Today, Talos is publishing a glimpse into the most prevalent threats we've observed between Oct. 13 and Oct. 20. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise, and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org , or ClamAV.net .
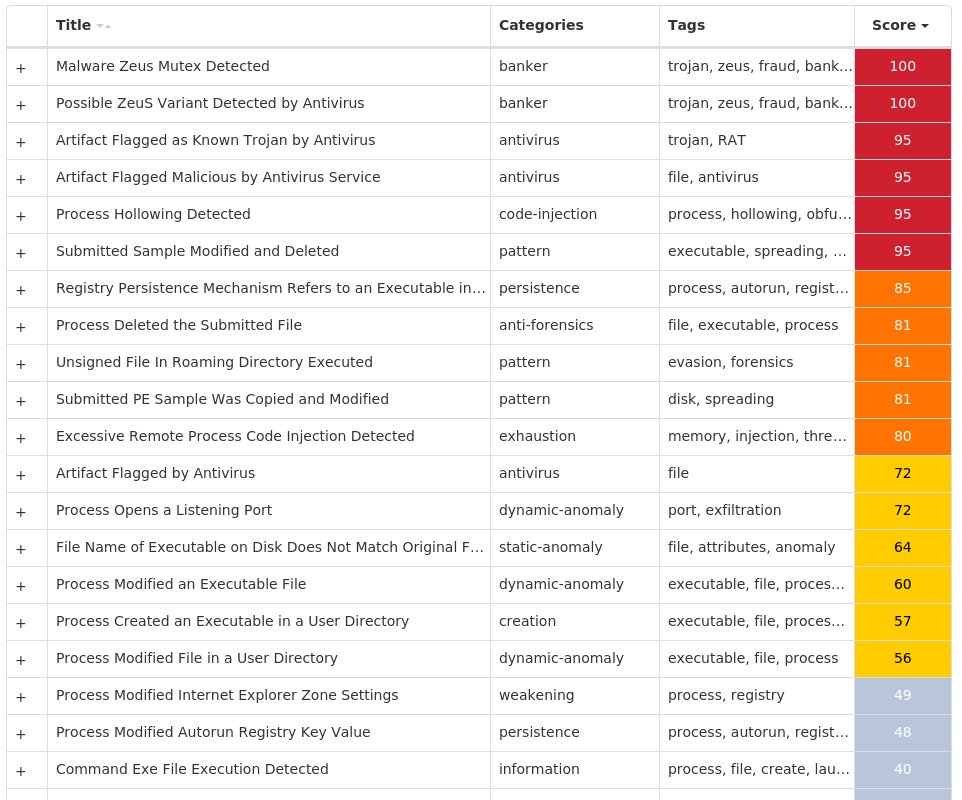
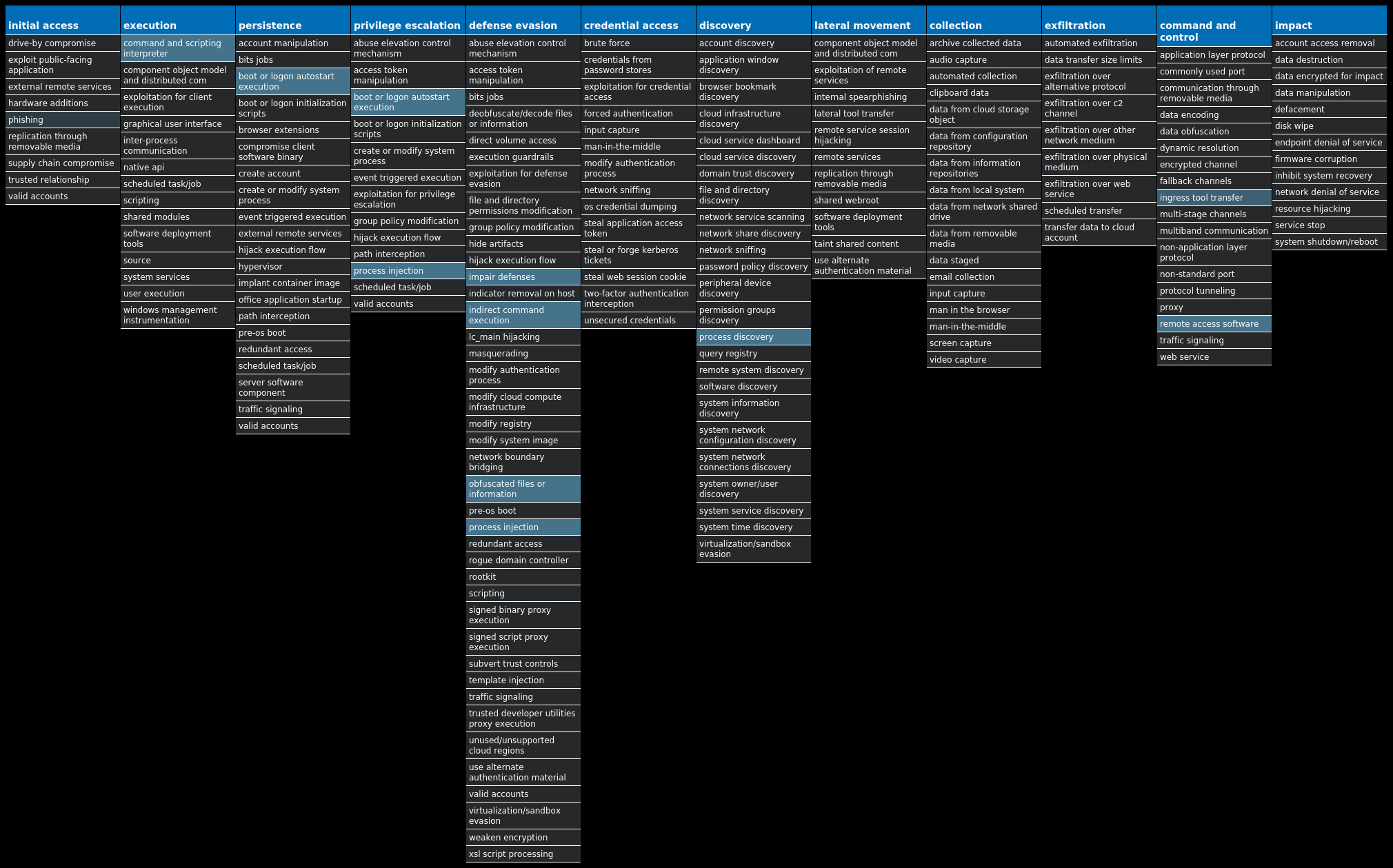
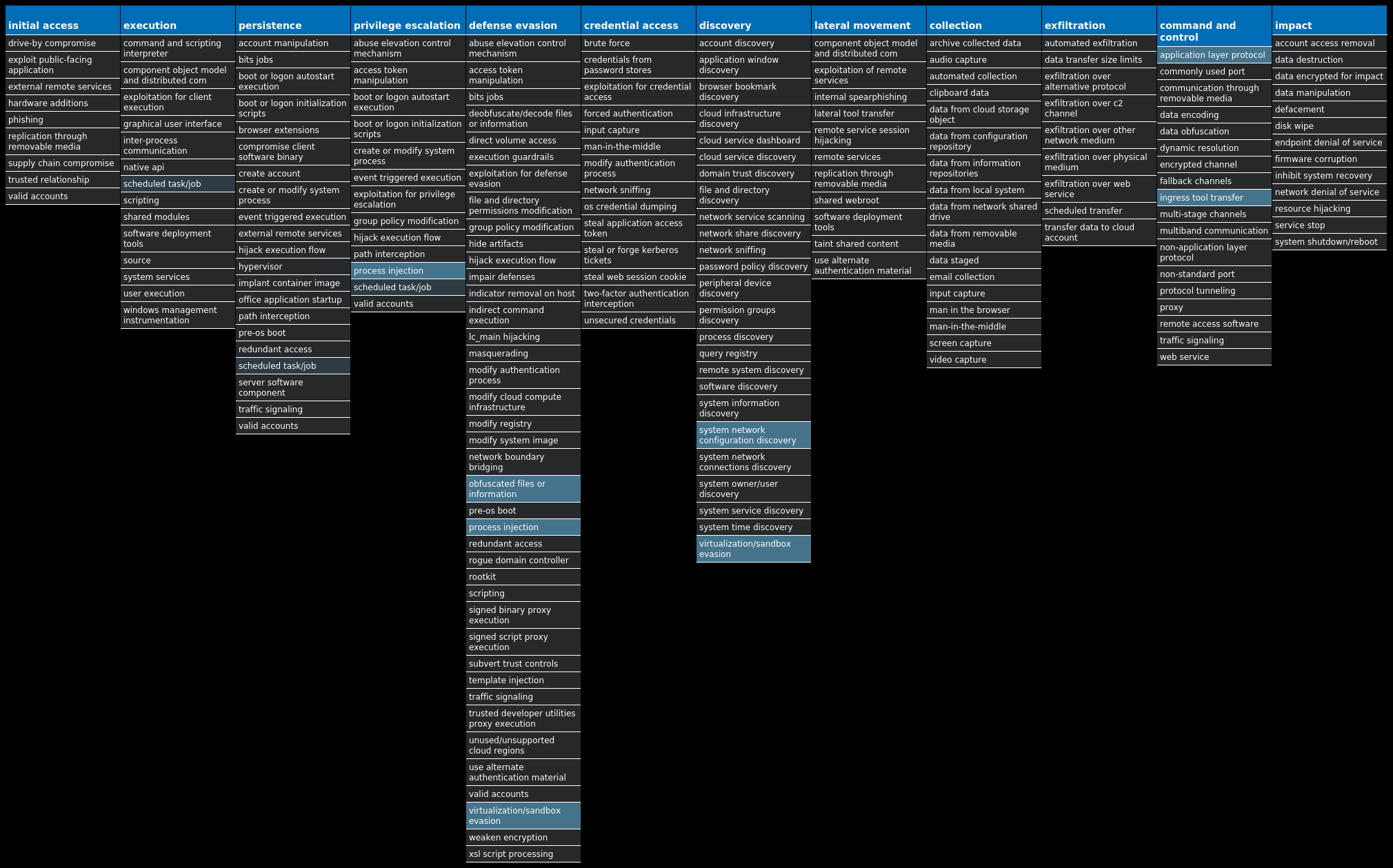
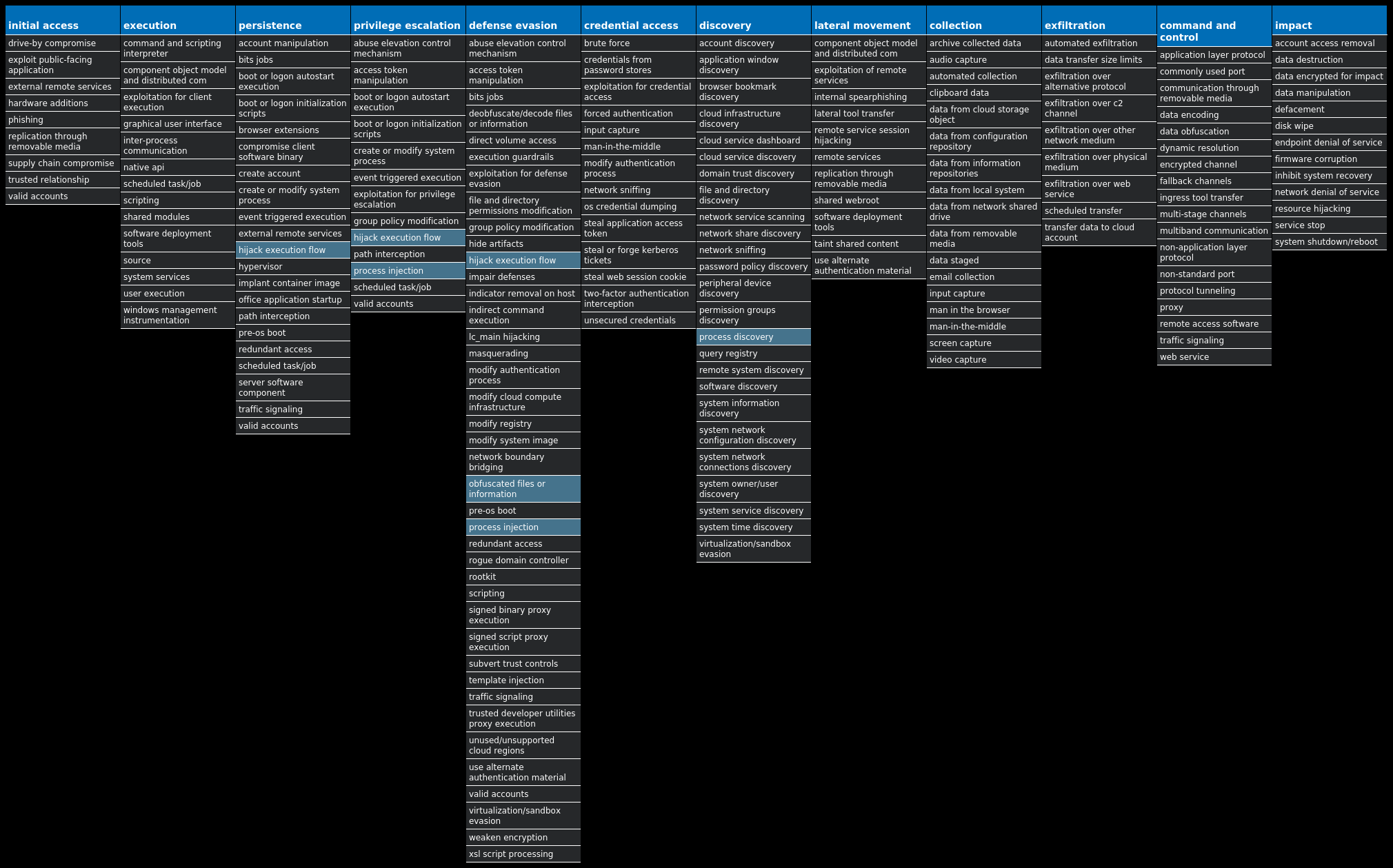
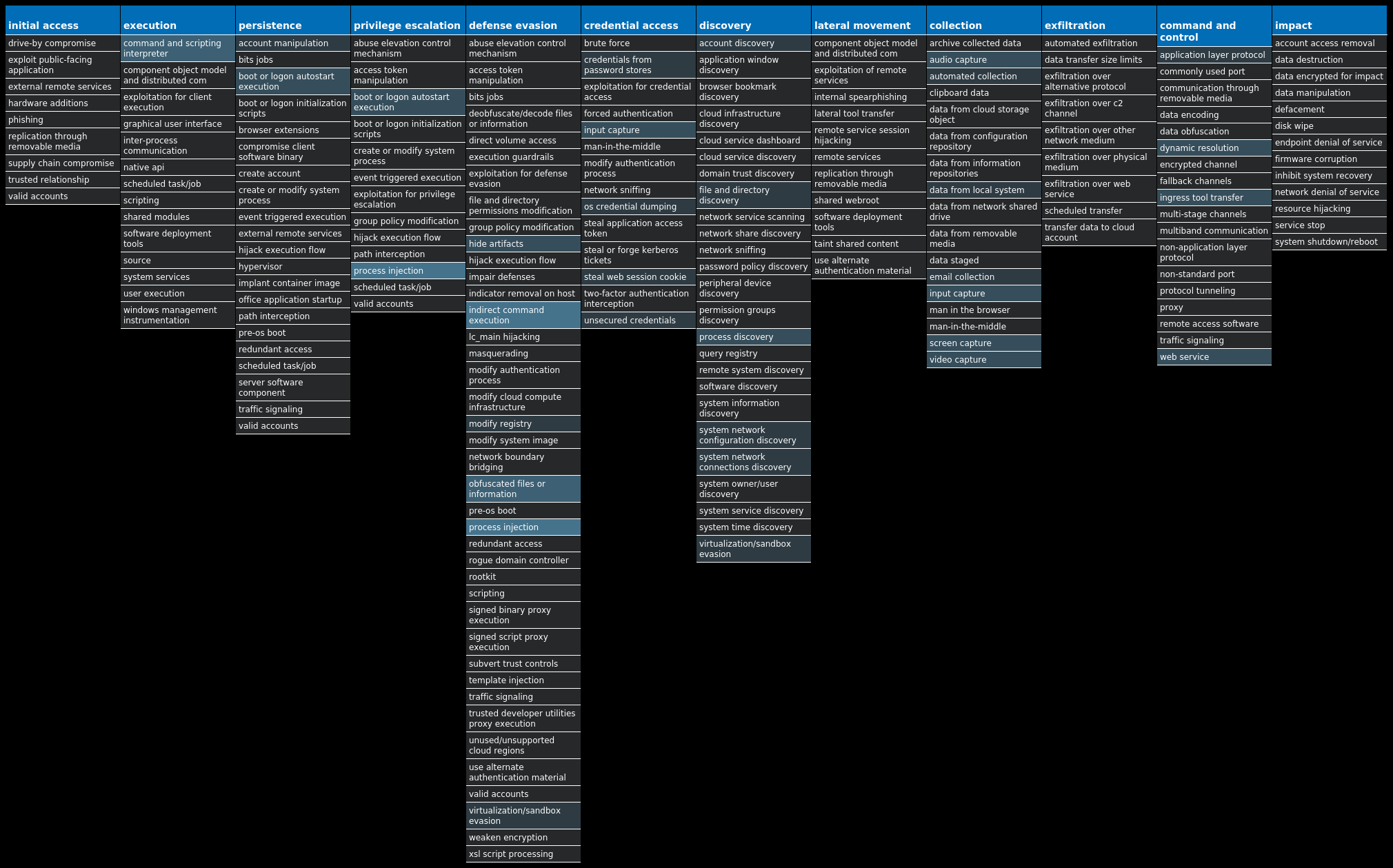
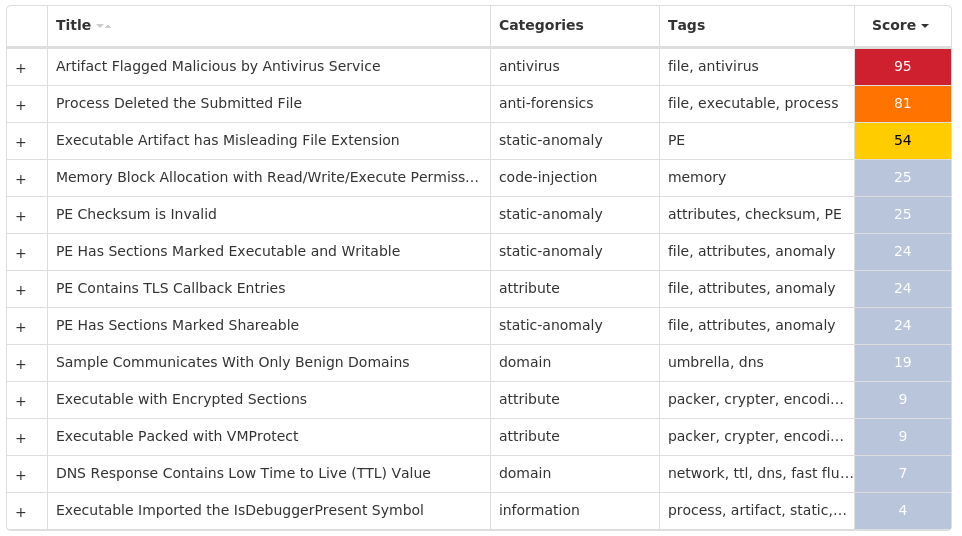
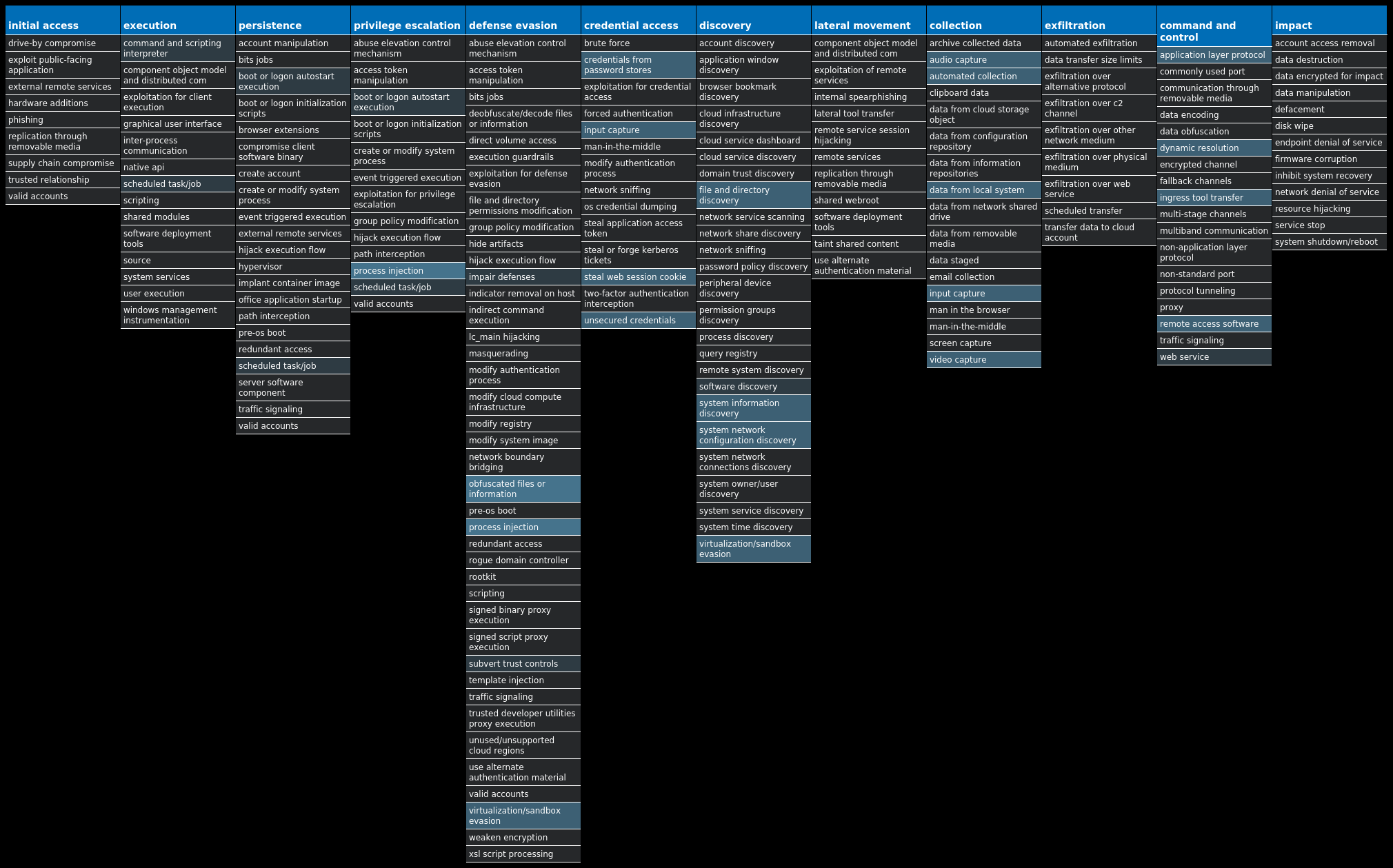
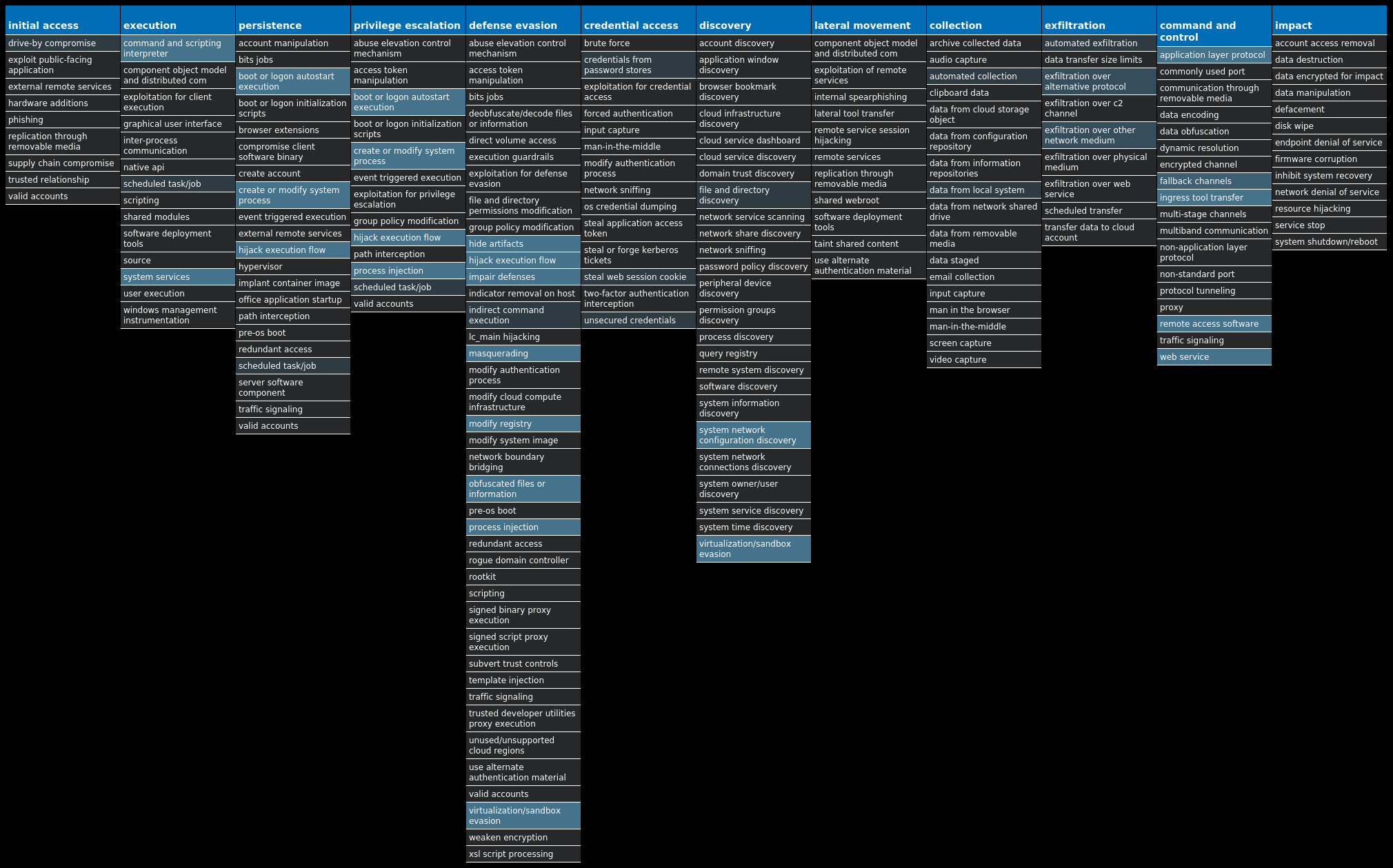
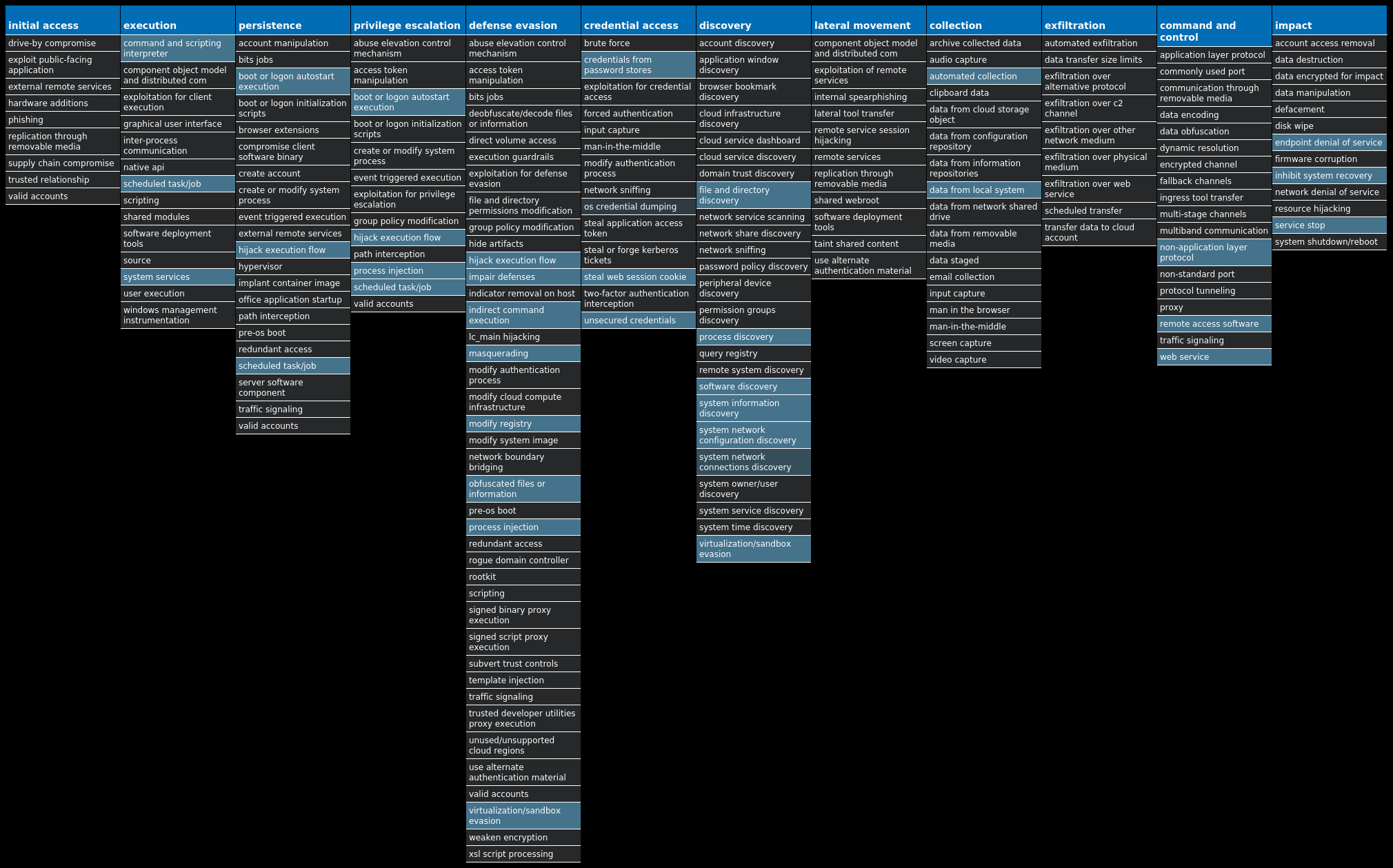
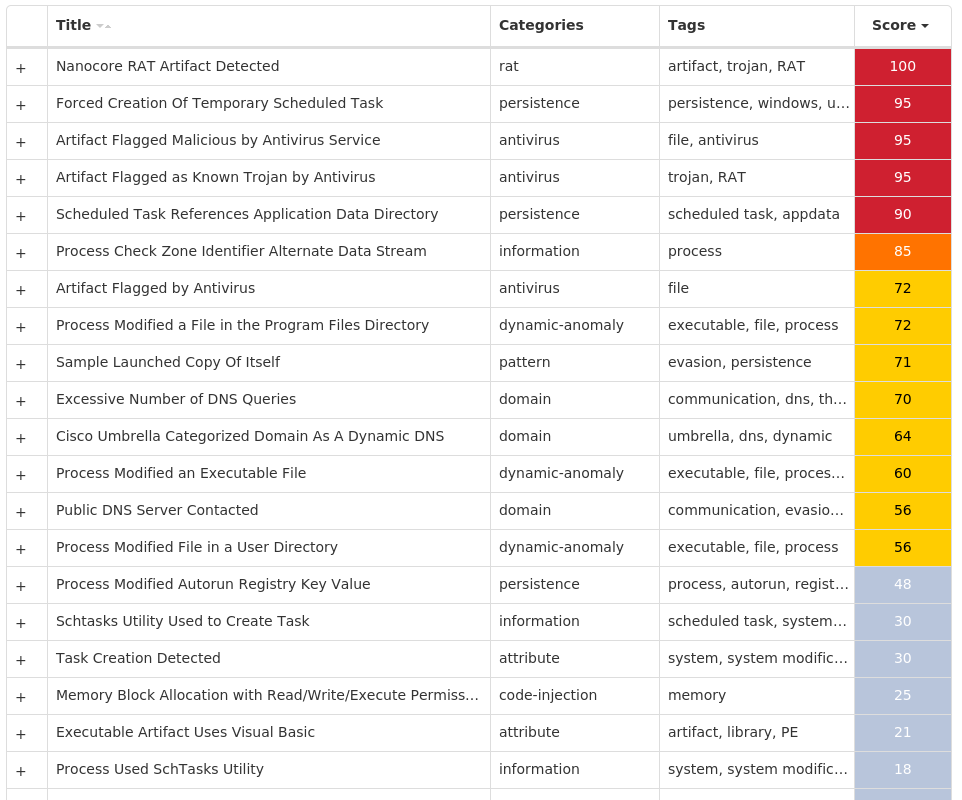
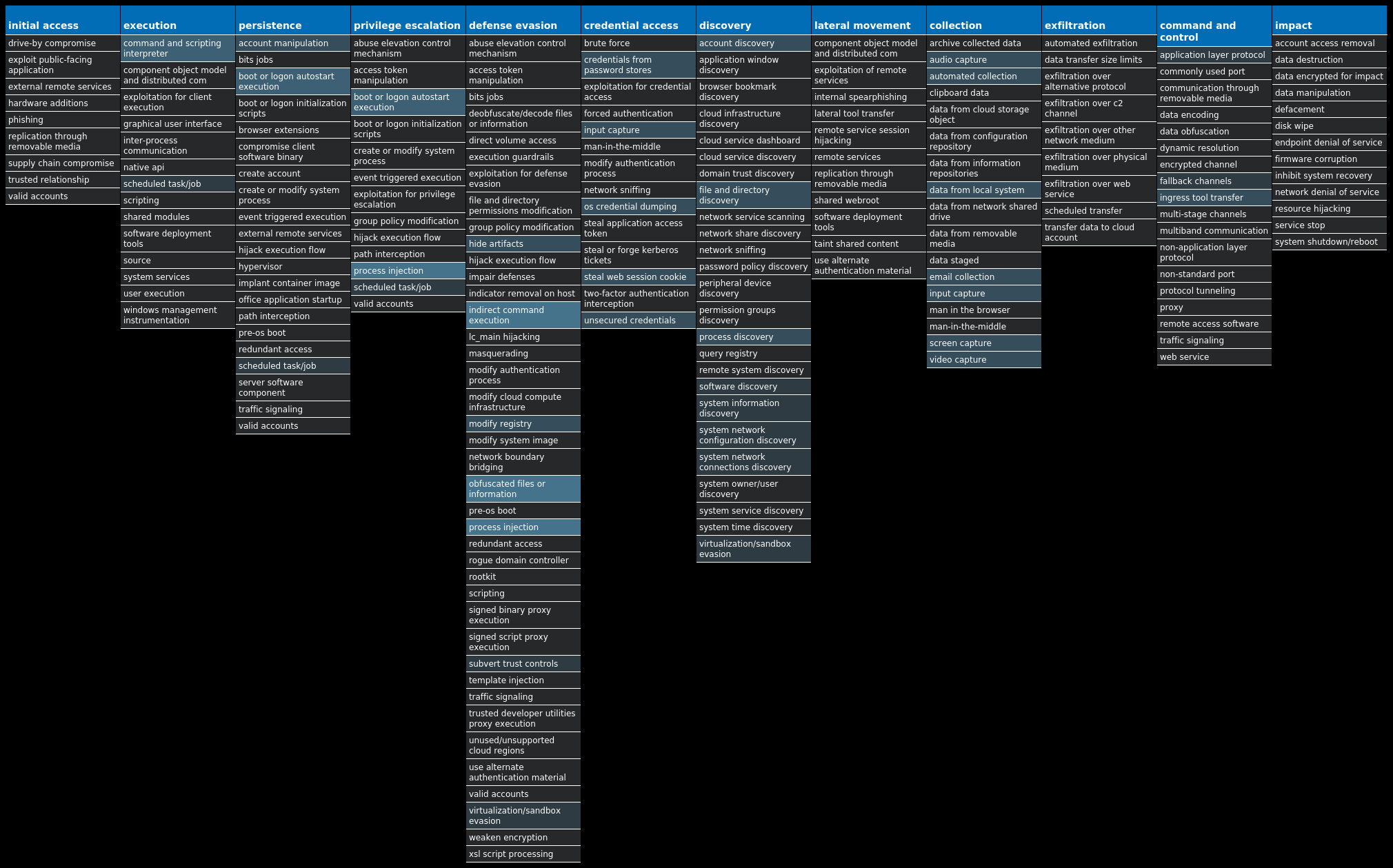
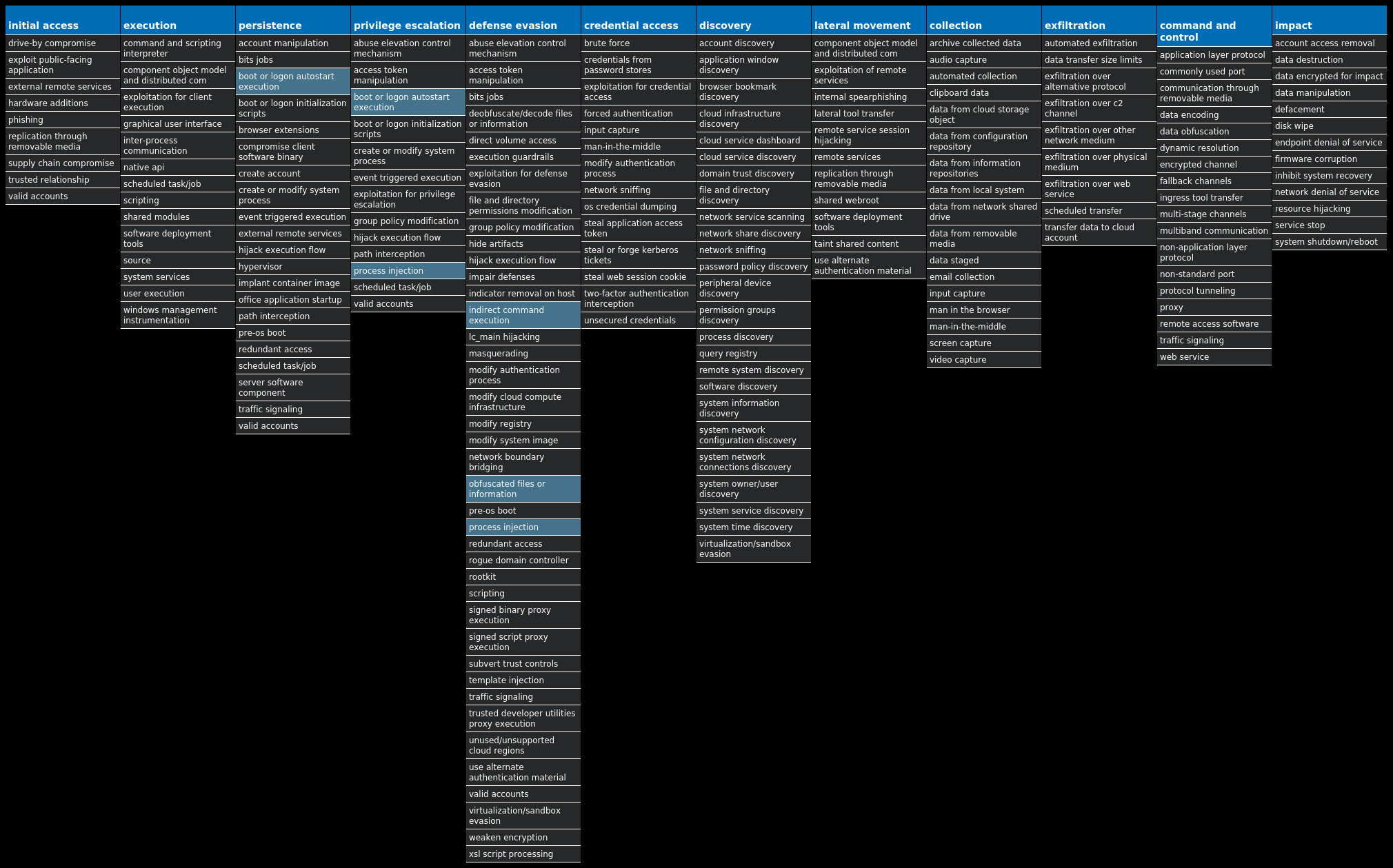
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found here that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name Type Description Win.Dropper.Zeus-10011479-0 Dropper Zeus is a trojan that steals information such as banking credentials using methods such as key-logging and form-grabbing. Win.Downloader.Upatre-10011416-0 Downloader Upatre is a malicious downloader often used by exploit kits and phishing campaigns. Upatre downloads and executes malicious executables, such as banking malware. Win.Packed.CoinMiner-10011305-1 Packed This malware installs and executes cryptocurrency-mining software. Win.Dropper.Remcos-10011195-0 Dropper Remcos is a remote access trojan (RAT) that allows attackers to execute commands on the infected host, log keystrokes, interact with a webcam, and capture screenshots. This malware is commonly delivered through Microsoft Office documents with macros, sent as attachments on malicious emails. Win.Malware.Zusy-10010855-0 Malware Zusy, also known as TinyBanker or Tinba, is a trojan that uses man-in-the-middle attacks to steal banking information. When executed, it injects itself into legitimate Windows processes such as "explorer.exe" and "winver.exe." When the user accesses a banking website, it displays a form to trick the user into submitting personal information. Win.Packed.AgentTesla-10010785-1 Packed AgentTesla is a remote access rojan that records keystrokes and attempts to steal sensitive information from web browsers and other installed applications. Win.Trojan.Tofsee-10010766-0 Trojan Tofsee is multi-purpose malware that features a number of modules used to carry out various activities such as sending spam messages, conducting click fraud, mining cryptocurrency, and more. Infected systems become part of the Tofsee spam botnet and are used to send large volumes of spam messages in an effort to infect additional systems and increase the overall size of the botnet under the operator's control. Win.Dropper.Glupteba-10010808-0 Dropper Glupteba is a multi-purpose trojan that is known to use the infected machine to mine cryptocurrency and steals sensitive information like usernames and passwords, spreads over the network using exploits like EternalBlue, and leverages a rootkit component to remain hidden. Glupteba has also been observed using the Bitcoin blockchain to store configuration information. Win.Dropper.Nanocore-10011208-0 Dropper Nanocore is a .NET remote access trojan. Its source code has been leaked several times, making it widely available. Like other RATs, it allows full control of the system, including recording video and audio, stealing passwords, downloading files and recording keystrokes. Win.Dropper.DarkComet-10011490-1 Dropper DarkComet and related variants are a family of remote access trojans designed to provide an attacker with control over an infected system. Capabilities of this malware include the ability to download files from a user's machine, mechanisms for persistence and hiding, and the ability to send back usernames and passwords from the infected system.
Threat Breakdown Win.Dropper.Zeus-10011479-0 Indicators of Compromise IOCs collected from dynamic analysis of 17 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\INTERNET EXPLORER\PRIVACY Value Name: CleanCookies 12 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{E8433B72-5842-4D43-8645-BC2C35960837}.CHECK.101 Value Name: CheckSetting 12 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{E8433B72-5842-4D43-8645-BC2C35960837}.CHECK.103 Value Name: CheckSetting 12 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{E8433B72-5842-4D43-8645-BC2C35960837}.CHECK.100 Value Name: CheckSetting 12 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{E8433B72-5842-4D43-8645-BC2C35960837}.CHECK.102 Value Name: CheckSetting 12 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{E8433B72-5842-4D43-8645-BC2C35960837}.CHECK.104 Value Name: CheckSetting 12 \Software\Microsoft\ 12 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: {C45BAE81-6FD8-625F-01B4-47867CA2B270} 5 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: {2AD245C9-6C14-D117-E84E-F21650C846A7} 2 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: {429DEFC0-AD95-8173-F328-FEDF80CD61A8} 2 \SOFTWARE\MICROSOFT\TAVIYR Value Name: Hyqafowo 1 \SOFTWARE\MICROSOFT\DIAQ Value Name: Tufa 1 \SOFTWARE\MICROSOFT\EDVA Value Name: Ruudibnir 1 \SOFTWARE\MICROSOFT\RAAMI Value Name: Oripxe 1 \SOFTWARE\MICROSOFT\HOOSS Value Name: Kuufture 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: {1B9B0642-9212-04C9-E76A-6689A279823D} 1 \SOFTWARE\MICROSOFT\EGNIB Value Name: Duvuoro 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: {82AFDD97-56B5-8180-6246-7EACFD9E3E11} 1 \SOFTWARE\MICROSOFT\OTIH Value Name: Umuz 1 \SOFTWARE\MICROSOFT\LUSYQO Value Name: Ecpiogtoi 1 \SOFTWARE\MICROSOFT\UCRUU Value Name: Yxyqnupio 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: {4DDC5D3F-09DB-40C8-8BE7-793502F0E15B} 1 \SOFTWARE\MICROSOFT\OSYCR Value Name: Okgeta 1 \SOFTWARE\MICROSOFT\WUENMU Value Name: Obyqupdot 1 \SOFTWARE\MICROSOFT\EQKURY Value Name: Itusri 1
Mutexes Occurrences 8548551517 GLOBAL\{} 12 Local\{} 12 Local\{224FD2A9-13F0-844B-01B4-47867CA2B270}5
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 34[.]98[.]99[.]305 109[.]203[.]118[.]162
Domain Names contacted by malware. Does not indicate maliciousness Occurrences conntact[.]com5 cursodegnosis[.]net3 wildlife-galleries[.]co[.]uk2 www[.]tuguarenas[.]com1 tuoitredakrlap[.]net1
Files and or directories created Occurrences %TEMP%\tmp.bat 12 %APPDATA%\12 %APPDATA%\.exe 12 %APPDATA%\Agumaz\ukuvt.oqd1 %APPDATA%\Rimuxy\gaka.aku1 %APPDATA%\Ukomim\heyf.deg1 %APPDATA%\Izxi\omly.eqe1 %APPDATA%\Umudb\odmok.evr1 %APPDATA%\Avke\egroo.agk1 %APPDATA%\Zaopy\vemoe.ebk1 %APPDATA%\Onsuca\goba.lyc1 %APPDATA%\Toze\avlo.pee1 %APPDATA%\Ygol\riyxd.apa1 %APPDATA%\Dywib\ysah.eki1 %APPDATA%\Nyyryz\muehe.avr1
File Hashes 0390a213c2f1e2044dc034ef69854250734d366b588e5ed56ccfd43d6e487c61
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
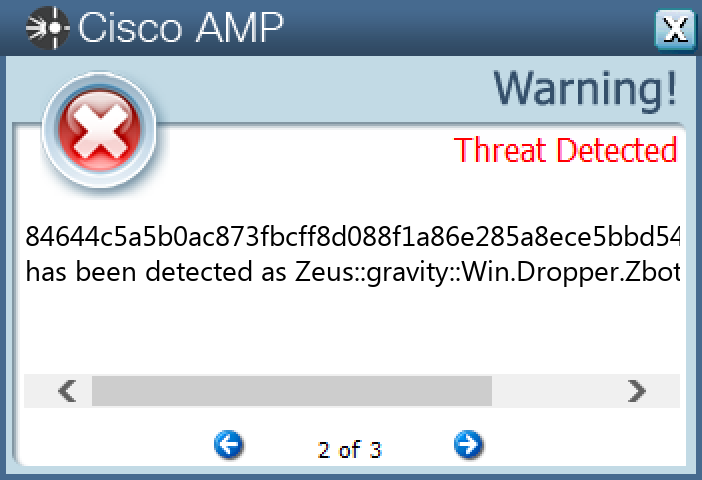
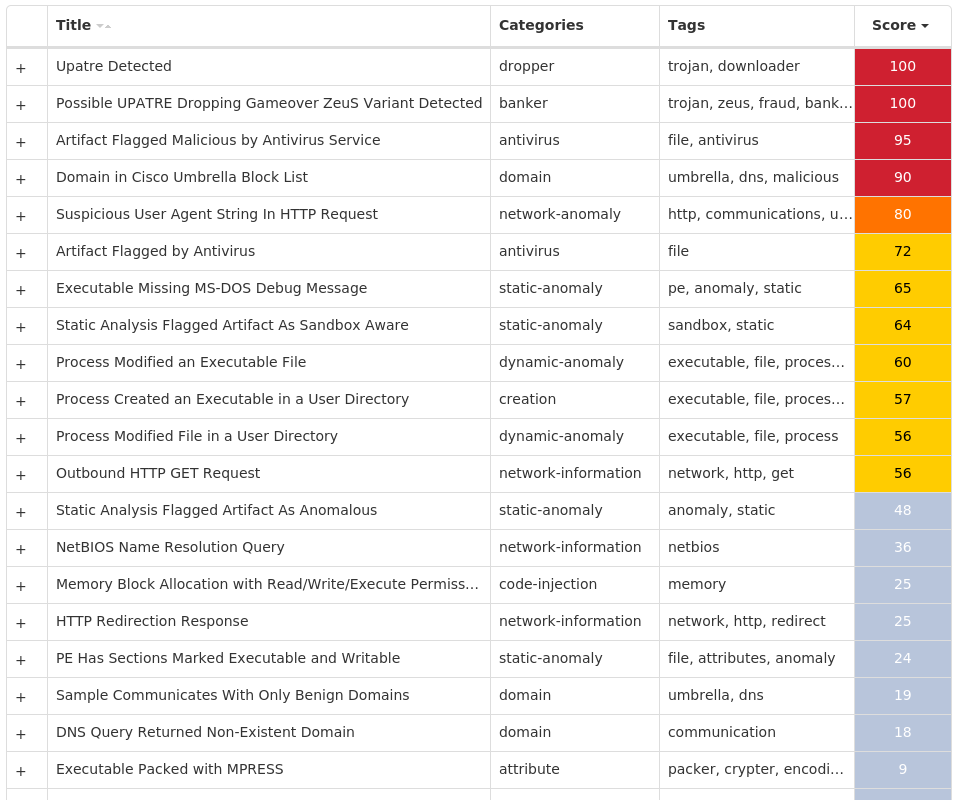
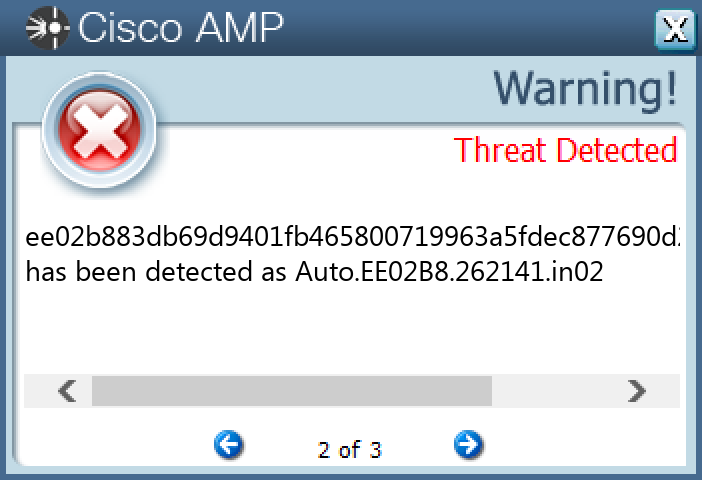
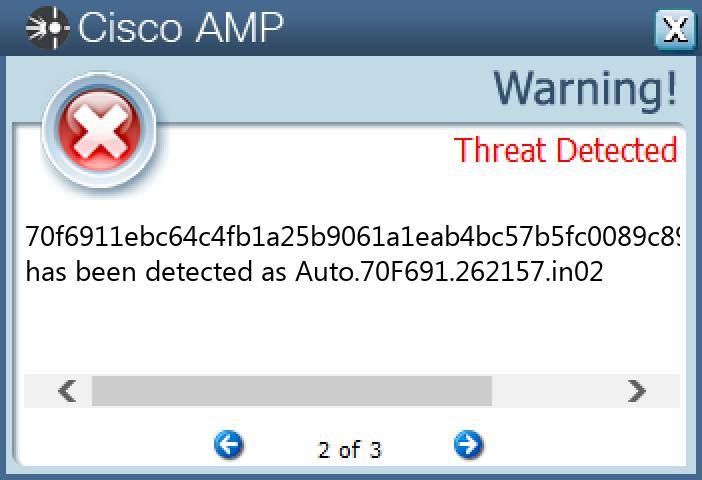
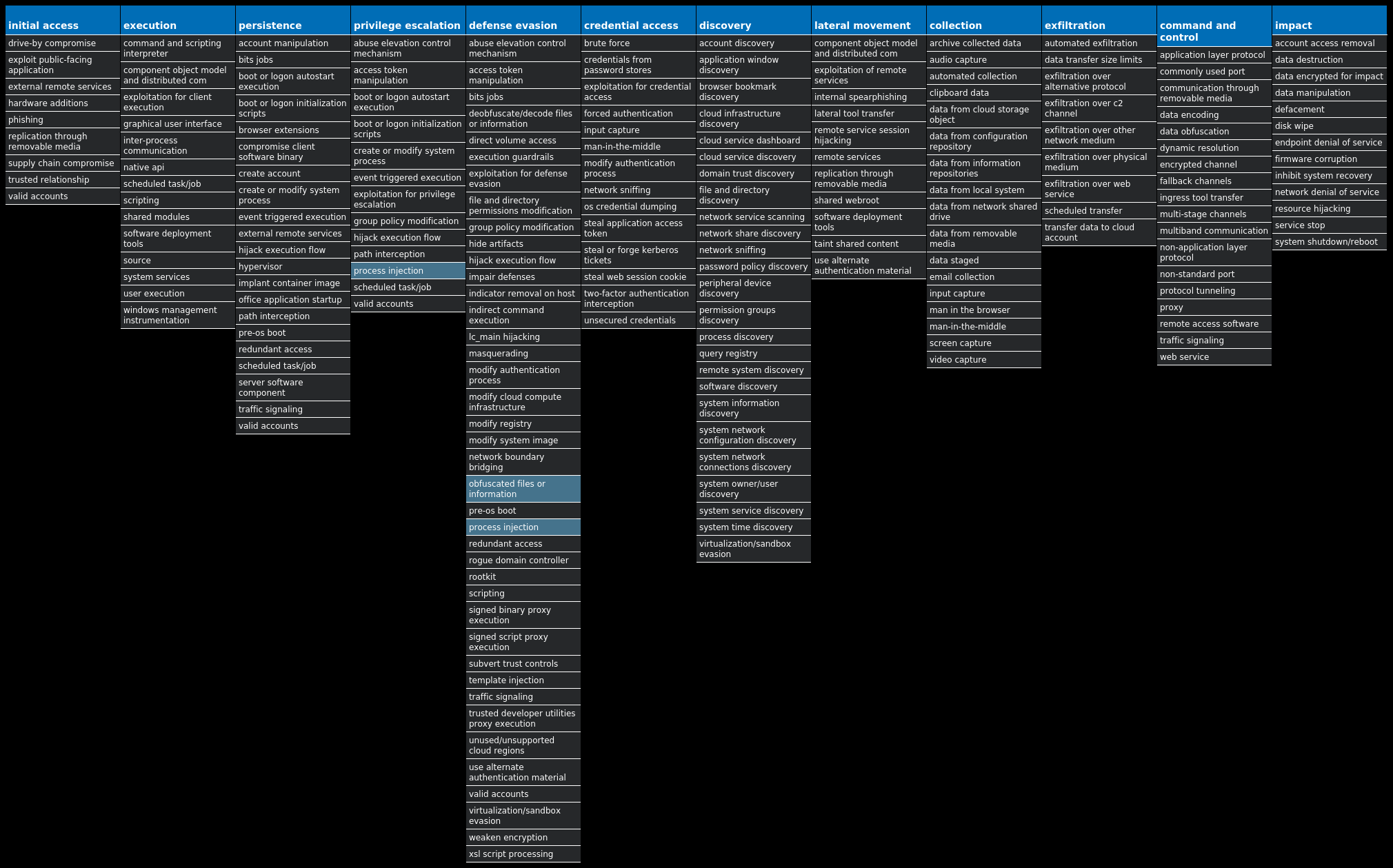
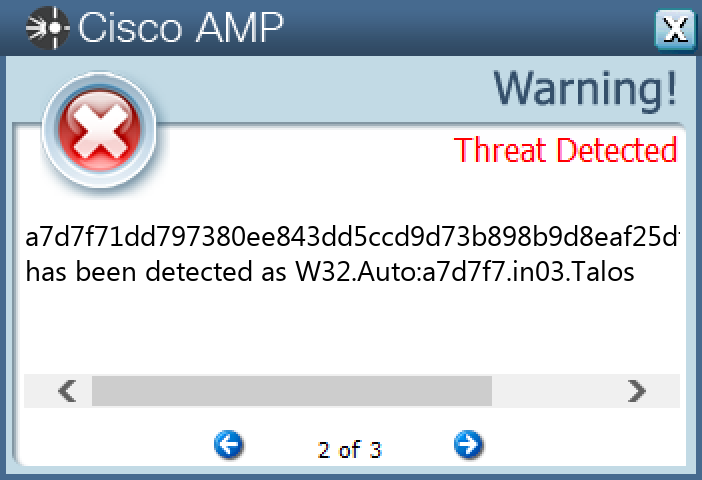
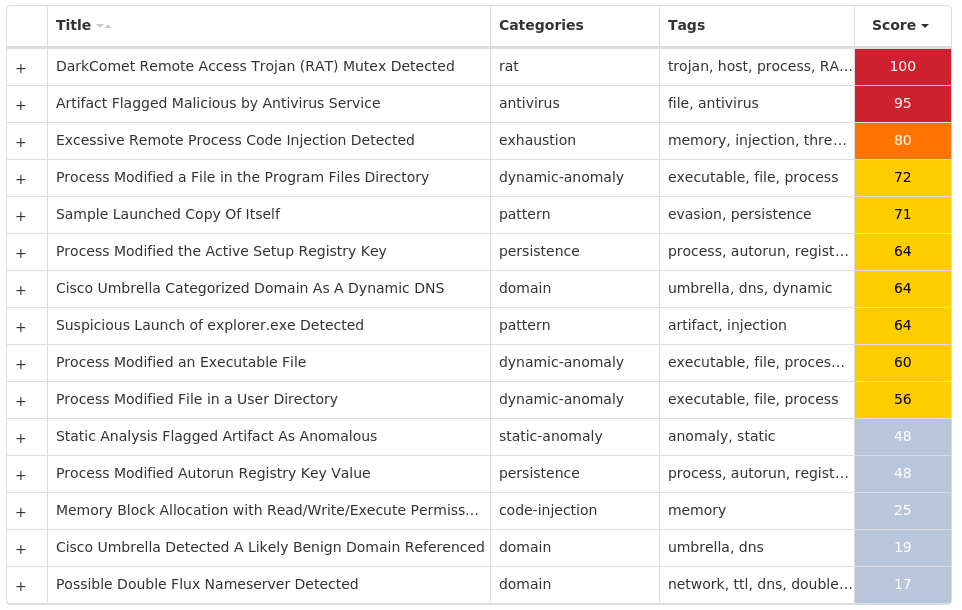
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Downloader.Upatre-10011416-0 Indicators of Compromise IOCs collected from dynamic analysis of 30 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\STARTPAGE Value Name: StartMenu_Balloon_Time 2
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 185[.]211[.]22[.]24229 23[.]205[.]105[.]15710 23[.]205[.]105[.]16910 23[.]205[.]105[.]1536 23[.]205[.]105[.]1462 23[.]219[.]154[.]1361
Domain Names contacted by malware. Does not indicate maliciousness Occurrences apps[.]identrust[.]com29 salahicorp[.]com29 ren7oaks[.]co[.]uk29
Files and or directories created Occurrences %TEMP%\budha.exe30
File Hashes 01d39073e8023b463aeeb09d7d745b79fd4d1d570448c41e1fbe290e4c24220e
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Packed.CoinMiner-10011305-1 Indicators of Compromise IOCs collected from dynamic analysis of 17 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\STARTPAGE Value Name: StartMenu_Balloon_Time 1
Mutexes Occurrences atwimjbzqckrcqbp17 Global\atwimjbzqckrcqbp17
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 142[.]202[.]242[.]4510 142[.]202[.]242[.]437
Domain Names contacted by malware. Does not indicate maliciousness Occurrences pool[.]hashvault[.]pro17
Files and or directories created Occurrences %APPDATA%\Google17 %APPDATA%\Google\Libs17 %APPDATA%\Google\Libs\WR64.sys17 %TEMP%\qdorobglftsq.tmp17
File Hashes 0418cdb7929843bb178117edceb2da83d7e5b2324102160d89b0501a2f98bbfd
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
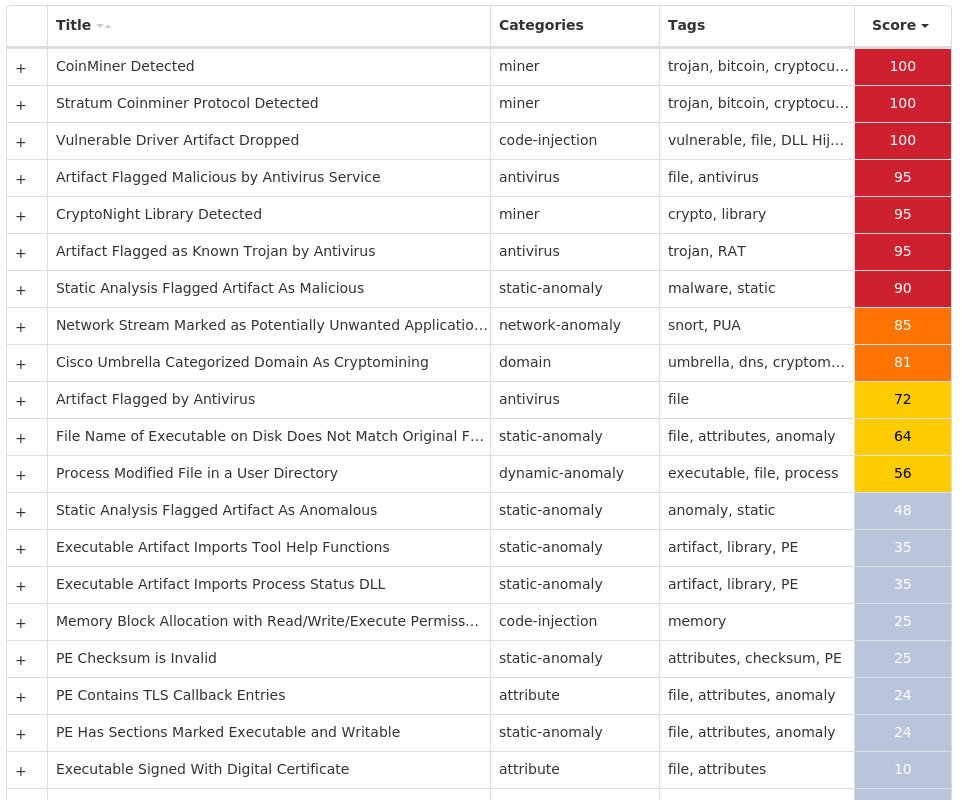
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.Remcos-10011195-0 Indicators of Compromise IOCs collected from dynamic analysis of 28 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: hpsupportdf 6 \SOFTWARE\HPSUPPORTA-3474R7 Value Name: exepath 6 \SOFTWARE\HPSUPPORTA-3474R7 Value Name: licence 6 \SOFTWARE\HPSUPPORTA-3474R7 6 \SOFTWARE\WINRAR 3 \SAM\SAM\DOMAINS\ACCOUNT\USERS\000003E9 Value Name: F 3 \SAM\SAM\DOMAINS\ACCOUNT\USERS\000001F5 Value Name: F 3 \SAM\SAM\DOMAINS\ACCOUNT\USERS\000003EC Value Name: F 3 \SOFTWARE\WINRAR Value Name: HWID 3 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: remcos 2 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: NetWire 2 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN 1 \SOFTWARE\MICROSOFT\INTERNET EXPLORER\INTELLIFORMS\STORAGE2 1 \SOFTWARE\WOW6432NODE\MOZILLA\MOZILLA FIREFOX 1 \SOFTWARE\WOW6432NODE\MOZILLA\MOZILLA FIREFOX\20.0.1 (EN-US)\MAIN 1 \SOFTWARE\WOW6432NODE\MOZILLA\MOZILLA THUNDERBIRD 1 \SOFTWARE\NETWIRE 1 \SOFTWARE\REMCOS_UAGFTAAWDGTKFLY Value Name: EXEpath 1 \SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{4KUJJ476-38ES-RCMH-QGW0-22030L368G76} Value Name: StubPath 1 \SOFTWARE\NETWIRE Value Name: HostId 1 \SOFTWARE\REMCOS_MPGOQKDCERXZZVE Value Name: EXEpath 1 \SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{4KUJJ476-38ES-RCMH-QGW0-22030L368G76} 1 \SOFTWARE\REMCOS_MPGOQKDCERXZZVE 1 \SOFTWARE\REMCOS_UAGFTAAWDGTKFLY 1 \SOFTWARE\NETWIRE Value Name: Install Date 1
Mutexes Occurrences Remcos_Mutex_Inj8 hpsupporta-3474R76 8-3503835SZBFHHZ1 remcos_uagftaawdgtkfly1 remcos_mpgoqkdcerxzzve1 5-7-7D18-X4vYDyz1 S-1-5-21-2580483-124428895676401 S-1-5-21-2580483-158835515888701
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 216[.]218[.]135[.]1186 192[.]169[.]69[.]254 61[.]139[.]126[.]541
Domain Names contacted by malware. Does not indicate maliciousness Occurrences teryts1802[.]sytes[.]net6 onelove03[.]duckdns[.]org1 fucktoto[.]duckdns[.]org1 drantvenaco[.]xyz1 www[.]hydzjg[.]com1 www[.]verysinr[.]com1 ebuxxxxx[.]duckdns[.]org1 tunedd30[.]duckdns[.]org1 www[.]salesnjinn[.]com1 www[.]christianroyaltyapparel[.]com1 www[.]augiticmisknow[.]party1 www[.]aow85[.]com1 www[.]horizonenterprisediscovery[.]com1 onlygoodm[.]com1
Files and or directories created Occurrences %TEMP%\install.vbs6 %APPDATA%\hpsupportl6 %APPDATA%\hpsupportl\logs.dat6 %APPDATA%\hpsupportk6 %APPDATA%\hpsupportk\hpsupportw.exe6 %APPDATA%\remcos2 %APPDATA%\remcos\logs.dat2 %APPDATA%\remcos\remcos.exe2 %APPDATA%\Install2 %APPDATA%\Install\Host.exe2 %TEMP%\install.bat2 %HOMEPATH%\file1 %HOMEPATH%\file\bin.exe1 %HOMEPATH%\file\bin.vbs1 %APPDATA%\5-7-7D181 %APPDATA%\5-7-7D18\5-7log.ini1 %APPDATA%\5-7-7D18\5-7logim.jpeg1 %APPDATA%\5-7-7D18\5-7logrc.ini1 %APPDATA%\5-7-7D18\5-7logri.ini1 %APPDATA%\5-7-7D18\5-7logrv.ini1 %ProgramFiles(x86)%\Lwbphud1 %TEMP%\Lwbphud1 %ProgramFiles(x86)%\Lwbphud\IconCacheojphll2x.exe1 %TEMP%\Lwbphud\IconCacheojphll2x.exe1 %TEMP%\1514536984.bat1
*See JSON for more IOCs
File Hashes 05981c05db85bd1116054ef5e99c5df384ac5c35ff79b76acffd6a99e7aca657
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
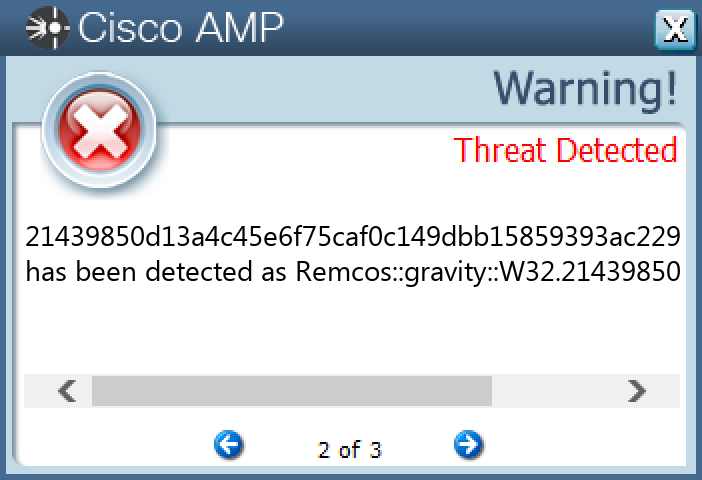
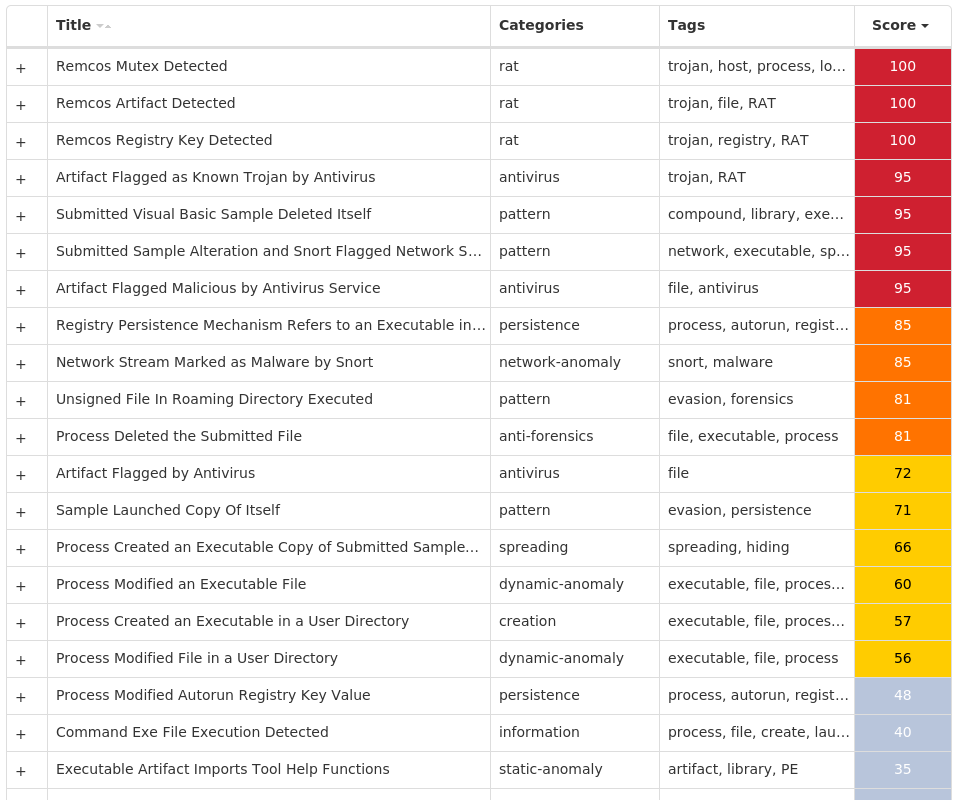
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Malware.Zusy-10010855-0 Indicators of Compromise IOCs collected from dynamic analysis of 25 samples IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 128[.]1[.]157[.]224/3017 128[.]1[.]157[.]2284 61[.]170[.]77[.]234/314 128[.]1[.]157[.]230/314 222[.]73[.]33[.]2092 114[.]80[.]179[.]2422 61[.]170[.]81[.]2502 101[.]226[.]26[.]134/312 101[.]226[.]26[.]136/312 61[.]170[.]77[.]2301 61[.]170[.]81[.]2041 101[.]226[.]26[.]1401 114[.]80[.]179[.]2151 114[.]80[.]179[.]2111 61[.]170[.]77[.]2291 101[.]226[.]26[.]1281 61[.]170[.]81[.]2151 61[.]170[.]77[.]2361 61[.]170[.]81[.]2341 222[.]73[.]33[.]2121
Domain Names contacted by malware. Does not indicate maliciousness Occurrences bucket-ynote-online-cdn[.]note[.]youdao[.]com25 note[.]youdao[.]com25
Files and or directories created Occurrences \TEMP\code.dll25 %TEMP%\1063874369\....1 %TEMP%\13977118451 %TEMP%\1397711845\....1 %TEMP%\13977117511 %TEMP%\1397711751\....1 %TEMP%\13977093171 %TEMP%\1397709317\....1 %TEMP%\13977083191 %TEMP%\1397708319\....1 %TEMP%\13977122501 %TEMP%\1397712250\....1 %TEMP%\13977093481 %TEMP%\1397709348\....1 %TEMP%\13977118601 %TEMP%\1397711860\....1 %TEMP%\13977126711 %TEMP%\1397712671\....1 %TEMP%\13977131391 %TEMP%\1397713139\....1 %TEMP%\13977138411 %TEMP%\1397713841\....1 %TEMP%\13977104091 %TEMP%\1397710409\....1 %TEMP%\13977129991
*See JSON for more IOCs
File Hashes 01cc53c302446a2e15a7b7a7a74916f046b4fd33065ef243fbffacd95766d459
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Packed.AgentTesla-10010785-1 Indicators of Compromise IOCs collected from dynamic analysis of 16 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\MULTIMEDIA\DRAWDIB 9 \SOFTWARE\MICROSOFT\MULTIMEDIA\DRAWDIB Value Name: 1152x864x32(BGR 0) 9 \SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: AGP Manager 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 Value Name: EnableFileTracing 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 Value Name: EnableConsoleTracing 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 Value Name: FileTracingMask 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 Value Name: ConsoleTracingMask 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 Value Name: MaxFileSize 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 Value Name: FileDirectory 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS Value Name: EnableFileTracing 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS Value Name: EnableConsoleTracing 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS Value Name: FileTracingMask 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS Value Name: ConsoleTracingMask 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS Value Name: MaxFileSize 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS Value Name: FileDirectory 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASAPI32 1 \SOFTWARE\WOW6432NODE\MICROSOFT\TRACING\_RASMANCS 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: MyOtApp 1
Mutexes Occurrences HMYAYDAVR5GSQKT8N5DJ1 Global\{691d653b-e3fd-4576-a193-64407d29eeee}1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 193[.]122[.]130[.]04 132[.]226[.]8[.]1694 193[.]122[.]6[.]1683 172[.]67[.]69[.]963 162[.]213[.]251[.]1342 149[.]154[.]167[.]2201 185[.]199[.]111[.]1331 45[.]67[.]228[.]511 158[.]101[.]44[.]2421 104[.]26[.]10[.]891 104[.]26[.]11[.]891 172[.]67[.]150[.]791 89[.]47[.]1[.]101
Domain Names contacted by malware. Does not indicate maliciousness Occurrences checkip[.]dyndns[.]org9 dispatchweekly[.]com5 kenesrakishev[.]net2 rakishev[.]net2 raw[.]githubusercontent[.]com1 api[.]telegram[.]org1
Files and or directories created Occurrences %APPDATA%\ScreenShot9 %APPDATA%\ScreenShot\screen.jpeg9 %ProgramFiles(x86)%\AGP Manager1 %ProgramFiles(x86)%\AGP Manager\agpmgr.exe1 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C51 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\Logs1 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\Logs\Administrator1 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\run.dat1 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\task.dat1 %System32%\Tasks\AGP Manager1 %System32%\Tasks\AGP Manager Task1 \TEMP\DotNetZip.dll1 %TEMP%\tmp791.tmp1 %APPDATA%\Adobe\R.exe1 %TEMP%\V8.exe1 %APPDATA%\Adobe\2.exe1 %APPDATA%\Adobe\.exe1 %APPDATA%\audddd1 %ProgramData%\Application Data\GL.exe1 %ProgramData%\Start Menu\9H6RQHZI64J.exe1 %ProgramData%\Microsoft\Windows\Start Menu\9H6RQHZI64J.exe1 %ProgramData%\GL.exe1 %APPDATA%\Identities\OIX.exe1 %LOCALAPPDATA%\7a5d2bcb028d0c29c6ab36d358820c4b1 %TEMP%\tmp6D17.tmp1
*See JSON for more IOCs
File Hashes 00515fe91a6b40d5c5ae851cb18d31c675ff38901edd352b3e6379087d5f2b26
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
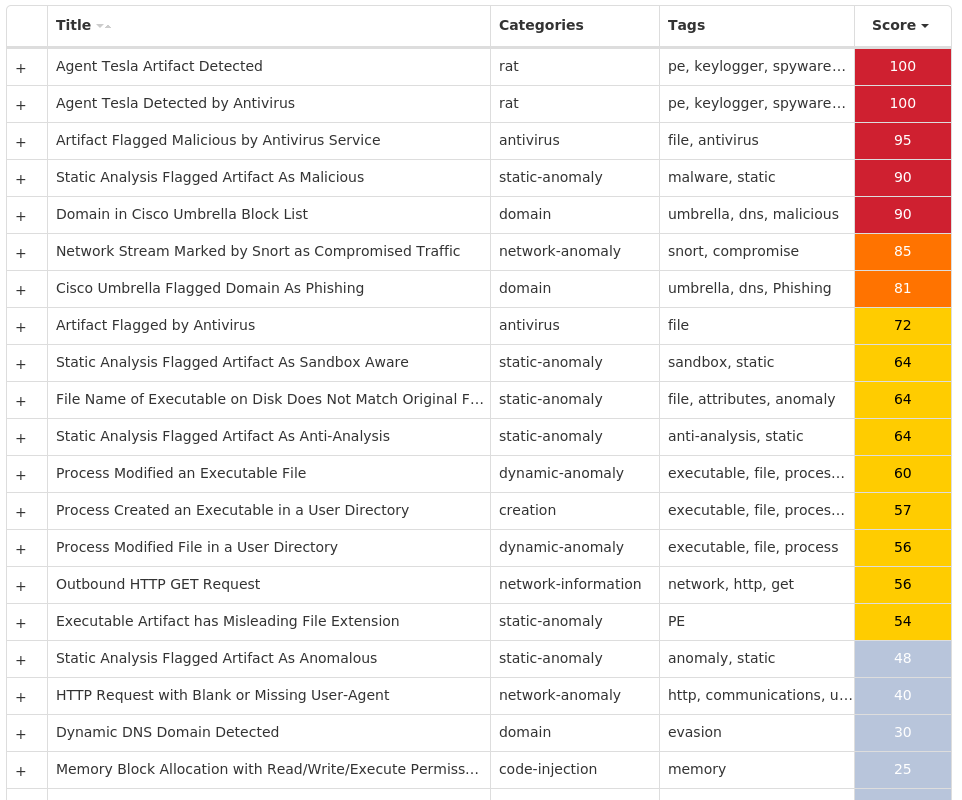
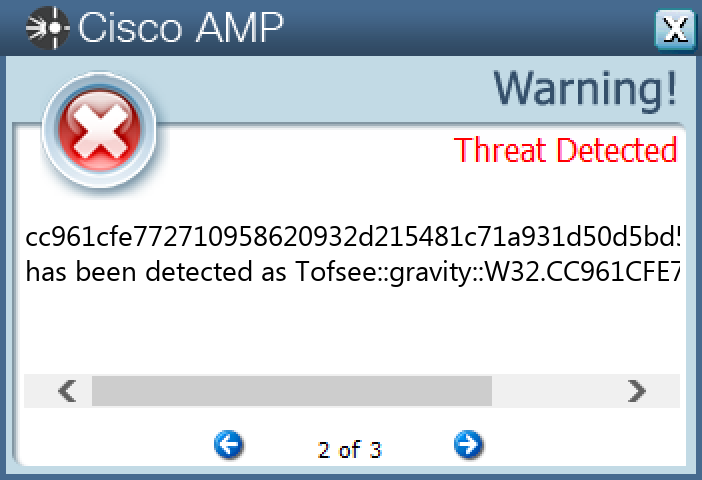
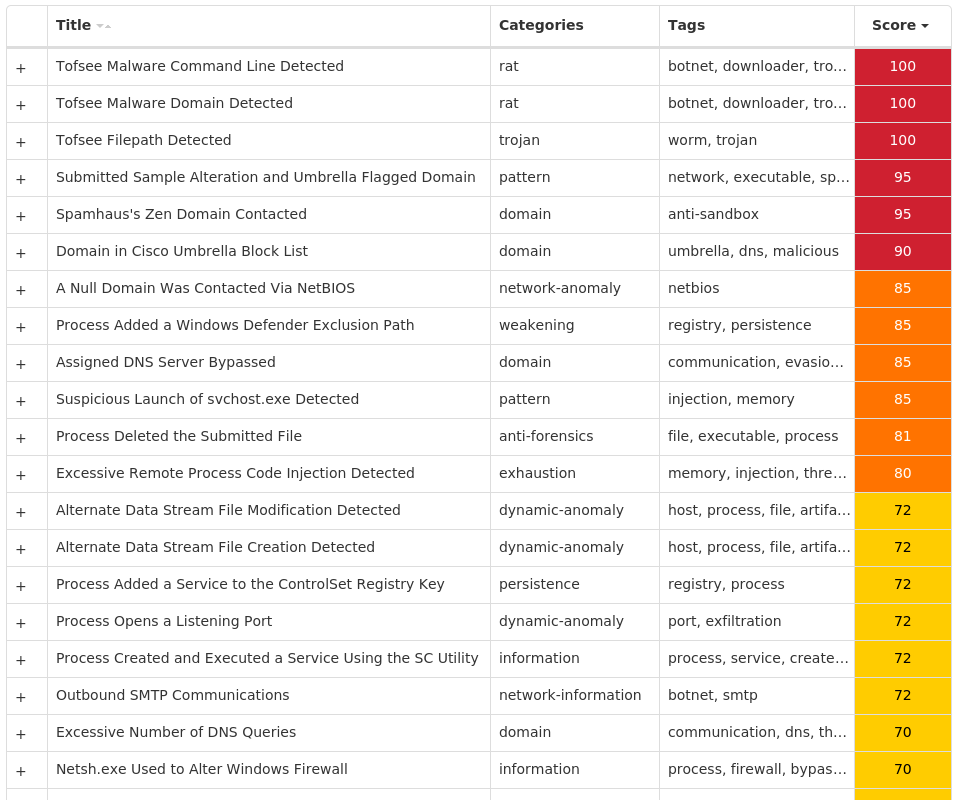
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Trojan.Tofsee-10010766-0 Indicators of Compromise IOCs collected from dynamic analysis of 17 samples Registry Keys Occurrences \SYSTEM\CONTROLSET001\SERVICES\ 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: Type 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: Start 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: ErrorControl 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: DisplayName 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: WOW64 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: ObjectName 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: ImagePath 14 \SYSTEM\CONTROLSET001\SERVICES\ Value Name: Description 12 \.DEFAULT\CONTROL PANEL\BUSES 11 \.DEFAULT\CONTROL PANEL\BUSES Value Name: Config2 11 \.DEFAULT\CONTROL PANEL\BUSES Value Name: Config0 11 \.DEFAULT\CONTROL PANEL\BUSES Value Name: Config1 11 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\isupldcy 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\vfhcyqpl 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\mwytphgc 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\fprmiazv 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\jtvqmedz 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\gqsnjbaw 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\tdfawonj 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\xhjeasrn 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\blniewvr 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\lvxsogfb 1 \SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHS Value Name: C:\Windows\SysWOW64\uegbxpok 1
Mutexes Occurrences SlimeLoveAllTheTime1 Global\439f74e1-67b1-11ee-9660-001517b0163a1 Global\1352bd61-6914-11ee-9660-0015174ac6a11 Global\15b95d21-6914-11ee-9660-0015175f9dd61
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 176[.]113[.]115[.]13614 80[.]66[.]75[.]414 176[.]113[.]115[.]13514 45[.]143[.]201[.]23814 62[.]122[.]184[.]9214 176[.]113[.]115[.]84/3114 62[.]122[.]184[.]5814 193[.]106[.]174[.]22014 142[.]250[.]80[.]6810 31[.]13[.]65[.]528 149[.]154[.]167[.]997 142[.]250[.]65[.]2277 93[.]115[.]25[.]497 93[.]115[.]25[.]737 31[.]13[.]65[.]1745 142[.]250[.]80[.]675 93[.]115[.]25[.]135 93[.]115[.]25[.]105 20[.]231[.]239[.]2465 93[.]115[.]25[.]1104 23[.]200[.]98[.]584 104[.]75[.]113[.]1004 34[.]120[.]241[.]2144 34[.]117[.]59[.]813 142[.]250[.]74[.]683
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences 249[.]5[.]55[.]69[.]in-addr[.]arpa14 www[.]google[.]com14 vanaheim[.]cn14 249[.]5[.]55[.]69[.]bl[.]spamcop[.]net11 249[.]5[.]55[.]69[.]cbl[.]abuseat[.]org11 249[.]5[.]55[.]69[.]dnsbl[.]sorbs[.]net11 249[.]5[.]55[.]69[.]sbl-xbl[.]spamhaus[.]org11 249[.]5[.]55[.]69[.]zen[.]spamhaus[.]org11 microsoft-com[.]mail[.]protection[.]outlook[.]com11 microsoft[.]com11 i[.]instagram[.]com8 www[.]google[.]es7 t[.]me7 steamcommunity[.]com7 api[.]steampowered[.]com7 www[.]instagram[.]com5 api[.]vk[.]com5 www[.]amazon[.]co[.]uk4 www[.]evernote[.]com4 ok[.]ru4 www[.]google[.]fr3 www[.]tiktok[.]com3 imap[.]rambler[.]ru3 www[.]yahoo[.]com2 www[.]google[.]com[.]au2
*See JSON for more IOCs
Files and or directories created Occurrences %SystemRoot%\SysWOW64\14 %TEMP%\.exe 13 %SystemRoot%\SysWOW64\config\systemprofile11 %SystemRoot%\SysWOW64\config\systemprofile:.repos11 %HOMEPATH%\AppData\LocalLow\sqlite3.dll1 %HOMEPATH%\AppData\LocalLow\freebl3.dll1 %HOMEPATH%\AppData\LocalLow\mozglue.dll1 %HOMEPATH%\AppData\LocalLow\msvcp140.dll1 %HOMEPATH%\AppData\LocalLow\nss3.dll1 %HOMEPATH%\AppData\LocalLow\softokn3.dll1 %HOMEPATH%\AppData\LocalLow\vcruntime140.dll1 %TEMP%\lualjyq.exe1 %HOMEPATH%\AppData\LocalLow\1T95Ye0aeftg1 %HOMEPATH%\AppData\LocalLow\1T95Ye0aeftg-shm1 %HOMEPATH%\AppData\LocalLow\1T95Ye0aeftg-wal1 %HOMEPATH%\AppData\LocalLow\7th8d2Q2U9801 %HOMEPATH%\AppData\LocalLow\EZi3W6aEj1e51
File Hashes 0c018ba0c0b75323b87ec3f55c6ed7302549b56e1ebd5b7c70c8a33fc6c5a65e
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
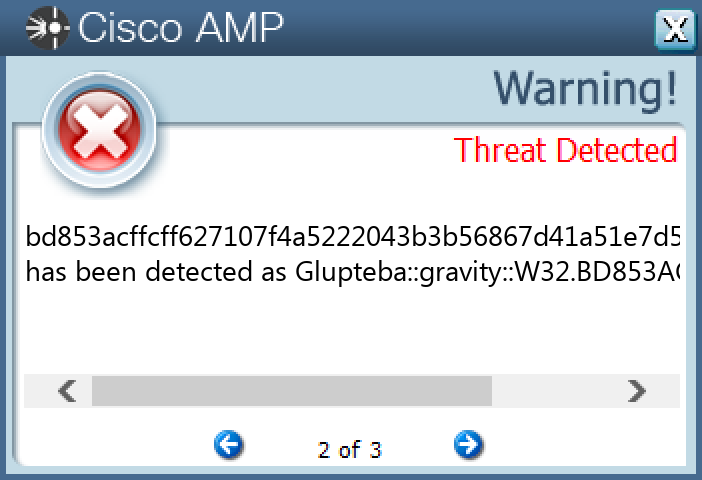
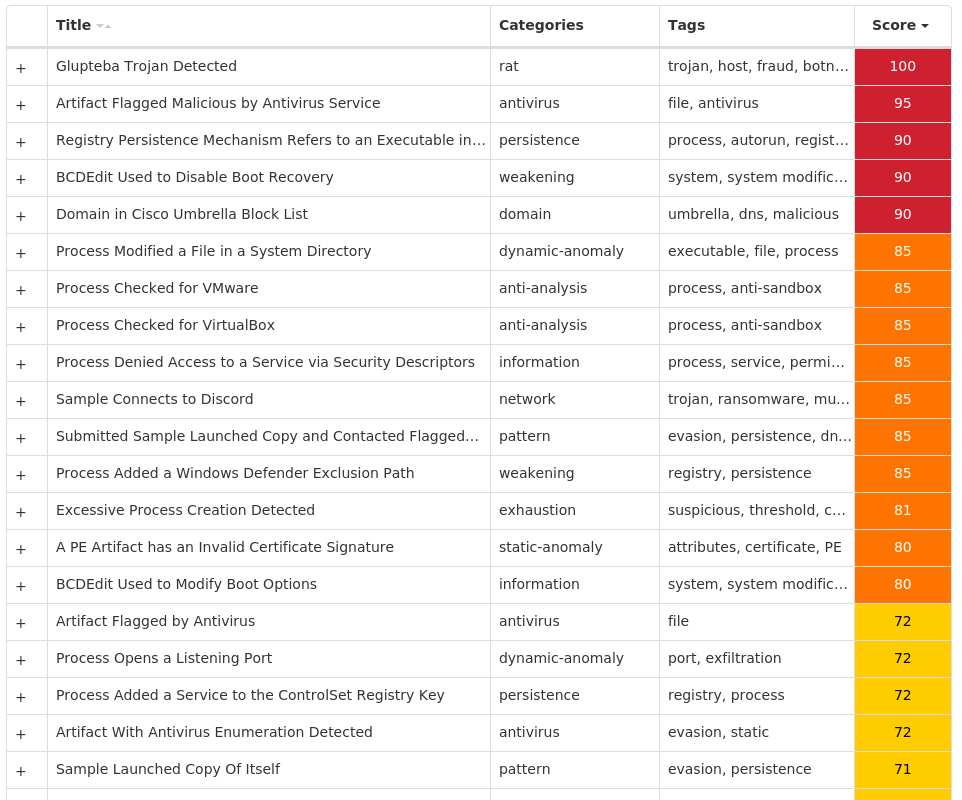
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.Glupteba-10010808-0 Indicators of Compromise IOCs collected from dynamic analysis of 13 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\A1890984 Value Name: PatchTime 12 \SOFTWARE\MICROSOFT\A1890984 Value Name: PGDSE 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXWDDM Value Name: DisplayName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXWDDM Value Name: WOW64 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXWDDM Value Name: ObjectName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: Type 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: Start 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: ErrorControl 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: ImagePath 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: DisplayName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: WOW64 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXSF Value Name: ObjectName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: Type 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: Start 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: ErrorControl 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: ImagePath 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: DisplayName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: WOW64 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXMOUSE Value Name: ObjectName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXGUEST Value Name: Type 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXGUEST Value Name: Start 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXGUEST Value Name: ErrorControl 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXGUEST Value Name: ImagePath 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXGUEST Value Name: DisplayName 12 \SYSTEM\CONTROLSET001\SERVICES\VBOXGUEST Value Name: WOW64 12
Mutexes Occurrences Global\SetupLog12 Global\WdsSetupLogInit12 Global\h48yorbq6rm87zot12 WininetConnectionMutex12 Global\qtxp9g8w12 Global\xmrigMUTEX313372 Global\923de961-62ac-11ee-9660-001517289b0f1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 204[.]79[.]197[.]21912 172[.]67[.]212[.]18810 20[.]150[.]38[.]2289 185[.]82[.]216[.]48/318 20[.]150[.]79[.]686 162[.]159[.]135[.]2334 172[.]253[.]120[.]1274 162[.]159[.]129[.]2333 74[.]125[.]128[.]1273 185[.]82[.]216[.]503 162[.]159[.]130[.]2332 162[.]159[.]134[.]2332 20[.]150[.]70[.]362 142[.]250[.]144[.]1272 104[.]21[.]23[.]1842 162[.]159[.]133[.]2331 142[.]250[.]15[.]1271 142[.]250[.]112[.]1271 3[.]33[.]249[.]2481 185[.]82[.]216[.]651 173[.]214[.]169[.]171 178[.]236[.]247[.]2321
Domain Names contacted by malware. Does not indicate maliciousness Occurrences msdl[.]microsoft[.]com12 vsblobprodscussu5shard35[.]blob[.]core[.]windows[.]net12 vsblobprodscussu5shard60[.]blob[.]core[.]windows[.]net12 cdn[.]discordapp[.]com12 walkinglate[.]com12 stun3[.]l[.]google[.]com4 stun[.]stunprotocol[.]org3 stun4[.]l[.]google[.]com3 79102df1-5f9d-4ca9-bdf6-1fa1060285b4[.]uuid[.]mypushtimes[.]net3 stun2[.]l[.]google[.]com2 server9[.]mypushtimes[.]net2 79102df1-5f9d-4ca9-bdf6-1fa1060285b4[.]uuid[.]haoshuruzhiyou[.]co[.]in2 79102df1-5f9d-4ca9-bdf6-1fa1060285b4[.]uuid[.]cdntokiog[.]studio2 stun[.]sipgate[.]net1 stun[.]l[.]google[.]com1 stun1[.]l[.]google[.]com1 server1[.]zaoshanghao[.]su1 server13[.]cdntokiog[.]studio1 79102df1-5f9d-4ca9-bdf6-1fa1060285b4[.]uuid[.]zaoshang[.]ru1 79102df1-5f9d-4ca9-bdf6-1fa1060285b4[.]uuid[.]zaoshanghao[.]su1 server6[.]safarimexican[.]net1 server6[.]haoshuruzhiyou[.]co[.]in1 79102df1-5f9d-4ca9-bdf6-1fa1060285b4[.]uuid[.]safarimexican[.]net1 server16[.]zaoshang[.]ru1 server1[.]haoshuruzhiyou[.]co[.]in1
*See JSON for more IOCs
Files and or directories created Occurrences %SystemRoot%\Logs\CBS\CBS.log12 %SystemRoot%\rss12 %SystemRoot%\rss\csrss.exe12 %TEMP%\csrss12 %TEMP%\csrss\dsefix.exe12 %TEMP%\csrss\patch.exe12 %System32%\drivers\Winmon.sys12 %System32%\drivers\WinmonFS.sys12 %System32%\drivers\WinmonProcessMonitor.sys12 %SystemRoot%\windefender.exe12 %TEMP%\Symbols12 %TEMP%\Symbols\ntkrnlmp.pdb12 %TEMP%\Symbols\ntkrnlmp.pdb\9E22A5947A15489895CE716436B45BE0212 %TEMP%\Symbols\ntkrnlmp.pdb\9E22A5947A15489895CE716436B45BE02\download.error12 %TEMP%\Symbols\pingme.txt12 %TEMP%\Symbols\winload_prod.pdb12 %TEMP%\Symbols\winload_prod.pdb\B7B16B17E078406E806A050C8BEE2E36112 %TEMP%\Symbols\winload_prod.pdb\B7B16B17E078406E806A050C8BEE2E361\download.error12 %TEMP%\dbghelp.dll12 %TEMP%\ntkrnlmp.exe12 %TEMP%\osloader.exe12 %TEMP%\symsrv.dll12 %TEMP%\csrss\DBG0.tmp12 %System32%\Tasks\csrss12 %TEMP%\csrss\injector12
*See JSON for more IOCs
File Hashes 086371131dd2487c7dbb05bc1e67afb2d18e85df7f54facecf8b04490fd269b2
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
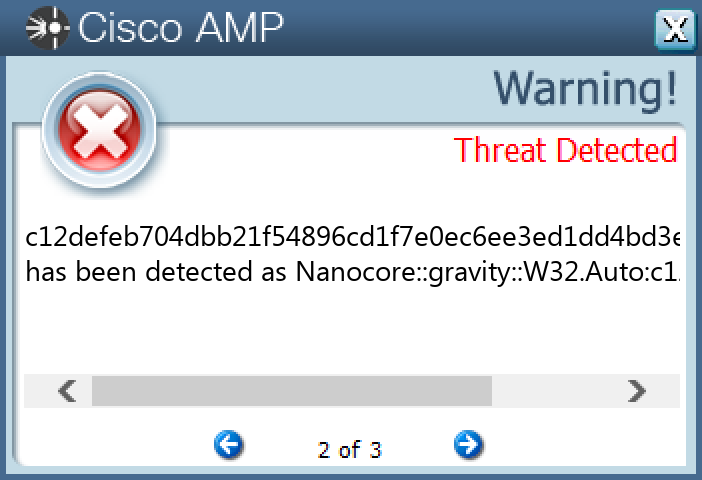
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.Nanocore-10011208-0 Indicators of Compromise IOCs collected from dynamic analysis of 25 samples Registry Keys Occurrences \SOFTWARE\WINRAR 6 \SAM\SAM\DOMAINS\ACCOUNT\USERS\000003E9 Value Name: F 6 \SAM\SAM\DOMAINS\ACCOUNT\USERS\000001F5 Value Name: F 6 \SAM\SAM\DOMAINS\ACCOUNT\USERS\000003EC Value Name: F 6 \SOFTWARE\WINRAR Value Name: HWID 6 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: hpsupportdf 4 \SOFTWARE\HPSUPPORTA-0NMJO7 Value Name: exepath 4 \SOFTWARE\HPSUPPORTA-0NMJO7 Value Name: licence 4 \SOFTWARE\HPSUPPORTA-0NMJO7 4 \SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: AGP Manager 3 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: NetWire 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: hpsupport 1 \SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON Value Name: Userinit 1 \SOFTWARE\NETWIRE 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN Value Name: 5J-XUFWH2T 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: chrome 1 \SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{R7881T2L-5Q6O-A6AF-YTOP-UR6LGAD671YS} Value Name: StubPath 1 \SOFTWARE\NETWIRE Value Name: HostId 1 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: Registry Key Name 1 \SOFTWARE\REMCOS_XOQLVKOBZX 1 \SOFTWARE\REMCOS_XOQLVKOBZX Value Name: EXEpath 1 \SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{R7881T2L-5Q6O-A6AF-YTOP-UR6LGAD671YS} 1 \SOFTWARE\NETWIRE Value Name: Install Date 1 \SOFTWARE\HPSUPPORT-14R0XW 1 \SOFTWARE\HPSUPPORT-14R0XW Value Name: exepath 1
Mutexes Occurrences Remcos_Mutex_Inj6 hpsupporta-0NMJO74 8-3503835SZBFHHZ1 7433cdb324b04dd5e3c3db213381216c7c539baa1 J14-9347TBE693E51 remcos_xoqlvkobzx1 hpsupport-14R0XW1
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 203[.]170[.]80[.]2501 213[.]186[.]33[.]51 192[.]169[.]69[.]251 91[.]195[.]240[.]1261 5[.]79[.]68[.]1071 65[.]99[.]252[.]2161 204[.]152[.]219[.]981 79[.]134[.]225[.]171 39[.]96[.]26[.]1451 198[.]187[.]30[.]1871 199[.]80[.]53[.]281 194[.]5[.]98[.]831 194[.]5[.]98[.]811 37[.]49[.]224[.]1721 34[.]237[.]212[.]1271 44[.]219[.]130[.]1551
Domain Names contacted by malware. Does not indicate maliciousness Occurrences manafuuh[.]ddns[.]net4 checkip[.]amazonaws[.]com2 www[.]gedhang[.]win1 www[.]regular123[.]com1 www[.]centronasser[.]com1 www[.]sondcn[.]com1 www[.]techotakus[.]com1 www[.]oligo-le-nuton[.]com1 www[.]hobonichidouga[.]com1 www[.]spasence[.]online1 www[.]lovendwild[.]com1 www[.]urgamesim[.]com1 www[.]1tzae[.]top1 www[.]coincoin9[.]com1 onlygoodm[.]com1 rezkathryn289[.]ddns[.]net1 ben1234[.]duckdns[.]org1 cepastr[.]ddns[.]net1 oluebebchi[.]duckdns[.]org1 locash[.]hopto[.]org1
Files and or directories created Occurrences %TEMP%\install.vbs5 %APPDATA%\hpsupportl4 %APPDATA%\hpsupportl\logs.dat4 %APPDATA%\hpsupportk4 %APPDATA%\hpsupportk\hpsupportw.exe4 %ProgramFiles(x86)%\AGP Manager3 %ProgramFiles(x86)%\AGP Manager\agpmgr.exe3 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C53 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\Logs3 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\Logs\Administrator3 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\run.dat3 %HOMEPATH%\subfolder\filename.exe1 %HOMEPATH%\subfolder\filename.vbs1 %APPDATA%\D19AB989-A35F-4710-83DF-7B2DB7EFE7C5\task.dat1 %System32%\Tasks\AGP Manager1 %System32%\Tasks\AGP Manager Task1 %APPDATA%\Install\Host.exe1 %TEMP%\install.bat1 %APPDATA%\chrome1 %APPDATA%\chrome\chrome.exe1 %ProgramData%\7433cdb324b04dd5e3c3db213381216c7c539baa1 %APPDATA%\hpsupport1 %APPDATA%\hpsupport\hpsupport.exe1 %APPDATA%\hpsupport\logs.dat1 %ProgramFiles(x86)%\Lqdfp\systrayzt48dxy8.exe1
*See JSON for more IOCs
File Hashes 00c935c3cf87816fd66654a66a5e3ec1a40674eabaf05b65082190e1a1bd55e4
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA
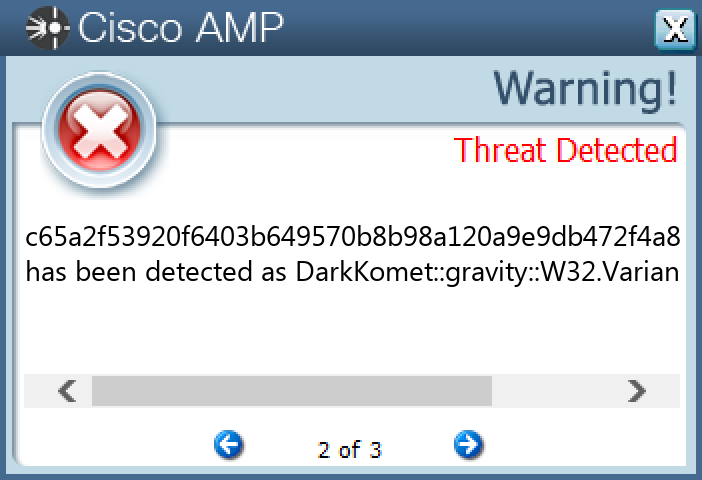
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Dropper.DarkComet-10011490-1 Indicators of Compromise IOCs collected from dynamic analysis of 27 samples Registry Keys Occurrences \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN 27 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN 27 \SOFTWARE\LOCAL APPWIZARD-GENERATED APPLICATIONS 27 \SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{1ONY8XDG-DX6S-CQ0K-8R1G-272WTPXC6H5P} 27 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN Value Name: Policies 27 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN Value Name: Policies 27 \SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: HKLM 27 \SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN Value Name: HKCM 27 \SOFTWARE\WOW6432NODE\MICROSOFT\ACTIVE SETUP\INSTALLED COMPONENTS\{1ONY8XDG-DX6S-CQ0K-8R1G-272WTPXC6H5P} Value Name: StubPath 27 \SOFTWARE\NOTEPAD 27 \SOFTWARE\NOTEPAD Value Name: NewIdentification 27 \SOFTWARE\NOTEPAD Value Name: FirstExecution 27 \SOFTWARE\MICROSOFT Value Name: PIDprocess 27
Mutexes Occurrences _x_X_BLOCKMOUSE_X_x_27 _x_X_PASSWORDLIST_X_x_27 _x_X_UPDATE_X_x_27 _y_X_PASSWORDLIST_X_y_27 JoKeR_MaSK_SEMUTEX27 lass27 lass_PERSIST27 lass_SAIR27 GREAME_RAT-_-MUTEX27
Domain Names contacted by malware. Does not indicate maliciousness Occurrences tigersa[.]no-ip[.]biz27
Files and or directories created Occurrences %APPDATA%\logs.dat27 %TEMP%\X-GRY-X.txt27 %ProgramFiles(x86)%\windows27 %TEMP%\GRY-XX-X27 %TEMP%\uU-GRY-Xx27 %ProgramFiles(x86)%\windows\lass.exe27
File Hashes 01b01c090edaec7b0cfd0b6354c66e696130f484edbe71b730d63f8d941f71a1
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
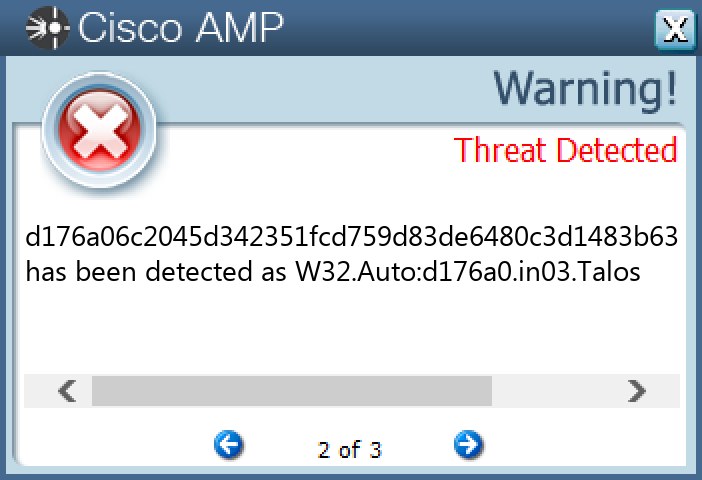
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK