IEC 60870-5-104 Protocol Detection Rules
Cisco Talos has released 33 Snort rules which are used to analyze/inspect IEC 60870-5-104 network traffic. These rules will help Industrial Control Systems/Supervisory Control and Data Acquisition (ICS/SCADA) asset owners to allow the identification of both normal and abnormal traffic in their environments.
In order for these rules to be effective they should be selectively turned on/enabled. SIDS 41053-41077 will detect various TypeIDs, if that specific TypeID is not in use then the rule should be enabled. SIDS 41078-41079 will detect IEC 104 traffic entering/exiting the ICS network. If 104 traffic is not supposed to enter/exit the ICS network then these sids should be enabled.
The rules will require both Snort $EXTERNAL_NET and $HOME_NET variables to be correctly configured for some of the rules to be effective. If a network does not have IEC 104 traffic these rules should not be enabled as they are only intended to detect IEC 104 traffic and will likely result in false positives (FPs) on non-IEC 104 traffic.
What is IEC 104? IEC 104 is a network protocol that is commonly used in ICS/SCADA environments. Various ICS/SCADA devices use IEC 104 to communicate with other ICS devices such as, but not limited to, Programmable Logic Controllers, Remote Terminal Unit, etc.
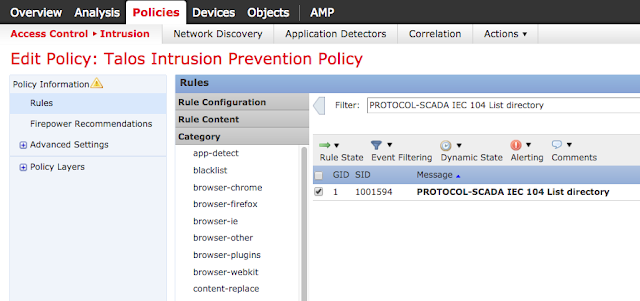
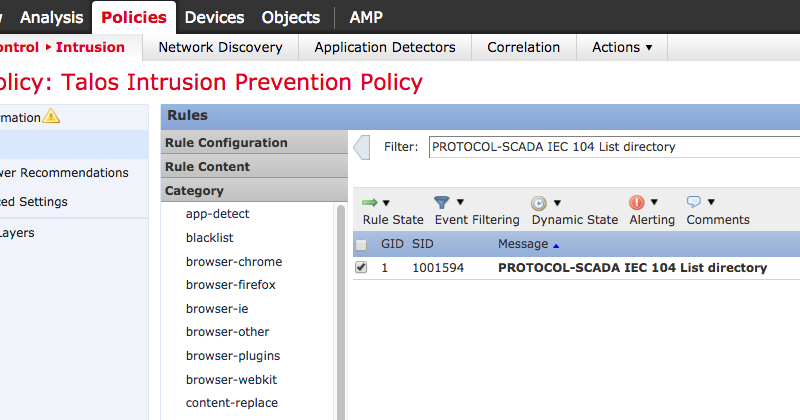
|
| FirePower 6.1 enabling a SID |
Read more on the snort blog here