An overview of ransomware threats in Japan in 2025 and early detection insights from Qilin cases
There were 134 ransomware incidents reported in Japan in 2025, representing a 17.5% year-over-year increase from 2024.
Ransomware in 2025: Blending in is the strategy
A summary of the top ransomware trends from the Talos 2025 Year in Review, with a focus on identity, attacker tactics, and practical defenses.
New BYOVD loader behind DeadLock ransomware attack
Cisco Talos has uncovered a new DeadLock ransomware campaign using a previously unknown BYOVD loader to exploit a Baidu Antivirus driver vulnerability, letting threat actors disable EDR defenses and escalate attacks.
Unleashing the Kraken ransomware group
In August 2025, Cisco Talos observed big-game hunting and double extortion attacks carried out by Kraken, a Russian-speaking group that has emerged from the remnants of the HelloKitty ransomware cartel.
Stopping ransomware before it starts: Lessons from Cisco Talos Incident Response
Explore lessons learned from over two years of Talos IR pre-ransomware engagements, highlighting the key security measures, indicators and recommendations that have proven effective in stopping ransomware attacks before they begin.
Ransomware incidents in Japan during the first half of 2025
Ransomware attackers continue to primarily target small and medium-sized manufacturing businesses in Japan.
Unmasking the new Chaos RaaS group attacks
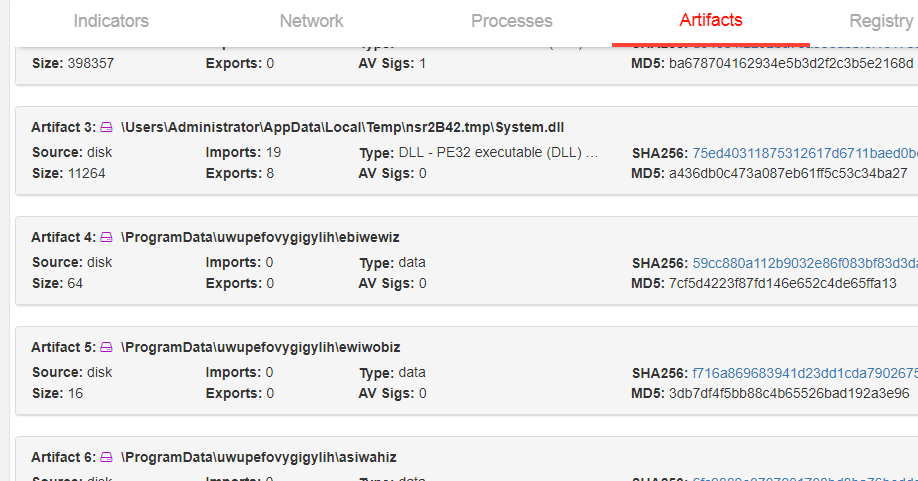
Cisco Talos Incident Response (Talos IR) recently observed attacks by Chaos, a relatively new ransomware-as-a-service (RaaS) group conducting big-game hunting and double extortion attacks.
Talos IR ransomware engagements and the significance of timeliness in incident response
The decision between immediate action and delayed response made the difference between ransomware prevention and complete encryption in these two real-world Talos IR engagements.
Cybercriminals camouflaging threats as AI tool installers
Cisco Talos has uncovered new threats, including ransomware like CyberLock and Lucky_Gh0$t, and a destructive malware called Numero, all disguised as legitimate AI tool installers to target victims.
Introducing ToyMaker, an initial access broker working in cahoots with double extortion gangs
Cisco Talos discovered a sophisticated attack on critical infrastructure by ToyMaker and Cactus, using the LAGTOY backdoor to orchestrate a relentless double extortion scheme.
Unwrapping the emerging Interlock ransomware attack
Cisco Talos Incident Response (Talos IR) recently observed an attacker conducting big-game hunting and double extortion attacks using the relatively new Interlock ransomware.
Akira ransomware continues to evolve
As the Akira ransomware group continues to evolve its operations, Talos has the latest research on the group's attack chain, targeted verticals, and potential future TTPs.
Threat actor believed to be spreading new MedusaLocker variant since 2022
The malware, called "BabyLockerKZ," has primarily affected users in Europe and South America.
GhostSec’s joint ransomware operation and evolution of their arsenal
Cisco Talos observed a surge in GhostSec, a hacking group’s malicious activities since this past year. GhostSec has evolved with a new GhostLocker 2.0 ransomware, a Golang variant of the GhostLocker ransomware.
New decryptor for Babuk Tortilla ransomware variant released
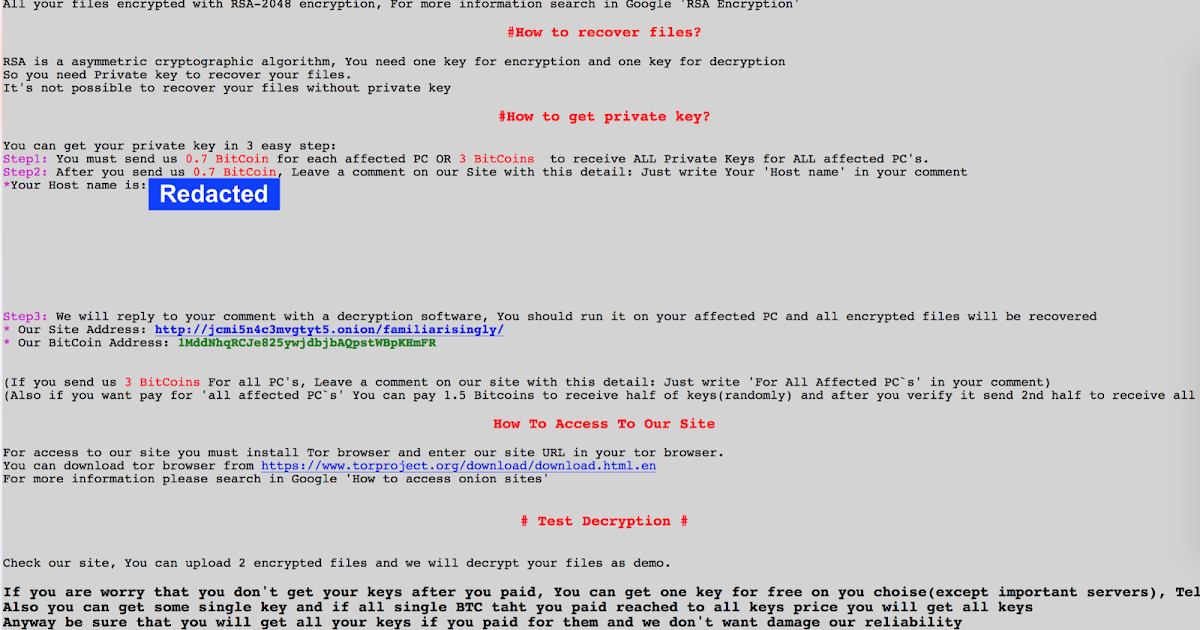
Cisco Talos obtained executable code capable of decrypting files affected by the Babuk Tortilla ransomware variant, allowing Talos to extract and share the private decryption key used by the threat actor.
Understanding the Phobos affiliate structure and activity
Cisco Talos identified the most prolific Phobos variants, TTPs and affiliate structure, based on their activity and analysis of over 1,000 samples from VirusTotal dating back to 2019. We assess with moderate confidence Eking, Eight, Elbie, Devos and Faust are the most common variants
What Cisco Talos knows about the Rhysida ransomware
The group appears to commonly deploy double extortion — of the victims that have been listed on the leak site, several of them have had some portion of their exfiltrated data exposed.
New threat actor targets Bulgaria, China, Vietnam and other countries with customized Yashma ransomware
Cisco Talos discovered an unknown threat actor, seemingly of Vietnamese origin, conducting a ransomware operation that began at least as early as June 4, 2023 with customized Yashma ransomware.
Active exploitation of the MOVEit Transfer vulnerability — CVE-2023-34362 — by Clop ransomware group
The Clop ransomware group has claimed responsibility for exploiting the vulnerability to deploy a previously unseen web shell, LemurLoot.
Newly identified RA Group compromises companies in U.S. and South Korea with leaked Babuk source code
Cisco Talos recently discovered a new ransomware actor called RA Group that has been operating since at least April 22, 2023.
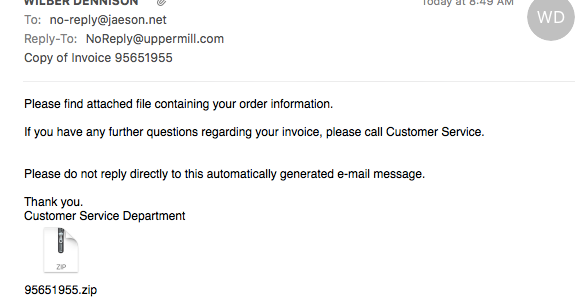
New MortalKombat ransomware and Laplas Clipper malware threats deployed in financially motivated campaign
Since December 2022, Cisco Talos has been observing an unidentified actor deploying two relatively new threats, the recently discovered MortalKombat ransomware and a GO variant of the Laplas Clipper malware, to steal cryptocurrency from victims.
Quarterly Report: Incident Response Trends in Q4 2022
Ransomware continued to be a top threat Cisco Talos Incident Response (Talos IR) responded to this quarter, with appearances from both previously seen and newly observed ransomware families.
Multiple ransomware data leak sites experience DDoS attacks, facing intermittent outages and connectivity issues
Cisco Talos has been monitoring suspected distributed denial-of-service (DDoS) attacks resulting in intermittent downtime and outages affecting several ransomware-as-a-service (RaaS) data leak sites.
De-anonymizing ransomware domains on the dark web
* We have developed three techniques to identify ransomware operators' dark websites hosted on public IP addresses, allowing us to uncover previously unknown infrastructure for the DarkAngels, Snatch, Quantum and Nokoyawa ransomware groups. * The methods we used to identify
Avos ransomware group expands with new attack arsenal
By Flavio Costa, * In a recent customer engagement, we observed a month-long AvosLocker campaign. * The attackers utilized several different tools, including Cobalt Strike, Sliver and multiple commercial network scanners. * The initial ingress point in this incident was a pa
The BlackByte ransomware group is striking users all over the globe
News summary * Cisco Talos has been monitoring the BlackByte Ransomware Group for several months, infecting victims all over the world, from North America to Colombia, Netherlands, China, Mexico and Vietnam. * The FBI released a joint cybersecurity advisory in February 2022 wa
Conti and Hive ransomware operations: What we learned from these groups' victim chats
As part of Cisco Talos’ continuous efforts to learn more about the current ransomware landscape, we recently examined a trove of chat logs between the Conti and Hive ransomware gangs and their victims. Ransomware-as-a-service groups have exploded in popularity over the past few
From BlackMatter to BlackCat: Analyzing two attacks from one affiliate
* BlackCat is a recent and growing ransomware-as-a-service (RaaS) group that targeted several organizations worldwide over the past few months. * There are rumors of a relationship between BlackCat and the BlackMatter/DarkSide ransomware groups, infamous for attacking the Colon
Translated: Talos' insights from the recently leaked Conti ransomware playbook
Executive summary Cisco Talos recently became aware of a leaked playbook that has been attributed to the ransomware-as-a-service (RaaS) group Conti. Talos has a team of dedicated, native-level speakers that translated these documents in their entirety into English. We also trans
Talos Takes Ep. #60: Everything you need to know about the Kaseya situation
By Jon Munshaw. The latest episode of Talos Takes is available now. Download this episode and subscribe to Talos Takes using the buttons below, or visit the Talos Takes page. In this special "XL edition" of Talos Takes, we're bringing you the audio version of our
REvil ransomware actors attack Kaseya in supply chain attack
Updated on July 6, 2021: As analysis of the ransomware attack affecting organizations using Kaseya VSA has continued, we are sharing an update containing additional information. As new details are identified, this information may be updated as needed. * This event consisted of
What’s past is prologue – A new world of critical infrastructure security
By Caitlin Huey, Joe Marshall and Thomas Pope. Attackers have targeted American critical infrastructure several times over the past few years, putting at risk U.S. electrical grids, oil pipelines and water supply systems. However, we collectively have not responded in a meaningf
A ransomware primer
Ransomware defense Cyber security is continually a relevant topic for Cisco customers and other stakeholders. Ransomware is quickly becoming one of the hottest topics in the technology space as these malware families target high-leverage companies and organizations. We at Cisco a
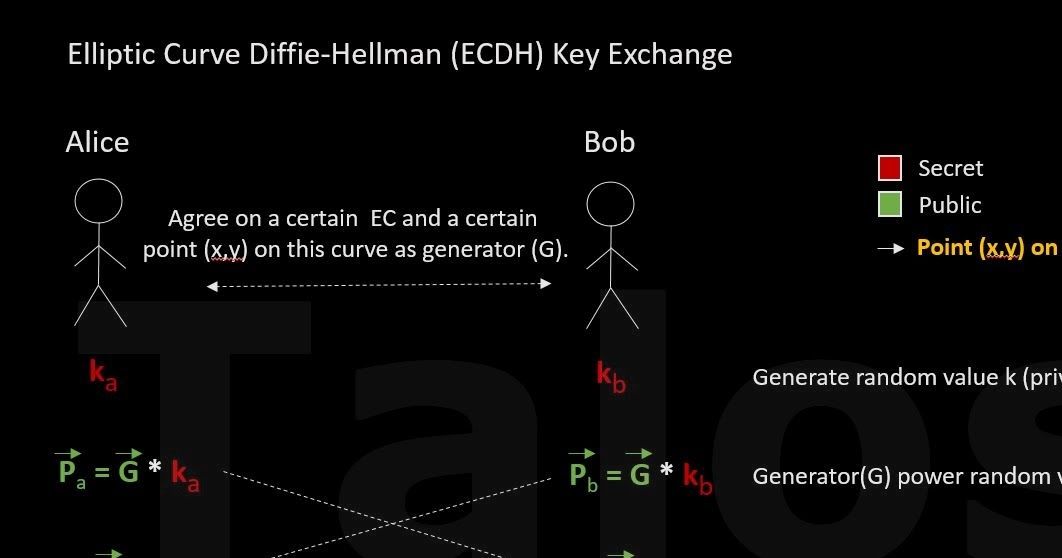
Nibiru ransomware variant decryptor
Nikhil Hegde developed this tool. Weak encryption The Nibiru ransomware is a .NET-based malware family. It traverses directories in the local disks, encrypts files with Rijndael-256 and gives them a .Nibiru extension. Rijndael-256 is a secure encryption algorithm. However, Ni
WastedLocker Goes "Big-Game Hunting" in 2020
By Ben Baker, Edmund Brumaghin, JJ Cummings and Arnaud Zobec. Threat summary * After initially compromising corporate networks, the attacker behind WastedLocker performs privilege escalation and lateral movement prior to activating ransomware and demanding ransom payment. *
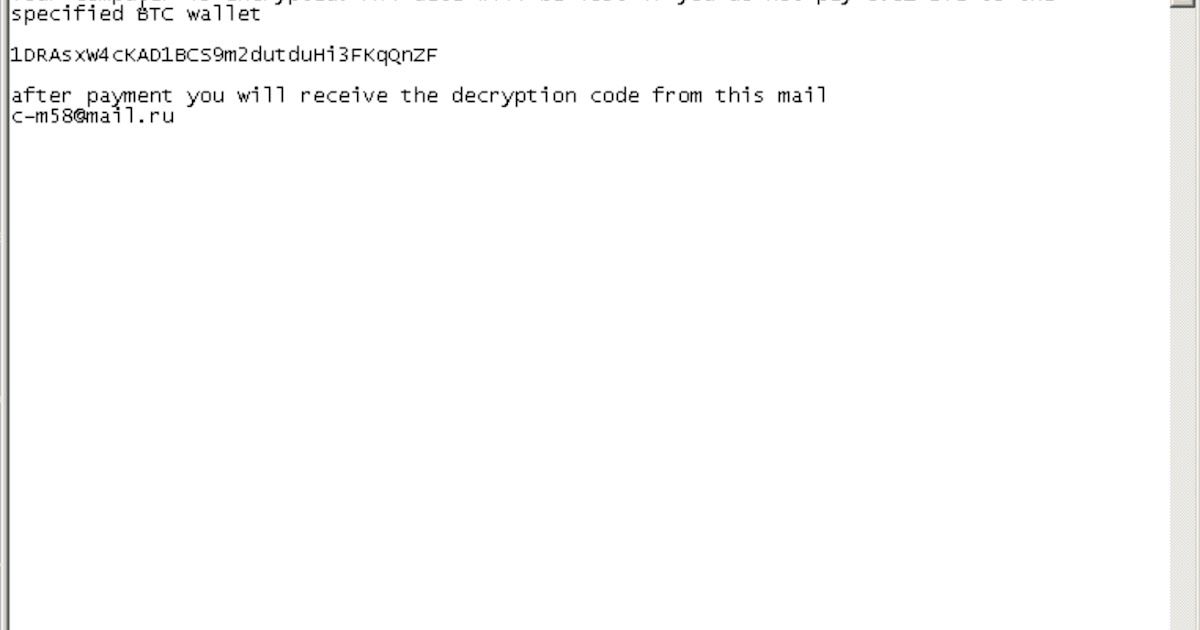
Threat Spotlight: MedusaLocker
By Edmund Brumaghin, with contributions from Amit Raut. Overview MedusaLocker is a ransomware family that has been observed being deployed since its discovery in 2019. Since its introduction to the threat landscape, there have been several variants observed. However, most of
Threat Source newsletter for April 16, 2020
Newsletter compiled by Jon Munshaw. Welcome to this week’s Threat Source newsletter — the perfect place to get caught up on all things Talos from the past week. It’s what — week 5 of this quarantine in the U.S.? Week 6? We’ve lost count. And so did the Beers with Talos guys. B
Threat Source newsletter for April 9, 2020
Newsletter compiled by Jon Munshaw. Welcome to this week’s Threat Source newsletter — the perfect place to get caught up on all things Talos from the past week. Nearly all devices have some sort of fingerprint scanner now, used to log users in. But these scanners prevent their
Threat Source newsletter (Jan. 16, 2019)
Newsletter compiled by Jon Munshaw. Welcome to this week’s Threat Source newsletter — the perfect place to get caught up on all things Talos from the past week. This wasn’t your average Patch Tuesday. Microsoft’s monthly security update was notable for a few reasons. For start
2019: The year in malware
February * Attackers use a malicious PowerPoint presentation to target members of the Tibetan government in the hopes of infecting them with ExileRAT. March * Talos discovers a new point-of-sale malware for sale online called “GlitchPOS” that is easy enough to use that any
Incident Response lessons from recent Maze ransomware attacks
By JJ Cummings and Dave Liebenberg This year, we have been flooded with reports of targeted ransomware attacks. Whether it's a city, hospital, large- or medium-sized enterprise — they are all being targeted. These attacks can result in significant damage, cost, and have many
Hunting for LoLBins
By Vanja Svajcer. Introduction Attackers' trends tend to come and go. But one popular technique we're seeing at this time is the use of living-off-the-land binaries — or "LoLBins". LoLBins are used by different actors combined with fileless malware and legiti
How adversaries use politics for compromise
By Nick Biasini and Edmund Brumaghin. Executive Summary With the U.S. presidential primaries just around the corner, even malware authors can't help but get behind the frenzy. Cisco Talos recently discovered several malware distribution campaigns where the adversaries were
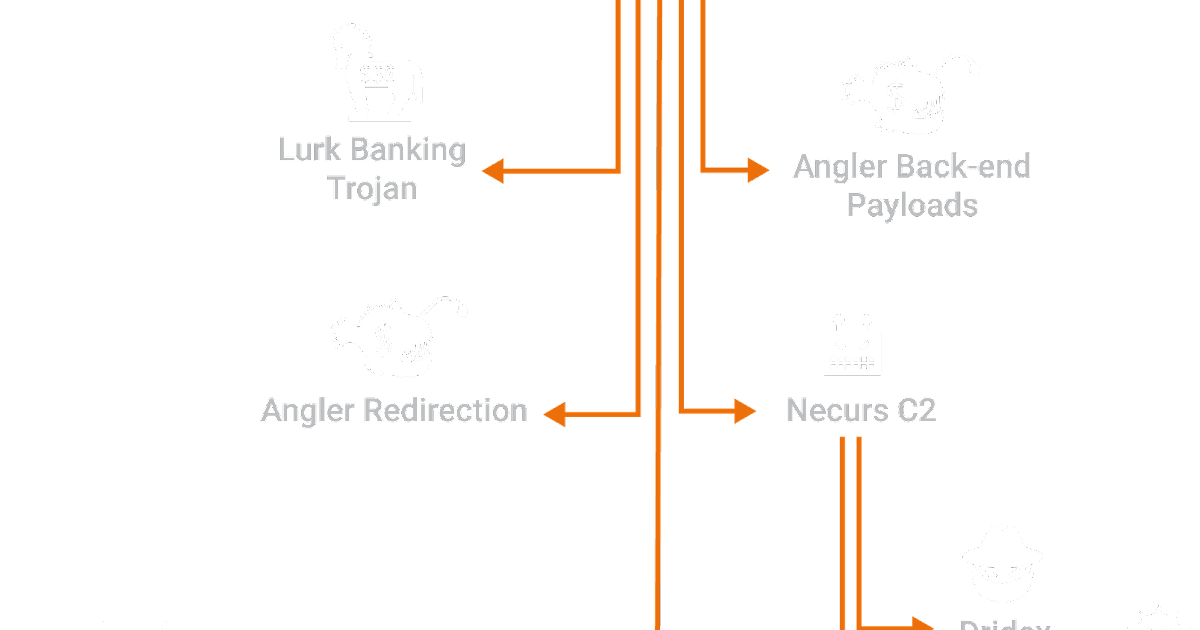
C2 With It All: From Ransomware To Carding
By Warren Mercer, Paul Rascagneres and Vitor Ventura. Summary Cisco Talos recently discovered a new server hosting a large stockpile of malicious files. Our analysis of these files shows that these attackers were able to obtain a deep level of access to victims' infrastruc
What you — and your company — should know about cyber insurance
By Jon Munshaw and Joe Marshall. It’s no longer a question of “if” any given company or organization is going to be hit with a cyber attack — it’s when. And when that attack comes, who is willing to take on that risk? For some groups, it may be that they feel they are fully pre
Should governments pay extortion payments after a ransomware attack?
"The risk must be judged to see if the cost is worth the attempt to get that data back or if these resources can do it within a reasonable timeframe. There are no guarantees in either direction."
The sights and sounds from the Talos Threat Research Summit
Cyber Security Week in Review (March 28)
Ransomware or Wiper? LockerGoga Straddles the Line
Executive Summary Ransomware attacks have been in the news with increased frequency over the past few years. This type of malware can be extremely disruptive and even cause operational impacts in critical systems that may be infected. LockerGoga is yet another example of this sor
Files Cannot Be Decrypted? Challenge Accepted. Talos Releases ThanatosDecryptor
This blog post was authored by Edmund Brumaghin, Earl Carter and Andrew Williams. Executive summary Cisco Talos has analyzed Thanatos, a ransomware variant that is being distributed via multiple malware campaigns that have been conducted over the past few months. As a result of
Gandcrab Ransomware Walks its Way onto Compromised Sites
This blog post authored by Nick Biasini with contributions from Nick Lister and Christopher Marczewski. Despite the recent decline in the prevalence of ransomware in the threat landscape, Cisco Talos has been monitoring the now widely distributed ransomware called Gandcrab. Gand
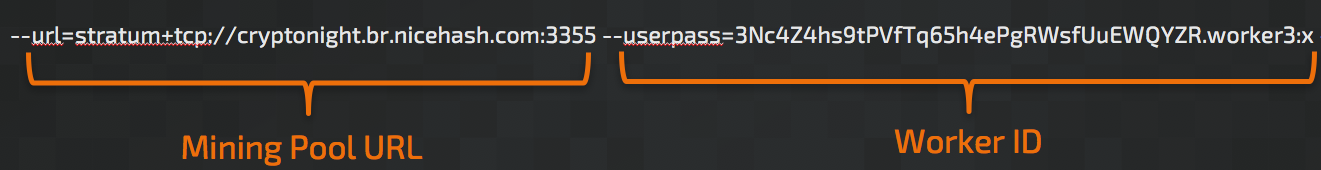
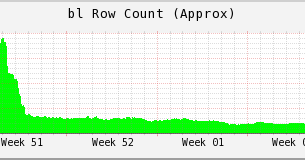
Ransom Where? Malicious Cryptocurrency Miners Takeover, Generating Millions
his post was authored by Nick Biasini, Edmund Brumaghin, Warren Mercer and Josh Reynolds with contributions from Azim Khodijbaev and David Liebenberg. Executive Summary The threat landscape is constantly changing; over the last few years malware threat vectors, methods and pay
SamSam - The Evolution Continues Netting Over $325,000 in 4 Weeks
This post was written by Vitor Ventura Introduction Talos has been working in conjunction with Cisco IR Services on what we believe to be a new variant of the SamSam ransomware. This ransomware has been observed across multiple industries including Government, Healthcare and
Threat Spotlight: Follow the Bad Rabbit
Note: This blog post discusses active research by Talos into a new threat. This information should be considered preliminary and will be updated as research continues. Update 2017-10-26 16:10 EDT: added additional information regarding the links between Nyetya and BadRabbit Upd
Back to Basics: Worm Defense in the Ransomware Age
This post was authored by Edmund Brumaghin "Those who cannot remember the past are condemned to repeat it." - George Santayana The Prequel In March 2017, Microsoft released a security update for various versions of Windows, which addressed a remote code execution vu
Taking the FIRST look at Crypt0l0cker
This post is authored by Matthew Molyett. Executive Summary In March, Talos reported on the details of Crypt0l0cker based on an extensive analysis I carried out on the sample binaries. Binaries -- plural -- because, as noted in the original blog, the Crypt0l0cker payload levera
The MeDoc Connection
Summary The Nyetya attack was a destructive ransomware variant that affected many organizations inside of Ukraine and multinational corporations with operations in Ukraine. In cooperation with Cisco Advanced Services Incident Response, Talos identified several key aspects of the
New Ransomware Variant "Nyetya" Compromises Systems Worldwide
Note: This blog post discusses active research by Talos into a new threat. This information should be considered preliminary and will be updated as research continues. Update 2017-07-06 12:30 EDT: Updated to explain the modified DoublePulsar backdoor. Since the SamSam attacks
Player 1 Limps Back Into the Ring - Hello again, Locky!
This post was authored by Alex Chiu, Warren Mercer, and Jaeson Schultz. Sean Baird and Matthew Molyettcontributed to this post. Back in May, the Necurs spam botnet jettisoned Locky ransomware in favor of the new Jaff ransomware variant. However, earlier this month Kaspersky dis
Player 3 Has Entered the Game: Say Hello to 'WannaCry'
By Martin Lee, Warren Mercer, Paul Rascagneres, and Craig Williams. Executive Summary A major ransomware attack has affected many organizations across the world reportedly including Telefonica in Spain, the National Health Service in the UK, and FedEx in the US. The malware re
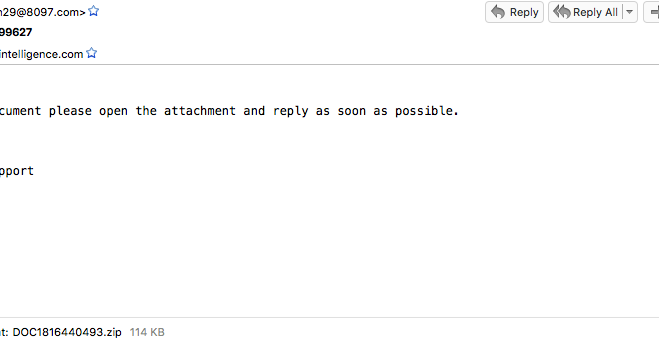
Jaff Ransomware: Player 2 Has Entered The Game
This post was written by Nick Biasini, Edmund Brumaghin and Warren Mercer with contributions from Colin Grady Summary Talos is constantly monitoring the email threat landscape and tracking both new threats as well as changes to existing threats. We recently observed several la
Crypt0l0cker (TorrentLocker): Old Dog, New Tricks
Without Necurs, Locky Struggles
This post authored by Nick Biasini with contributions from Jaeson Schultz Locky has been a devastating force for the last year in the spam and ransomware landscape. The Locky variant of ransomware has been responsible for huge amounts of spam messages being sent on a daily basis
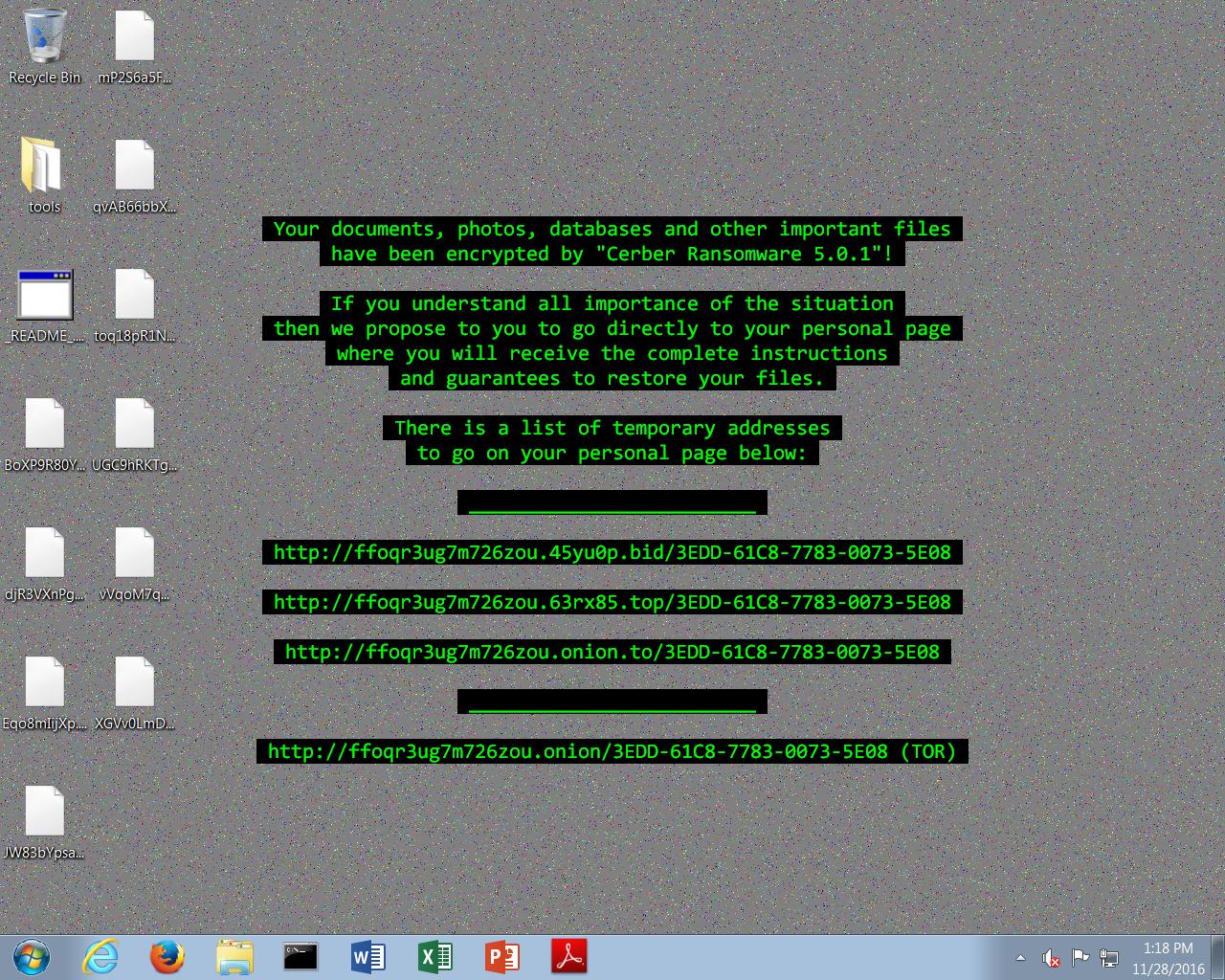
Cerber Spam: Tor All the Things!
This post authored by Nick Biasini and Edmund Brumaghin with contributions from Sean Baird and Andrew Windsor. Executive Summary Talos is continuously analyzing email based malware always looking at how adversaries change and the new techniques that are being added on an almo
Pumpkin Spiced Locky
This post was authored by Warren Mercer & Edmund Brumaghin Summary We had .locky, we had .odin and then we had .zepto but today we hit rock bottom and we now have Locky using .shit as their encrypted file extension. In today's latest wave of spam, Talos has observed
MBRFilter - Can't Touch This!
Update: 10/20/2016 - MBRFilter has been intentionally made difficult to remove to prevent malware from simply disabling or removing this protection during the infection process. Test thoroughly before deploying within production environments. Summary Ransomware has become incr
LockyDump - All Your Configs Are Belong To Us
This post was authored by Warren Mercer and Matthew Molyett Summary Locky has continued to evolve since its inception in February 2016. This has made it difficult to track at times due to changes in the way in which it's distributed as well as various characteristics of the
Ransomware: Because OpSec is Hard?
This blog was authored by Edmund Brumaghin and Warren Mercer Summary Talos recently published research regarding a new variant of destructive ransomware, which we dubbed Ranscam. During further analysis of Ranscam samples, we discovered several indicators of compromise (IOCs
When Paying Out Doesn't Pay Off
This blog post was authored by Edmund Brumaghin and Warren Mercer Summary Talos recently observed a new ransomware variant targeting users. This ransomware shows that new threat actors are continuing to enter the ransomware market at a rapid pace due to the lucrative nature of
Connecting the Dots Reveals Crimeware Shake-up
This Post Authored by Nick Biasini For a couple of weeks in June the threat landscape was changed. Several high profile threats fell off the scene, causing a shake-up that hadn't been seen before. For a period of three weeks the internet was safer, if only for a short time.
Gotta be SWIFT for this Spam Campaign!
This blog post was authored by Warren Mercer Summary Talos have observed a large uptick in the Zepto ransomware and have identified a method of distribution for the Zepto ransomware, Spam Email. Locky/Zepto continue to be well known ransomware variants and as such we will focus
Cryptolocker 4 White Paper Available: The Evolution Continues
We are pleased to announce the availability of the Cryptolocker 4 white paper. Over the past year, Talos has devoted a significant amount of time to better understanding how ransomware operates, its relation to other malware, and its economic impact. This research has proven valu
Widespread JBoss Backdoors a Major Threat
Recently a large scale ransomware campaign delivering Samsam changed the threat landscape for ransomware delivery. Targeting vulnerabilities in servers to spread ransomware is a new dimension to an already prolific threat. Due to information provided from our Cisco IR Services Te
TeslaCrypt 3.0.1 - Tales From The Crypt(o)!
This post is authored by Andrea Allievi and Holger Unterbrink Executive Summary Ransomware is malicious software that is designed to hold users' files (such as photos, documents, and music) for ransom by encrypting their contents and demanding the user pay a fee to decryp
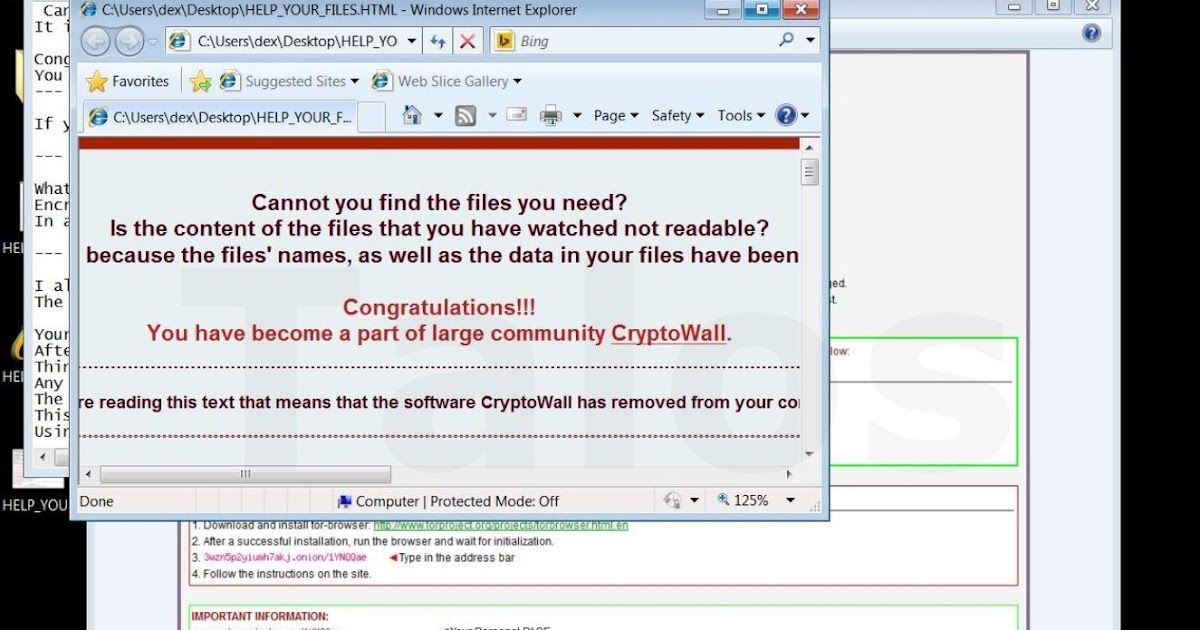
Threat Spotlight: CryptoWall 4 - The Evolution Continues
This post is authored byAndrea Allievi and Holger Unterbrink with contributions from Warren Mercer. Executive Summary Over the past year, Talos has devoted a significant amount of time to better understanding how ransomware operates, its relation to other malware, and its ec
Your Files Are Encrypted with a "Windows 10 Upgrade"
This post was authored by Nick Biasini with contributions from Craig Williams & Alex Chiu Update 8/1: To see a video of this threat in action click here Adversaries are always trying to take advantage of current events to lure users into executing their malicious payload. T
Cryptowall 3.0: Back to the Basics
This post was authored by Andrea Allievi & Earl Carter Ransomware continues to impact a large number of organizations and the malware continues to evolve. In January, we examined Cryptowall 2.0 and highlighted new features incorporated into the dropper and Cryptowall binary
Ransomware on Steroids: Cryptowall 2.0
This post was authored by Andrea Allievi and Earl Carter. Ransomware holds a user’s data hostage. The latest ransomware variants encrypt the user’s data, thus making it unusable until a ransom is paid to retrieve the decryption key. The latest Cryptowall 2.0, utilizes TOR to obf