Threat Spotlight: "Kyle and Stan" Malvertising Network Threatens Windows and Mac Users With Mutating Malware
This post was authored by Shaun Hurley, David McDaniel and Armin Pelkmann. Malware was discovered by Richard Harman. Update 2014-09-22: Updates on this threat can be found here Have you visited amazon.com, ads.yahoo.com, www.winrar.com, youtube.com, or any of the 74 domains lis
Malware Using the Registry to Store a Zeus Configuration File
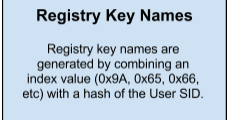
This blog was co-authored by Andrea Allievi. A few weeks ago I came across a sample that was reading from and writing a significant amount of data to the registry. Initially, it was thought that the file may be a binary, but after some analysis it was determined that the file is
Betabot Process Injection
Introduction A few weeks ago I received a PE file (MD5: 34105EF38CEA1B4B2ABADD0CB3404E69) and was asked to figure out if it is related to the Betabot malware family. It didn’t take long to figure out that this file is Betabot, but this seemed like an excellent sample to cover met
Using the Immunity Debugger API to Automate Analysis
Osx.Trojan.Leverage, a Breakdown Using Dtrace
This article provides a brief introduction to canned DTrace scripts for the purposes of analyzing the malwaresample, Osx.Trojan.Leverage. For this sample, I only needed to use a few of the canned scripts to gather a significant amount of data about how this piece of malware impac