Today, Talos is publishing a glimpse into the most prevalent threats we've observed between April 28 and May 5. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org , or ClamAV.net .
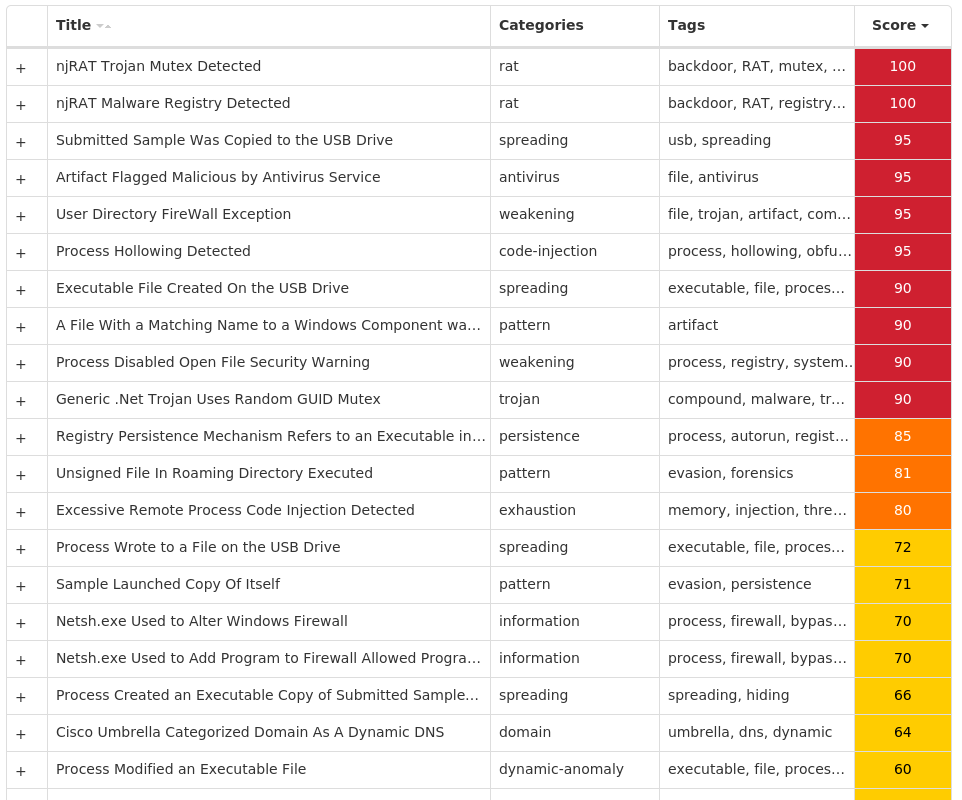
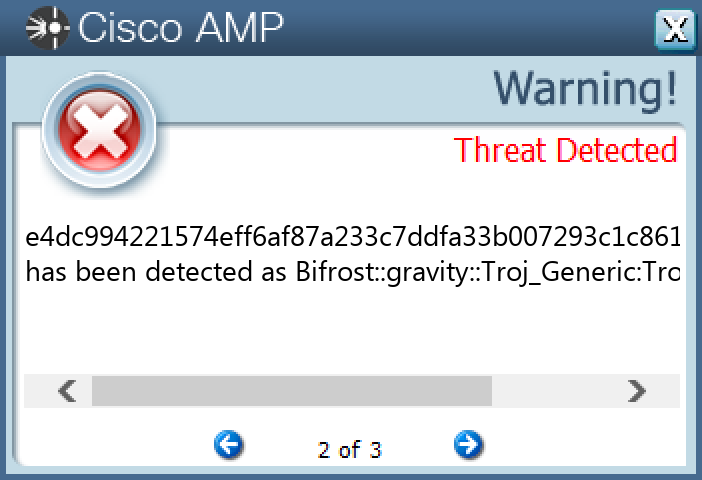
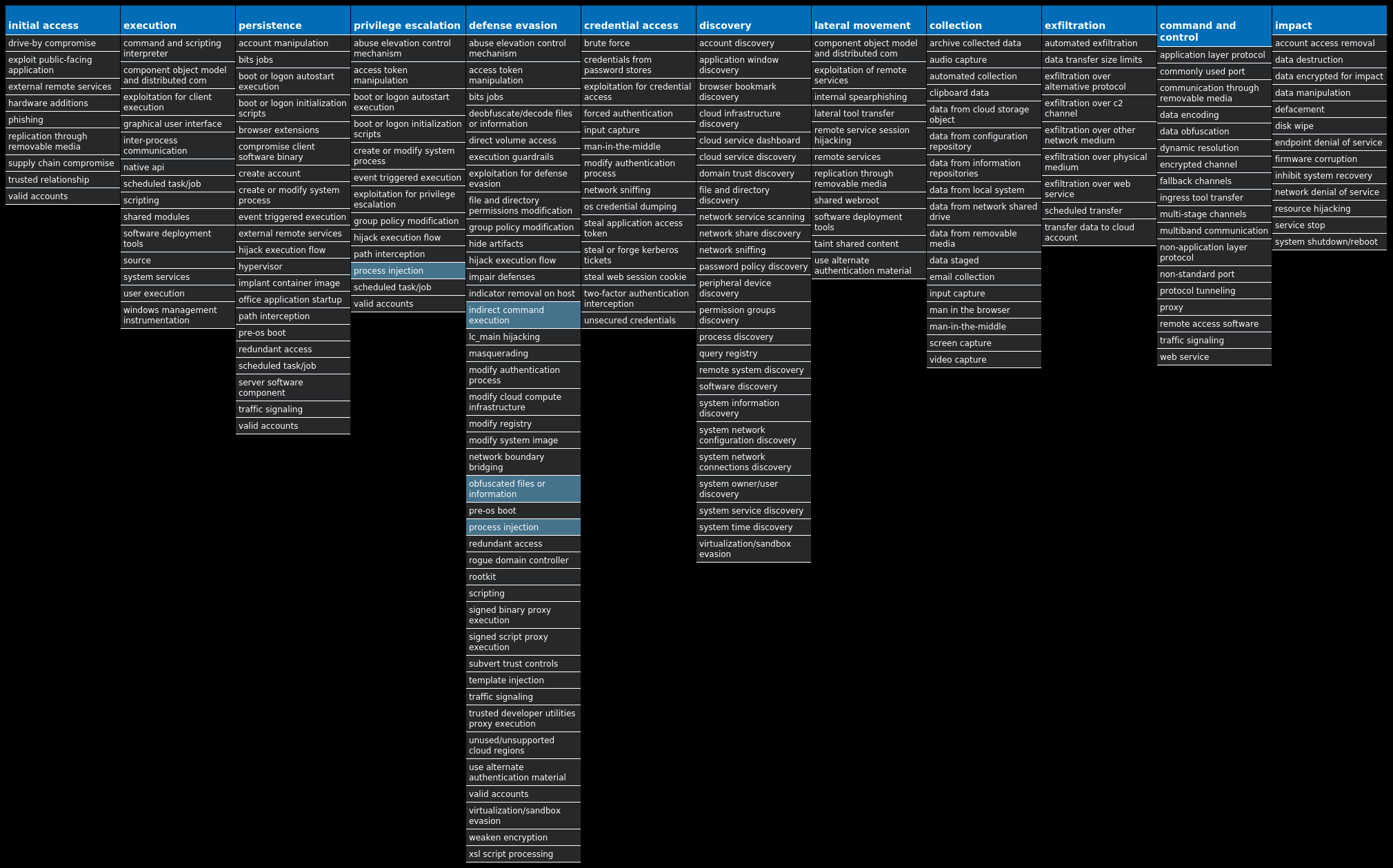
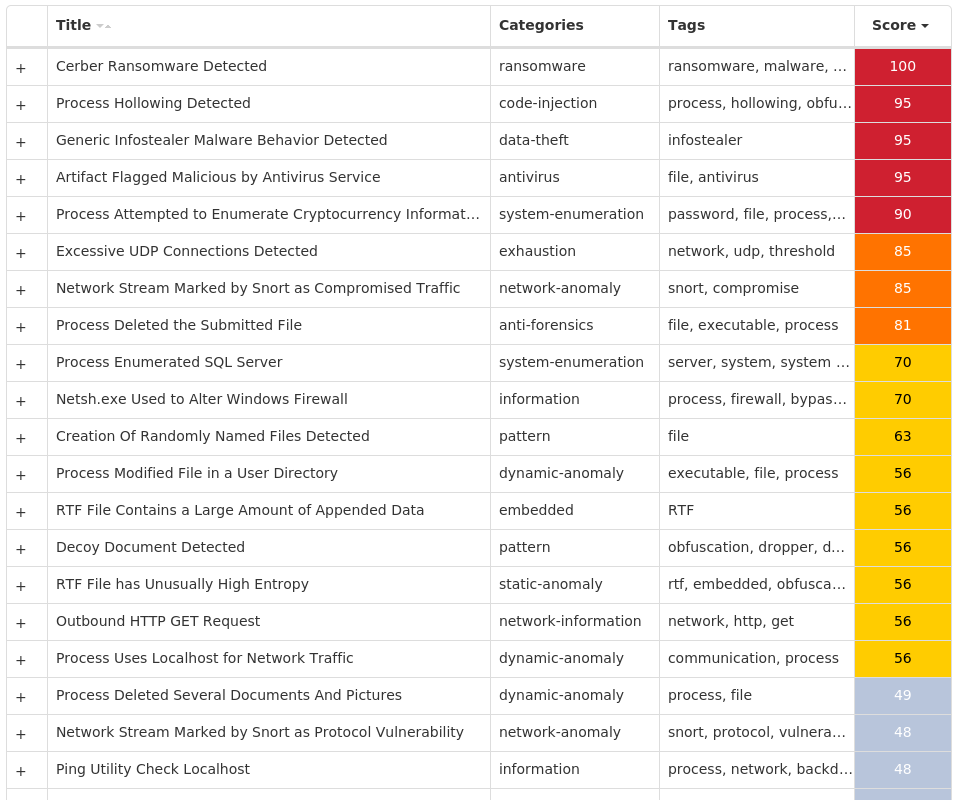
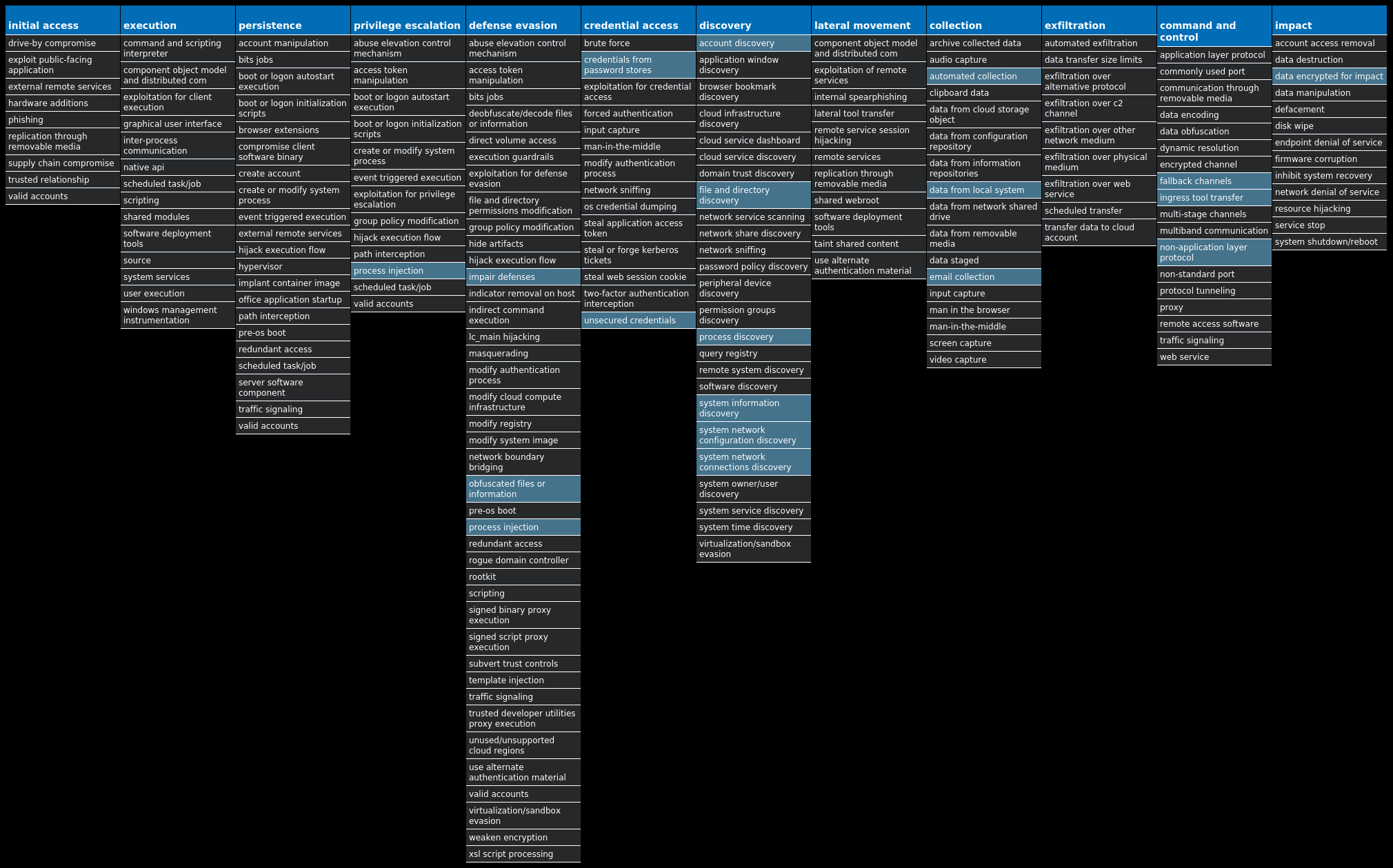
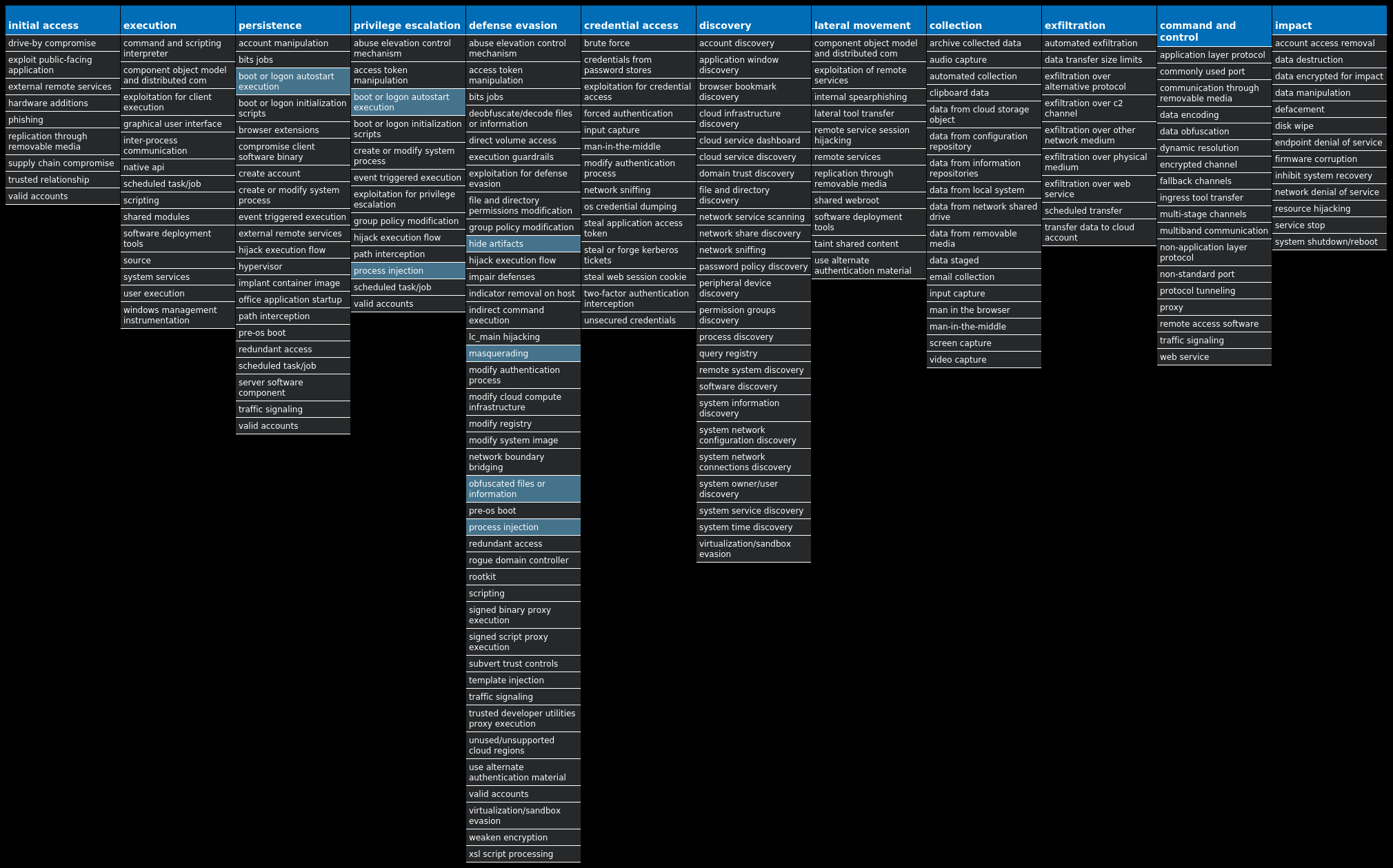
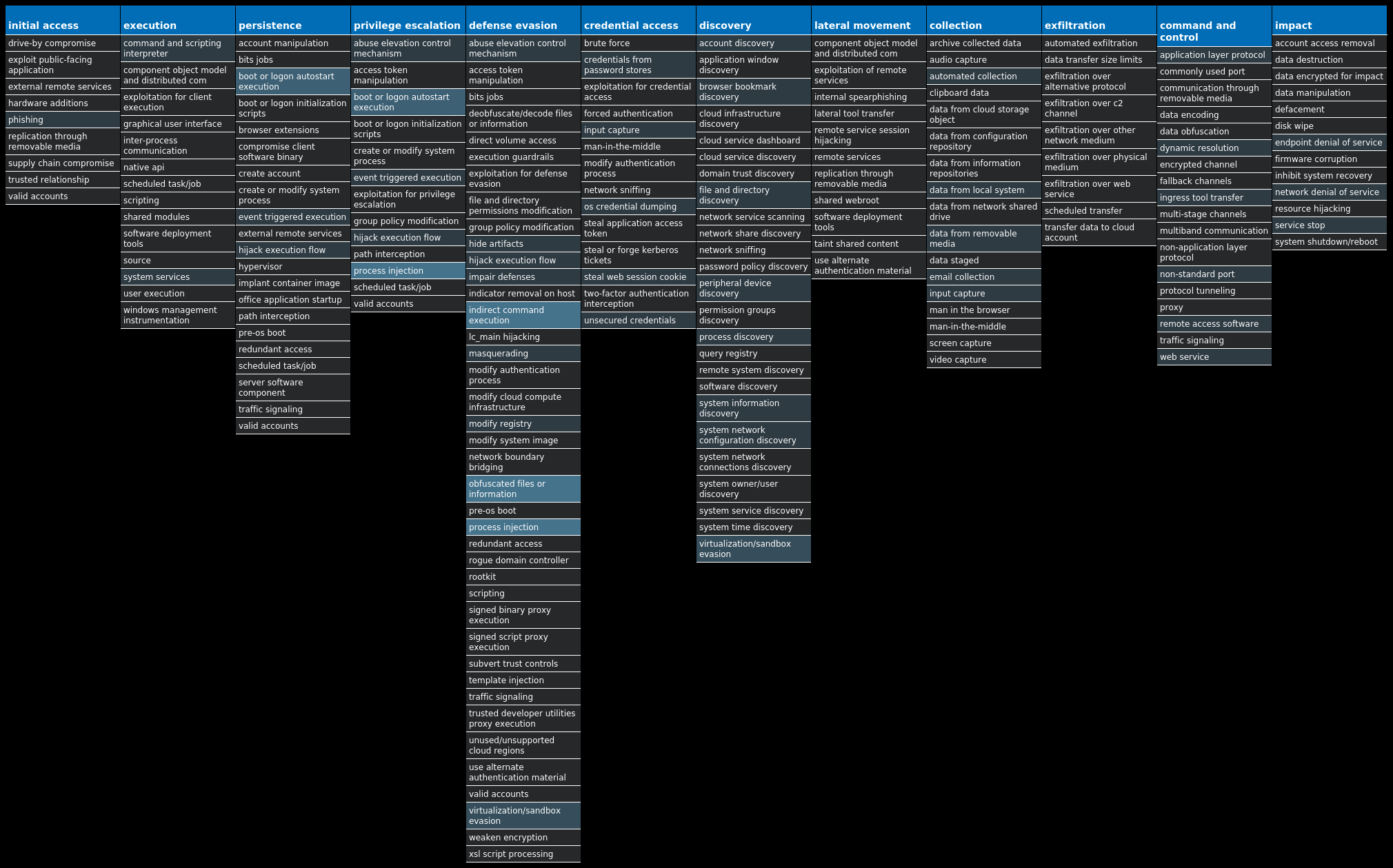
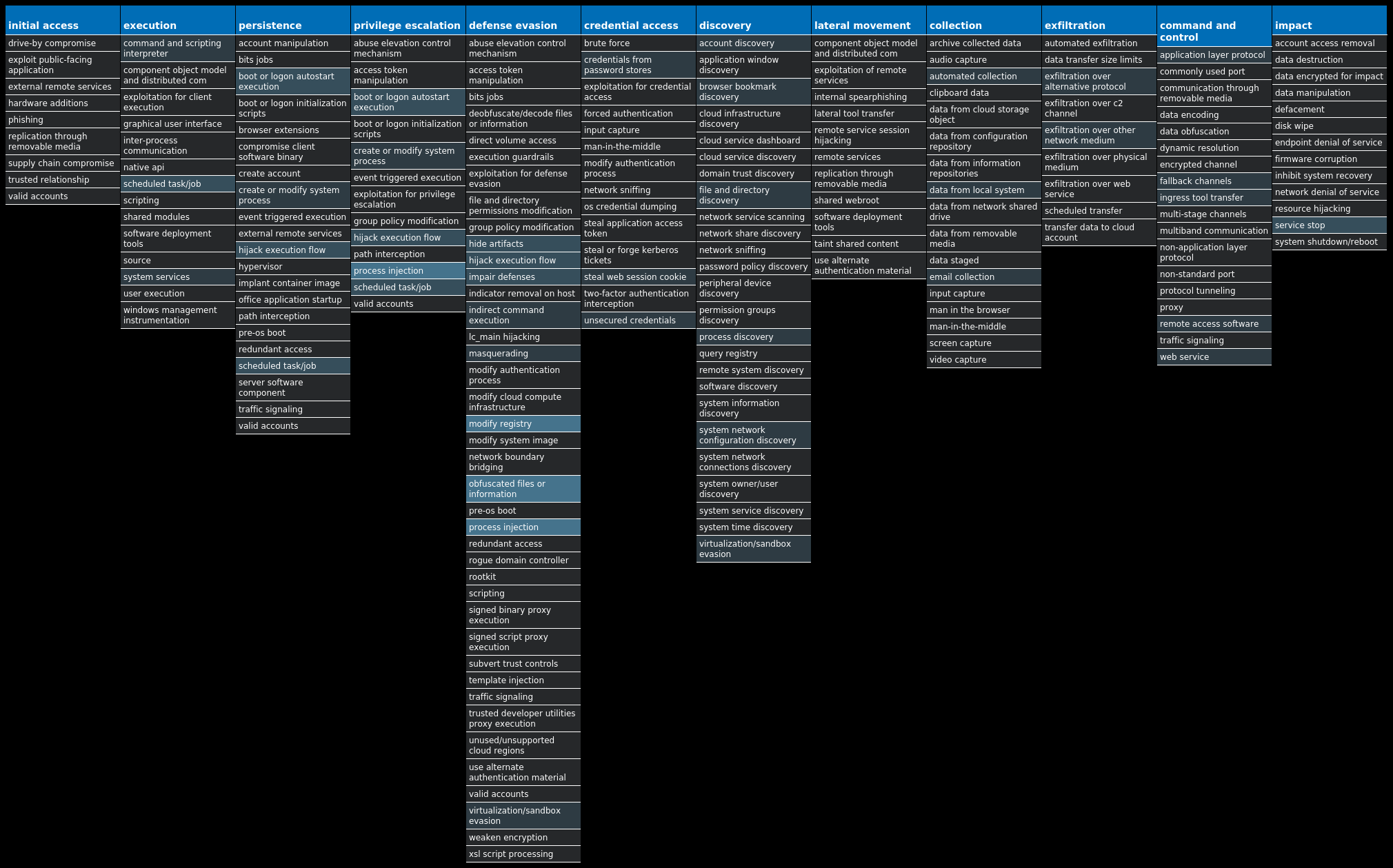
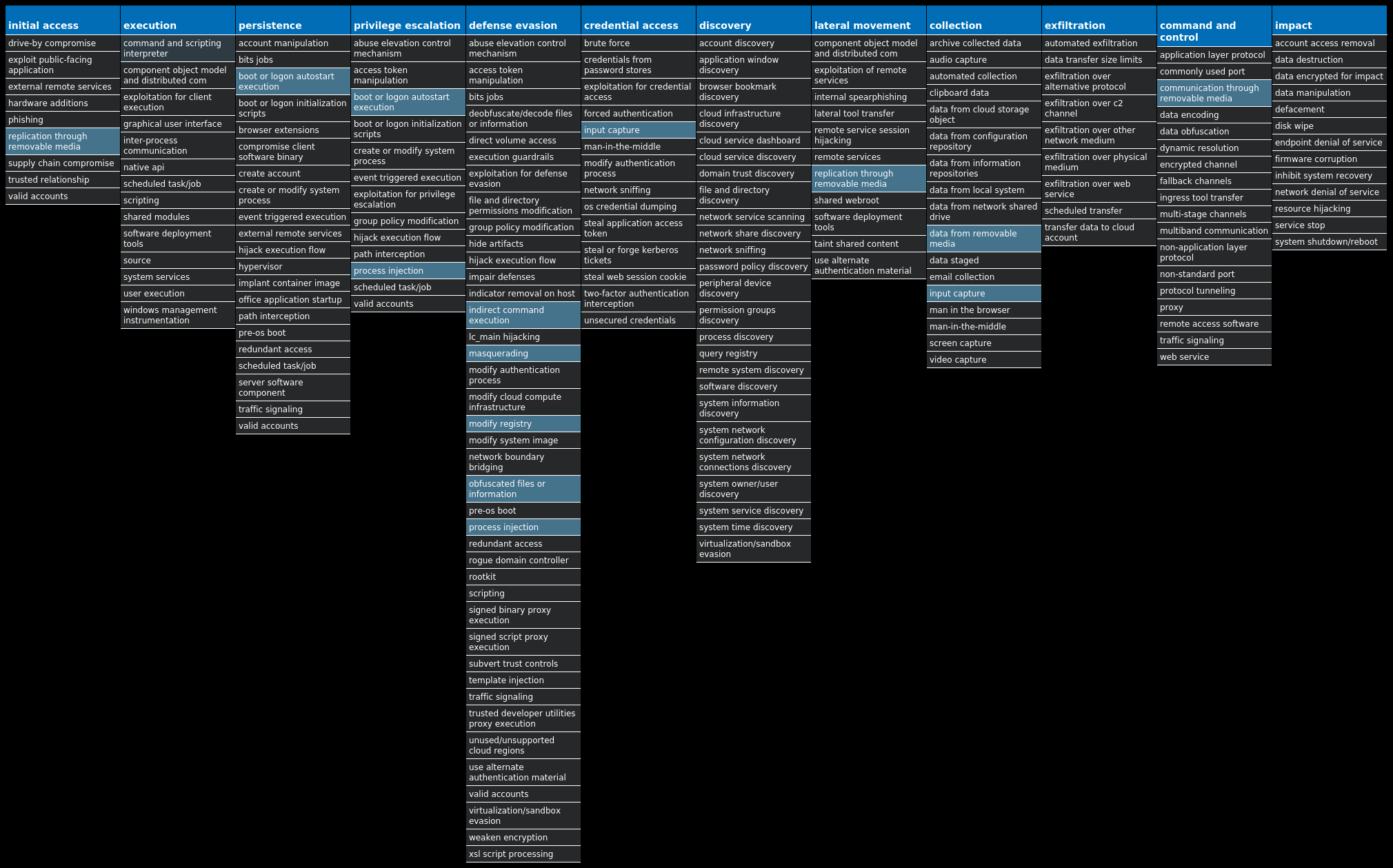
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found here that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name Type Description Win.Packed.njRAT-9999411-0 Packed njRAT, also known as Bladabindi, is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes and remotely turn on the victim's webcam and microphone. njRAT was developed by the Sparclyheason group. Some of the largest attacks using this malware date back to 2014. Win.Dropper.Bifrost-9999421-0 Dropper Bifrost is a backdoor with more than 10 variants. Bifrost uses the typical server, server builder and client backdoor program configuration to allow a remote attacker who uses the client to execute arbitrary code on the compromised machine. The malware contains standard RAT features including a file manager, screen capture utility, keylogging, video recording, microphone and camera monitoring, and a process manager. To mark its presence in the system, Bifrost uses a mutex that may be named "Bif1234" or "Tr0gBot." Win.Ransomware.Cerber-9999985-0 Ransomware Cerber is ransomware that encrypts documents, photos, databases and other important files. Historically, this malware would replace files with encrypted versions and add the file extension ".cerber," although in more recent campaigns, other file extensions are used. Win.Dropper.Kuluoz-9999994-0 Dropper Kuluoz, sometimes known as "Asprox," is a modular remote access trojan that is also known to download and execute follow-on malware, such as fake antivirus software. Kuluoz is often delivered via spam emails pretending to be shipment delivery notifications or flight booking confirmations. Win.Dropper.XtremeRAT-10000002-0 Dropper XtremeRAT is a remote access trojan active since 2010 that allows the attacker to eavesdrop on users and modify the running system. The source code for XtremeRAT, written in Delphi, was leaked online and has since been used by similar RATs. Win.Dropper.Tofsee-10000005-0 Dropper Tofsee is multi-purpose malware that features several modules to carry out various activities such as sending spam messages, conducting click fraud, mining cryptocurrency and more. Infected systems become part of the Tofsee spam botnet and send large volumes of spam messages to infect additional systems and increase the size of the botnet under the operator's control. Win.Trojan.Ramnit-10000021-1 Trojan Ramnit is a banking trojan that monitors web browser activity on an infected machine and collects login information from financial websites. It can also steal browser cookies and hide from popular anti-virus software.
Threat Breakdown Win.Packed.njRAT-9999411-0 Indicators of Compromise IOCs collected from dynamic analysis of 12 samples Registry Keys Occurrences <HKCU>\ENVIRONMENT Value Name: SEE_MASK_NOZONECHECKS 8 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: 23556fb1360f366337f97c924e76ead3 3 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: 23556fb1360f366337f97c924e76ead3 3 <HKCU>\SOFTWARE\23556FB1360F366337F97C924E76EAD33 <HKCU>\SOFTWARE\23556FB1360F366337F97C924E76EAD3 Value Name: US 3 <HKCU>\SOFTWARE\BA4C12BEE3027D94DA5C81DB2D196BFD Value Name: US 2 <HKCU>\SOFTWARE\BA4C12BEE3027D94DA5C81DB2D196BFD2 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: 5cd8f17f4086744065eb0992a09e05a2 1 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: 5cd8f17f4086744065eb0992a09e05a2 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: ba4c12bee3027d94da5c81db2d196bfd 1 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: ba4c12bee3027d94da5c81db2d196bfd 1 <HKCU>\SOFTWARE\5CD8F17F4086744065EB0992A09E05A2 Value Name: US 1 <HKCU>\SOFTWARE\5CD8F17F4086744065EB0992A09E05A21 <HKCU>\SOFTWARE\D8D7C4726DD94E5629F337DB2965C1AF1 <HKCU>\SOFTWARE\D8D7C4726DD94E5629F337DB2965C1AF Value Name: US 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: d8d7c4726dd94e5629f337db2965c1af 1 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: d8d7c4726dd94e5629f337db2965c1af 1 <HKCU>\SOFTWARE\0F170B3532C72267660723E333127B4D1 <HKCU>\SOFTWARE\0F170B3532C72267660723E333127B4D Value Name: US 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: 0f170b3532c72267660723e333127b4d 1 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: 0f170b3532c72267660723e333127b4d 1
Mutexes Occurrences <32 random hex characters>7
Domain Names contacted by malware. Does not indicate maliciousness Occurrences torrent-leech[.]servebeer[.]com3 test0102[.]zapto[.]org1 hamzahacker84[.]no-ip[.]biz1 de7kaaat[.]zapto[.]org1 bobica[.]no-ip[.]info1
Files and or directories created Occurrences %APPDATA%\svchost.exe3 %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\23556fb1360f366337f97c924e76ead3.exe3 %APPDATA%\svchost.exe.tmp3 E:\23556fb1360f366337f97c924e76ead3.exe3 \23556fb1360f366337f97c924e76ead3.exe3 %TEMP%\svchost.exe2 \5cd8f17f4086744065eb0992a09e05a2.exe1 \ba4c12bee3027d94da5c81db2d196bfd.exe1 \TEMP\.tmp1 %TEMP%\Trojan.exe1 %TEMP%\Trojan.exe.tmp1 %TEMP%\svchost.exe.tmp1 %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\ba4c12bee3027d94da5c81db2d196bfd.exe1 E:\5cd8f17f4086744065eb0992a09e05a2.exe1 %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\5cd8f17f4086744065eb0992a09e05a2.exe1 E:\ba4c12bee3027d94da5c81db2d196bfd.exe1 %TEMP%\hamza.exe1 %TEMP%\hamza.exe.tmp1 %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\d8d7c4726dd94e5629f337db2965c1af.exe1 %ProgramData%\isystem.exe1 %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\0f170b3532c72267660723e333127b4d.exe1
File Hashes 2167739d4cf736cf94b6f2156107cab8c312eac07b5a1eb26317564a9e5592b340ddedff2d7a63f99419ff69023258668d23217999e87134cf047038e59f88e449489f01e57b62d0f7a6ab2958589e3b888ae550bf32e4d6709df1c3364201e78ec9406c6818b968da592497a20a54a5d078686f652dfbde51d7ab510b6a58bda7b5eeea6104af0c07fa7af2cfab24670d43c4ce4aa3c113939f64b3a8c5f36eaf81e25f6aecf9306272e46a0267a3625b19f412e0499beaee617c6ae2489371b965b370bf5205a592a1756e2c02e3ccd974d4dc2d63dc6ad90135afc5c74a0ec1edf108bf51d26e6672d720ffab35de23cb2b14500f4c51372d31e2d789ce05c82097083a498aaec3bbdcbdecfc8205c92fc5eadc643d917d3a56a065e77767c89def53ae08d75d4164de3f3d37c5b01de1216125691fa127fb0f3e9e7591f1e69a60228101d497ddc68c11e919402fb228413c09d5d3af426451880907b95ce8cdabd65b244c74c37b21c8949fc5a80fec74aee34f159cd4b81d8cdeb7e293
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
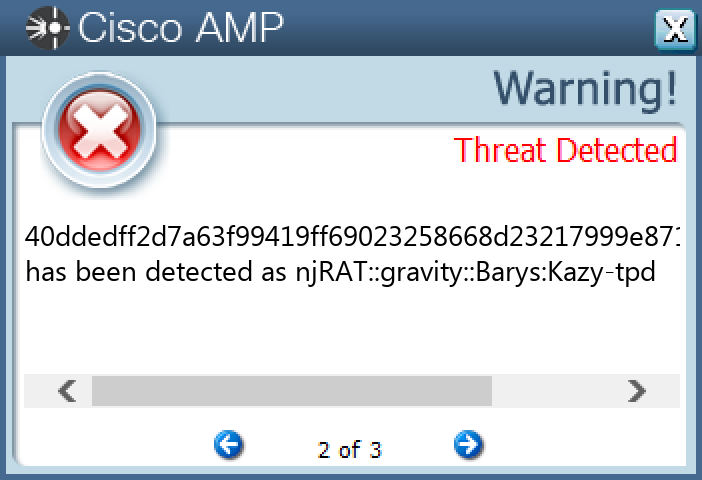
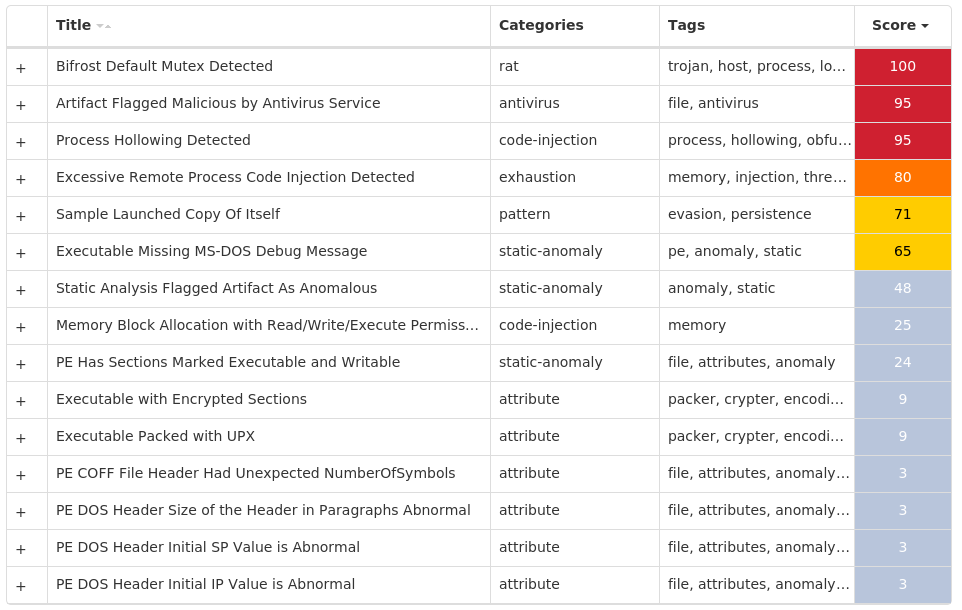
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.Bifrost-9999421-0 Indicators of Compromise IOCs collected from dynamic analysis of 23 samples Mutexes Occurrences Bif123418 <random, matching [a-zA-Z0-9]{5,9}>5
Files and or directories created Occurrences %APPDATA%\addons.dat2
File Hashes 0585e38214fea7ac0452aa4c91ce1866a7c11196c3ac433d5d2c8f0926b1d99305b60c3808ba135a4782eb1ee6bec09856f5677154ece35a180033d7cece493c0a2742d35fef3309868a747e585d542912fa8e6b82ff64b6df0ddec693b954e015b848b09c13701b9cf4d7ec1546abaf4843a8cd4f93219465082594109b5a152d3c4909441820d1de63983c97ad0964558f6024da7e3df9f96175d4403bf218317ad67576e5f51b4503b5a58790ae583d1298e2ad50c42f1d54f1607e74086539df2f083999781a16ab03af79cae3f5e7ecb33e616d073e3669114ecc5d644b3e434e528d5bdce10d103f262e13053037ba3f1d7d0cac058b697edbc5e7cf1f528e5c62e0e8e3af8fc991a7c0401202675b71267e58ed2053631064b7bd0196559fcab27f1bf9546475545d540aa891b901611247ede2b475c5093d31c859b370531690675458171a874b65e0446279933e41fceebb0510b43d0b910874b11172d732766780f90c15b04466e29dfae232a2080b6a53a8a7d0b375f13bb59ded7baa86e12a2c0cced0a644f2e0de4b34d3183e14e0ec0229decb7df669a1edf77f8ba1643800ef5c68f36fc5c7bd5f58e4bbf3488d1afe9457db3ff9f192f72c8ecaeb0d4ab61d5b194f532e91402ee67f56cfeeca7f14bafe310f6c4f17ca8ba25c4046bcb78ca6a41cf37262365cb6e630713d996962c5ed5624de6b70ce77b1b116c818bb99e56d2bf16797fc561848ddbe2ce1fddc83a4c3533cd3686084c98f65ea7dd4196e3c68318d4c51322bd5cfe6d4449dc2be633e0aab32509bdbe4dc994221574eff6af87a233c7ddfa33b007293c1c8619c22414b1ff051f719ea3ae31a4b957e8f7b34fe94599a2c34b0acc3dd6d8f01409fd68c90d50da2a4f81ab857124dd17d90252c5b291d0e23f8d2331109a5b25f4651e4ad955e10b3f90910b0082c3cb94d48d090d0910f14fc3e62d9c05781e136e99c28bc977436f9aa6fa501379435e45be9a9a626ee1205b7dfa193c36c5e8530d88ec6effa28
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
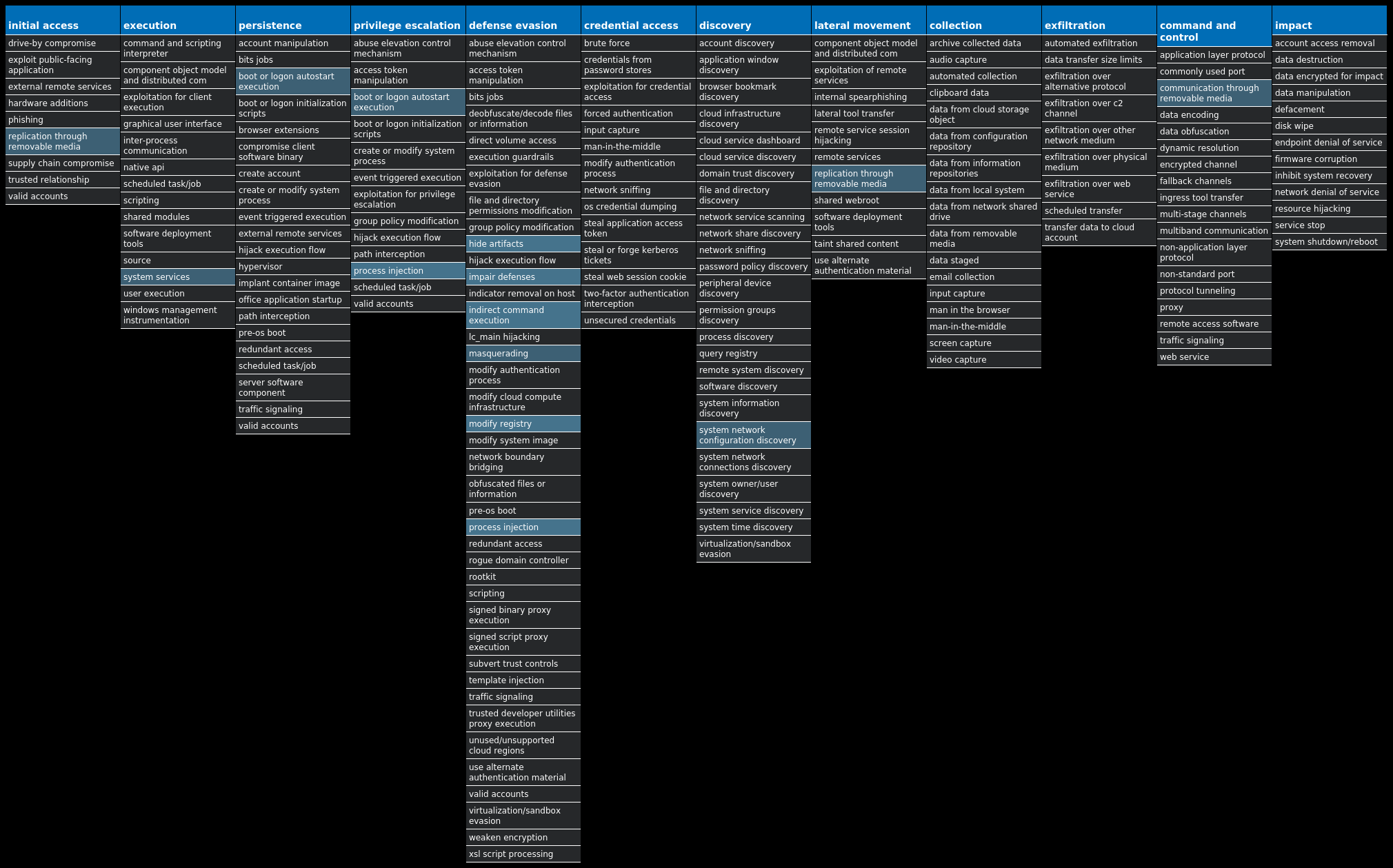
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Ransomware.Cerber-9999985-0 Indicators of Compromise IOCs collected from dynamic analysis of 54 samples Mutexes Occurrences shell.{381828AA-8B28-3374-1B67-35680555C5EF}54
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 94[.]21[.]172[.]0/2754 94[.]22[.]172[.]0/2754 94[.]23[.]172[.]0/2254 104[.]20[.]20[.]25121 172[.]67[.]2[.]8819 104[.]20[.]21[.]25114 178[.]128[.]255[.]17912 172[.]67[.]74[.]495 104[.]26[.]8[.]864 104[.]26[.]9[.]863
Domain Names contacted by malware. Does not indicate maliciousness Occurrences api[.]blockcypher[.]com54 hjhqmbxyinislkkt[.]1j9r76[.]top42 bitaps[.]com12 chain[.]so12 btc[.]blockr[.]io12
Files and or directories created Occurrences %TEMP%\d19ab98954 %TEMP%\d19ab989\4710.tmp54 %TEMP%\d19ab989\a35f.tmp54 %LOCALAPPDATA%\Microsoft\Office\Groove1\System\CSMIPC.dat54 <dir>\_READ_THIS_FILE_<random, matching [A-F0-9]{4,8}>_.hta54 <dir>\_READ_THIS_FILE_<random, matching [A-F0-9]{4,8}>_.txt54
File Hashes 03611a3d29c5bfc9c60478a389999d647f07d6a906057101deace299db87ed0c0c14954805c6df5ed7e3a7e6eff41d49607d6952208b1bd462f3dc416b7916640fd37123332104ce76d91a35e5393992b5cd81fd977afb97aecd5e27ad8c37b115155a362eb1e40c71af031bef0dd2dd92cf5fa7b549b365b576577decf5d01c18e1ec6e2bdde5242db231d2c07d951e53568017a18c21e445feb3b513e0a94626688f001590ab3312067b177c7b7abe9d1519dc6736aa846d5702a27eaabd33297ba2b3bc3a1cb638b8791df4e5e76a4ab55dcdea9063e9e851d41289625def2aae4f76bed26ed00582a82ee73cb7b58e9d54ca568047c3b7e1d7aaa32540a42c6b60e3d9593789b7bcd045d5ace99c90fd39de1485c3f4cb32d4cad84834562db8fc26bc17121b1724d72ad7abf2672710445a6fc35a3728c23f5d7dfc9c0c31f78896c577b0fd9f8de7323e3b37448f1b683b38fa338c1c10b08fab8a048932b7762b08c045e310f15f9f8fdc16cef87f1779505c922b9076b5644064163633f754ae9862b34b210b14a2b5bf1a966c136c6204e2af11cbbba91d11ccdb5d359f1f7442d25411e9e948fe57fddc19700af351a08252f64671d24b4bad0ae93743ee2c437b0458bcf3f0d605dd7aa9b5a6f7278463659028652c119cb90e3243b84a6ad0cd2ee1d40cc93a17785e7bc01e946e4176a98a74aa98a74e50c7304611109e19c031e3fff93c947cc23193e20dcc545b2837f01ab63c62b482a6c849d3e05ce3c566ab41fc5de938cbc02886b79cd62e310f5c1ab2a7ad1dd7b61451729b1d1902b3b9bc628f866f60895a84b01307964fdeb9ba7cef683d9eeec451fade9c1740e082ecd32c6971fe399863e8a386eb4bcbf32b3eaf2f8984583757033c8389b211d9e9726fb70bed63843ab99e1d214c5dcdc5dc9e76a53571ca5c814e00d32a00c46b071595af010a1ef3109ec025068449ece9886ded140a2e60507ad97df7c8e3eeda9733d926462a1def4944d8c764db869dbeb661221ce7664be3a91ac7ac0e54a5a07525a9aeddf62a94df72ebc07a6ec03e26eaef0aa06d585e98246c9469086f418ec6a7645a43e3de2fa360db95f23f9a71cd6d8c77
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
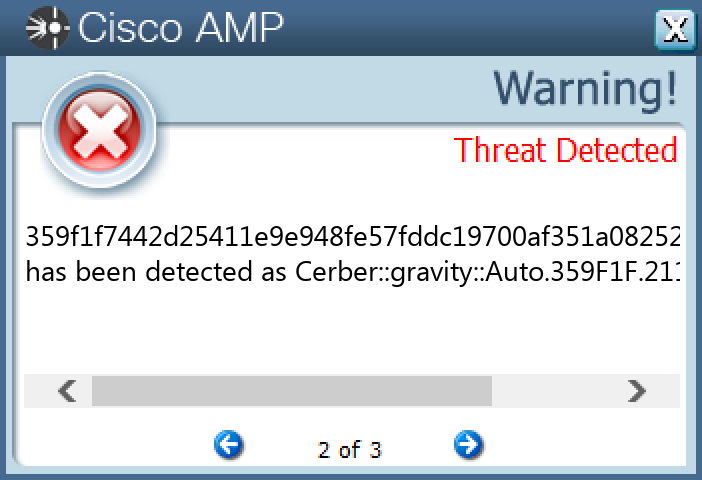
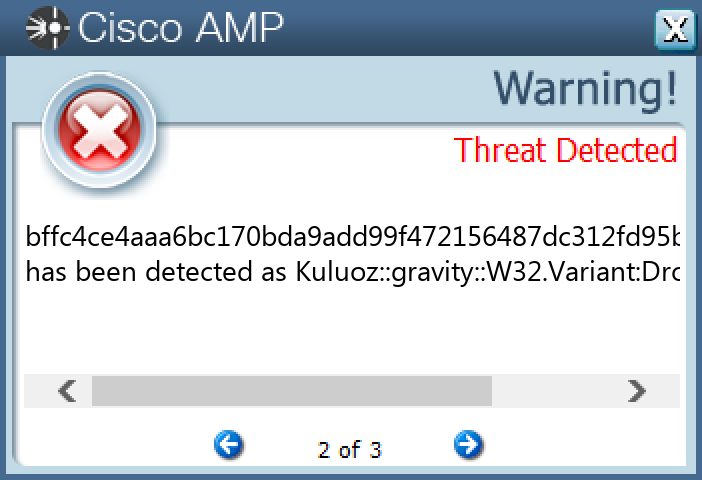
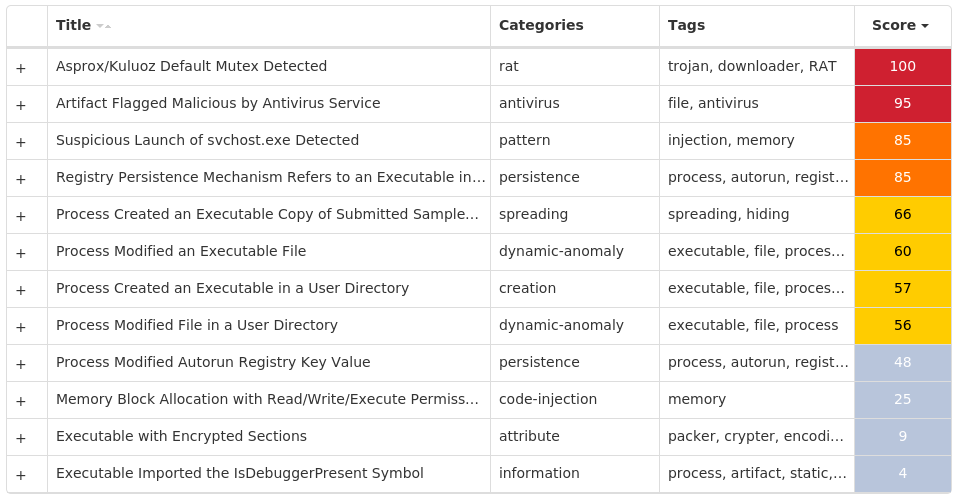
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.Kuluoz-9999994-0 Indicators of Compromise IOCs collected from dynamic analysis of 22 samples Registry Keys Occurrences <HKCU>\SOFTWARE\<random, matching '[a-zA-Z0-9]{5,9}'>22 <HKCU>\SOFTWARE\WAMXWQPD Value Name: smujtlwk 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: luvplgpk 1 <HKCU>\SOFTWARE\QPVIUNPR Value Name: frptnefc 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: rjkqqpxr 1 <HKCU>\SOFTWARE\EUMGPSEO Value Name: cbovpnfk 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: cnggsxff 1 <HKCU>\SOFTWARE\ETTNCOSJ Value Name: lwbgsdcv 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: ttaxvitj 1 <HKCU>\SOFTWARE\CTTQGKIS Value Name: cmxfrtnw 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: pbqsbklx 1 <HKCU>\SOFTWARE\NAXXBCNW Value Name: oafjkbjk 1 <HKCU>\SOFTWARE\CNEBDSXT Value Name: bchenplg 1 <HKCU>\SOFTWARE\CDEKCHEP Value Name: wwbdhrid 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: rrdssxrn 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: nsungxkd 1 <HKCU>\SOFTWARE\RTNNUWUL Value Name: wtmaaxmw 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: lwvjaujt 1 <HKCU>\SOFTWARE\CPHRRTRK Value Name: soxcrgal 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: dptacodg 1 <HKCU>\SOFTWARE\CDLCLVRJ Value Name: guiqcbwp 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: vniggsma 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: wpbtwsab 1 <HKCU>\SOFTWARE\LECNFNCL Value Name: sxofspsj 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: qxmseevb 1
Mutexes Occurrences 2GVWNQJz122
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 5[.]39[.]86[.]9717 77[.]237[.]121[.]1917 78[.]47[.]33[.]17115 162[.]216[.]112[.]21714 194[.]146[.]226[.]8113 187[.]95[.]41[.]19411 164[.]177[.]152[.]1108 190[.]124[.]250[.]296
Files and or directories created Occurrences %LOCALAPPDATA%\<random, matching '[a-z]{8}'>.exe22
File Hashes 00417d6eb1a336d0e1414544264bff6f924822e3da217cd61892f322c30e5f9d10c08a7e1cd4f6561f3996b871831d21c7c4671c9dc42176c8f560e8c515f8d219cff7bd4713b5d8103f19715c96e6878dcbb2634ba901a05719d2bd0fb2ff4b1c77cbe7e26592746c4f7b8e3995234ce89efab7a1f08f4c725935ee6ed469e11e55c11a9f3bd854166e1c6ef53a384fece89b8fc421047359a2b99fa049cf6e29e0a59f6d38ec701ca6aa122c6a54726d5b0ed5536d2f89abdecca3f1a2de2434a354c972b87640c6dc11e76be22c81da7ead7da852e64ac5d917df6c71faa6464d669aeb5c011158cf8faca6a674fdaaa7df444c91948837d3b8c75c8c9a34506602749b567b9884d91c7a728764d2500d3860c32ee315703148dc594e594c5a422203f58d9e0344c737cc1166aba480742ede8d3baf2903ae42c3a0279e43667b0dfd97f1a4b6f66681f49621a2ec69f5f72f0aaf7d210d8fa7fca40f0d7d66b435ae8f847ca30c42ff42ea504d099c04b017410b6770fb675973428c9e647ad944253149901bdadc966f740c6e56b7ce87ec2678d31bccb7b4622a3b0516924a3c1317e1f4cc772b9a0de3e95ec4f9f8070f407bd537c4e51574a6c159959f07d324155b0aa405671f8e56d8a36ccbc7a66842d175f379029c6480a84077aad3e3b8506fe64eaca3828050ce78be32582a621a79e869e253e924f2dca99eaca38b67e6d24e77fae537d82f49ffd344ef75bc4458d626b697ac0be4ebbab4ba905bf22b38e1f3869279bfef60f3998e0521c0b2f9e045adc9b517826f8dcfbaed3471b03a58c6e1a8eb071a7222c8b3cddc9e060b037b20f7688cab589428bffc4ce4aaa6bc170bda9add99f472156487dc312fd95bf6c78ed26e2c2309a3e53a65c88ac8a732e06305b6ac0fbb8fc9f6b1035f71e7191df440daa75099c1f2fa0559b22f7db6171a49318175f20e70052f9c4f747e79434c419c0fba0806
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
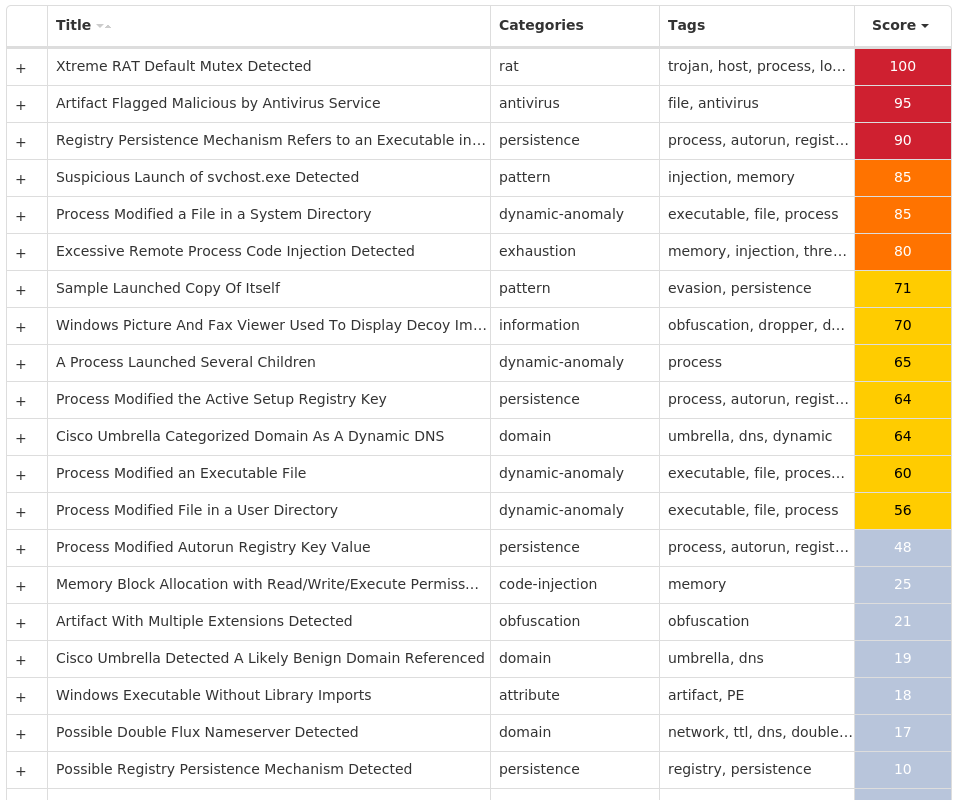
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.XtremeRAT-10000002-0 Indicators of Compromise IOCs collected from dynamic analysis of 81 samples Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN25 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN25 <HKCU>\SOFTWARE\<random, matching '[a-zA-Z0-9]{5,9}'>14 <HKCU>\SOFTWARE\<random, matching '[a-zA-Z0-9]{5,9}'> Value Name: NewIdentification 12 <HKCU>\SOFTWARE\<random, matching '[a-zA-Z0-9]{5,9}'> Value Name: FirstExecution 7 <HKCU>\SOFTWARE\REMOTE Value Name: NewGroup 6 <HKCU>\SOFTWARE\MICROSOFT\INTERNET EXPLORER\SEARCHSCOPES\{0633EE93-D776-472F-A0FF-E1416B8B2E3A} Value Name: FaviconPath 5 <HKCU>\SOFTWARE\MICROSOFT\INTERNET EXPLORER\SEARCHSCOPES\{0633EE93-D776-472F-A0FF-E1416B8B2E3A} Value Name: Deleted 5 <HKCU>\SOFTWARE\MICROSOFT\INTERNET EXPLORER\SEARCHSCOPES Value Name: DefaultScope 5 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXT\STATS\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}5 <HKCU>\SOFTWARE\DC3_FEXEC3 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWS Value Name: Load 3 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWS Value Name: Load 3 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{2J58XP0K-ERQO-J3F4-1E5X-JB44DFP82S24}3 <HKCU>\SOFTWARE\MASD3 <HKCU>\SOFTWARE\MASD Value Name: NewIdentification 3 <HKCU>\SOFTWARE\MASD Value Name: NewGroup 3 <HKCU>\SOFTWARE\INFECTED HACKING3 <HKCU>\SOFTWARE\INFECTED HACKING Value Name: NewIdentification 3 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE Value Name: EnableFirewall 2 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{5460C4DF-B266-909E-CB58-E32B79832EB2} Value Name: StubPath 2 <HKCU>\SOFTWARE\MICROSOFT\--((SPYNET))-- Value Name: InstalledServer 2 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{5460C4DF-B266-909E-CB58-E32B79832EB2}2 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{08B0E5JF-4FCB-11CF-AAA5-00401C6XX500}2 <HKCU>\SOFTWARE\MICROSOFT\--((SPYNET))--2
Mutexes Occurrences _x_X_BLOCKMOUSE_X_x_14 _x_X_PASSWORDLIST_X_x_14 _x_X_UPDATE_X_x_14 <random, matching '[A-Z0-9]{14}'>12 Administrator510 ***MUTEX***8 ***MUTEX***_PERSIST8 ***MUTEX***_SAIR8 <random, matching '[A-Z0-9]{14}'>_SAIR8 Administrator17 Administrator47 <random, matching [a-zA-Z0-9]{5,9}>7 UFR36 SPY_NET_RATMUTEX5 Global\<random guid>5 <random, matching [A-Z0-9]{10}>5 XTREMEUPDATE4 xXx_key_xXx3 --((SpyNet))--2 --((SpyNet))--CHECK2 --((SpyNet))--INJECT2 --((SpyNet))--UPDATE2 1G3W5JF701F082Administrator152 ((Mutex))1 XxXx1
*See JSON for more IOCs
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 104[.]127[.]184[.]495 23[.]7[.]178[.]1575 52[.]8[.]126[.]804 13[.]107[.]21[.]2001 217[.]69[.]139[.]1601 94[.]100[.]180[.]1601 198[.]23[.]57[.]81 66[.]220[.]9[.]501 212[.]46[.]196[.]1331 109[.]74[.]195[.]1901 142[.]251[.]40[.]2381 23[.]62[.]230[.]1591 200[.]6[.]76[.]91 2[.]81[.]154[.]1161
Domain Names contacted by malware. Does not indicate maliciousness Occurrences go[.]microsoft[.]com5 www[.]bing[.]com5 learn[.]microsoft[.]com5 www[.]server[.]com4 huhu1234[.]no-ip[.]org3 gamer9090[.]no-ip[.]org3 smtp[.]mail[.]ru2 google[.]com1 vids[.]p0rn-lover[.]us1 whatismyip[.]akamai[.]com1 ftp[.]drivehq[.]com1 xtremo190278[.]zapto[.]org1 ftp[.]freehostia[.]com1 sandra81[.]no-ip[.]org1 entony[.]no-ip[.]org1 anton124354[.]aiq[.]ru1 hackermibb[.]no-ip[.]info1 amoral999[.]p[.]ht1 api[.]bitcoin[.]cz1 darkcometkiller[.]no-ip[.]biz1 ro[.]sytes[.]net1 ambrella[.]p[.]ht1 merlim2[.]no-ip[.]org1 leechersau[.]no-ip[.]biz1 m3hl2ad[.]no-ip[.]org1
*See JSON for more IOCs
Files and or directories created Occurrences %APPDATA%\logs.dat14 %TEMP%\XX--XX--XX.txt13 %TEMP%\UuU.uUu13 %TEMP%\XxX.xXx13 %TEMP%\Administrator710 %TEMP%\Administrator810 %TEMP%\Administrator2.txt10 %APPDATA%\Administratorlog.dat7 %SystemRoot%\SysWOW64\<random, matching '[a-zA-Z0-9]{4,19}'>.exe7 %APPDATA%\dclogs3 %SystemRoot%\InstallDir3 %SystemRoot%\InstallDir\Server.exe3 %APPDATA%\98B68E3C3 %APPDATA%\98B68E3C\ak.tmp3 %APPDATA%\Administrator-wchelper.dll3 %TEMP%\x.html3 %SystemRoot%\SysWOW64\install3 \TEMP\ufr_reports3 %APPDATA%\explorer.exe3 \Win3 \Win\MSstart.exe3 %APPDATA%\explorer.exe\explorer.exe3 \directory\CyberGate\install\server.exe2 %SystemRoot%\SysWOW64\install\server.exe2 %SystemRoot%\SpyNet\Server.exe2
*See JSON for more IOCs
File Hashes 013663989aa28f3582e2aa90eed455a969d0de2abe419b5b3ec8824fc7a7fef2022a66b7d76fa2bbee56a8d848675aa96b3eddc509fac5d8fbdbb97bed96e9be0b1a97dcdc4b5277f369f8be6df8d3cd65eecfea1f38b65bc2f296b3e55622dd0c1996f1cbad0ab32bc9806290ffd696c71184ee6a5622790dde2316b6a787b00e7b5c92e2c18f75466fbc674fbb7cd728778fa094e590fea7b26def741ca48a113fddf6ffad33cc8ddccabb51d1530529b5ad93f5881282ddc64977dbe3258313df35df42bc3c6c1c47b18b280722923396284f9c3d5b05f6db2de90e7bb9a0143cb3c0433dc9e9bdb163a08b279b8ca1df76841a62c52819fc460a86a3384c1a63251dd369eecd63916d0835327d68da1aa50aa28623a2f4bd1481e968d2381cd038ba74864d02eddc3eb3c3219b7fdebd00e7563229224fc06fa74f4d837d1e3e862c60e25429d06231f72a5271c46528066bc82cf49431c4ad52552d0ebc203652f28faffcf14891f31df19f5843c4ebca55e6c0225a2d0e17f1d610dc7022037f54606da56dab0da53ba84cac987a99c1d81787a170e19812ad3ed6b0b22ec90cfa025740aa44baecf8eee2de66707678df216b4d555d95ee14221f1830314e8e577dacf2287a1205ceb98ff4548ba513ee4b55a634ee48acce14f63c9432fef765f38580d1c018596d379620487cb8a0ab03ac149aeef6e9b42d8c792b361ecf702e46b665843216d9be94fbdd84b231575c1a2026f04e6a4cced6f57738712d1de42f33c02e3ff7bd73caff8bb5e4c7f89fd11f6920207b094bc81fa63e848b438998dcd3aa40311d041d40c230ed22125625e5396f03d6265a5834fa41eec2a4b3f6589097321436053722c95ab9b81f2f71c508e67a9764372e0fe74327d0f53f24d02cd6761ce90773cb02a085328ea261f7449686c4fd35e5ecca457a450ff6b934e8bb4c9c96a6be3065a009221474d4a950651285c1572f5dbd45bded663194abc4170e80e83abbe48e74fc91b4a2b2c5043e5479d89bd2b9e74847ff9a4a02048dd5d9fccaa0d9e1bf377193f141ed0d3ce11aa554424e1e454a20d0d4786573ffa78c283fd882080b30a860f3668c81fb027640b8e0faaf3d
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
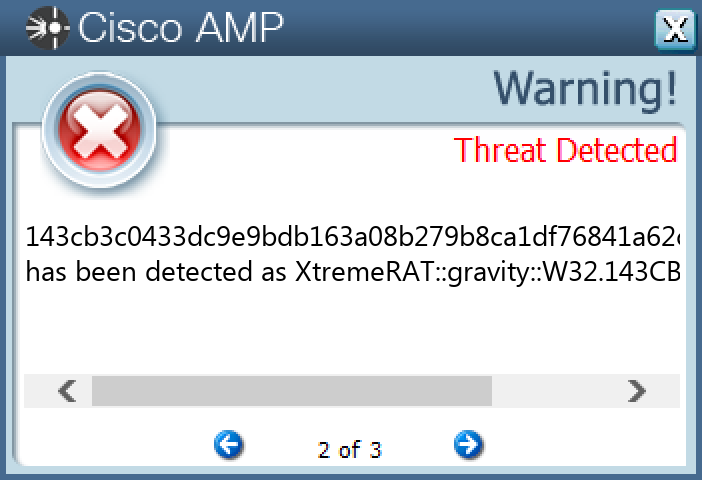
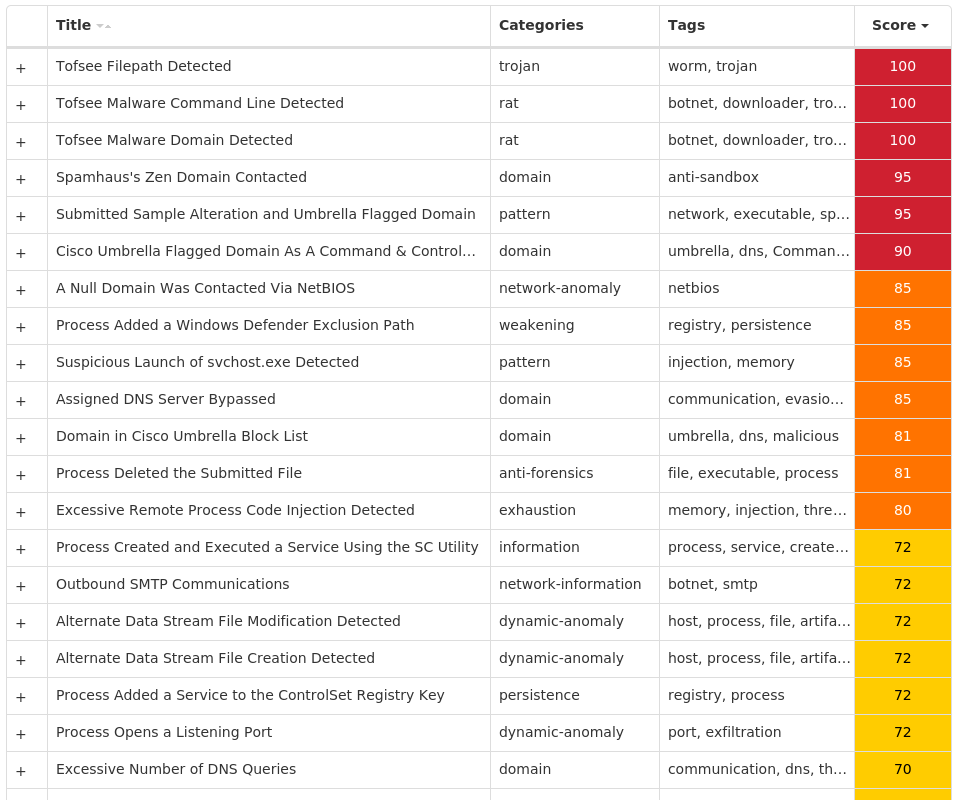
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.Tofsee-10000005-0 Indicators of Compromise IOCs collected from dynamic analysis of 83 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\USER SHELL FOLDERS Value Name: Startup 27 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER Value Name: DisableAntiSpyware 26 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\WINDEFEND Value Name: Start 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE\AU26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE\AU Value Name: NoAutoRebootWithLoggedOnUsers 26 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\WUAUSERV Value Name: Start 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE\AU Value Name: NoAutoUpdate 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\REAL-TIME PROTECTION Value Name: DisableBehaviorMonitoring 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\REAL-TIME PROTECTION Value Name: DisableOnAccessProtection 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\REAL-TIME PROTECTION Value Name: DisableScanOnRealtimeEnable 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\REAL-TIME PROTECTION Value Name: DisableIOAVProtection 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\REAL-TIME PROTECTION26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE26 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS DEFENDER\FEATURES26 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS DEFENDER\FEATURES Value Name: TamperProtection 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER\REAL-TIME PROTECTION Value Name: DisableRealtimeMonitoring 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER SECURITY CENTER26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE\AU Value Name: AUOptions 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE\AU Value Name: AutoInstallMinorUpdates 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER SECURITY CENTER\NOTIFICATIONS26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS DEFENDER SECURITY CENTER\NOTIFICATIONS Value Name: DisableNotifications 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE\AU Value Name: UseWUServer 26 <HKLM>\SOFTWARE\POLICIES\MICROSOFT\WINDOWS\WINDOWSUPDATE Value Name: DoNotConnectToWindowsUpdateInternetLocations 26 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\ISUPLDCY Value Name: Description 1
Mutexes Occurrences 006700e5a2ab05704bbb0c589b88924d27 Global\<random guid>14
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 193[.]3[.]19[.]15427 194[.]25[.]134[.]1151 212[.]27[.]48[.]21 149[.]154[.]167[.]991 152[.]195[.]33[.]1321 31[.]13[.]65[.]521 66[.]254[.]114[.]411 198[.]133[.]159[.]2501 104[.]244[.]42[.]661 176[.]113[.]115[.]1361 142[.]250[.]65[.]2281 212[.]54[.]56[.]521 142[.]251[.]40[.]1421 20[.]103[.]85[.]331 80[.]66[.]75[.]2541 80[.]66[.]75[.]41 20[.]44[.]209[.]2091 176[.]113[.]115[.]2391 176[.]113[.]115[.]1351 104[.]127[.]87[.]2101 40[.]93[.]207[.]71 176[.]124[.]192[.]331 23[.]15[.]9[.]581 185[.]161[.]248[.]731 176[.]124[.]192[.]2121
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences 249[.]5[.]55[.]69[.]bl[.]spamcop[.]net1 249[.]5[.]55[.]69[.]cbl[.]abuseat[.]org1 249[.]5[.]55[.]69[.]dnsbl[.]sorbs[.]net1 249[.]5[.]55[.]69[.]in-addr[.]arpa1 249[.]5[.]55[.]69[.]sbl-xbl[.]spamhaus[.]org1 249[.]5[.]55[.]69[.]zen[.]spamhaus[.]org1 i[.]instagram[.]com1 microsoft-com[.]mail[.]protection[.]outlook[.]com1 microsoft[.]com1 www[.]google[.]com1 www[.]youtube[.]com1 www[.]tiktok[.]com1 t[.]me1 api[.]twitter[.]com1 www[.]pornhub[.]com1 imap[.]free[.]fr1 mx01[.]bnr[.]ca1 imap[.]ntlworld[.]com1 imap[.]t-online[.]de1 steamcommunity[.]com1 api[.]steampowered[.]com1 api[.]solscan[.]io1 in-jsproxy[.]globh[.]com1 cv-h[.]phncdn[.]com1 vanaheim[.]cn1
*See JSON for more IOCs
Files and or directories created Occurrences %APPDATA%\006700e5a2ab0527 %APPDATA%\006700e5a2ab05\clip64.dll27 %APPDATA%\006700e5a2ab05\cred64.dll27 %System32%\Tasks\oneetx.exe27 %TEMP%\cb7ae701b327 %TEMP%\cb7ae701b3\oneetx.exe27 %SystemRoot%\SysWOW64\config\systemprofile1 %SystemRoot%\SysWOW64\config\systemprofile:.repos1 %TEMP%\IXP001.TMP1 %TEMP%\IXP001.TMP\TMP4351$.TMP1 %TEMP%\IXP002.TMP1 %TEMP%\IXP002.TMP\TMP4351$.TMP1 %TEMP%\IXP003.TMP1 %TEMP%\IXP003.TMP\TMP4351$.TMP1 %LOCALAPPDATA%\Yandex1 %LOCALAPPDATA%\Yandex\YaAddon1 %SystemRoot%\SysWOW64\isupldcy1 %SystemRoot%\Temp\1.exe1 %TEMP%\wmixskiq.exe1 %TEMP%\10000110511 %TEMP%\1000011051\foto0174.exe1 %TEMP%\10000120511 %TEMP%\1000012051\foto34.exe1 %TEMP%\IXP000.TMP\s54755209.exe1 %TEMP%\IXP000.TMP\y52881425.exe1
*See JSON for more IOCs
File Hashes 015446106849e64c790d08cf9ccc81523b1022f358b7f3f22b0faf6dce4d1cd90585f6fdd47eea51bddd77a2a4ff35d8d601d1b9a0a5120d74d86887c3f31f3c0ec37d41525ee0c5995446e6163fa32d0b6fd05a92bcab4b973b83791d0221550f2584ba5e0633404ff7a283a0c4931c2a161c052ad6e91385744512c12972dd12c4f1a7804bcd0557676c249d7ac371f2871bf8057f5ea88664f05c77bed71912d076a14fa94b8e4a290a8b96afaa95fc336bdd0e2551b61694db67a1e49d431639c21ce9570b200bcbc40da2c299ef18366f24fce3f81ff4621c264128e1c419db38a3d52c3f9196ea1bf1db4b687fe8b887467213c4138b34665aa717392f1b203972e5f19418d1ac3516ccd2805f2622058608e70e106bf083d06b26af6a1c3641047cd096ea8ae7c13ac0dfe7e57b97920a2002c86cd1dc475782229fe71deff8f3cab9e0cb8b42a9cae86778344b69bfa227f0fc96265236a7066bfa681f2164eed8463a61b8b74c726eca872492b7998ec1b93637d88982acf677fece1f5a48c6de3756ea45bc49d01425438dbef0000494d93394277e37838dd0e2c2200acae29bca6ce1a2446970d7591628aa18bcaca901fb078802b36cd4bab4c12557e803f9addcdaf17a57b3bb8d424cc7befb24aa26f9e856be185897c57116273530b5aa7733745abea770ee350b56d6014a763e11ddee56ebf065757ba4ca2748358acbd71868da3945a1c0bff0c3f215f9a6f674e6cc7eae01da08fb3ebb30f356b7c5b33da719938b1ecf3674097bb9a80373aee214dd4962712c0fc5aa31460296fbfc4dcd31b5bd8978088dce48c1e60357f64730de6d952e6bee33fe3341fb4c70db0226c50d769ecc2ee479890a1f42d59c8e67a90a9264dd17529f347b42a92d481e418ed9b7a34d493bf53b374e4b71ac8f0431556a4912abd86339e9ea2973521669029531407fad8e193a98f84d88626bb2323fd4b9d0cf389a3a0821a19a70e429adf239ad8c1f36709d3a446872a0fbb7e1eec995a9ffd6563d16f9d8728cf8e0e1b8e437e31f97b93c2816fcf7115b913250efa194c0708f40902f59d70b569b4b240116bd43593746395042f99d96c1d31770e7fd670509
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
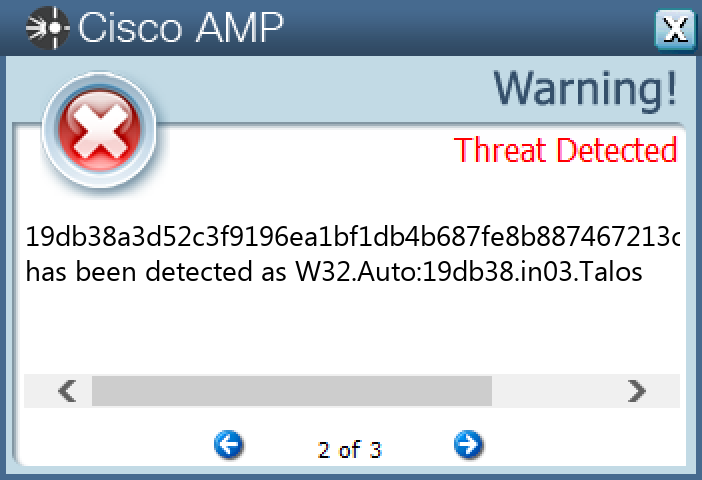
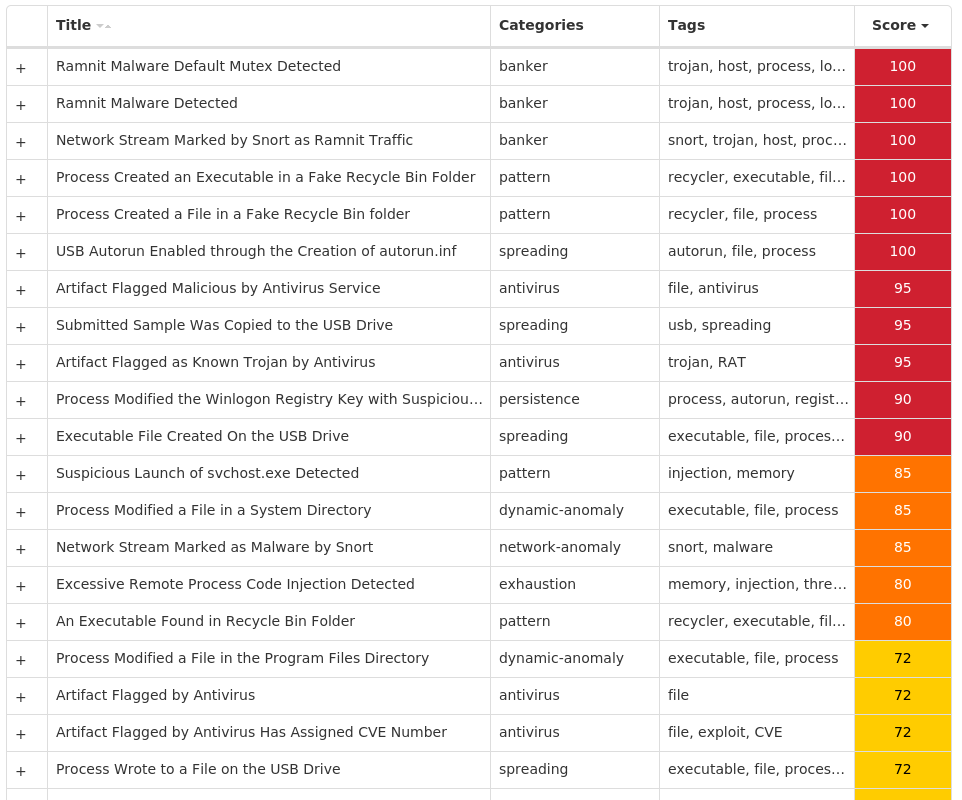
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Trojan.Ramnit-10000021-1 Indicators of Compromise IOCs collected from dynamic analysis of 17 samples Registry Keys Occurrences <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON Value Name: Userinit 17
Mutexes Occurrences Global\SYSTEM_DEMETRA_CONTROL17 Global\SYSTEM_DEMETRA_MAIN17 Global\SYSTEM_DEMETRA_SHUTDOWN17 Global\SYSTEM_DEMETRA_HOOK_0000000017 Global\SYSTEM_DEMETRA_HOOK_0000000417 Global\SYSTEM_DEMETRA_HOOK_000000CC17 Global\SYSTEM_DEMETRA_HOOK_0000012017 Global\SYSTEM_DEMETRA_HOOK_0000015017 Global\SYSTEM_DEMETRA_HOOK_0000015817 Global\SYSTEM_DEMETRA_HOOK_0000017417 Global\SYSTEM_DEMETRA_UNIQ_0000000017 Global\SYSTEM_DEMETRA_UNIQ_0000000417 Global\SYSTEM_DEMETRA_UNIQ_000000CC17 Global\SYSTEM_DEMETRA_UNIQ_0000012017 Global\SYSTEM_DEMETRA_UNIQ_0000015017 Global\SYSTEM_DEMETRA_UNIQ_0000015817 Global\SYSTEM_DEMETRA_UNIQ_0000017417 Global\SYSTEM_DEMETRA_HOOK_000001AC17 Global\SYSTEM_DEMETRA_HOOK_000001BC17 Global\SYSTEM_DEMETRA_HOOK_000001C417 Global\SYSTEM_DEMETRA_HOOK_000001F017 Global\SYSTEM_DEMETRA_HOOK_0000021C17 Global\SYSTEM_DEMETRA_HOOK_0000025C17 Global\SYSTEM_DEMETRA_HOOK_0000029417 Global\SYSTEM_DEMETRA_HOOK_000002EC17
*See JSON for more IOCs
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 72[.]26[.]218[.]7017 142[.]250[.]80[.]11017
Domain Names contacted by malware. Does not indicate maliciousness Occurrences google[.]com17 fget-career[.]com17
Files and or directories created Occurrences %CommonProgramFiles(x86)%\microsoft shared\TRANSLAT\ESEN\MSB1ESEN.DLL17 %CommonProgramFiles(x86)%\microsoft shared\TRANSLAT\FREN\MSB1FREN.DLL17 %CommonProgramFiles(x86)%\microsoft shared\TRANSLAT\WTSP61MS.DLL17 %CommonProgramFiles(x86)%\microsoft shared\VS Help Data\8.0\Resources\1033\InterstitialPage.htm17 %CommonProgramFiles(x86)%\microsoft shared\VS7Debug\coloader80.dll17 %CommonProgramFiles(x86)%\microsoft shared\VS7Debug\csm.dll17 %CommonProgramFiles(x86)%\microsoft shared\VS7Debug\dbgautoattach.dll17 %CommonProgramFiles(x86)%\microsoft shared\VS7Debug\msdbg2.dll17 %ProgramFiles(x86)%\Microsoft Office\Office14\ADDINS\MSVCR71.DLL17 %ProgramFiles(x86)%\Microsoft Office\Office14\AccessWeb\CLNTWRAP.HTM17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsBlankPage.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsBrowserUpgrade.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsColorChart.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsFormTemplate.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsHomePage.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsImageTemplate.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsMacroTemplate.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsPreviewTemplate.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms3\FormsPrintTemplate.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms\FormsBlankPage.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms\FormsBrowserUpgrade.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms\FormsDoNotTrust.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms\FormsHomePage.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms\FormsPreviewTemplate.html17 %ProgramFiles(x86)%\Microsoft Office\Office14\Groove\ToolData\groove.net\GrooveForms\FormsPrintTemplate.html17
*See JSON for more IOCs
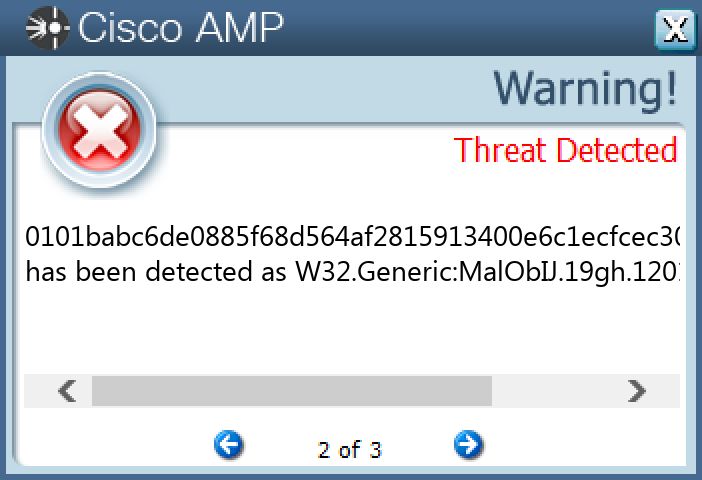
File Hashes 0101babc6de0885f68d564af2815913400e6c1ecfcec309ed358a17dfee6e4af0d36eb4b1c7d8fdf73e6160144265fa488d0b5b5741d183099f77537067068b21d3ec82f736135526133101405b0287a703b7d19e55ed547ca5b38a4e0888e1c2e71faa6419936869da29b10761a4cb85bfa5216f53a2a71214823cf246bb3a3325c33566126539544c5ee9e20cb457768bbfd1323e7b52541ad087672289d8742b2382ace5f7574144c09b28d4758ad25b369e33bb317e4f4fdb4196e1a79044c3db94d4426234d1d57ba85e99109fcac8894ce89546766b947878888e966558ddb1ac3a421311ef930fa41dc04506fd01a2d7d298e68234c26701ec1c34ee7986e58cf8a11498f2eba1f93be224c9d94b6e5a0fef3e0ddb7528a6a8874773ea517e2930f308f58a6a5d8fec58d523aeade89b1239335e4da38ed9062f5598fafa8d3d2b57a56efc94dbacfc815eeb94fc2f88ed405b3c4f8ede6d5ca61ead4b30d5cbe7413e449245f5e3a39e51c1fb77a734b6431626f0cc918892bcee0a6b94712e6768ef42f5069ff432bbbf5b917b292fe43beb35c17613b1d60d3e832c7d9a2c3eca11892a61ee2f55f186ce73d3f322fd7885bb1346f7e5dc0f0c495cd70f028723d38966ae882a63bae7276c48e173f69b293da99d8be9ece9b0befe3004c3b51fa179d9c8f67904a94f296c130194d82aff35a25e0acfe2c13ee97fe683c7b877c2d95af6922d80d88591868d7a7fd602a0ab2679c5f28fac0432e
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK