage of certutil.exe involves retrieving certificate information. Attackers can use this utility to download additional malicious payloads.
Maze ransomware detected - (368)
Maze ransomware has been detected injecting into rundll32.exe or regsvr32.exe. Maze can encrypt files on the victim and demand a ransom. It can also exfiltrate data back to the attacker prior to encryption.
Installcore adware detected - (251)
Install core is an installer which bundles legitimate applications with offers for additional third-party applications that may be unwanted. The unwanted applications are often adware that display advertising in the form of popups or by injecting into browsers and adding or altering advertisements on webpages. Adware is known to sometimes download and install malware.