Today, Talos is publishing a glimpse into the most prevalent threats we've observed between Sept. 24 and Oct. 1. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org , or ClamAV.net .
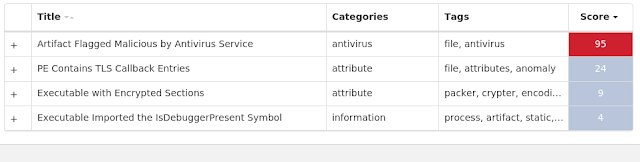
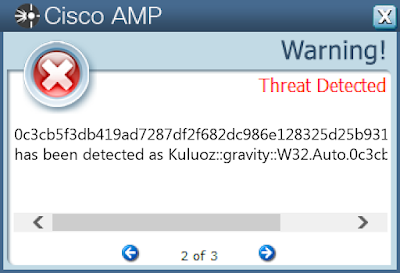
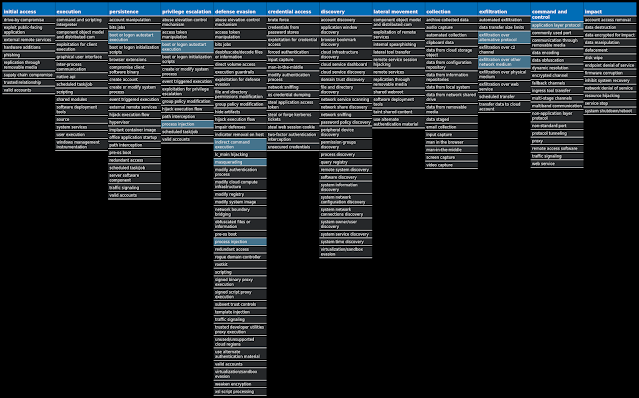
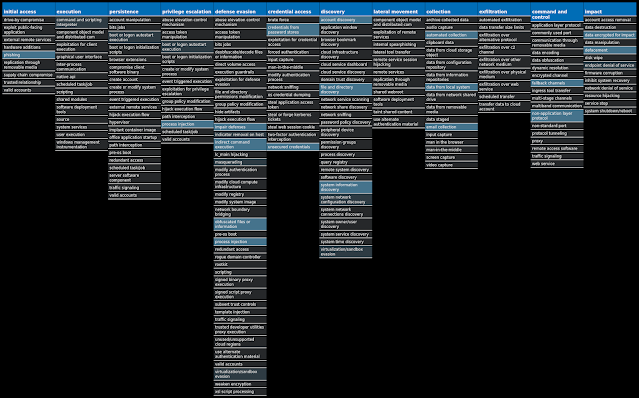
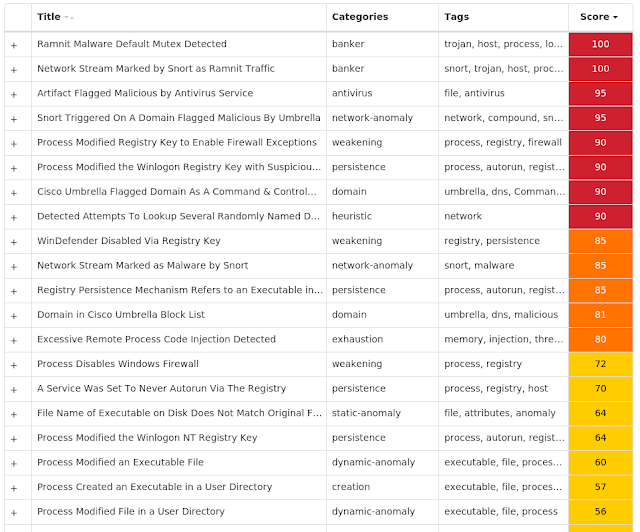
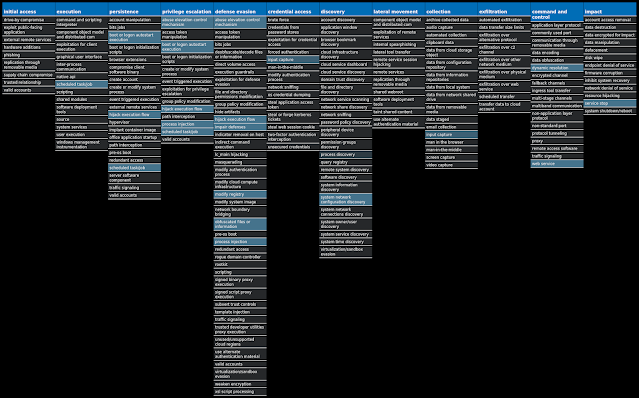
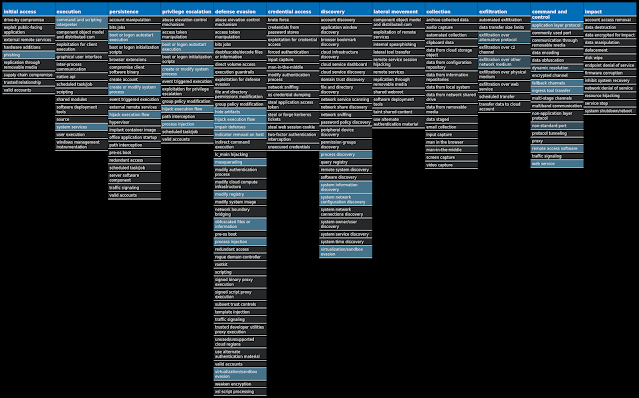
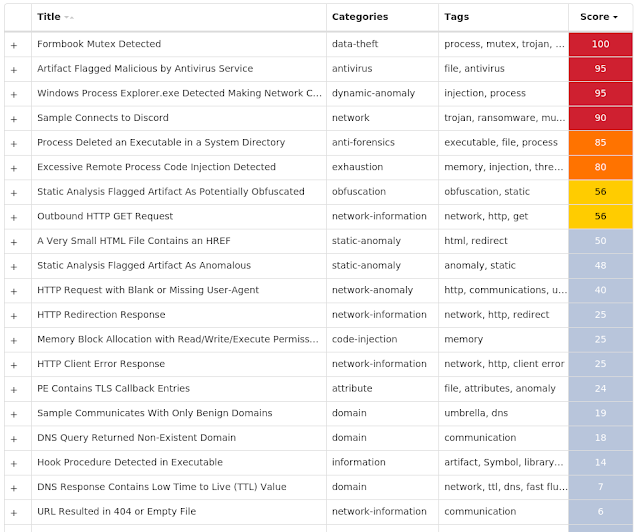
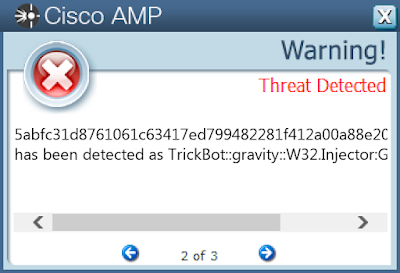
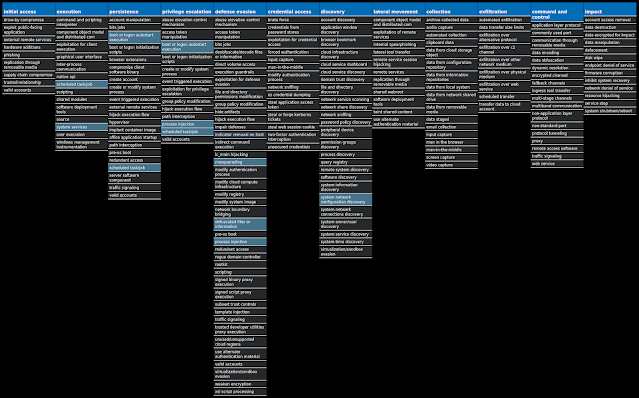
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found here that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name Type Description Win.Malware.Razy-9896045-0
Malware
Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypt the data, and send it to a command and control (C2) server. Information collected might include screenshots. The samples modify auto-execute functionality by setting and creating a value in the registry for persistence.
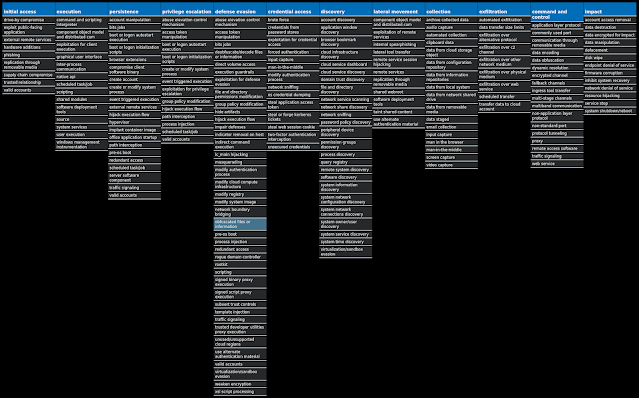
Win.Dropper.Kuluoz-9896046-0
Dropper
Kuluoz, sometimes known as "Asprox," is a modular remote access trojan that is also known to download and execute follow-on malware, such as fake antivirus software. Kuluoz is often delivered via spam emails pretending to be shipment delivery notifications or flight booking confirmations.
Win.Ransomware.Cerber-9896367-0
Ransomware
Cerber is ransomware that encrypts documents, photos, databases and other important files. Historically, this malware would replace files with encrypted versions and add the file extension ".cerber," although in more recent campaigns other file extensions are used.
Win.Virus.Ramnit-9897435-0
Virus
Ramnit is a banking trojan that monitors web browser activity on an infected machine and collects login information from financial websites. It also has the ability to steal browser cookies and attempts to hide from popular antivirus software.
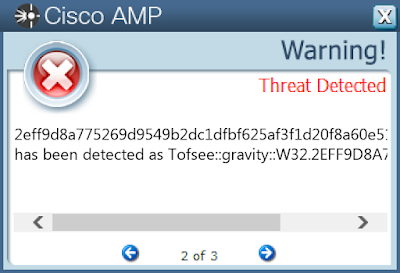
Win.Packed.Tofsee-9896988-1
Packed
Tofsee is multi-purpose malware that features a number of modules used to carry out various activities such as sending spam messages, conducting click fraud, mining cryptocurrency, and more. Infected systems become part of the Tofsee spam botnet and are used to send large volumes of spam messages in an effort to infect additional systems and increase the overall size of the botnet under the operator's control.
Win.Exploit.Remcos-9896449-0
Exploit
Remcos is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes, interact with a webcam, and capture screenshots. This malware is commonly delivered through Microsoft Office documents with macros, sent as attachments on malicious emails.
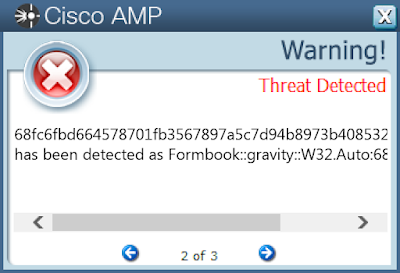
Win.Dropper.Formbook-9897307-0
Dropper
Formbook is an information stealer that attempts to collect sensitive information from an infected machine by logging keystrokes, stealing saved web browser credentials, and monitoring information copied to the clipboard.
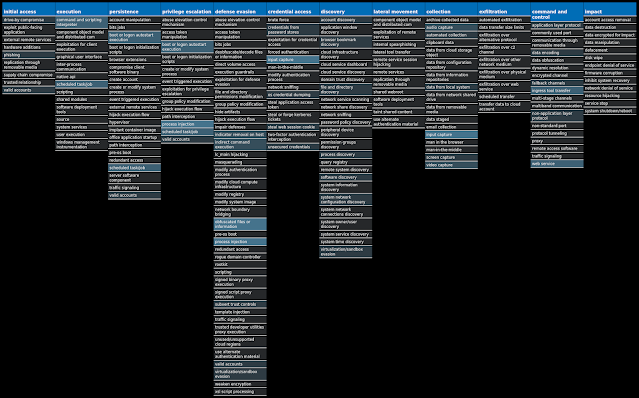
Win.Dropper.TrickBot-9897455-0
Dropper
TrickBot is a banking trojan targeting sensitive information for certain financial institutions. This malware is frequently distributed through malicious spam campaigns. Many of these campaigns rely on downloaders for distribution, such as VB scripts.
Win.Dropper.Gh0stRAT-9896856-0
Dropper
Gh0stRAT is a well-known family of remote access trojans designed to provide an attacker with complete control over an infected system. Capabilities include monitoring keystrokes, collecting video footage from the webcam, and uploading/executing follow-on malware. The source code for Gh0stRAT has been publicly available on the Internet for years, significantly lowering the barrier for actors to modify and reuse the code in new attacks.
Threat Breakdown Win.Malware.Razy-9896045-0 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
15
Files and or directories created Occurrences %SystemRoot%\SERVIC~2\Local Settings\AppData\Local\Temp\MpCmdRun.log
15
File Hashes 417c1828d98ba4f05f7a2edb71a9105f0aebf3d554393970b96e59d4db7b4473
52614db3f7ecc04bc6ba0d98d6a24b7291dc7ac61f749fa94f8861e437c6f672
58af67d6f6caacbf9bb2f31a54a344c38e182b8d610a1f52718ca9014d33abcf
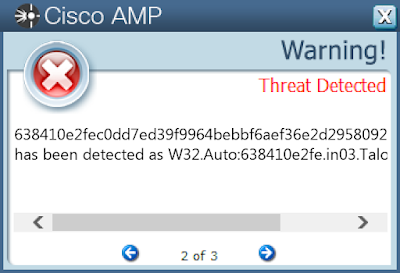
638410e2fec0dd7ed39f9964bebbf6aef36e2d2958092fc1beee464948854cf7
66329edeeebb899f807b43760da1759782a2c6dc9d6f6b6a6b8612e6b4c484c2
73b0a978d94f1513bd5210a3783a5263d52799d2c92f5592f1b8c35039f7a91c
929753f4b2a6c0e6efaf00eda436cba21ee3040217a01db6ff53646824a04a86
932f5d359ec264342d3dc6ad011f5dfa01669084df7bfbd4a4c247c671cbdb69
9645dc385a8decbcc1b50987a42c0d6cec18059bcf7263707e4d1bd5d374e095
a2a5f793a385216b883581d018ecfe267a4afda0eff89917a39cf9d165686574
bb2b275008b1533550bf4626fa5b22357b6264d930ad252863d742001e548746
c26827f37218490b206215d65019cfa71646bf7a99eb2cc2f1b870d0d79d09d1
c5d2f0da18fb33a25b53fd8b9b98f0bfa95458e3c0feb687852f469167a0110c
d894f2f8d02e9cadd6ce7a478043cf093796aae5b57e93e3cf607496f207d635
fe672dce6beee57745d8240bcea11412bd68749b84620d2508e8ed83d3f97e28Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
Screenshots of Detection AMP
ThreatGrid
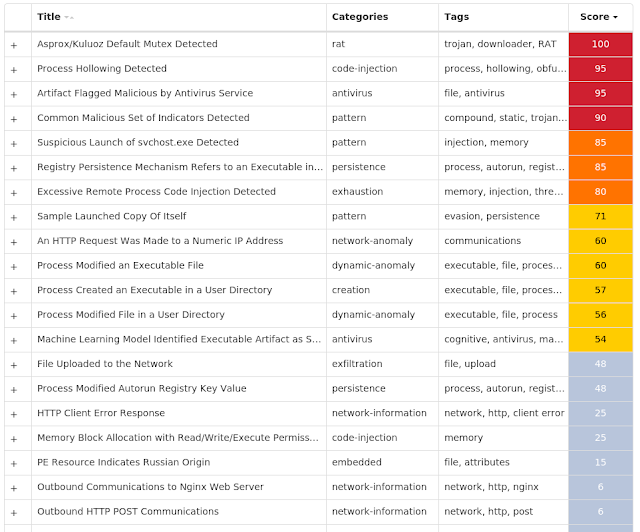
MITRE ATT&CK Win.Dropper.Kuluoz-9896046-0 Indicators of Compromise IOCs collected from dynamic analysis of 298 samples Registry Keys Occurrences <HKCU>\SOFTWARE\<random, matching '[a-zA-Z0-9]{5,9}'>
298
<HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
297
<HKCU>\SOFTWARE\PUTGGCPU
Value Name: kmpbnwik
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: qgavgrqi
1
<HKCU>\SOFTWARE\XQKMJPIM
Value Name: qgbjxjgh
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: qfrjmmws
1
<HKCU>\SOFTWARE\WJIXKQMH
Value Name: ubvsnlbc
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: gxkblwto
1
<HKCU>\SOFTWARE\WNAOIJPV
Value Name: tqefesdo
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: dudaknvw
1
<HKCU>\SOFTWARE\RIHWERER
Value Name: aikjhten
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: snesokri
1
<HKCU>\SOFTWARE\GKGQHTBG
Value Name: lxfiouuu
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: dgvxfjga
1
<HKCU>\SOFTWARE\BNOMGOXS
Value Name: boxeinlo
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: moefnqxt
1
<HKCU>\SOFTWARE\SKLPUMKG
Value Name: gpgebcob
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: dwrgsfnk
1
<HKCU>\SOFTWARE\WPONRPNC
Value Name: gewvvbku
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: bwwpcwjb
1
<HKCU>\SOFTWARE\WNOISUUX
Value Name: cpeejapi
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: tgbqlhgo
1
<HKCU>\SOFTWARE\OVAWEQGR
Value Name: pgvjqtav
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: qmlfbkle
1
<HKCU>\SOFTWARE\IWXBGAGS
Value Name: lujoaidd
1
Mutexes Occurrences aaAdministrator
298
abAdministrator
298
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 115[.]29[.]6[.]237
235
195[.]96[.]246[.]93
217
129[.]121[.]182[.]100
216
91[.]121[.]208[.]114
209
103[.]245[.]153[.]143
209
198[.]8[.]62[.]166
197
173[.]230[.]130[.]14
193
13[.]32[.]208[.]34
1
Files and or directories created Occurrences %LOCALAPPDATA%\<random, matching '[a-z]{8}'>.exe
298
%HOMEPATH%\Local Settings\Application Data\phogcurw.exe
1
%HOMEPATH%\Local Settings\Application Data\hsbviuss.exe
1
%HOMEPATH%\Local Settings\Application Data\kqtoladj.exe
1
File Hashes 002ceb27623eead01506aea2d2463a338cc8963130fec0894372e47306ef73fb
018b0d02684823c7b609167b69701db5167096884e76e297cd281e93ccf90ad2
01a12a952f90138931d2810372c1b2d70491337f694ee3509b8473848fa2f47f
026342d232fbed976bc7145de4f20c0977c8a659e705eaa3125eb212e986a764
0396ce72acaaa900aed666f92a2088b53fe07f4c2631ab55f04b329cf03ee884
04c2c686e687f04c6d1e6bce5d37e57ce3486d60f6b6e209e4e10fdcbc54dc90
050dbb29f6d16203849a1951355887ddbec3ec54871426b797c04f8b15c5620f
0519bf52d718cc193056077c29aab92f65e31aff13e16047453997f7036a414f
05fb0199c2da2844a1c8a557f36811b8cf38b43efc359c2a3ca246aa2fabcdd4
06274203bf1fbef2440acddf3cfbaa00b6942f4d78e13a8ba140b941c43a0ee1
0852d0010acbd0c5abfb4081513ee79858d8f71a603a98699780e77cab953608
08f86c4a9ae551cba0fe5b5ebadc3a3fb259088000dcdecaa2ea5f33a92d7302
0a76b891a8cf1329da73dcb26b7fbb4340157b7a8de4cca4e20b14f48a0e6ee4
0b7abb4fe3d30919422534465f76b2a91a10cf8d8ba472cf800388972065514f
0c3cb5f3db419ad7287df2f682dc986e128325d25b931a1fd8c708cc264b7df1
0d079ee7f1d664a5b703c9adc46e289b5e649858cb066d551656a9f5637b10df
0d1dc9a7508e7b82a746ae6b38bb568b7cb2c0894356d8b31432e22544c6a175
0d9ddf3426fc8a34fb587b128aa8e490d2212926e589d8c57e47060c5b08cccb
0f5e931d2908f1beb20ef5bb5752c76a917364e54bbe440d97bc5e77831da516
0fbe65c4431b2553049695cd9c1e42d1dcb5bfc3ed00df15e86bd030a167dd75
1028b5912e63f32ef9894fccb69f808e70f6a7635177e11231c18e685f2cfc5c
12842bcb5a12043e0dfafcac5fdade0aa9c4c5e80f468a4796738acbc8e7f7b9
1450a7a54499fd9afb462a2274b6c16b7270c6f733b1872f9bb39cb0fb9bb02f
156467a3c87a1f6d0b66a148d47d56e2342b3de2460f009fe86369949b390752
15885d379de711290161bb77c848314cea22441fefcc5921a98c4291d85fa1a8*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Ransomware.Cerber-9896367-0 Indicators of Compromise IOCs collected from dynamic analysis of 52 samples Registry Keys Occurrences <HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
52
<HKCU>\Software\Microsoft\<random, matching '[A-Z][a-z]{3,11}'>
5
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: sessionstore.exe
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: profiles.exe
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: webapps.exe
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH\\APPLEXICONS
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH\\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH\\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}\FILES
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH
Value Name: CLSID
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH
Value Name: Generation
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: WXUN5IEN.exe
1
<HKCU>\SOFTWARE\MICROSOFT\CYIPCI
Value Name: Lutys
1
<HKCU>\SOFTWARE\MICROSOFT\FTP
Value Name: Iqez
1
<HKCU>\SOFTWARE\MICROSOFT\SPEECH\\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}\FILES
Value Name: Datafile
1
<HKCU>\SOFTWARE\MICROSOFT\FAX
Value Name: Umpityi
1
<HKCU>\SOFTWARE\MICROSOFT\LYSY
Value Name: Fianloy
1
Mutexes Occurrences shell.{381828AA-8B28-3374-1B67-35680555C5EF}
45
shell.{<random GUID>}
24
Frz_State
4
Sandboxie_SingleInstanceMutex_Control
4
MicrosoftVirtualPC7UserServiceMakeSureWe'reTheOnlyOneMutex
4
<32 random hex characters>
4
Global\4c90cd81-1d42-11ec-b5f8-00501e3ae7b6
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 87[.]96[.]148[.]0/27
46
87[.]97[.]148[.]0/27
46
87[.]98[.]148[.]0/22
46
5[.]196[.]159[.]173
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences urasnev[.]top
4
Files and or directories created Occurrences %TEMP%\tmp<random, matching [A-F0-9]{1,4}>.bmp
46
<dir>\_HELP_HELP_HELP_<random, matching '[A-F0-9]{4,8}'>_.hta
46
<dir>\_HELP_HELP_HELP_<random, matching '[A-F0-9]{4,8}'>_.png
46
%TEMP%\d19ab989
45
%TEMP%\d19ab989\4710.tmp
45
%TEMP%\d19ab989\a35f.tmp
45
%LOCALAPPDATA%\Microsoft\Office\Groove1\System\CSMIPC.dat
45
%TEMP%\tmp<random, matching [A-F0-9]{1,4}>.tmp
45
%TEMP%\24e2b309\1719.tmp
24
%TEMP%\24e2b309\4436.tmp
24
%HOMEPATH%\documents\documents\resume.docm.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.docx.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.dot.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.dotm.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.dotx.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.pdf.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.rtf.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.x.odt.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.x.xml.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.xml.b195 (copy)
24
%HOMEPATH%\documents\documents\resume.xps.b195 (copy)
24
%HOMEPATH%\documents\presentations\presentation 1.odp.b195 (copy)
24
%HOMEPATH%\documents\presentations\presentation 1.potx.b195 (copy)
24
%HOMEPATH%\documents\presentations\presentation 1.ppsx.b195 (copy)
24
%HOMEPATH%\documents\presentations\presentation 1.ppt.b195 (copy)
24
*See JSON for more IOCs
File Hashes 01788eb2ba5b8069d0d911873f75cb3baf3d5caf97626e946b6ae8adf4b9d7af
0c4e731c72db5a5b1d7e11fbdc489def705ef7153217e0b92923b0a4d53c8c83
0d392649b431a30429b0969319613e6c3fa6bcf4578703e089e3e37fdd9349b8
22f48c2edd32135ba4b6a58e055ce5a74734820fed87832b642f4345af5a06ec
2c99423c1ab24243645196ac1ce310dba02c5fd4131e41823f90d502fbc5d90d
2ecd5154b514f08b35f39d2016a3414df58e9447e8ec64292a0693eacdb4cc35
300ab9a57d6acff7b1c29cb5afceb3b8419d562620b31e29539bc560243db3f8
3209e62e2c340f0276492671b3737ab244e3a53e756f80db049e3cd4d32e07c8
329a7c76210f2efdad84d9dc13ddadddc2328a868d1d2a42e7e8a6e9c44948b6
349b2fcf9ee62a9ee12b2af4f947b862fa036ffd08936e318fb6b4fb31456f98
35e6d0f641b1110254c892bf8b9f057ad57f4e4aeb6a8226741994a7025d3cb3
37c7844c8b2612087c805ccafee15112af5b83e333487c8a035b872eaa54c939
408975aa1bfa592381e142e2c684af508e36770e7db7888286b8e832f4c50539
430fb7445cc2122738f8fe96c5d0081e145795f5580a8c4a67b1c6d07372a7ec
508a9dc923581db21a8ea519b09fe953c9e95f277ea6cff5fad22eb5b35efa8a
5351b8867e09bbea11ed4b4c75167e0175d121d50982bafe7a11ca27f6c343b3
5911f624ba495ff83e15703b812e9aa2655c33cd6e0656ed10e7db44dc83570d
5a50f469f50289da4870b24ec122dea9eb59ece22052ef5c4a5ea940a33fc1cd
62aec8e564d2597b55f2c77389f458fc686f1558c57bcc2de8ce5080375d6bd2
64a1274e9fbd76ff9fb5708584c12d04f6246c1d56943949d77d800751605a47
662246097fd86b64775fb83b4e3ddd85e6e0fa7ec387b36a0b073a394b0b1bcb
66b3209cae9eb604861936bdde37c24fce8609ee93f1db1d02391d5f29a89bbe
67dcfb7d2a1627e72e96af8890c0a3018343cd6bba34e0934b46e2127f35b929
6b73cb1f66960b632f48a623c0dba5f1ef9505a4c26dcaf0a521a2feabb2a743
6f6f727a15695b3134bcd958a8acf9f98985acbd1f45d25850bd1b351a339f44*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
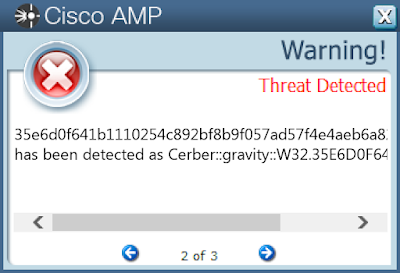
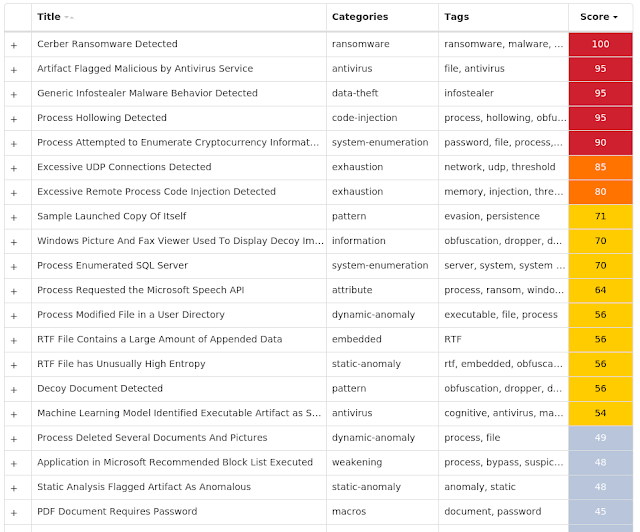
Screenshots of Detection AMP
ThreatGrid
Malware
MITRE ATT&CK Win.Virus.Ramnit-9897435-0 Indicators of Compromise IOCs collected from dynamic analysis of 25 samples Registry Keys Occurrences <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER
Value Name: AntiVirusOverride
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER
Value Name: AntiVirusDisableNotify
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER
Value Name: FirewallDisableNotify
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER
Value Name: FirewallOverride
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER
Value Name: UpdatesDisableNotify
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER
Value Name: UacDisableNotify
20
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\SYSTEM
Value Name: EnableLUA
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE
Value Name: EnableFirewall
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE
Value Name: DoNotAllowExceptions
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE
Value Name: DisableNotifications
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WSCSVC
Value Name: Start
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WINDEFEND
Value Name: Start
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\MPSSVC
Value Name: Start
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION
Value Name: jfghdug_ooetvtgk
20
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: JudCsgdy
20
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\WUAUSERV
Value Name: Start
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Windows Defender
20
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON
Value Name: Userinit
20
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON
Value Name: Userinit
20
<HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
5
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\TELEPHONY\HANDOFFPRIORITIES
Value Name: RequestMediaCall
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\TELEPHONY\HANDOFFPRIORITIES\MEDIAMODES
1
Mutexes Occurrences {79345B6A-421F-2958-EA08-07396ADB9E27}
25
{7930D12C-1D38-EB63-89CF-4C8161B79ED4}
20
Global\570c0a61-2042-11ec-b5f8-00501e3ae7b6
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 46[.]165[.]254[.]201
20
72[.]26[.]218[.]70
20
195[.]201[.]179[.]207
20
208[.]100[.]26[.]245
20
206[.]191[.]152[.]58
20
142[.]250[.]72[.]110
20
Domain Names contacted by malware. Does not indicate maliciousness Occurrences google[.]com
20
testetst[.]ru
20
mtsoexdphaqliva[.]com
20
uulwwmawqjujuuprpp[.]com
20
twuybywnrlqcf[.]com
20
wcqqjiixqutt[.]com
20
ubgjsqkad[.]com
20
iihsmkek[.]com
20
tlmmcvqvearpxq[.]com
20
flkheyxtcedehipox[.]com
20
edirhtuawurxlobk[.]com
20
tfjcwlxcjoviuvtr[.]com
20
Files and or directories created Occurrences %LOCALAPPDATA%\bolpidti
20
%LOCALAPPDATA%\bolpidti\judcsgdy.exe
20
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\judcsgdy.exe
20
\TEMP\zZwuFpyA
2
\TEMP\uwb4h23
2
%HOMEPATH%\Desktop\zZwuFpyA
2
%HOMEPATH%\Desktop\uwb4h23
2
\TEMP\ruTa4e3
1
%HOMEPATH%\Desktop\4iStXw6B
1
%HOMEPATH%\Desktop\v2PyeKNXo
1
%HOMEPATH%\Desktop\bnpOS23
1
\TEMP\bnpOS23
1
\TEMP\sIwHNkPC
1
\TEMP\koJBB23
1
\TEMP\S3sBQJC
1
\TEMP\gsk3yx52
1
\TEMP\bVo73f3
1
\TEMP\rGC0mo9
1
\TEMP\mc0SHzBNf
1
\TEMP\hSGxoMwC7
1
\TEMP\JWCOV23
1
\TEMP\JO9X3l07U
1
\TEMP\EOgRPZ3
1
\TEMP\7XnLOOevK
1
\TEMP\lFpszloEL
1
*See JSON for more IOCs
File Hashes 062169ecbc78865432f2629f0f51841208d4f9499882c07e095010a28469af40
1199597c3c7f46e67aa9e4fc7f63f3d5bfa9cd82e957c322a4d4172e5797cfa8
1661a3b85badf8db19bcdf927b94b607b64b37f50338946b49600308af55b5ec
182920c477c2d102f9f581349e19815c3e68bebf4b26a4fcfffdbf328292a5ab
1a951a2f39c524247aa059d606a99afbc3a1a3a1ac8c7efb07fd43c4731ca71c
1ad4b2416494554ada270452933776503394768767140d88d18ea44386203ced
1f7b6a681212c990591abbc428302d873c6f0d5ad506149a49280dbba8e9329f
2070d08afacabb3674db18d2fe07aa525e76b8e824f7b784f26fd75354428cb5
27d21e1b682d657cfce8b32fa201e360888e67a99aee86d0827ac51fd411bd9a
346ef2091571143477264744e3870d1d94d84fbc78021f5e9671f1ee394bdc90
378e360d4ccf0a1d139445edad168a2c6ee052a449f3c8d58e6c33e504ea3685
40f7ad5a05e9fdf91d528d03bdb62a6902bf59af48d6c19ceb84a47c44b0d54b
45e79c378ae5549c7432587a3b9d257c83d09dc27d77df8ae81ed17dc5f565bc
472ba96e3a4af993729a16f2226a0e321a5a7a3292ab0493af926080789dcc07
484f90cb973a6619b01020c43342bd760693c938caca1e7d5f1acc67bfd92d02
4d5a5d7fc2b3a700891ef6e0b7f5f5c56bf9fd42aa806fb9ce8a8b815ae4c8e7
54876cbe72546025fe747d68d347dcab4f665518e64dc8d20c2b1648e3aeeb84
563de4f4d711a39eb4e8d80b65fe0a3bbc7bf1580359148c1dd40e02044ad32a
57eff249c0da28826261504d72841b7a640d8127f26a77de5da1871c47129ad2
5c2c8731cc361375bc0547f703e4e3c0ed5a44b2bc26d81385cc80dc56965002
5da70dd7c9e2b7ffda21951ccbf5320be23988ecd1c3e04b546f107a047d0d73
5ef1ad9d962a280803987885d103f0dfb4008fa4b20b5bca1b0edd3553009ed6
642a568dd11f39646b836610c6892fa45027d76581260e3219bc25c905b13c4c
6b1b98bc8063de8a97769f2dcf9f7885569149353ca836442dcae5e0ca06793e
6ff884476fa41aebbc1a6ffee50ff4e94520e680260a185c3fe2c59f37a6041a*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Packed.Tofsee-9896988-1 Indicators of Compromise IOCs collected from dynamic analysis of 45 samples Registry Keys Occurrences <HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config4
44
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
44
<HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Type
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Start
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ErrorControl
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: DisplayName
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: WOW64
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ObjectName
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: Description
44
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config0
44
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config1
44
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config2
44
<HKU>\.DEFAULT\CONTROL PANEL\BUSES
Value Name: Config3
44
<HKLM>\SYSTEM\CONTROLSET001\SERVICES\<random, matching '[A-Z0-9]{8}'>
Value Name: ImagePath
22
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\oyavrjie
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\gqsnjbaw
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\cmojfxws
4
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\isupldcy
3
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\pzbwskjf
3
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\eoqlhzyu
2
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\wgidzrqm
2
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\fprmiazv
2
<HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS
Value Name: C:\Windows\SysWOW64\scezvnmi
2
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 193[.]56[.]146[.]42/31
45
192[.]0[.]47[.]59
44
74[.]208[.]5[.]20/31
44
193[.]56[.]146[.]188
44
193[.]56[.]146[.]41
44
77[.]222[.]55[.]43
44
92[.]38[.]129[.]26
44
185[.]49[.]68[.]143
44
96[.]114[.]157[.]80
43
144[.]160[.]235[.]143
43
64[.]136[.]44[.]37
41
51[.]81[.]57[.]58/31
41
64[.]98[.]36[.]4
39
103[.]224[.]212[.]34
38
125[.]209[.]238[.]100
38
211[.]231[.]108[.]46/31
37
67[.]195[.]204[.]72/30
34
142[.]250[.]80[.]68
34
157[.]240[.]229[.]174
33
212[.]54[.]56[.]11
29
117[.]53[.]116[.]15
29
62[.]141[.]42[.]208
29
67[.]231[.]149[.]140
27
64[.]233[.]186[.]26/31
27
98[.]136[.]96[.]92/31
26
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences microsoft[.]com
44
www[.]google[.]com
44
whois[.]arin[.]net
44
whois[.]iana[.]org
44
mx-aol[.]mail[.]gm0[.]yahoodns[.]net
44
defeatwax[.]ru
44
comcast[.]net
43
mx1[.]comcast[.]net
43
al-ip4-mx-vip1[.]prodigy[.]net
43
aspmx[.]l[.]google[.]com
42
mx[.]dca[.]untd[.]com
41
mx01[.]mail[.]icloud[.]com
41
sbcglobal[.]net
41
att[.]net
41
mx1[.]seznam[.]cz
40
verizon[.]net
40
mx01[.]oxsus-vadesecure[.]net
40
mx00[.]mail[.]com
40
nam[.]olc[.]protection[.]outlook[.]com
39
mx1[.]naver[.]com
38
naver[.]com
38
seznam[.]cz
38
park-mx[.]above[.]com
38
bellsouth[.]net
38
mail[.]com
37
*See JSON for more IOCs
Files and or directories created Occurrences %SystemRoot%\SysWOW64\config\systemprofile
44
%SystemRoot%\SysWOW64\config\systemprofile:.repos
44
%SystemRoot%\SysWOW64\<random, matching '[a-z]{8}'>
44
%TEMP%\<random, matching '[a-z]{8}'>.exe
44
%System32%\config\systemprofile:.repos
27
%System32%\<random, matching '[a-z]{7,8}'>\<random, matching '[a-z]{6,8}'>.exe (copy)
27
%TEMP%\jokcadp.exe
2
unknown
1
%TEMP%\ejfxvyk.exe
1
%TEMP%\afbtrug.exe
1
%TEMP%\tyumknz.exe
1
File Hashes 0b4e2c9b67f936875746e032496209ca425f8aef448f33f2c7aff72d174a2f94
0f9012815e5f4aa61b97a690fe091d59dd68926ab6ba5d85226b4f571a01c254
10b7994528717f496d9f2299c3c64abd3d9961f26c6e64b714607f56438b7c5a
1d100f428cf90a965ae5df622f1b2633b1f473321ce8b3837932ba9ceb4408d7
26b6716ceed916eeea55424d39518ddf15970f8315790fe6e422c445b198ed89
295000e5f030d99d6a2237d4126e3223660f49a7e5027f060d5f43e1a8677a66
2da0036e0229f7302c9a00aa3bca40b49b177f964e4e7589172958a6820e5469
2eff9d8a775269d9549b2dc1dfbf625af3f1d20f8a60e51a2590fd9bf464830a
321a449d4fe34de4b177cc18d158ab7c165e6ccc865a2736974c3452a35b4a13
3ae52f1048ef5c443101d2604c4700e0483002655e4ceed11da832ccc429658a
3cdfc9ac1ff7be14c1f115c168606e68b43c19cdabe0971b166a2c56e6ce27a2
3ef0a75ff61bb53bed611360b1be0377cfb729c413bcbb87d3f2ee5197267462
449e9c391ad5f2ff3bbe19cb4858b4ec071578fefd2e17ab09158b0884b6b787
51e23a0b883f72033453b9924bbd800bea6732ebb70bbd148b87c293e239090b
5263dae6e8781d5d31208bf28a879d9bdde260c08b5827220e35e1d5a2a2c848
5594f1a1ceb9eeaf54ec1d0807b0dbc8bf5cd884fea52dbdf1dd993cdb59ef1d
58e8bdf2bdeae74db6715e2bee515c334f5c798c16835029dc29f03ac08d5724
65cc65205f380529c29619296d0ff2a2f8b1c3377d6561ccdf1c0a8f4d4740f3
6a6d7cc1525ef5c15dddddecb3f4bab641109113734b037ebd2bfdefb0e3ee54
6b75a9a7b59e16d6f14029d14fe7899ee30add9e78b71eb64a6ad2c37d0cce83
6ece315f6c13127daa234ba16133f941a4f66c95898e5f20a90c6f81fe0fa4bf
717d9a956090dbc0e17fcd76529cd30a8e7c92d5e0b98cc1d50a72fae58b9c0d
7375f82042d938426b5b98e012b078edf655e85570bb324085892140bbd99b44
7598d4a188c19d42de5c49b2ed5e976bff5e5970faac0803b7b10123f5fa8970
78d334908aa47a40e54afb2768856ecb1b04d98ef9aecfc1264e156c6ba6a99e*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
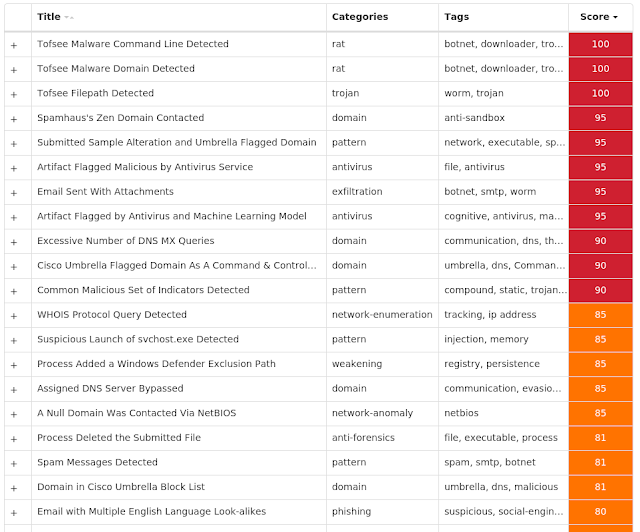
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Exploit.Remcos-9896449-0 Indicators of Compromise IOCs collected from dynamic analysis of 17 samples Registry Keys Occurrences <HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
12
<HKCU>\SOFTWARE\13ASDADSSDSSDSDSD12132AZ-DE8H5O
11
<HKCU>\SOFTWARE\13ASDADSSDSSDSDSD12132AZ-DE8H5O
Value Name: exepath
11
<HKCU>\SOFTWARE\13ASDADSSDSSDSDSD12132AZ-DE8H5O
Value Name: licence
11
<HKCU>\SOFTWARE\REMCOS-YLWG0R
2
<HKCU>\SOFTWARE\REMCOS-YLWG0R
Value Name: exepath
2
<HKCU>\SOFTWARE\REMCOS-YLWG0R
Value Name: licence
2
<HKCU>\SOFTWARE\REMCOS-9TTY5N
2
<HKCU>\SOFTWARE\REMCOS-9TTY5N
Value Name: exepath
2
<HKCU>\SOFTWARE\REMCOS-9TTY5N
Value Name: licence
2
<HKCU>\SOFTWARE\REMCOS-OH0RTL
1
<HKCU>\SOFTWARE\REMCOS-OH0RTL
Value Name: exepath
1
<HKCU>\SOFTWARE\REMCOS-OH0RTL
Value Name: licence
1
Mutexes Occurrences Remcos_Mutex_Inj
16
13asdadsSDSSDSDSD12132az-DE8H5O
11
Remcos-YLWG0R
2
Remcos-9TTY5N
2
Remcos-OH0RTL
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 151[.]101[.]248[.]193
17
37[.]1[.]206[.]16
11
199[.]232[.]36[.]193
9
185[.]158[.]115[.]38
5
Domain Names contacted by malware. Does not indicate maliciousness Occurrences i[.]imgur[.]com
17
ipv4[.]imgur[.]map[.]fastly[.]net
9
Files and or directories created Occurrences %APPDATA%\log
4
%APPDATA%\log\logs.dat
4
%TEMP%\8264ea72.png
1
%TEMP%\82831890.png
1
%TEMP%\heert\logs.dat
1
%TEMP%\21137fd7.png
1
%TEMP%\22979f87.png
1
%TEMP%\2323c0a7.png
1
%TEMP%\23848a15.png
1
%TEMP%\2c687393.png
1
%TEMP%\2ccbe4dd.png
1
%TEMP%\2d098877.png
1
%TEMP%\28629aa9.png
1
%TEMP%\286e770b.png
1
%TEMP%\2898069f.png
1
%TEMP%\28f0d5e3.png
1
%TEMP%\29015699.png
1
%TEMP%\29015b67.png
1
%TEMP%\2a496bd1.png
1
%TEMP%\2a6a5d01.png
1
%TEMP%\2aa7b671.png
1
%TEMP%\2b37a21b.png
1
%TEMP%\2e029a9f.png
1
%TEMP%\2e0c3dd1.png
1
%TEMP%\2e35091f.png
1
*See JSON for more IOCs
File Hashes 0162fab653723779f15a521d3685d026de2da29a76e885d1da46fcc52307afc1
0ab18843c438b19690d77bc36f71256fbb81f2479303e13d29da2cd3b65b776d
23a16ac07241022aee8822e8c4e05f2331a42b85f5002aeb23ed9ee23c69a22f
271e7a902e447edc2dfa495b7bf8506423a98f60b97b7b49a4a0e7cded2966db
2995e37af90e1111fd6942ad5013f312a93abe21d5143a68c17df5a5dc41c5a8
3401f12db8aa80085135b3ecc7b2fa828fdc3cd002992bf541f3c553659b61bf
3688d08bb5633ae00afa3b3c17175f4c797ca1836cdc632987a96c2d5f496f09
3779cc684c8cd7cf3123062b6842698c846b4507dc7c35a3e1be67d9cf21eb12
3ca5a39516fb278ae23885c814dac380948875e20b2f6fe5b243c7f9b4b2c55e
6b9a5c59867970abc27117817db6dcd067dd2d17ce1361460601d5f7a12f936c
a8fc0b662156d82b8a7ff82ce5bae303dbdfcb32fdbfc838451cf0726f287f8e
ca41eba8256eb3bed9245547c92c9c6d48310f0035851ee80063f8e71529ed59
cdfcb467a1ffc9ecb78d8fdcb0e4bc11fbf843d8e0c34868911e49db2055a104
d6c079623357414a71392a308efd105161cae42dae547cf216f8390e6c55e118
ed4bc525e8b79029bb1316281668071fe0fff270c83fe66e275e4452f159d58d
eda91a21dd01e298503a7b225d73223690a34d4ce8c54869046f9d38bb133293
f52623e5d33cfb953bd2958d2621772db68415791f32c0a958c459b6f30b2130Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
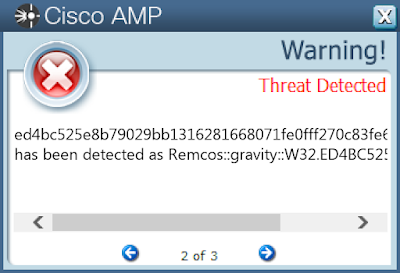
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Indicators of Compromise IOCs collected from dynamic analysis of 20 samples Registry Keys Occurrences <HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
19
<HKCU>\ENVIRONMENT
Value Name: windir
10
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Xkkzuif
2
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Kuhlnor
2
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Zjopims
2
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\P33DDE0GM9
1
<HKCU>\SOFTWARE\OFFICE360-ASSYPK
1
<HKCU>\SOFTWARE\OFFICE360-ASSYPK
Value Name: exepath
1
<HKCU>\SOFTWARE\OFFICE360-ASSYPK
Value Name: licence
1
<HKCU>\SOFTWARE\REMCOS-8VTGWT
1
<HKCU>\SOFTWARE\REMCOS-8VTGWT
Value Name: exepath
1
<HKCU>\SOFTWARE\REMCOS-8VTGWT
Value Name: licence
1
<HKCU>\SOFTWARE\REMCOS-54EHDX
1
<HKCU>\SOFTWARE\REMCOS-54EHDX
Value Name: exepath
1
<HKCU>\SOFTWARE\REMCOS-54EHDX
Value Name: licence
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Nucfvvj
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Rdsjdfv
1
<HKCU>\SOFTWARE\REMCOS-GIA6OR
1
<HKCU>\SOFTWARE\REMCOS-GIA6OR
Value Name: exepath
1
<HKCU>\SOFTWARE\REMCOS-GIA6OR
Value Name: licence
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Szvmbmi
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Zrzsaez
1
<HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: Cdtbwmp
1
Mutexes Occurrences 8-3503835SZBFHHZ
4
Remcos_Mutex_Inj
4
L50P-7PUFX6AYHMZ
2
S-1-5-21-2580483-9083183940534
2
80ONCA3AF1DGC91-
2
S-1-5-21-2580483-90819155372
1
office360-ASSYPK
1
Remcos-8VTGWT
1
Remcos-AF5FCY
1
Remcos-54EHDX
1
Remcos-GIA6OR
1
Global\cd9f7c91-1faf-11ec-b5f8-00501e3ae7b6
1
Global\cd127701-1faf-11ec-b5f8-00501e3ae7b6
1
Global\cf5663f1-1faf-11ec-b5f8-00501e3ae7b6
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 192[.]35[.]177[.]64
4
72[.]21[.]81[.]240
3
162[.]159[.]135[.]233
3
13[.]107[.]42[.]12/31
3
34[.]102[.]136[.]180
3
103[.]141[.]138[.]110
3
88[.]198[.]46[.]71
3
91[.]195[.]240[.]94
2
213[.]171[.]195[.]105
2
162[.]159[.]130[.]233
2
162[.]159[.]129[.]233
2
162[.]159[.]134[.]233
2
23[.]227[.]38[.]74
2
67[.]20[.]113[.]94
2
156[.]232[.]245[.]157
2
135[.]125[.]21[.]72
2
162[.]215[.]240[.]160
2
40[.]126[.]26[.]134/31
2
184[.]168[.]131[.]241
1
69[.]164[.]0[.]128
1
198[.]71[.]232[.]3
1
47[.]91[.]170[.]222
1
217[.]26[.]48[.]101
1
192[.]185[.]5[.]146
1
162[.]159[.]133[.]233
1
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences cdn[.]discordapp[.]com
6
apps[.]digsigtrust[.]com
4
apps[.]identrust[.]com
4
cs11[.]wpc[.]v0cdn[.]net
3
login[.]live[.]com
3
nadzakov[.]mk
3
onedrive[.]live[.]com
2
shops[.]myshopify[.]com
2
pouros[.]com
2
www[.]pouros[.]com
2
www[.]thebusinessfitclub[.]com
2
www[.]jakesplacebarbers[.]com
2
pentester01[.]duckdns[.]org
2
www[.]thespoonteller[.]com
2
www[.]lafabricadisseny[.]com
2
cutting-tools[.]in
2
engkaa[.]ddns[.]net
1
blessings4x4[.]hopto[.]org
1
oqyu9w[.]sn[.]files[.]1drv[.]com
1
www[.]lapurtcedd[.]com
1
www[.]cohenasset[.]info
1
www[.]paulettecallen[.]com
1
www[.]mariangelamata[.]com
1
mysekrit[.]com
1
www[.]westwooddesign[.]net
1
*See JSON for more IOCs
Files and or directories created Occurrences %PUBLIC%\nest
11
%PUBLIC%\KDECO.bat
11
%PUBLIC%\Trast.bat
11
%PUBLIC%\UKO.bat
11
%PUBLIC%\nest.bat
9
%ProgramFiles%\Microsoft DN1
3
%PUBLIC%\Libraries\Zjopims\Zjopims.exe
2
%PUBLIC%\Libraries\smipojZ.url
2
%PUBLIC%\Libraries\Xkkzuif
2
%PUBLIC%\Libraries\Xkkzuif\Xkkzuif.exe
2
%PUBLIC%\Libraries\fiuzkkX.url
2
%PUBLIC%\Libraries\Kuhlnor
2
%PUBLIC%\Libraries\Kuhlnor\Kuhlnor.exe
2
%PUBLIC%\Libraries\ronlhuK.url
2
%PUBLIC%\Libraries\Gieftwm
2
%PUBLIC%\Libraries\Gixpfha
2
%PUBLIC%\Libraries\Zjopims
2
%LOCALAPPDATA%\Microsoft Vision
1
\REGISTRY\MACHINE\SOFTWARE\Classes\AllFilesystemObjects
1
%PUBLIC%\Libraries\Bjivlrx\Bjivlrx.exe
1
%PUBLIC%\Libraries\xrlvijB.url
1
%APPDATA%\ajyzEaq.tmp
1
%APPDATA%\gys..hh.tmp
1
%PUBLIC%\Libraries\Uwffwej
1
%PUBLIC%\Libraries\Nucfvvj
1
*See JSON for more IOCs
File Hashes 03811a474b07747d26379d33ee6788366f0d49bf993334d16607b361093463af
198a6c69303e222c1e37be51ff9cf68615b4879fb2b152f96aad90daf49c7df1
1dcfdd6b6b25255658faf41cae5b9177ca760d249b95342100a09c9794004485
1ddb357041ae22e5c39f309d8432bf9b64e5b07ee9fcf578b7d94543005714fa
3bd6a9adf74441ad24715295a3a63d76cb6ea26139b4f60de88dfe642129faf0
4479f2a8ba10224ab48953c468ece2bf5fcb1ebc3f2546681bbd4de5f5d286dd
68fc6fbd664578701fb3567897a5c7d94b8973b4085324b7dce91a9b123b5ff8
8a39968eafe739591b3506c908fe5efc9ebc97654d8d2bde8f22299b6fdf0d3f
8bc32885f532e286073afa7781733d97338f3bab7b22f55680b38fe1926d103b
90e9c971939cb7168124cf0fb865d1166e6218608ccfeea19bd507b6df20bb5f
970a9e6833244c70bef835b3bcdcaca5d4ba325509fd8264f7a901bfd9a1c4c0
a1b21077e09e0021aeabaea974f7a304f3b5f89b34bd19eb9045a67451f63f79
acdd6834ed905603a968ba017285e27238e8817d1b211d7f5a2e8a51e7d06e93
b05d244488d629ef3c2dc85ada466ffc16afdf0c69bf48453f9df84e6711994f
c58d5b907f0eb1e164f6416a122ae8177bae14a6a4ab2f00cffa2dc72a328068
d105b717b7320c3f5da89c8faabba236d360688d44d76e0a2fc2d62620ba0de6
d4a0c2c9e8f7e470b0fcf5e575f51ac83cd4be6ad1c188b2509672016ae8675a
d4f68d6197e020ae43c75b2a27fd8b5285c3c7dee32ca1f17a205602ab6cb33a
f81a53f5f0190d7d896949a8c28a1fd9d67736c060e779f430c5aa1b8b963acf
fc1248de64bf4f37a88e7f088dbb15c49d332e97ac434da57cc1085abad17d15Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
WSA
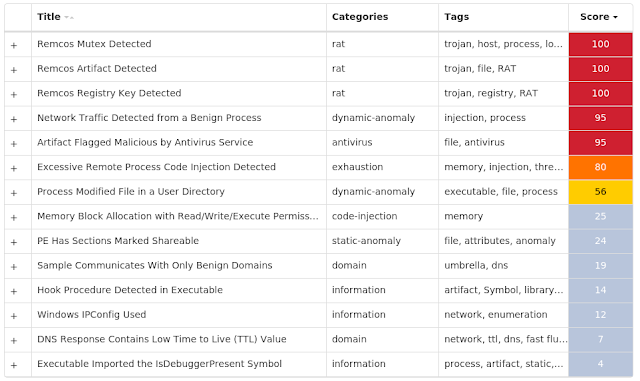
Screenshots of Detection AMP
ThreatGrid
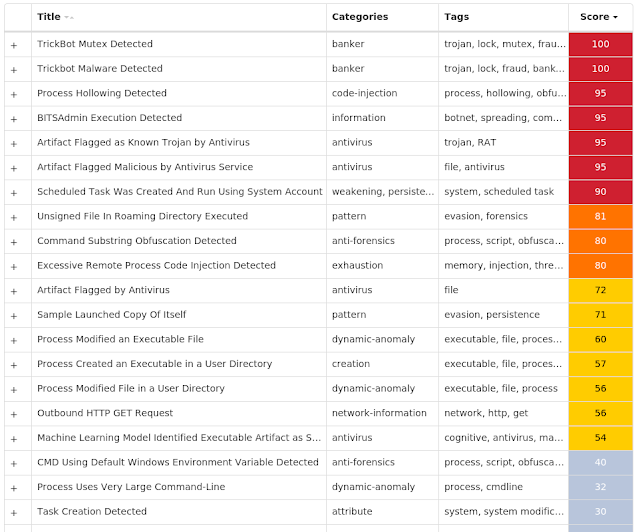
MITRE ATT&CK Win.Dropper.TrickBot-9897455-0 Indicators of Compromise IOCs collected from dynamic analysis of 44 samples Registry Keys Occurrences <HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
44
<HKU>\.DEFAULT\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\CA\CERTIFICATES\A053375BFE84E8B748782C7CEE15827A6AF5A405
5
<HKU>\.DEFAULT\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\CA\CERTIFICATES
Value Name: A053375BFE84E8B748782C7CEE15827A6AF5A405
5
<HKU>\.DEFAULT\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\CA\CERTIFICATES\A053375BFE84E8B748782C7CEE15827A6AF5A405
Value Name: Blob
5
Mutexes Occurrences 316D1C7871E00
44
785161C887200
1
1003FDECF7B0128
1
037C8F603D800
1
BAF949D027400
1
7FCFFACAEB2832832
1
7B76E7489D200
1
FCA2CB162C5832960
1
B1CC8CDC3370128
1
51D15B746DD0128
1
701B7E88FA200
1
C3AEA3548D50128
1
D8AB066819A00
1
1C16670A9C2832832
1
F7F0D3A64E9832960
1
EC20E656995832960
1
5A4E270C9C30128
1
FD4085DC1770128
1
91A08AC42B10128
1
205FC6CC1B30128
1
29F86466919832960
1
02895116445832960
1
298B6AB2AAC832832
1
9C4653C84F200
1
0AFA6B6AADA832832
1
*See JSON for more IOCs
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 34[.]117[.]59[.]81
20
37[.]230[.]114[.]93
8
141[.]255[.]167[.]124
7
78[.]24[.]218[.]206
6
116[.]203[.]16[.]95
5
92[.]63[.]106[.]43
5
95[.]154[.]199[.]237
5
23[.]3[.]125[.]111
5
62[.]109[.]25[.]11
4
95[.]213[.]195[.]169
4
62[.]109[.]14[.]24
4
104[.]18[.]7[.]156
4
92[.]63[.]102[.]238
4
62[.]109[.]26[.]251
3
62[.]109[.]24[.]242
3
193[.]233[.]62[.]60
3
194[.]87[.]103[.]210
3
94[.]127[.]111[.]14
2
52[.]204[.]109[.]97
2
78[.]155[.]218[.]189
2
82[.]146[.]57[.]127
2
54[.]39[.]106[.]25
2
194[.]87[.]146[.]135
2
78[.]155[.]218[.]137
2
95[.]213[.]237[.]49
2
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences cw57146[.]tmweb[.]ru
44
ipecho[.]net
11
api[.]ipify[.]org
6
checkip[.]amazonaws[.]com
6
myexternalip[.]com
6
icanhazip[.]com
5
ip[.]anysrc[.]net
5
r3[.]i[.]lencr[.]org
5
oiltrend[.]ru
3
ipinfo[.]io
3
wtfismyip[.]com
2
Files and or directories created Occurrences %System32%\Tasks\services update
44
%APPDATA%\localservice
44
%APPDATA%\localservice\Modules
44
%APPDATA%\localservice\client_id
44
%APPDATA%\localservice\group_tag
44
%APPDATA%\LOCALSERVICE\<original file name>.exe
44
%APPDATA%\localservice\939ee2656636g8c700fbece672ec0ce4.exe
1
%APPDATA%\localservice\2b6e562f7ab73b3fg663e2677g8496e8a6b392e8b5969b25g67e6cca890e5026.exe
1
%APPDATA%\localservice\03e85e00g50c8337e62773864ef526ca47aea42bb78a3026b02585g38ag60cec.exe
1
%APPDATA%\localservice\bg7ef8g05ef6f69b36g3gcb86629098f0ea557a39c907g56f3b50b2a5b40gcb5.exe
1
%APPDATA%\localservice\69a9653a0ag6b746e0bgg5a4662936f8f9g7eecg3fb6e2a6a0c262ee8b5f4466.exe
1
%APPDATA%\localservice\509b48e859e25870f94a6307ga8c5bcb3ff5e8g3efgcccgcb6040a395e6968ca.exe
1
%APPDATA%\localservice\2g52c6e42e6e38fa6735cfgacbf256402a60a2g9f6g64g9276927580g56095c0.exe
1
%APPDATA%\localservice\4c0f86b806ega36b6c467ce435c89bgabe080750075g3accgbaf5e33af33cg49.exe
1
%APPDATA%\localservice\2497efb929ff2c5675969a530a5696g370b34b845egc6279f6g66ba48ab360c4.exe
1
%APPDATA%\localservice\6b2cf38277b66ff26e0gegb6e7a4a79baa80e32bf93f6g684a746fb69e602e60.exe
1
%APPDATA%\localservice\93eab556bff458a3627e979b8969e75f28e0f5750c56a8a89602a5cbg64e0a53.exe
1
%APPDATA%\localservice\g95f6605abgb726g38bb73e7e5fgfg470gc68a6g32fb7gb666f9792353929fe6.exe
1
%APPDATA%\localservice\g963735be6c0cg6008c276538c328ee7c456ag228a90449676a7369g5e83640c.exe
1
%APPDATA%\localservice\af6bgc3c36a7ga96gb9363c40763g20e606862a2gf53c60e4fagb06764a6b662.exe
1
%APPDATA%\localservice\be457fa00agb065e2b9fb8728b3eg6f0b3e85e46ca43acc7b0b5730ebf078b30.exe
1
%APPDATA%\localservice\59575e00be62eb6ce399048a2g6237agb66269f63ae6555604geb65874fa88f0.exe
1
%APPDATA%\localservice\ac957566g66658ea9af66f2gec07626b8b83ba86a56b6gc83gf062824ceg6cf6.exe
1
%APPDATA%\localservice\g966af2935c83068960ba863ge00gag6797f67ebf567f2663g523f0g3ag24a7c.exe
1
%APPDATA%\localservice\872e86267cf6c5039eae332964ag28848f6ff792c86638a748c6c374657g683e.exe
1
*See JSON for more IOCs
File Hashes 02d84d00f40c8227d51772863de415ca37ada31bb78a2016b01484f28af60cdc
08b8396290a4138a59a396786c54d9aa79128ae17bbe75a5f42cb7716e17661e
0db5a116a4bd1e22650b89d6da4462749ce1b198d568cc2fa3bf7231670fa265
1397deb919ee1c4574969a420a4696f270b23b834dfc5179e6f55ba38ab250c3
159e117a315aab00ea23dbd39440203ec961e8c9a831ea1c629a6f4fc1116ea5
184ce8dffff4f4f0f8824e690a8150b1706493a0949e42a9e6634641333aa1a5
1b6d451e7ab72b2ef562d1577f8396d8a6b291d8b4959b14f67d6cca890d4015
1b949dd78253c6d5a34fb7514fb6957b17b4296b78be197a0eb1a58d6b90d552
1e8d38a6dc628565790750f1590cc1d64adae5cc6523e9188dadc8d62ec36e56
1f41c6d31d5d28ea5724cefacbe145301a50a1f9e5f63f9175917480f46094c0
26f6344ef60dcd4a1424a3330fd1594285dbaafb8e7fd4a4d061fd5d74a85a0f
2b373a0d5820039ead4219e3fe80493147f5ec070f3942a4116dd30b57241ea9
2c79a713408188549524a75bc4559ef446f17eb147602330a5364fcf4cc46b77
2f8ae451c18767acafbfa8b9722f3480101e76a512b4f58fcf66abd6d4495eb2
3323e1a7ff45e3d4ab891e8d2c07420dfe5afb47a2005133420b4de366ccff64
359375b4d76ece4ebe11b44624f6654bfb870f970d1d014aa71d8f8540e9be65
360989dbe8f345176f1fe203d1690c3ff4f90fa2320e21912cf956e41383bffc
3a29d1b5ebf27c4347142d93afeca399c91f1e05b2cf39ab3982e9c273242f5c
3c0e85b806dfa25b5c367cd324c89bfabd080740074f2accfbae4d22ae22cf39
3f1097f955d846304ebf6c1610ef884ea1f1097faeaed20bf5d465a41afad060
409b38d849d14870e93a6207fa8c4bcb2ee4d8f2defcccfcb6030a294d6968ca
40d2dadcc66d5382b2588ba198b8d8e42a7d2b39347838b9b2a0ec51ed59ef28
44d56973b2e2efd04075e87fee6c23cb1f71dd4bb70d9cab1c43f17e62cb9c51
44fcc04abf3811ee7d037eaaa517cbc9783430edaf367d30ec1155b8321fb848
49474d00bd61db5cd299038a1f6127afb56159e52ad5444603fdb54873ea88e0*See JSON for more IOCs
Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
Screenshots of Detection AMP
ThreatGrid
MITRE ATT&CK Win.Dropper.Gh0stRAT-9896856-0 Indicators of Compromise IOCs collected from dynamic analysis of 14 samples Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SCHEDULE
Value Name: NextAtJobId
13
<HKCR>\LOCAL SETTINGS\SOFTWARE\MICROSOFT\WINDOWS\SHELL\BAGS\159
13
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 7A4E2DB7
8
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 2DF1B9FE
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 7A13344E
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 9C7F6B03
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: 14897893
1
<HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
Value Name: E2720FC3
1
Mutexes Occurrences cdn.vpsktq.com:12723127.0.0.1:2012127.0.0.1:2012
8
q.vvcq.net:12723127.0.0.1:2012127.0.0.1:2012
1
kor.koral2013.com:8808199.36.74.20:8808:
1
q.vvbhgv.com:12711127.0.0.1:2012127.0.0.1:2012
1
126.114.227.193:1313127.0.0.1:2012127.0.0.1:2012
1
108.171.247.74:77888::
1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 126[.]114[.]227[.]193
1
199[.]36[.]74[.]20
1
108[.]171[.]247[.]74
1
13[.]249[.]38[.]69
1
Domain Names contacted by malware. Does not indicate maliciousness Occurrences cdn[.]vpsktq[.]com
8
q[.]vvbhgv[.]com
1
q[.]vvcq[.]net
1
kor[.]koral2013[.]com
1
Files and or directories created Occurrences %System32%\Tasks\At1
13
%System32%\Tasks\At10
13
%System32%\Tasks\At11
13
%System32%\Tasks\At12
13
%System32%\Tasks\At13
13
%System32%\Tasks\At14
13
%System32%\Tasks\At15
13
%System32%\Tasks\At16
13
%System32%\Tasks\At17
13
%System32%\Tasks\At18
13
%System32%\Tasks\At19
13
%System32%\Tasks\At2
13
%System32%\Tasks\At20
13
%System32%\Tasks\At21
13
%System32%\Tasks\At22
13
%System32%\Tasks\At23
13
%System32%\Tasks\At24
13
%System32%\Tasks\At3
13
%System32%\Tasks\At4
13
%System32%\Tasks\At5
13
%System32%\Tasks\At6
13
%System32%\Tasks\At7
13
%System32%\Tasks\At8
13
%System32%\Tasks\At9
13
%SystemRoot%\Tasks\At1.job
13
*See JSON for more IOCs
File Hashes 172e9f7f697fec4463a9b41233ebbf8063bc25b26657c08770c59f2279038aea
218905c47aa02c3b70ffb6298a89ff6742e74a48ce3a8495941d09dadf7b80ac
3bf0bf7eec064fa7feb03c9b3c407fb56cc16a451d85aef27842d929debea324
3fcd920d06218d8f78cfc80b506a498932e99fcdfa84127220f870599d957378
6612ae1eff861adb6fa8299591b6a56cb54127601a531f5af750082ed3609af2
683ed3ad71b6e04d1c3a36b1c072db6ae1417c314a4ce5cce0c83184c6c0ee78
6970e2bffc086b30caad7cf9a8d153f2de4e8a5dd508fb8689d23b513529267d
8ecaf09c62f7df0d5c5ed2ecf028c52748517a49e759294444d9e8748fbe05bc
a7a2cacc0d7871620c54a56a8ed26b9f34a27e0ad820ee72ee29328018ddb6a7
bc18d5f0e6109c6e3cfdd68a98c7e11d5819509409698c38facc58bef136c8c3
bc2c74160da7528efdcb1463c59324bffc0018d2321b851e033a0f23cb64b711
c239fd0c6973493704d648a87528b41d0735d252c2e80d6afdde9d9226a0ada2
c9cdcfa8640ab493725b6e94a7322f7bad9314df45a6629ec5835df2b5005537
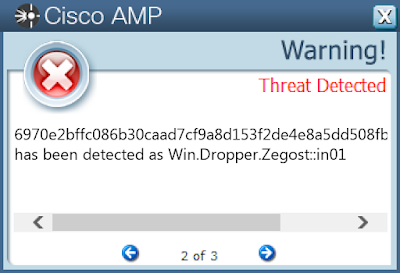
ff1110d7ba1f155bc6dcddc16f5cdcf2eac13cf1d0dc826b9f580b5024552ef2Coverage Product Protection AMP
Cloudlock
N/A
CWS
Email Security
Network Security
N/A
Stealthwatch
N/A
Stealthwatch Cloud
N/A
Threat Grid
Umbrella
N/A
WSA
N/A
Screenshots of Detection AMP
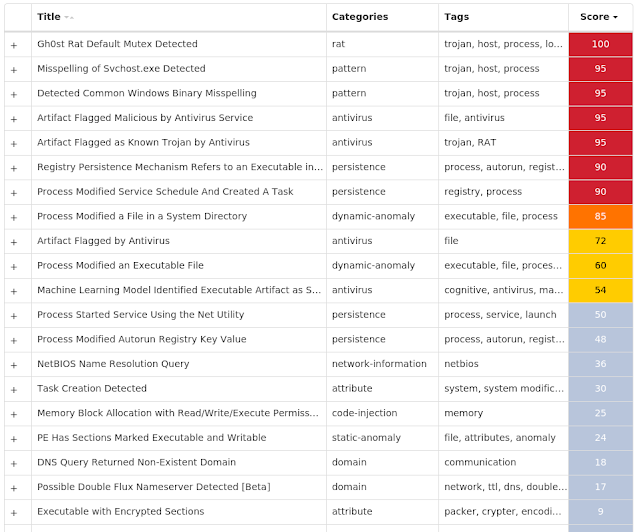
ThreatGrid
MITRE ATT&CK Exploit Prevention Cisco AMP for Endpoints protects users from a variety of malware functions with exploit prevention. Exploit prevention helps users defend endpoints from memory attacks commonly used by obfuscated malware and exploits. These exploits use certain features to bypass typical anti-virus software, but were blocked by AMP thanks to its advanced scanning capabilities, even protecting against zero-day vulnerabilities.
Process hollowing detected - (15818)
Process hollowing is a technique used by some programs to avoid static analysis. In typical usage, a process is started and its obfuscated or encrypted contents are unpacked into memory. The parent then manually sets up the first stages of launching a child process, but before launching it, the memory is cleared and filled in with the memory from the parent instead.
Excessively long PowerShell command detected - (9924)
A PowerShell command with a very long command line argument that may indicate an obfuscated script has been detected. PowerShell is an extensible Windows scripting language present on all versions of Windows. Malware authors use PowerShell in an attempt to evade security software or other monitoring that is not tuned to detect PowerShell based threats.
Crystalbit-Apple DLL double hijack detected - (7395)
Crystalbit-Apple DLL double hijack was detected. During this attack, the adversary abuses two legitimate vendor applications, such as CrystalBit and Apple, as part of a dll double hijack attack chain that starts with a fraudulent software bundle and eventually leads to a persistent miner and in some cases spyware deployment.
A Microsoft Office process has started a windows utility. - (4492)
A process associated with Microsoft Office, such as EXCEL.exe, OUTLOOK.exe or WINWORD.exe, has started a Windows utility such as powershell.exe or cmd.exe. This is typical behavior of malicious documents executing additional scripts. This behavior is extremely suspicious and is associated with many malware different malware campaigns and families.
Reverse tcp payload detected - (3770)
An exploit payload intended to connect back to an attacker controlled host using tcp has been detected.
CVE-2020-1472 exploit detected - (3150)
An attempt to exploit CVE-2020-1472 has been detected. Also known as "Zerologon". This is a privelege escalation vulnerability in Netlogon.
Kovter injection detected - (3051)
A process was injected into, most likely by an existing Kovter infection. Kovter is a click fraud Trojan that can also act as an information stealer. Kovter is also file-less malware meaning the malicious DLL is stored inside Windows registry and injected directly into memory using PowerShell. It can detect and report the usage of monitoring software such as wireshark and sandboxes to its C2. It spreads through malicious advertising and spam campaigns.
Expiro Malware detected - (2952)
Expiro malware is unique in that it infiltrates executable files on both 32- and 64-bit Windows systems by appending its viral code to the host. It can be used to install malicious browser extensions, lower browser security settings, and steal account credentials.
Dealply adware detected - (1156)
DealPly is adware, which claims to improve your online shopping experience. It is often bundled into other legitimate installers and is difficult to uninstall. It creates pop-up advertisements and injects advertisements on webpages. Adware has also been known to download and install malware.
Squiblydoo application control bypass attempt detected. - (655)
An attempt to bypass application control via the "Squiblydoo" technique has been detected. This typically involves using regsvr32.exe to execute script content hosted on an attacker controlled server.