- Cisco Talos recently discovered a new attack framework called "Manjusaka" being used in the wild that has the potential to become prevalent across the threat landscape. This framework is advertised as an imitation of the Cobalt Strike framework.
- The implants for the new malware family are written in the Rust language for Windows and Linux.
- A fully functional version of the command and control (C2), written in GoLang with a User Interface in Simplified Chinese, is freely available and can generate new implants with custom configurations with ease, increasing the likelihood of wider adoption of this framework by malicious actors.
- We recently discovered a campaign in the wild using lure documents themed around COVID-19 and the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. These maldocs ultimately led to the delivery of Cobalt Strike beacons on infected endpoints.
- We have observed the same threat actor using the Cobalt Strike beacon and implants from the Manjusaka framework.
Introduction
Cisco Talos has discovered a relatively new attack framework called "Manjusaka" (which can be translated to "cow flower" from the Simplified Chinese writing) by their authors, being used in the wild.
As defenders, it is important to keep track of offensive frameworks such as Cobalt Strike and Sliver so that enterprises can effectively defend against attacks employing these tools. Although we haven't observed widespread usage of this framework in the wild, it has the potential to be adopted by threat actors all over the world. This disclosure from Talos intends to provide early notification of the usage of Manjusaka. We also detail the framework's capabilities and the campaign that led to the discovery of this attack framework in the wild.
The research started with a malicious Microsoft Word document (maldoc) that contained a Cobalt Strike (CS) beacon. The lure on this document mentioned a COVID-19 outbreak in Golmud City, one of the largest cities in the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province. During the investigation, Cisco Talos found no direct link between the campaign and the framework developers, aside from the usage of the framework (which is freely available on GitHub). However, we could not find any data that could support victimology definition. This is justifiable considering there's a low number of victims, indicating the early stages of the campaign, further supported by the maldoc metadata that indicates it was created in the second half of June 2022.
While investigating the maldoc infection chain, we found an implant used to instrument Manjusaka infections, contacting the same IP address as the CS beacon. This implant is written in the Rust programming language and we found samples for Windows and Linux operating systems. The Windows implant included test samples, which had non-internet-routable IP addresses as command and control (C2). Talos also discovered the Manjusaka C2 executable — a fully functional C2 ELF binary written in GoLang with a User Interface in Simplified Chinese — on GitHub. While analyzing the C2, we generated implants by specifying our configurations. The developer advertises it has an adversary implant framework similar to Cobalt Strike or Sliver.
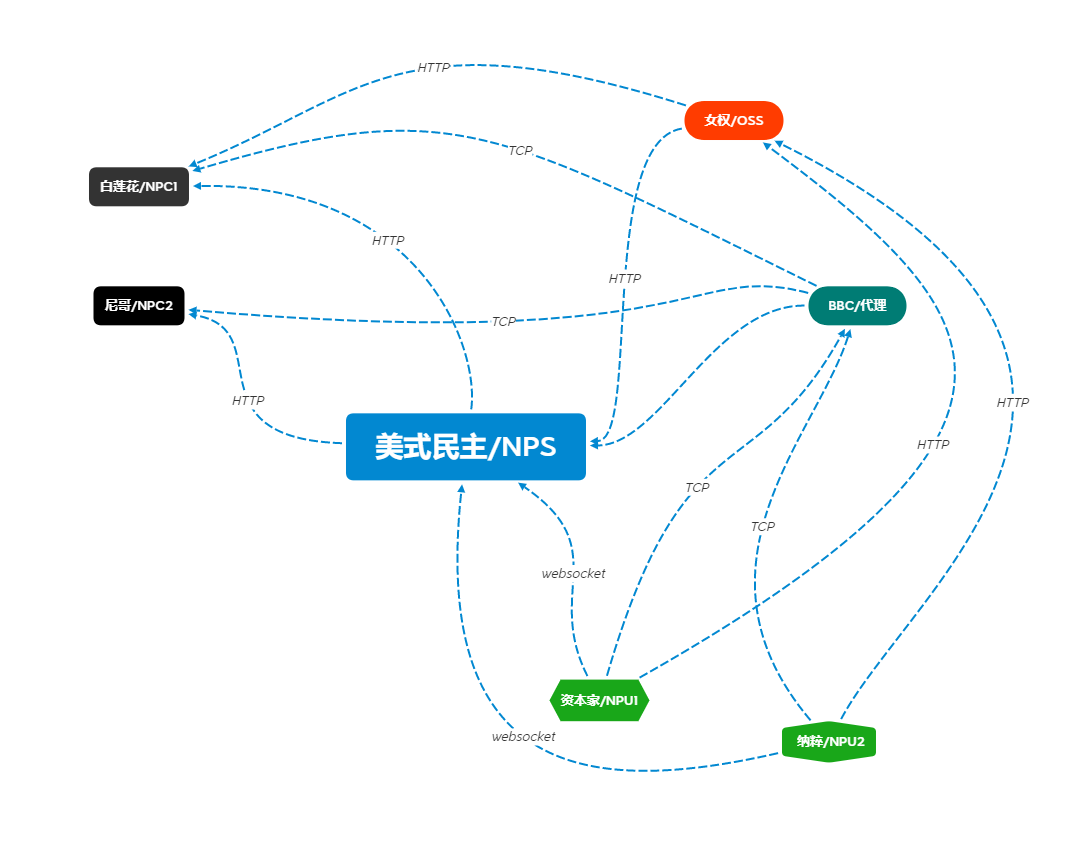
The developers have provided a design diagram of the Manjusaka framework illustrating the communications between the various components. A lot of these components haven't been implemented in the C2 binary available for free. Therefore, it is likely that either:
- The framework is actively under development with these capabilities coming soon OR
- The developer intends to or is already providing these capabilities via a service/tool to purchase - and the C2 available for free is just a demo copy for evaluation.
Manjusaka attack framework
The malware implant is a RAT family called "Manjusaka." The C2 is an ELF binary written in GoLang, while the implants are written in the Rust programming language, consisting of a variety of capabilities that can be used to control the infected endpoint, including executing arbitrary commands. We discovered EXE and ELF versions of the implant. Both sets of samples catering to these platforms consist of almost the same set of RAT functionalities and communication mechanisms.
Communications
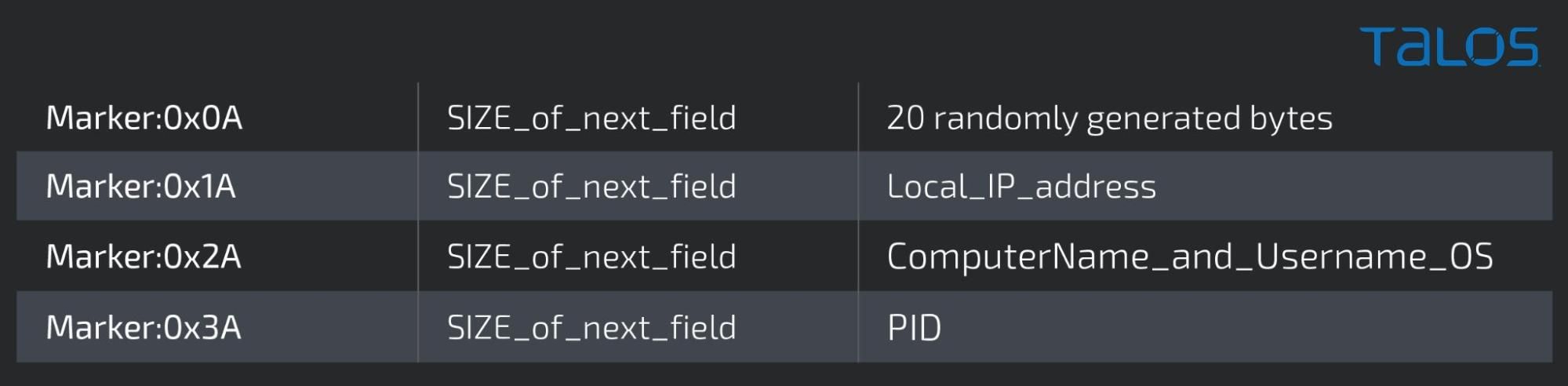
The sample makes HTTP requests to a fixed address http[:]//39[.]104[.]90[.]45/global/favicon.png that contains a fixed session cookie defined by the sample rather than by the server. The session cookie in the HTTP requests is base64 encoded and contains a compressed copy of binary data representing a combination of random bytes and system preliminary information used to fingerprint and register the infected endpoint with the C2. The image below shows the information used to generate such a session cookie.
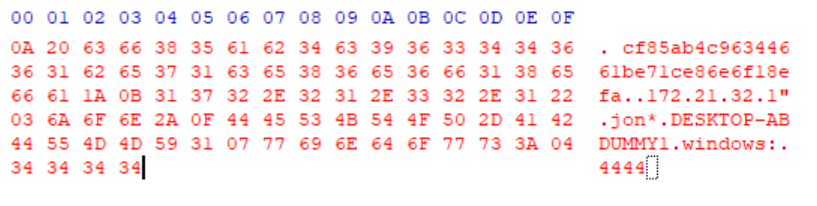
The information on the cookie is arranged as described in the table below before it is compressed and encoded into base64.
The communication follows a regular pattern of communication, the implant will make a request to an URL which in this case is '/global/favicon.png', as seen in the image below.

Even though the request is an HTTP GET, it sends two bytes that are 0x191a as data. The reply is always the same, consisting of five bytes 0x1a1a6e0429. This is the C2 standard reply, which does not correspond to any kind of action on the implant.
If the session cookie is not provided, the server will reply with a 302 code redirecting to http[:]//micsoft[.]com which is also redirected, this time with a 301, to http[:]//wwwmicsoft[.]com. At the time of publishing, the redirection seems like a trick to distract researchers. Talos could not find any direct correlation between the domains and the authors and/or operators of this C2.
Implant capabilities
The implant consists of a multitude of remote access trojan (RAT) capabilities that include some standard functionality and a dedicated file management module.

COMMANDS SERVICED BY THE RAT
The implant can perform the following functions on the infected endpoint based on the request and accompanying data received from the C2 server:
- Execute arbitrary commands: The implant can run arbitrary commands on the system using "cmd.exe /c".

- Get file information for a specified file: Creation and last write times, size, volume serial number and file index.
- Get information about the current network connections (TCP and UDP) established on the system, including Local network addresses, remote addresses and owning Process IDs (PIDs).
- Collect browser credentials: Specifically for Chromium-based browsers using the query: SELECT signon_realm, username_value, password_value FROM logins ; Browsers targeted: Google Chrome, Chrome Beta, Microsoft Edge, 360 (Qihoo), QQ Browser (Tencent), Opera, Brave and Vivaldi.
- Collect Wi-Fi SSID information, including passwords using the command: netsh wlan show profile <WIFI_NAME> key=clear

- Obtain Premiumsoft Navicat credentials: Navicat is a graphical database management utility that can connect to a variety of DB types such as MySQL, Mongo, Oracle, SQLite, PostgreSQL, etc. The implant enumerates through the installed software's registry keys for each configured DB server and obtains the values representing the Port, UserName, Password (Pwd).

- Take screenshots of the current desktop.
- Obtain comprehensive system information from the endpoint, including:
- System memory global information.
- Processor power information.
- Current and critical temperature readings from WMI using "SELECT * FROM MSAcpi_ThermalZoneTemperature"
- Information on the network interfaces connected to the system: Names
- Process and System times: User time, exit time, creation time, kernel time.
- Process module names.
- Disk and drive information: Volume serial number, name, root path name and disk free space.
- Network account names, local groups.
- Windows build and major version numbers.
- Activate the file management module to carry out file-related activities.
FILE MANAGEMENT CAPABILITIES
The file management capabilities of the implant include:
- File enumeration: List files in a specified location on disk. This is essentially the "ls" command.
- Create directories on the file system.
- Get and set the current working directory.
- Obtain the full path of a file.
- Delete files and remove directories on disk.
- Move files between two locations. Copy the file to a new location and delete the old copy.

- Read and write data to and from the file.
ELF variant
The ELF variant consists of pretty much the same set of functionalities as its Windows counterpart. However, two key functionalities missing in the ELF variant are the ability to collect credentials from Chromium-based browsers and harvest Wi-Fi login credentials.
Just like the Windows version, the ELF variant also collects a variety of system-specific information from the endpoint:
- Global system information such as page size, clock tick count, current time, hostname, version, release, machine ID, etc.
- System memory information from /proc/meminfo including cached memory size, free and total memory, swap memory sizes and Slab memory sizes.
- System uptime from /proc/uptime: System uptime and idle time of cores.
- OS identification information from /proc/os-release and lsb-release.
- Kernel activity information from /proc/stat.
- CPU information from /proc/cpuinfo and /sys/devices/system/cpu/cpu*/cpufreq/scaling_max_freq
- Temperature information from /sys/class/hwmon and /sys/class/thermal/thermal_zone*/temp
- Network interfaces information and statistics from /sys/class/net.
- Device mount and file system information. SCSI device information.
- Account information from /etc/passwd and group lists of users.
Both versions contain functionally equivalent file management modules that are used exclusively for managing files and directories on the infected system.

EXE vs ELF versions of the implant containing functionally equivalent file management modules.
Command and control server
During the course of our investigation, we discovered a copy of the C2 server binary for Manjusaka hosted on GitHub at hxxps://github[.]com/YDHCUI/manjusaka.
It can monitor and administer an infected endpoint and can generate corresponding payloads for Windows and Linux. The payloads generated are the Rust implants described earlier.
The C2 server and admin panel are primarily built on the Gin Web Framework which is used to administer and issue commands to the Rust-based implants/stagers.

After filling in the several options, the operator presses the "generate" button. This fires a GET request to the C2 following the format below.
http://<C2_IP_ADDRESS>:<Port>/agent?c=<C2_IP_ADDRESS>:<PORT>&t=<EXTENDED_URL_for_C2>&k=<ENCRYPTION_KEY>&w=true
The C2 server will then generate a configured Rust-based implant for the operator. The C2 uses packr to store the unconfigured Rust-based implant within the C2 binary consisting of a single packaged C2 binary that generates implants without any external dependencies.
The C2 will open a "box" — i.e., a virtual folder within the GoLang-based C2 binary — that consists of a dummy Rust implant at location "plugins/npc.exe". This executable is a pre-built version of the Rust implant that is then hot-patched by the C2 server based on the C2 information entered by the operator via the Web UI.
The skeleton Rust implant contains placeholders for the C2 IP/domain and the extended URLs in the form of repeated special characters "$" and "*" respectively, 0x21 repetitions.
E.g. The place holder for the C2 IP/Domain in the dummy implant is (hex):
24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24
which is then replaced by the C2 with an IP address such as:
33 39 2E 31 30 34 2E 39 30 2E 34 35 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24 24
The hot-patched binary is then served to the operator to download in response to the HTTP GET request from earlier.
THE CAMPAIGN: INFECTION CHAIN
We've also discovered a related campaign that consisted of a distribution of a maldoc to targets leading to the deployment of Cobalt Strike beacons on the infected systems.
The infection chain involves the use of a maldoc masquerading as a report and advisory on the COVID-19 pandemic in Golmud City, one of the largest cities in the Haixi Mongol and Tibetan Autonomous Prefecture, Qinghai Province — specifically citing a case of COVID-19 and the subsequent contact tracing of individuals.

Maldoc analysis
The maldoc contains a VBA macro that executes rundll32.exe and injects Metasploit shellcode (Stage 1) into the process to download and execute the next stage (Stage 2) in memory.
The Stage 1 shellcode reached out to 39[.]104[.]90[.]45/2WYz.

Stage 2 analysis
The next stage payload downloaded from the remote location is yet another shellcode that consists of:
- XOR-encoded executable: Cobalt Strike.
- Shellcode for decoding and reflectively loading the Cobalt Strike beacon into memory.

Stage 3: Cobalt Strike beacon
The Cobalt Strike beacon decoded by the previous stage is then executed from the beginning of the MZ file. The beacon can reflectively load itself into the memory of the current process.

The beacon's config is XOR encoded with the 0x4D single byte key. The configuration is:
BeaconType - HTTPS
Port - 443
SleepTime - 60000
MaxGetSize - 1048576
Jitter - 0
MaxDNS - Not Found
PublicKey -
b'0\x81\x9f0\r\x06\t*\x86H\x86\xf7\r\x01\x01\x01\x05\x00\x03\x81\x8d\x000\x81\x89\x02\x81\x81\x00\x95\xe2\xd1\xdd1N\x99\x13W%\xdd\x86\x1ep\xf7c\x12\x8f\xf3\xc3\x81\x93\xc7\n84\xa2^T\x13\x93\x8d6\xec\xb5V\x931\x01\xd2\x87o\xa1\xa8\x10\xea\x9f\x8c\xc2uY\x92\xa0z\x82d1m\x02\xa44\xdbc\xdf\xd7\x1d#2U\x1b\x158\xc8\x1dqX\x91\xe5\x9b@\x9a\xe2\xea\x0b\xd2\xcd\x9f\xae\xb1h\x08\x15|\xa3\x0cc\xde<\x17o|\x0c\x96\x878\xd2\xb4|\x86}\xa7H\x99\xd7\x8fc\xc8#\xe7W7\xec\x8fmx\xeb\xe3{\x02\x03\x01\x00\x01\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00'
C2Server - 39[.]104[.]90[.]45,/IE9CompatViewList.xml
UserAgent - Not Found
HttpPostUri - /submit.php
HttpGet_Metadata - Not Found
HttpPost_Metadata - Not Found
SpawnTo - b'\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00'
PipeName - Not Found
DNS_Idle - Not Found
DNS_Sleep - Not Found
SSH_Host - Not Found
SSH_Port - Not Found
SSH_Username - Not Found
SSH_Password_Plaintext - Not Found
SSH_Password_Pubkey - Not Found
HttpGet_Verb - GET
HttpPost_Verb - POST
HttpPostChunk - 0
Spawnto_x86 - %windir%\syswow64\rundll32.exe
Spawnto_x64 - %windir%\sysnative\rundll32.exe
CryptoScheme - 0
Proxy_Config - Not Found
Proxy_User - Not Found
Proxy_Password - Not Found
Proxy_Behavior - Use IE settings
Watermark - 999999
bStageCleanup - False
bCFGCaution - False
KillDate - 0
bProcInject_StartRWX - True
bProcInject_UseRWX - True
bProcInject_MinAllocSize - 0
ProcInject_PrependAppend_x86 - Empty
ProcInject_PrependAppend_x64 - Empty
ProcInject_Execute - CreateThread
SetThreadContext
CreateRemoteThread
RtlCreateUserThread
ProcInject_AllocationMethod - VirtualAllocEx
bUsesCookies - True
ATTRIBUTION
Before even thinking about the attribution, it's important to distinguish between the developer of the malware and the campaign operators. The C2 binary is fully functional (although limited in features), self contained and publicly available, which means that anyone could have downloaded it and used it in the campaign we discovered.
As such, we have decided to list the data points that could be interpreted as a possible indicator and encourage the community to perform the analysis and add other data points that might contribute to the attribution, either for the campaign or for the developers behind the framework.
For this campaign, there isn't much to lead to formal attribution with any confidence, besides the fact that the maldoc refers to a COVID-19 outbreak in Golmud City, offering a detailed timeline of the outbreak.
For the developer of Manjusaka, we have several indicators:
- The Rust-based implant does not use the standard crates.io library repository for the dependency resolving. Instead, it was manually configured by the developers to use the mirror located at ustc[.]edu[.]cn, which stands for the University Science and Technology of China.
- The C2 menus and options are all written in Simplified Chinese.
- Our OSINT suggests that the author of this framework is located in the GuangDong region of China.
CONCLUSION
The availability of the Manjusaka offensive framework is an indication of the popularity of widely available offensive technologies with both crimeware and APT operators. This new attack framework contains all the features that one would expect from an implant, however, it is written in the most modern and portable programming languages. The developer of the framework can easily integrate new target platforms like MacOSX or more exotic flavors of Linux as the ones running on embedded devices. The fact that the developer made a fully functional version of the C2 available increases the chances of wider adoption of this framework by malicious actors.
Organizations must be diligent against such easily available tools and frameworks that can be misused by a variety of threat actors. In-depth defense strategies based on a risk analysis approach can deliver the best results in the prevention. However, this should always be complemented by a good incident response plan which has been not only tested with tabletop exercises and reviewed and improved every time it's put to the test on real engagements.
COVERAGE
Ways our customers can detect and block this threat are listed below.

Cisco Secure Endpoint (formerly AMP for Endpoints) is ideally suited to prevent the execution of the malware detailed in this post. Try Secure Endpoint for free here.
Cisco Secure Web Appliance web scanning prevents access to malicious websites and detects malware used in these attacks.
Cisco Secure Email (formerly Cisco Email Security) can block malicious emails sent by threat actors as part of their campaign. You can try Secure Email for free here.
Cisco Secure Firewall (formerly Next-Generation Firewall and Firepower NGFW) appliances such as Threat Defense Virtual, Adaptive Security Appliance and Meraki MX can detect malicious activity associated with this threat.
Cisco Secure Malware Analytics (Threat Grid) identifies malicious binaries and builds protection into all Cisco Secure products.
Umbrella, Cisco's secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs and URLs, whether users are on or off the corporate network. Sign up for a free trial of Umbrella here.
Cisco Secure Web Appliance (formerly Web Security Appliance) automatically blocks potentially dangerous sites and tests suspicious sites before users access them.
Additional protections with context to your specific environment and threat data are available from the Firewall Management Center.
Cisco Duo provides multi-factor authentication for users to ensure only those authorized are accessing your network.
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
IOCS
IOCs for this research can also be found at our Github repository here.
Hashes
MALDOC AND CS BEACON SAMPLES
58a212f4c53185993a8667afa0091b1acf6ed5ca4ff8efa8ce7dae784c276927
8e7c4df8264d33e5dc9a9d739ae11a0ee6135f5a4a9e79c354121b69ea901ba6
54830a7c10e9f1f439b7650607659cdbc89d02088e1ab7dd3e2afb93f86d4915
RUST SAMPLES
8e9ecd282655f0afbdb6bd562832ae6db108166022eb43ede31c9d7aacbcc0d8
a8b8d237e71d4abe959aff4517863d9f570bba1646ec4e79209ec29dda64552f
3f3eb6fd0e844bc5dad38338b19b10851083d078feb2053ea3fe5e6651331bf2
0b03c0f3c137dacf8b093638b474f7e662f58fef37d82b835887aca2839f529b
C2 BINARIES
fb5835f42d5611804aaa044150a20b13dcf595d91314ebef8cf6810407d85c64
955e9bbcdf1cb230c5f079a08995f510a3b96224545e04c1b1f9889d57dd33c1
URLs
https[://]39[.]104[.]90[.]45/2WYz
http[://]39[.]104[.]90[.]45/2WYz
http[://]39[.]104[.]90[.]45/IE9CompatViewList.xml
http[://]39[.]104[.]90[.]45/submit.php
USER-AGENTS
Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Mozilla/5.0 (Windows NT 8.0; WOW64; rv:58.0) Gecko/20120102 Firefox/58
Mozilla/5.0 (Windows NT 8.0; WOW64; rv:40.0) Gecko
IPs
39[.]104[.]90[.]45