Talos is publishing a glimpse into the most prevalent threats we've observed from July 22 - 29. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting key behavioral characteristics, indicators of compromise and discussing how our customers are automatically protected from these threats.
As a reminder, the information provided for the following threats in this post is non-exhaustive and current as of the date of publication. Additionally, please keep in mind that IOC searching is only one part of threat hunting. Spotting a single IOC does not necessarily indicate maliciousness. Detection and coverage for the following threats is subject to updates, pending additional threat or vulnerability analysis. For the most current information, please refer to your Firepower Management Center, Snort.org , or ClamAV.net .
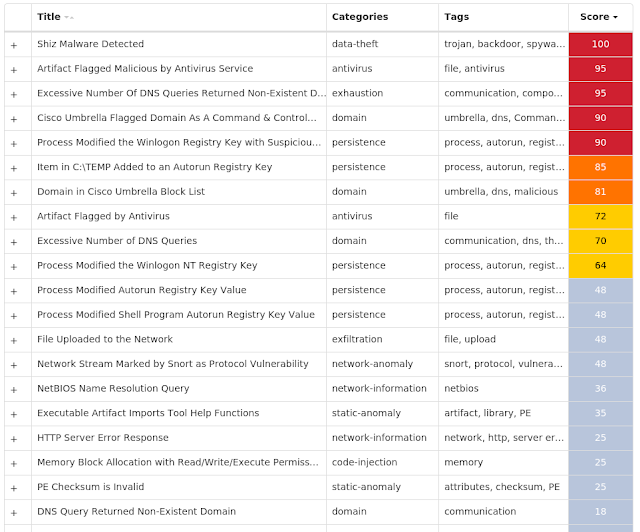
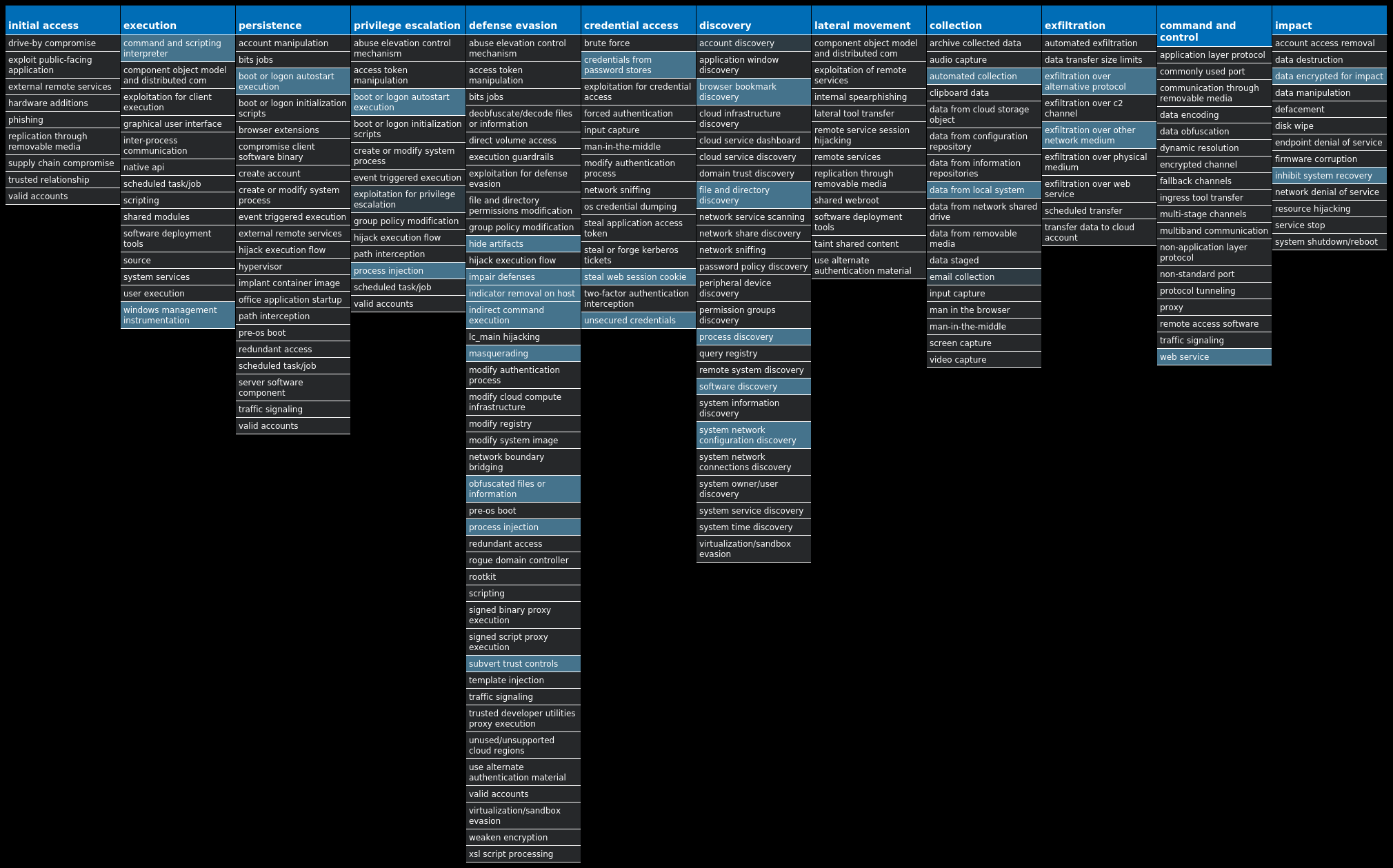
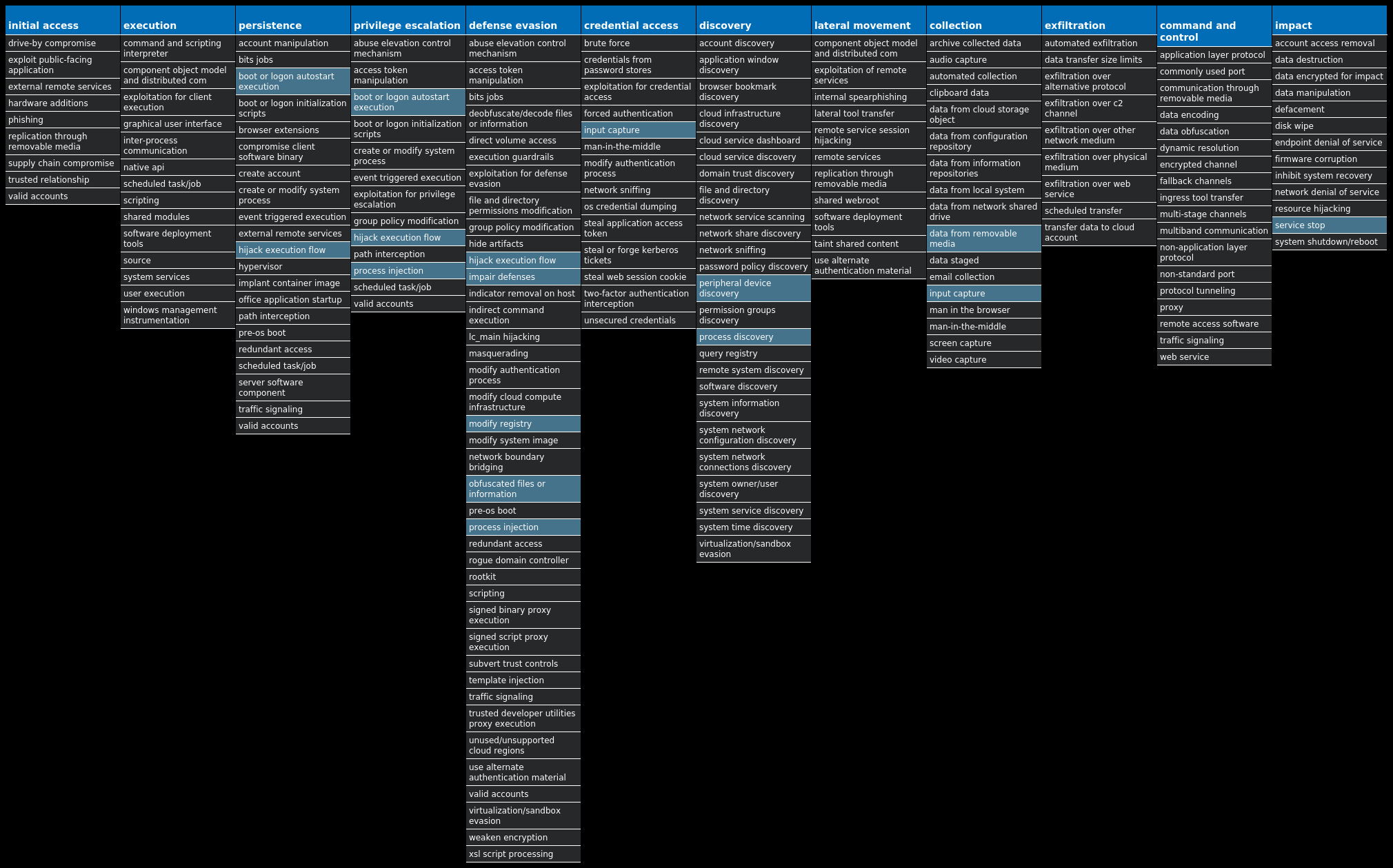
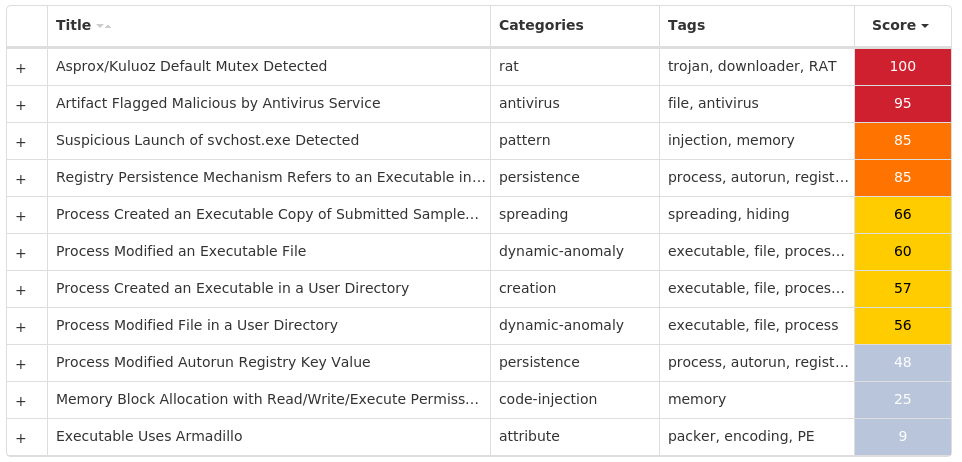
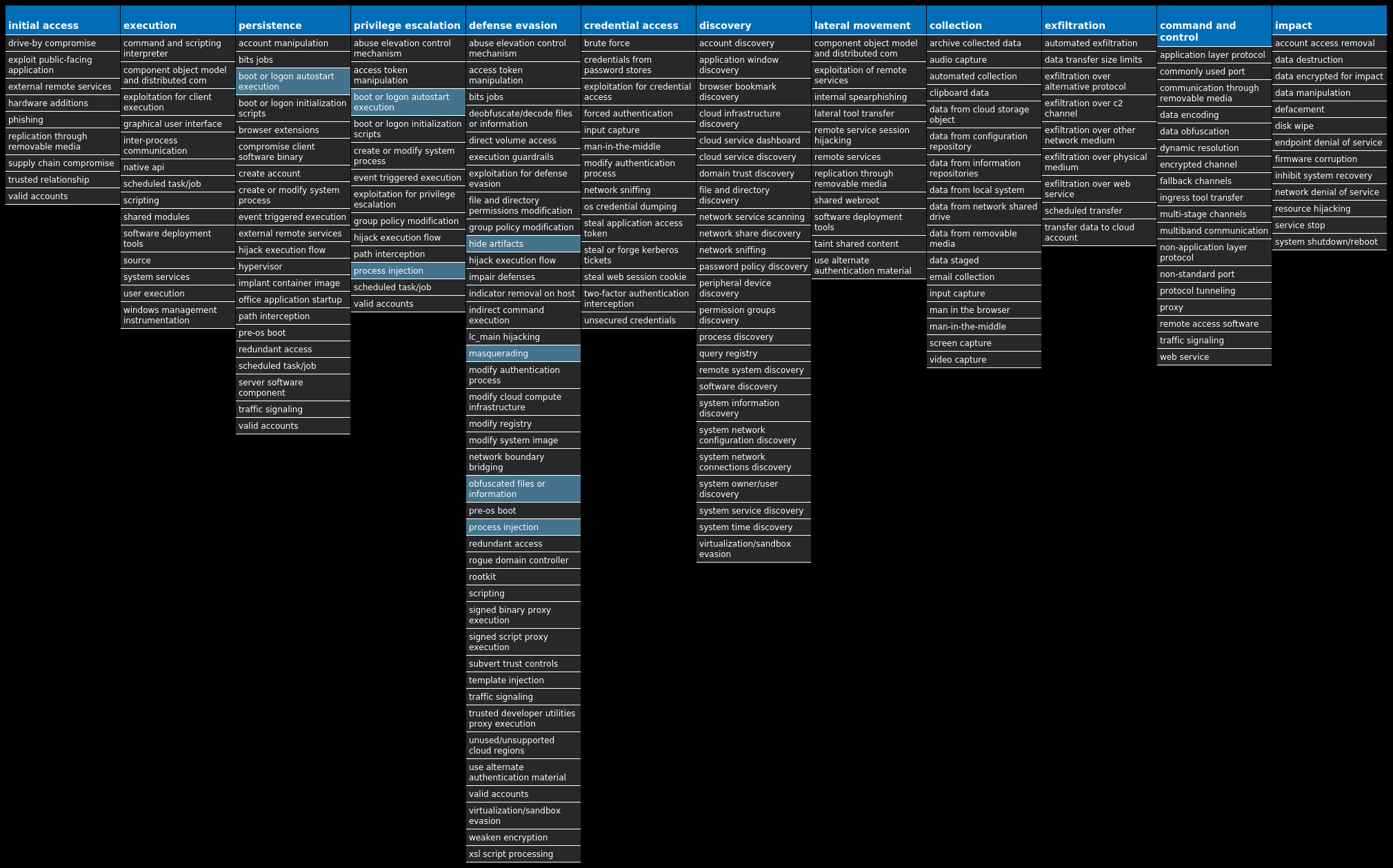
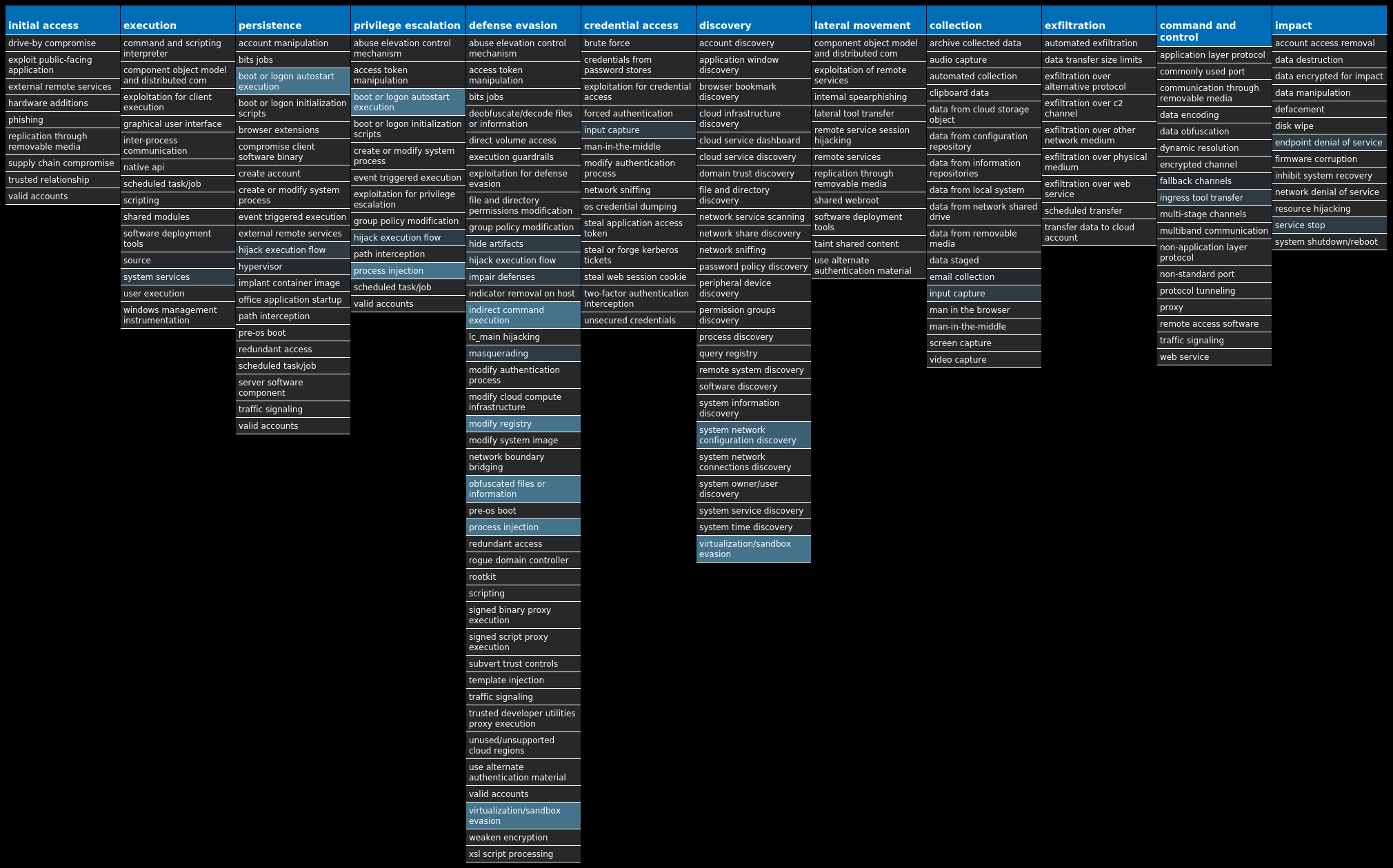
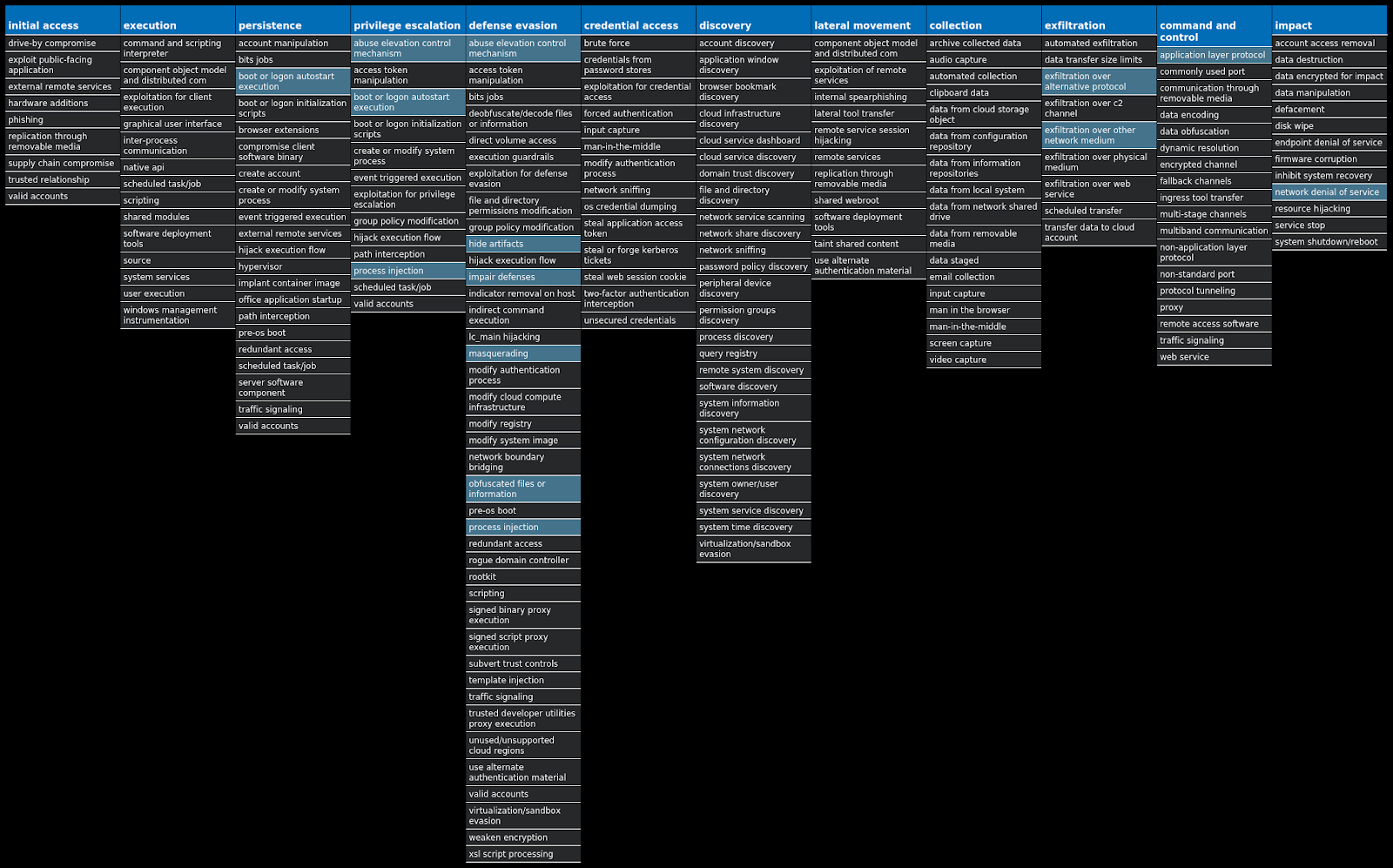
For each threat described below, this blog post only lists 25 of the associated file hashes and up to 25 IOCs for each category. An accompanying JSON file can be found here that includes the complete list of file hashes, as well as all other IOCs from this post. A visual depiction of the MITRE ATT&CK techniques associated with each threat is also shown. In these images, the brightness of the technique indicates how prevalent it is across all threat files where dynamic analysis was conducted. There are five distinct shades that are used, with the darkest indicating that no files exhibited technique behavior and the brightest indicating that technique behavior was observed from 75 percent or more of the files.
The most prevalent threats highlighted in this roundup are:
Threat Name Type Description Win.Dropper.Shiz-9957065-0 Dropper Shiz is a remote access trojan that allows an attacker to access an infected machine in order to harvest sensitive information. It is commonly spread via droppers or by visiting a malicious site. Win.Dropper.Tofsee-9957067-0 Dropper Tofsee is multi-purpose malware that features a number of modules used to carry out various activities such as sending spam messages, conducting click fraud, mining cryptocurrency, and more. Infected systems become part of the Tofsee spam botnet and are used to send large volumes of spam messages to infect additional systems and increase the size of the botnet under the operator's control. Win.Ransomware.TeslaCrypt-9957356-0 Ransomware TeslaCrypt is a well-known ransomware family that encrypts a user's files with strong encryption and demands Bitcoin in exchange for a file decryption service. A flaw in the encryption algorithm was discovered that allowed files to be decrypted without paying the ransomware, and eventually, the malware developers released the master key allowing all encrypted files to be recovered easily. Win.Virus.Expiro-9957505-0 Virus Expiro is a known file infector and information-stealer that hinders analysis with anti-debugging and anti-analysis tricks. Win.Dropper.Kuluoz-9957187-0 Dropper Kuluoz, sometimes known as "Asprox," is a modular remote access trojan that is also known to download and execute follow-on malware, such as fake antivirus software. Kuluoz is often delivered via spam emails pretending to be shipment delivery notifications or flight booking confirmations. Win.Dropper.DarkComet-9957280-1 Dropper DarkComet and related variants are a family of remote access trojans designed to provide an attacker with control over an infected system. This malware can download files from a user's machine and contains mechanisms for persistence and hiding. It also sends back usernames and passwords from the infected system. Win.Trojan.Sality-9957294-1 Trojan Sality is a file infector that establishes a peer-to-peer botnet. Although it's been prevalent for over a decade, we continue to see new samples that require marginal attention to remain consistent with detection. Once perimeter security has been bypassed by a Sality client, the end goal is to execute a downloader component capable of executing additional malware.
Threat Breakdown Win.Dropper.Shiz-9957065-0 Indicators of Compromise IOCs collected from dynamic analysis of 27 samples Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFTValue Name: 67497551a 27 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGONValue Name: 98b68e3c 27 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGONValue Name: userinit 27 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGONValue Name: System 27 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWSValue Name: load 27 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINDOWSValue Name: run 27 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: userinit 27
Mutexes Occurrences Global\674972E3a27 Global\MicrosoftSysenterGate727 internal_wutex_0x000000e027 internal_wutex_0x0000038c27 internal_wutex_0x0000044827 internal_wutex_0x<random, matching [0-9a-f]{8}>15 internal_wutex_0x0000064012
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 13[.]107[.]21[.]20019 45[.]79[.]19[.]1968 72[.]14[.]185[.]437 96[.]126[.]123[.]2445 45[.]33[.]23[.]1835 45[.]33[.]18[.]445 45[.]56[.]79[.]234 45[.]33[.]2[.]794 45[.]33[.]20[.]2354 198[.]58[.]118[.]1673 45[.]33[.]30[.]1973 85[.]94[.]194[.]1692 173[.]255[.]194[.]1342 72[.]14[.]178[.]1742
Domain Names contacted by malware. Does not indicate maliciousness Occurrences vocijekyqiv[.]eu27 foxofewuteq[.]eu27 nozapekidis[.]eu27 makymykakic[.]eu27 galerywogej[.]eu27 qeguxylevus[.]eu27 rydohyluruc[.]eu27 lysafurisam[.]eu27 kefilyrymaj[.]eu27 purumulazux[.]eu27 ciqivutevam[.]eu27 vopycyfutoc[.]eu27 fotulybidyq[.]eu27 norijyfohop[.]eu27 mamasufexix[.]eu27 gaqofubakeh[.]eu27 jenerunybem[.]eu27 qebequgyqip[.]eu27 kevybunureh[.]eu27 rycucugisix[.]eu27 tulojigakit[.]eu27 lyxilunogem[.]eu27 xukafinezeg[.]eu27 pujepigeviz[.]eu27 cihyrimymen[.]eu27
*See JSON for more IOCs
Files and or directories created Occurrences %TEMP%\<random, matching [A-F0-9]{1,4}>.tmp27
File Hashes 0067560aba08824dfeb770ca27e3d0e1ece982b8460187f8d9b5a141436577d8 00b97ecd94f57d5a56cdf81df2b5031886913dc017b0d089ea453db9fbf84a41 00e5836b518919f036f5757d5d7fb19b8deec74d1b9f4974e832e72d24158620 019e5844590d1519e9e75d605dac69e3216eab3395d64edae9682f522a02680e 054c5a47542510462512167f374d1bca1ad18d04c26cb7d94a2fce9d7646438a 072b0b3d68b21de76ceb5296f3dba4cb9741f59dacf8b1e7d7bc06976da86149 0772ed398daf5d48a638ad446bb989c5ce74319f9c364c933ab5917572123388 09825454a9f3e88b69f21307efa2e6093f2394d9e5a246ba87547e15a2d4ac86 09fce5411ee6353ddaa268c2e49a3557546dc2c83fcba0a6292a640498facf82 0a07532300d240f7346be75bc5e44d130f7dab376de86ea2ea385bc8cf86d425 0b2b2c70f849d8edbc124f00879fd5ed3ed6c86253bc3c4851885467974fd567 0c22d4fe5ddbecded7048875e9a7e0cdddd5198350aa8dfc7048b9cb24d49022 0d36aa152877523190d50d72eb7c383e27312286cda6eedc3feaaa9c7b407a8c 0d53b772610ba18ea4b296d94b33730e1f16f82e81719d887b303d5ffd0bb724 0d9e7df2c3f7ee39261b2b5af1e70d924ff931473bdc795b0cad29fbcf65d22b 0db7fb425f0e5fe4fe7cc0e9f155a1bb6fa36469487274418e0cf10350264248 0e54984099f81c595ff7ced76bef3bc8547731f8f0e12c298437f08774fffcb4 139be07d5ad7673637d6249789061171692738737023c86a35e9332000f8cac2 1517de689fc7d424de67c20031ee04cff3fc878e1ebe0e8545df14efb159a98b 15f23b0f7665d6092eaee9b28bcbc43086e652cb35633cfaa2f061d9d5b4b3b0 1905329fc88cff0c323d75d844050dddf71f085b1b031cd78eb286e3b49aa30a 198d9692d11bffc2a5c5dd4504f7fa13743a25d785e08d0cab9073142900c45e 19e233e3a11bcc6916977b99cb89df850230812a7087fb9b11b9b4ed0f33c2f3 1eed66a3938ff9a7dd07a443c0922b54d71877463ad0429123e902e97acc3523 213fe1fdb10d80b6abd770e2020913ad6a1872411224fccff3aa58d334414040*See JSON for more IOCs
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
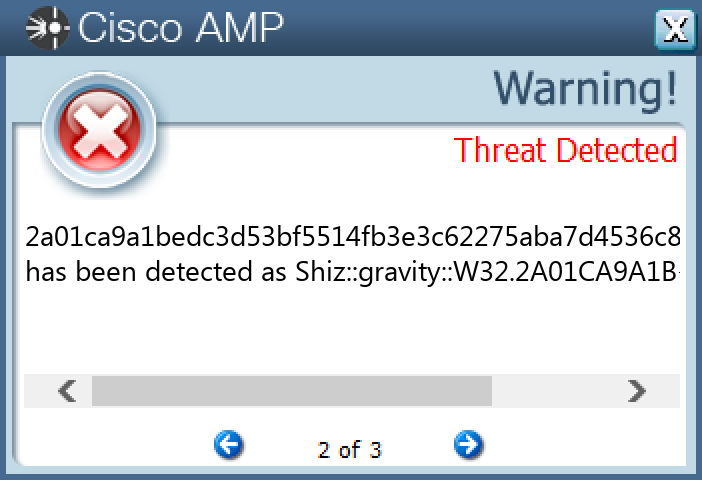
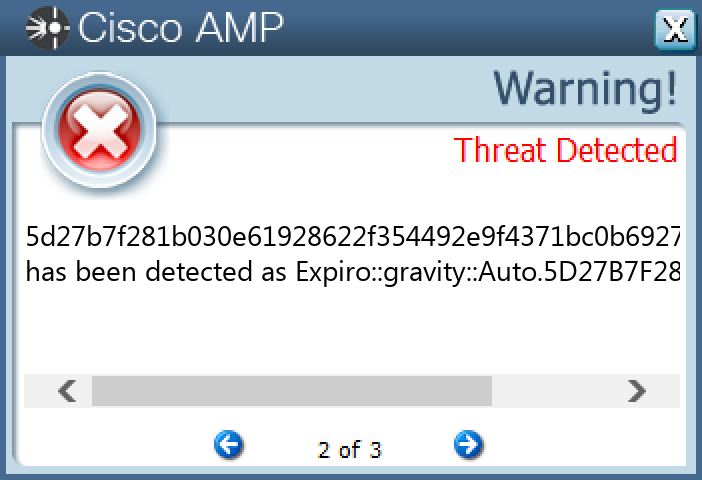
Screenshots of Detection Secure Endpoint
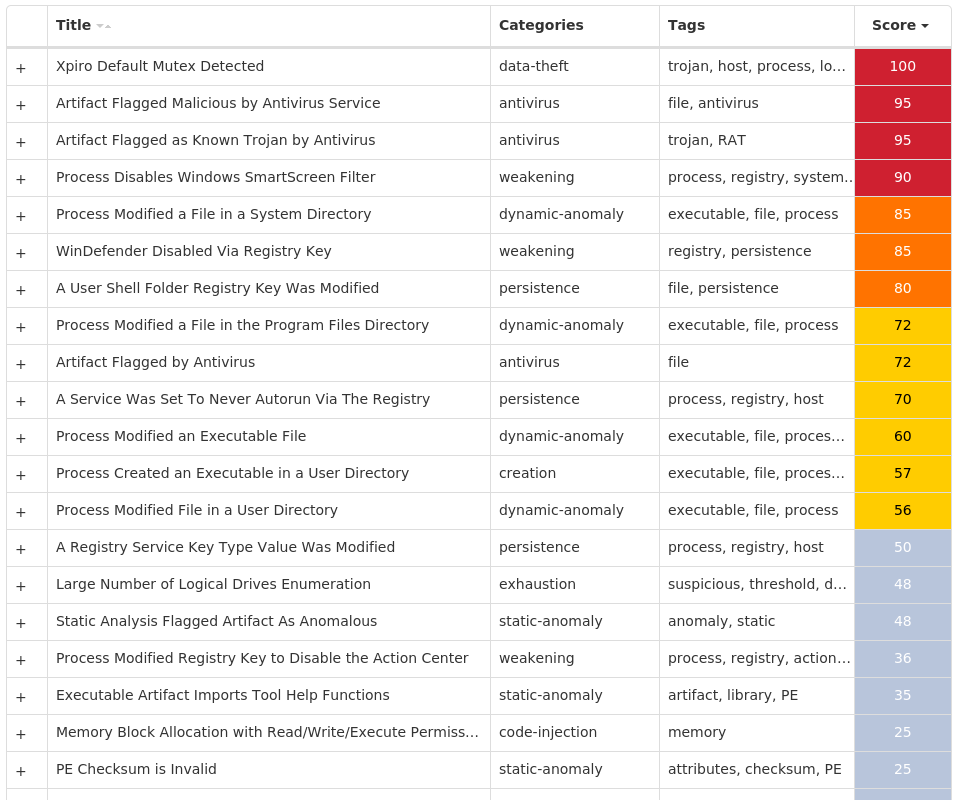
Secure Malware Analytics
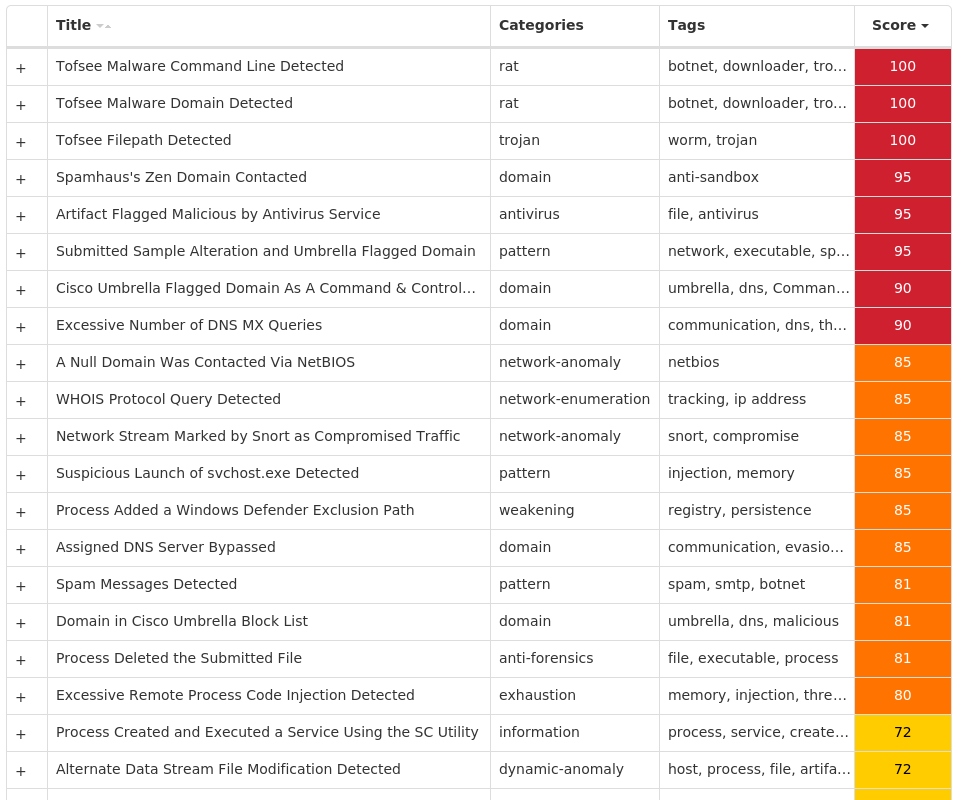
MITRE ATT&CK Win.Dropper.Tofsee-9957067-0 Indicators of Compromise IOCs collected from dynamic analysis of 17 samples Registry Keys Occurrences <HKU>\.DEFAULT\CONTROL PANEL\BUSESValue Name: Config4 4 <HKU>\.DEFAULT\CONTROL PANEL\BUSES4 <HKU>\.DEFAULT\CONTROL PANEL\BUSESValue Name: Config0 4 <HKU>\.DEFAULT\CONTROL PANEL\BUSESValue Name: Config1 4 <HKU>\.DEFAULT\CONTROL PANEL\BUSESValue Name: Config2 4 <HKU>\.DEFAULT\CONTROL PANEL\BUSESValue Name: Config3 4 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHD1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: Type 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: Start 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: ErrorControl 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: DisplayName 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: WOW64 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: ObjectName 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\NXZUQIHDValue Name: Description 1 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHSValue Name: C:\Windows\SysWOW64\nxzuqihd 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYU1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: Type 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: Start 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: ErrorControl 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: DisplayName 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: WOW64 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: ObjectName 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EOQLHZYUValue Name: Description 1 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS DEFENDER\EXCLUSIONS\PATHSValue Name: C:\Windows\SysWOW64\eoqlhzyu 1 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\TDFAWONJ1
Mutexes Occurrences Global\07ada3c1-08f4-11ed-b5f8-00501e3ae7b61 Global\067cf3c1-08f4-11ed-b5f8-00501e3ae7b61 Global\08e8d341-08f4-11ed-b5f8-00501e3ae7b61
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 212[.]77[.]101[.]44 142[.]250[.]72[.]1004 31[.]41[.]244[.]824 31[.]41[.]244[.]854 80[.]66[.]75[.]2544 80[.]66[.]75[.]44 31[.]41[.]244[.]1284 31[.]41[.]244[.]126/314 185[.]165[.]123[.]134 208[.]71[.]35[.]1373 208[.]76[.]51[.]513 216[.]146[.]35[.]353 199[.]5[.]157[.]1313 208[.]76[.]50[.]503 195[.]46[.]39[.]393 23[.]90[.]4[.]63 194[.]25[.]134[.]83 144[.]160[.]235[.]1433 193[.]222[.]135[.]1503 209[.]244[.]0[.]33 119[.]205[.]212[.]2193 67[.]231[.]152[.]943 31[.]13[.]65[.]1743 117[.]53[.]116[.]153 172[.]253[.]115[.]26/313
*See JSON for more IOCs
Domain Names contacted by malware. Does not indicate maliciousness Occurrences 249[.]5[.]55[.]69[.]bl[.]spamcop[.]net4 249[.]5[.]55[.]69[.]cbl[.]abuseat[.]org4 249[.]5[.]55[.]69[.]dnsbl[.]sorbs[.]net4 249[.]5[.]55[.]69[.]in-addr[.]arpa4 249[.]5[.]55[.]69[.]sbl-xbl[.]spamhaus[.]org4 249[.]5[.]55[.]69[.]zen[.]spamhaus[.]org4 microsoft-com[.]mail[.]protection[.]outlook[.]com4 microsoft[.]com4 www[.]google[.]com4 whois[.]arin[.]net4 whois[.]iana[.]org4 aspmx[.]l[.]google[.]com4 wp[.]pl4 ameritrade[.]com4 mxa-000cb501[.]gslb[.]pphosted[.]com4 mx[.]wp[.]pl4 svartalfheim[.]top4 www[.]instagram[.]com3 mta5[.]am0[.]yahoodns[.]net3 hanmail[.]net3 freenet[.]de3 korea[.]com3 t-online[.]de3 o2[.]pl3 nate[.]com3
*See JSON for more IOCs
Files and or directories created Occurrences %SystemRoot%\SysWOW64\config\systemprofile4 %SystemRoot%\SysWOW64\config\systemprofile:.repos4 %SystemRoot%\SysWOW64\nxzuqihd1 %SystemRoot%\SysWOW64\eoqlhzyu1 %SystemRoot%\SysWOW64\tdfawonj1 %SystemRoot%\SysWOW64\hrtokcbx1 %TEMP%\oacsevkh.exe1 %TEMP%\htrzurov.exe1 %TEMP%\rzwntxyj.exe1 %TEMP%\mcilsztg.exe1
File Hashes 1b64011f2f80b0ded096cbdb81c2bdac9786dc8a4ea7425b15547bdca34e043f 34c17bb102b2ed718471668da1ddc7daf397175979582942bf89d8e272cfa141 59bdcd1599938f1c5c2845d1fef198a0d97b03744432fc6705c9c67f13eedab4 64d6709c3cfbf8765e9434abfe6fc8bad67d87a3e4fe0622e68aa1d15aac8d6b 6857bce2c5f73e1d1bc4b14cb7b281beb33fed8cb580a43f236460c2af0e65e2 6eb7dd7f943a22822b0aaef6301d32b54eb43e432070c41b7d3c6a3d041ec8b3 6f3ef01ce9f2896b54c06fe4cd5e5769dda3a958868557a20469feb21c7e1273 79699aa58081b925c0b75140f0110f3ebf9a47e9bc8ba1699d53d7b14cb49591 7e2975f6cb11bb324bd49ec6fd4b77478e3488bf99fe623851a29f06e9b1fb37 89974e5d8be578da3cc6c0a33398659aabb160cdb03f7158066969f430dab796 9449f5dd9a6728664a3be973ccb91adbf64ffe980ff96de05a0419eb0a77bbd7 b77c2b3942f50e8fef2440481de894d506418f7a7c35fb29d40cfa8ce795ebf4 cbbc899843ca8f5908c27645960a33952fbecbf3d5cefc5054ab1dd023bb8582 d0596ec9d08cdd81f86e07d5ab70b518c6ca23a9ed4f557d041d3307b3ca7020 d518bbcb40208cfd7cbb6965e1647fabd5f65f2f1c1520e1217996957a1ada8d e6411e18f8a1096f9b5d7528a24f6acdf1f97d120dd0dae4d76703c8eb5e4040 efced050e17235d050db86e0d763a07cfff375771d586736bbd17520725f1ebf
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA
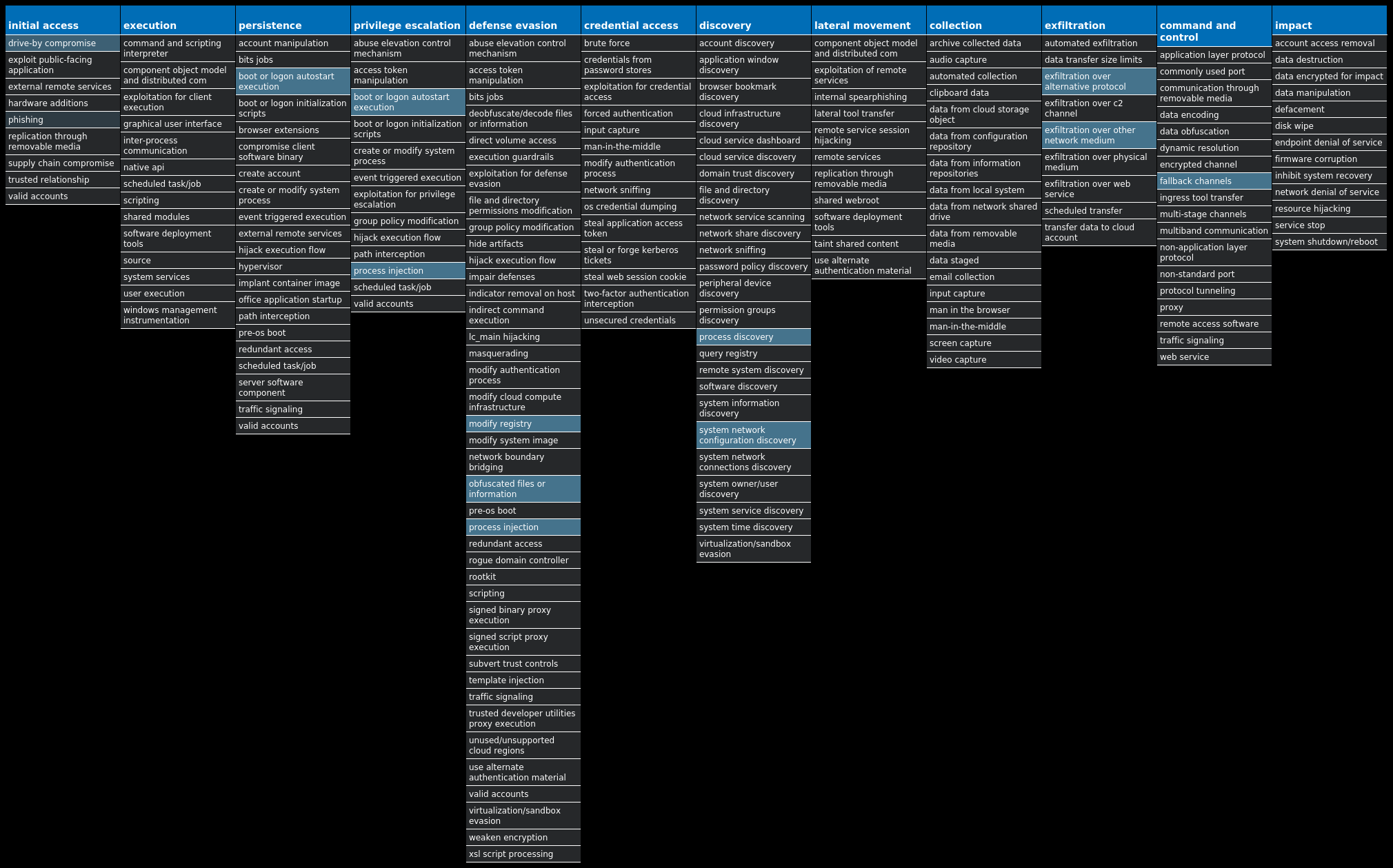
Secure Endpoint
Secure Malware Analytics
MITRE ATT&CK Win.Ransomware.TeslaCrypt-9957356-0 Indicators of Compromise IOCs collected from dynamic analysis of 25 samples Registry Keys Occurrences <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\SYSTEMValue Name: EnableLinkedConnections 25 <HKCU>\SOFTWARE\XXXSYS25 <HKCU>\SOFTWARE\XXXSYSValue Name: ID 25 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\ACTION CENTER\CHECKS\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.CHECK.0Value Name: CheckSetting 25 <HKCU>\Software\<random, matching '[A-Z0-9]{14,16}'>24 <HKCU>\Software\<random, matching '[A-Z0-9]{14,16}'>Value Name: data 24 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: hdtjbroygvvb 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: owvhajogulen 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: pyfepfifrjwi 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: xbmnkkfnowvh 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: gulenopvybnq 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: tbqdqvojagik 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: hajogulenopv 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: mgtbqdqvcoqj 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: ulenopvybnqj 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: lpyfepfifrjw 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: epfifrjwiqou 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: ifrjwiqouteu 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: teumgtbqdqvo 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: nrxbmnkkfnow 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: whmtlmoxvcsc 1 <HKCU>\SOFTWARE\159643D83772F1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: bmnkkfnowvha 1 <HKCU>\SOFTWARE\159643D83772FValue Name: data 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: vcscusnnmyjx 1
Mutexes Occurrences ityeofm9234-2342325
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 107[.]6[.]161[.]16225
Domain Names contacted by malware. Does not indicate maliciousness Occurrences jessforkicks[.]com25 heizhuangym[.]com25 infotlogomas[.]malangkota[.]go[.]id25 csucanuevo[.]csuca[.]org25 snibi[.]se25 danecobain[.]com25 www[.]danecobain[.]com25
Files and or directories created Occurrences %ProgramFiles%\7-Zip\Lang\ka.txt25 %ProgramFiles%\7-Zip\Lang\kaa.txt25 %ProgramFiles%\7-Zip\Lang\kab.txt25 %ProgramFiles%\7-Zip\Lang\kk.txt25 %ProgramFiles%\7-Zip\Lang\ko.txt25 %ProgramFiles%\7-Zip\Lang\ku-ckb.txt25 %ProgramFiles%\7-Zip\Lang\ku.txt25 %ProgramFiles%\7-Zip\Lang\ky.txt25 %ProgramFiles%\7-Zip\Lang\lij.txt25 %ProgramFiles%\7-Zip\Lang\lt.txt25 %ProgramFiles%\7-Zip\Lang\lv.txt25 %ProgramFiles%\7-Zip\Lang\mk.txt25 %ProgramFiles%\7-Zip\Lang\mn.txt25 %ProgramFiles%\7-Zip\Lang\mng.txt25 %ProgramFiles%\7-Zip\Lang\mng2.txt25 %ProgramFiles%\7-Zip\Lang\mr.txt25 %ProgramFiles%\7-Zip\Lang\ms.txt25 %ProgramFiles%\7-Zip\Lang\nb.txt25 %ProgramFiles%\7-Zip\Lang\ne.txt25 %ProgramFiles%\7-Zip\Lang\nl.txt25 %ProgramFiles%\7-Zip\Lang\nn.txt25 %ProgramFiles%\7-Zip\Lang\pa-in.txt25 %ProgramFiles%\7-Zip\Lang\pl.txt25 %ProgramFiles%\7-Zip\Lang\ps.txt25 %ProgramFiles%\7-Zip\Lang\pt-br.txt25
*See JSON for more IOCs
File Hashes 11bf02df58d00bf7dfc22e46b27db8a2cfcb9c8d03ad38b2e3baafa193bbbd89 1a4a1e76c6d2dc585ce77c9be7163163c0d614d5668a0c83601bb3d6f91376a0 1c2ddbf956ee1e2b40472b70603371ed21817fbf95d5825b2f75bbf6f9728089 1d4114c8ee19f343f3dcf80a542295af29df63d9745ad77cce43562c909551c5 2f1f927c219ccfcffeb997c9433733a04200ae35a2fc0c48fc07cb49062cddc7 3ef3021ce3ffdffcfba2bd590c4186c3a3ecdd3b6ce40d51d2500897fb55ffb0 41ab6446df889a5a24e4e859146c0225d13a2ba8553c83cb93e45017212884b2 4bae8a4e0124724e695c10202a94eec99cf5990507fbc94ec3f08e11de3ce2c2 4dc12416bf7c3be9d573c8fa07847050307bd05cb67480e3c3874696614b73e9 4fa8c1eaa4846a8a06fb2480a746d5526f743cee314f7101db0508577bdd3776 5207a70e0e818741279d7c25c0d9cb6be136a4fc8ca8fe6f48112c4d0572d64f 5aaad74cb36db78ad6da4d499a75c41d2ace8b97ff8f88c5bc7f738ad353d3d7 67e2caf00dd0293080cb5b45d2db11d4f567ce9a3d6fd5c9723358d18da80e71 6a9e6e5c50b3b90376530ee4e9e81cdf5cdc9b7c07cdb71207b3a1799f77ec7a 6ab8f9569a70beb0f96bf4e030381e70bcce7703b308a05542f4ccf1b6002af9 71f0f23220cb0f5d8b31fce30f08bc1687acd675b7c3a8ae7e0538bacb0d3eec a3a6b4f405f2175af97128c64d9ad68700e05e22d66c43dad966add8436af79f a760b60722cfa7c719e79b5c97cfe789720c6300a200421c846e13287cdb160a d8be6b950a872b1b7c752cc83a5440b4cfe62870097df78794f10986fb7fcb63 dd6483183967845c18a3d5cc6154233aa8f3a48acb4e9cccd3606afe7d4d7eef de5dc2aed0e06894e0bb1292fb68343fadc46b489e6c85e6cca56cf5bad70c09 e1a00e6beb02475b4bdd8d821ccac3e67bbafd182332cbf35a45c6766ad83b87 e8c460f171e964db6fff16eb38684b9ec82134c4fd1a1cdc64ba338941ef1199 f69edf352cdca309c7faa71f87a429daf2b46e4ae6ed85a25ff03aa34b4702c4 fbcec257455e5546a294ec1534f7e11f05d144c73ef583a0e891e14759e133eb
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella WSA
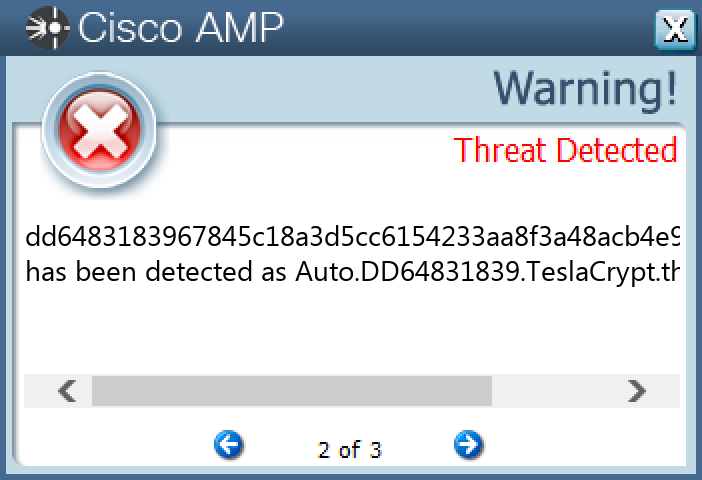
Screenshots of Detection Secure Endpoint
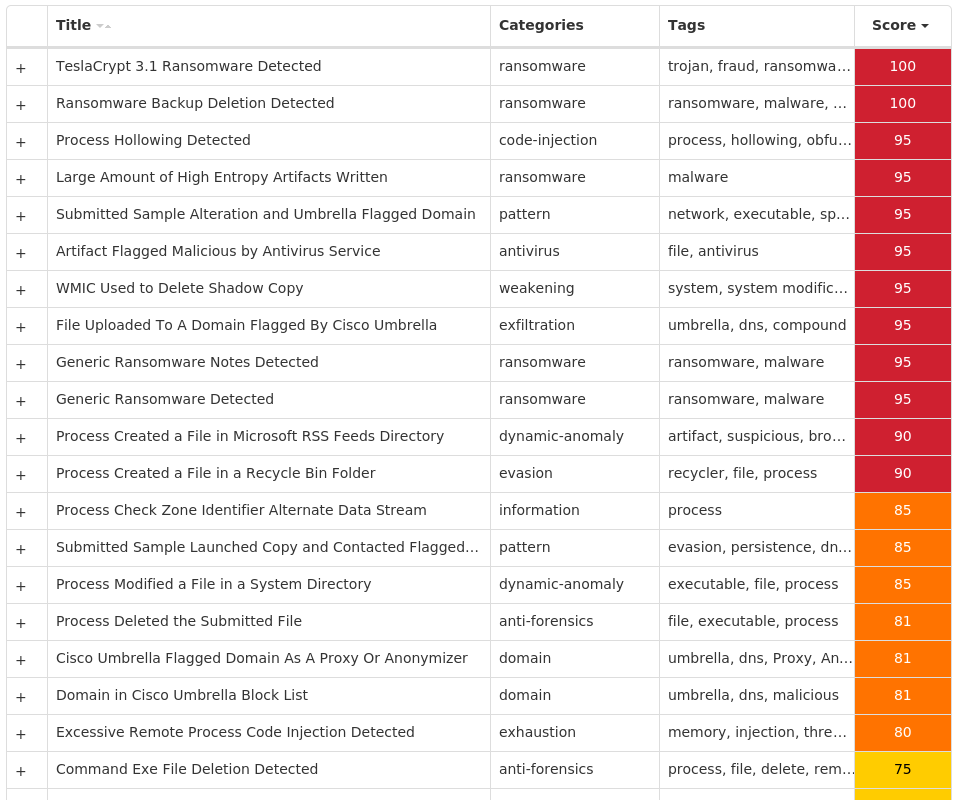
Secure Malware Analytics
MITRE ATT&CK
Win.Virus.Expiro-9957505-0 Indicators of Compromise IOCs collected from dynamic analysis of 97 samples Registry Keys Occurrences <HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V4.0.30319_32Value Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V4.0.30319_64Value Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\COMSYSAPPValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\IEETWCOLLECTORSERVICEValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\MOZILLAMAINTENANCEValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSISERVERValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V2.0.50727_32Value Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\ALGValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EHRECVRValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\EHSCHEDValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\FAXValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\MICROSOFT SHAREPOINT WORKSPACE AUDIT SERVICEValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\MSDTCValue Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\CLR_OPTIMIZATION_V2.0.50727_64Value Name: Start 97 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\FAXValue Name: ObjectName 97 <HKLM>\SOFTWARE\MICROSOFT\.NETFRAMEWORK\V2.0.50727\NGENSERVICE\STATEValue Name: AccumulatedWaitIdleTime 97 <HKLM>\SOFTWARE\MICROSOFT\.NETFRAMEWORK\V2.0.50727\NGENSERVICE\LISTENEDSTATEValue Name: RootstoreDirty 97 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\.NETFRAMEWORK\V2.0.50727\NGENSERVICE\STATEValue Name: AccumulatedWaitIdleTime 97 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\.NETFRAMEWORK\V2.0.50727\NGENSERVICE\LISTENEDSTATEValue Name: RootstoreDirty 97 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\MEDIA CENTER\SERVICE\SCHEDULER97 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\MEDIA CENTER\SERVICE\SCHEDULERValue Name: ServiceFailures 97 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\MEDIA CENTER\SERVICE\SCHEDULERValue Name: ServiceStarted 97 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\MEDIA CENTER\SERVICE\SCHEDULERValue Name: Heartbeat 97 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\MEDIA CENTER\SERVICE\SCHEDULERValue Name: WaitingForShutdown 97 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\MEDIA CENTER\SERVICE\SCHEDULERValue Name: HeartbeatIntervalMs 97
Mutexes Occurrences http://www.microsoft.com/windowsxp/mediacenter/ehtray.exe/singleinstancemutex97 Global\MCStoreCreateTable_a1d78cdcc411921ce3b07770aa2a0e0745789b1197 Global\MCStoreOpen_b4cae1f9a3aead62bebb934ca33cadb730c8d3ed97 Global\MCStoreSyncMem_02004a9f865399b5c2a02973d5e53544ed4ce2ea97 Global\MCStoreSyncMem_5ea381292eeb3ed3e61dc84a3dbd4d7f59767eca97 Global\MCStoreSyncMem_71bdfe29063ac557a4e7b3205ed180408457fcd497 Global\MCStoreSyncMem_7715dc857070a1523dea43f32f1fe67c1ce58e0b97 Global\__?_c:_programdata_microsoft_ehome_mcepg2-0.db97 Global\__?_c:_programdata_microsoft_ehome_mcepg2-0.db:x97 Global\eHome_DbMutex_197 Global\eHome_DbMutex_297 Global\eHome_DbRWMutex_197 Global\Multiarch.m0yv-98b68e3c311dcc78-inf97 Global\Multiarch.m0yv-98b68e3c311dcc78493cd690-b97 Global\Multiarch.m0yv-98b68e3c311dcc789ea72c54-b97 Global\MCStoreAddStoredType_a1d78cdcc411921ce3b07770aa2a0e0745789b1194 Global\eHome_DbMutex_394 Global\OfficeSourceEngineMutex92 Global\Media Center Tuner Request70 Global\eHome_DbMutex_469 Global\eHome_DbMutex_569 Global\PVRLibraryLock_a1d78cdcc411921ce3b07770aa2a0e0745789b1157 Global\eHome_DbRWMutex_254 Global\__?_c:_programdata_microsoft_ehome_mcepg2-0.db:splk:10368 Global\__?_c:_programdata_microsoft_ehome_mcepg2-0.db:splk:9245
*See JSON for more IOCs
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 172[.]105[.]27[.]6195 167[.]99[.]35[.]8870 206[.]191[.]152[.]5866 63[.]251[.]106[.]2562 178[.]162[.]217[.]10720 85[.]17[.]31[.]8216 178[.]162[.]203[.]20215 5[.]79[.]71[.]20514 85[.]17[.]31[.]12214 173[.]231[.]184[.]12411 63[.]251[.]126[.]1011 178[.]162[.]203[.]22610 178[.]162[.]203[.]2119 5[.]79[.]71[.]2257 35[.]234[.]136[.]136 185[.]185[.]69[.]772 82[.]112[.]184[.]1971
Domain Names contacted by malware. Does not indicate maliciousness Occurrences pywolwnvd[.]biz97 ssbzmoy[.]biz97 cvgrf[.]biz78 npukfztj[.]biz75 przvgke[.]biz71 zlenh[.]biz68 knjghuig[.]biz8 uhxqin[.]biz8 anpmnmxo[.]biz1 lpuegx[.]biz1
Files and or directories created Occurrences %ProgramFiles(x86)%\Microsoft Office\Office14\GROOVE.EXE97 %ProgramFiles(x86)%\Mozilla Maintenance Service\maintenanceservice.exe97 %SystemRoot%\Microsoft.NET\Framework64\v2.0.50727\mscorsvw.exe97 %SystemRoot%\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe97 %SystemRoot%\Microsoft.NET\Framework\v2.0.50727\mscorsvw.exe97 %SystemRoot%\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe97 %System32%\FXSSVC.exe97 %System32%\alg.exe97 %System32%\dllhost.exe97 %System32%\ieetwcollector.exe97 %System32%\msdtc.exe97 %System32%\msiexec.exe97 %SystemRoot%\ehome\ehrecvr.exe97 %SystemRoot%\ehome\ehsched.exe97 %SystemRoot%\Microsoft.NET\Framework\v2.0.50727\ngen_service.log97 %SystemRoot%\Microsoft.NET\Framework64\v2.0.50727\ngen_service.log97 %SystemRoot%\Registration\{02D4B3F1-FD88-11D1-960D-00805FC79235}.{33EC2C09-9668-4DE7-BCC0-EFC69D7355D7}.crmlog97 %SystemRoot%\Microsoft.NET\Framework64\v4.0.30319\ngen_service.log97 %SystemRoot%\Microsoft.NET\Framework\v4.0.30319\ngen_service.log97 %SystemRoot%\Microsoft.NET\Framework\v4.0.30319\ngenservicelock.dat97 %SystemRoot%\Microsoft.NET\Framework64\v4.0.30319\ngenrootstorelock.dat97 %SystemRoot%\Microsoft.NET\Framework64\v4.0.30319\ngenservicelock.dat97 %SystemRoot%\Microsoft.NET\Framework\v2.0.50727\ngen_service.lock97 %SystemRoot%\Microsoft.NET\Framework\v2.0.50727\ngenservicelock.dat97 %SystemRoot%\Microsoft.NET\Framework64\v2.0.50727\ngen_service.lock97
*See JSON for more IOCs
File Hashes 003197ab7aab0056ef0fbeb11dd4b6762216c3d27540ca4825f181fab330a832 01b59d7b8d9e128753e33b88705d6b0ee2be945fd4bd95c92c25fe160bcc2a28 01c2d4cecc87e39c6c08db505065e5ef9d4927fac599f0e1e752407e15c4e633 024c5d8975e9e34be65107327c05e119c8b595c954eadb25b07cbf55cbc898a9 032794dc64b0ac4b893561771732bd67ae0962f1f381c53bdef1be6a5155df3e 03d2208d010c08559d1625142d2efc90b48bd94cc19f33123b8b665e6e607b34 03d83413d2881f01a23c0794d66d0d29510ce12ccb66f1005ab64910cd4e7f07 03db00a2082925d5504e4d46eeab2dab8d9ef3a18c96eb9b8ab8717fd0ccbe8d 03f7b3af2bf5e87b1c975459f64756b7a79baa18d42d90f0e0cae4599d08fe90 043c30b9943b579599eb43e475c1d25ede670783c187700a3e7bbdb26bfeea63 04eb47a0bd5b0f3cc4eee02186545267cfed907b9eb9c496b771e95b48554060 058f0d75c3422806327c0a7d4834481e69b1e92b080aa260361c3702e5469e7b 0648fd62ac4c8b83f30aba65893b6b9598a7186a1ad55c39b4c7055d17702053 06bc99dec80527c04d4c623ab723f162d794c019b426a017d7ad41d83e055357 074729717198ab9a66bf4da155e5d4fdc5c430c60f344e64b7de97e57f344c4d 0763bb050181bab831d844067d18dc1492d0500a491664c3f9b90e19e6d2b781 08094e18e7913ca6c8eaf4cd94927fbd099c45c889cd65e4fd67ce2009c97725 095a0557fade67da6e340307af110014f915168df9b124a9fec1f197d52c4640 0a570f1ebd5fe52d306ce5a3b4bd19d399f2fcbe7002dff34a3d6bfff905e584 0b68ddbf260f48f30b24dd0f11e76572c5b10cf48abdb8f99de3d1d1c2e841de 0c37b22edd74cda6accb4f7a2325f149a78ccf5cb81af509714c202729815020 0c80ed840ae70061a0cc5ccd1f3c12832e3a51a5e937a5be3319c6fbbb47360e 0dbcd43911ae093ae0fb18adbe4488c7260e7dc8f4217241fd3ae5de7b795b9f 1022b2e11bd77dd96b27522ec5c889746c75c9a8eadf58e5396fa87da10e8331 10abdec91ee97c257bfe44b29232ea57a485d3d1cc72f8f706f3ed586910434b*See JSON for more IOCs
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA
Screenshots of Detection Secure Endpoint
Secure Malware Analytics
MITRE ATT&CK Win.Dropper.Kuluoz-9957187-0 Indicators of Compromise IOCs collected from dynamic analysis of 15 samples Registry Keys Occurrences <HKCU>\SOFTWARE\<random, matching '[a-zA-Z0-9]{5,9}'>15 <HKCU>\SOFTWARE\FVXBJPWUValue Name: vcariano 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: llqjxikf 1 <HKCU>\SOFTWARE\PWWTTVLVValue Name: twekalil 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: xxdfmerx 1 <HKCU>\SOFTWARE\EWMGTFIMValue Name: anxufehi 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: nqrwcsef 1 <HKCU>\SOFTWARE\WFPJGFQRValue Name: vjiwxwuh 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: wddfjook 1 <HKCU>\SOFTWARE\DRBVCKTPValue Name: lpeeclca 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: igudfpld 1 <HKCU>\SOFTWARE\TBTCBEWSValue Name: qbdbpkdf 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: ddgljbjp 1 <HKCU>\SOFTWARE\ATTOEKENValue Name: euvumrrn 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: kxadigun 1 <HKCU>\SOFTWARE\NWOLGMSDValue Name: okhudfoo 1 <HKCU>\SOFTWARE\SXPMECNOValue Name: vbuvphur 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: bshrfueu 1 <HKCU>\SOFTWARE\NAFNCVOVValue Name: iatqgcgc 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: lnxhasuw 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: oxviaxao 1 <HKCU>\SOFTWARE\BPLLBGMGValue Name: aqonboar 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: iurwprlq 1 <HKCU>\SOFTWARE\BEOHVVNCValue Name: mujhuapl 1 <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUNValue Name: qsmriksl 1
Mutexes Occurrences aaAdministrator15
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 162[.]209[.]14[.]3212 222[.]124[.]143[.]1210 176[.]123[.]0[.]1609 173[.]255[.]197[.]319 46[.]105[.]117[.]138 195[.]5[.]208[.]878 195[.]65[.]173[.]1335 64[.]128[.]16[.]1445
Files and or directories created Occurrences %LOCALAPPDATA%\<random, matching '[a-z]{8}'>.exe15
File Hashes 060286b4d0f8a14abe1ef08c1b3298eedd6ca8d7136514cbd28a64a80e4e5dd3 0dd7adbeab2b75d5d1e9d00ac3f59ac9e67dd4a7e2ac763e2de683d368b9f7ef 150f82c49d0a42de8a82632bb18077078076e9ba378291e5654e6cf0b14fb351 2c00d6f49dcc5bafbd868cf5c3894ddb21aa2216c54bfe148a7b861723c47a65 34f0305175ea18e197c488b450535c0cd8db1eccebdd6ecb2a2996fc813f14e7 4f4ccbcab032d9c6b8c97b452027d976b6dca4dd3c4237b8a3532f3d11bebd64 6ac1fa955677a1012e17bb3f35acf922f50d1f8810e94939ba2074756948aeae 81ce4d06b1af27b542e809e4e9f8e188782d4d14edf2a2dc94d9c857fe0c0560 8ef2563081b7dfd5e6c7c5d502b06e0d4c9fdf405b0fddbd60aff47a688e3a68 933f42380d718778039317a56fea346fbca1b07353edf46a97692ca4a6e20ba6 c9d671789d74e64450c9f33c2bb45a3337ce40ba06eb5632471fe624e2872616 cbf0ec5ad28bc4c6d44057398b3232fd519229ead06b88260b7b2d50bd5d95ac d178feddad4373a848f2fe9361b96ef7a907e1b1bd5127a5bb74926bb270d1a1 f22ba989587086403663558e7912a43b3a339f67ad42654b93c95e9120532de9 f3e21ed6c8cfc19a65076b58eddfe69683268b704649a47b513f5ef61368fe38
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
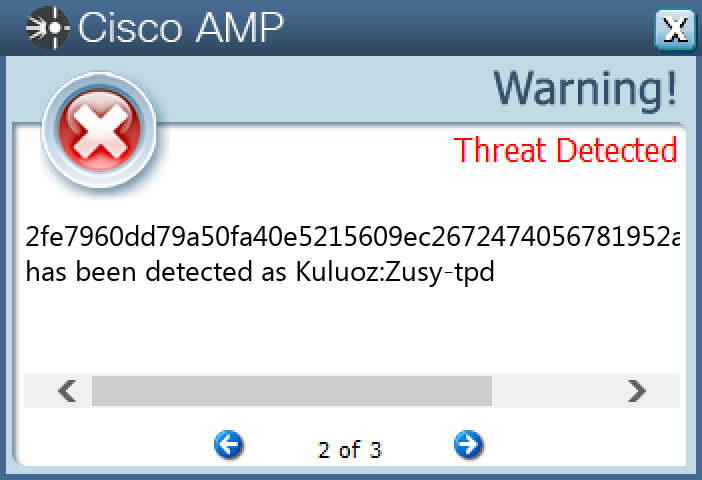
Screenshots of Detection Secure Endpoint
Secure Malware Analytics
MITRE ATT&CK Win.Dropper.DarkComet-9957280-1 Indicators of Compromise IOCs collected from dynamic analysis of 12 samples Registry Keys Occurrences <HKCU>\SOFTWARE\DC3_FEXEC10
Mutexes Occurrences DC_MUTEX-F75JL2010
Files and or directories created Occurrences %TEMP%\Crypted.exe12
File Hashes 0753d1475d7a3779684afe69f76ff81d7da01766fd34d85a23c1455008546108 0c7c5afce5165fd6be988f7aabe03abdbfdd8f0671dfe7f4b9fa73f243c9a9f1 238022cdf5b4fc75ecbb0db1654586b4686b43fcbabbcb17fec891879cdf3ba8 27bbe0f40ecf946a841f727101d707d57aadc31e4e5ca8699fe67aa61568c9b3 318eb4c14be4777bb921bbe44c1f7512d910c344fe4dbdfa373746cc7e767b1b 5631d5b53191510f47896a6fc0e9ba21e973cd35f25b21d26b984c1a46a7aca5 b45c2ab96c70d2beb2fda40032e1695324278c39918b0a8dfa3474a667c6312d b8adaf25ff8faa4c00b08993080daad260a6ba124199c020deabc8e38e636a3f c5469b740d9c2c7ffde2ea1e606fe044b87c4b21b4a502fdf63a7fd02aabc426 e36abaab1b6871ccb3ea2331168c7f04627f6861964b87b047241d79d56e664b e5daaf2b2c3c03711c622d482e0274ff1d4dbe3909969992864f2ea73c77ea8a ff107b513ffcf70490a9cef3e594bc15aba3c3f573e7b792d257f6e3188bf236
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security N/A Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
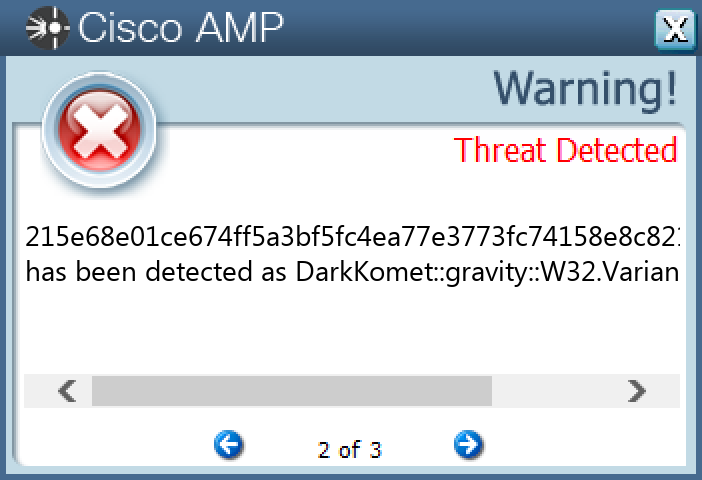
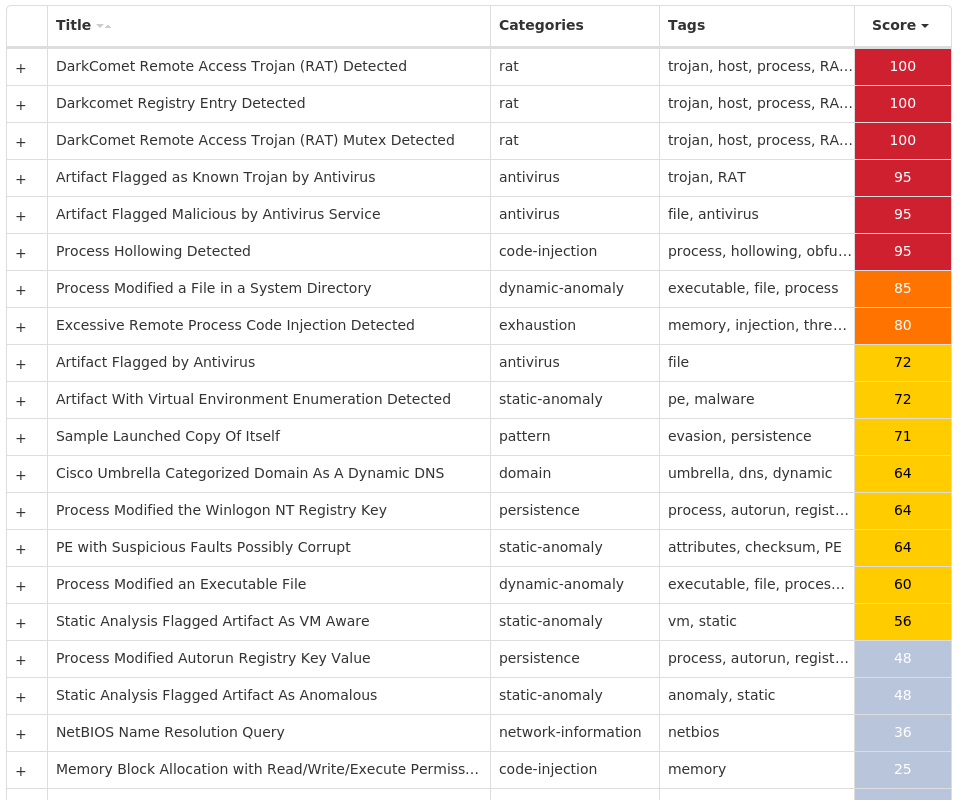
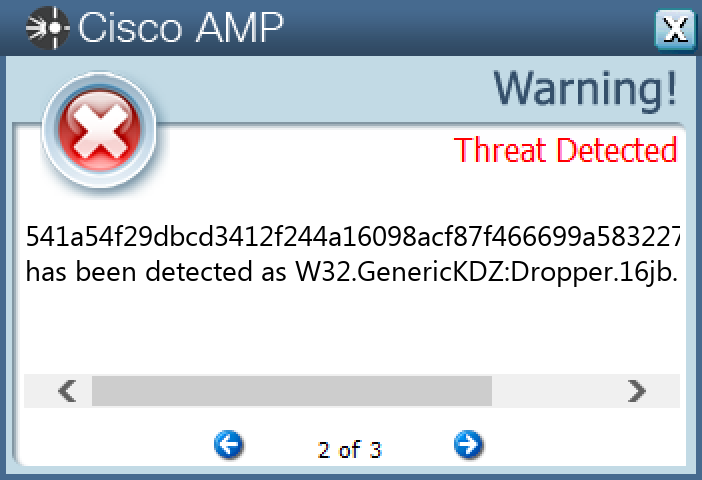
Screenshots of Detection Secure Endpoint Secure Malware Analytics MITRE ATT&CK Win.Trojan.Sality-9957294-1 Indicators of Compromise IOCs collected from dynamic analysis of 23 samples Registry Keys Occurrences <HKCU>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\ADVANCEDValue Name: Hidden 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTERValue Name: AntiVirusOverride 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTERValue Name: AntiVirusDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTERValue Name: FirewallDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTERValue Name: FirewallOverride 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTERValue Name: UpdatesDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTERValue Name: UacDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER\SVCValue Name: AntiVirusOverride 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER\SVCValue Name: AntiVirusDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER\SVCValue Name: FirewallDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER\SVCValue Name: FirewallOverride 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER\SVCValue Name: UpdatesDisableNotify 23 <HKLM>\SOFTWARE\WOW6432NODE\MICROSOFT\SECURITY CENTER\SVCValue Name: UacDisableNotify 23 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\SYSTEMValue Name: EnableLUA 23 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILEValue Name: EnableFirewall 23 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILEValue Name: DoNotAllowExceptions 23 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILEValue Name: DisableNotifications 23 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE\AUTHORIZEDAPPLICATIONS\LISTValue Name: C:\Windows\SysWOW64\msiexec.exe 23 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE\AUTHORIZEDAPPLICATIONS\LISTValue Name: C:\Windows\SysWOW64\svchost.exe 23 <HKLM>\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\EXPLORER\RUN23 <HKLM>\SYSTEM\CONTROLSET001\SERVICES\SHAREDACCESS\PARAMETERS\FIREWALLPOLICY\STANDARDPROFILE\AUTHORIZEDAPPLICATIONS\LIST23 <HKCU>\SOFTWARE\AASPPAPMMXKVS\-993627007Value Name: -757413758 21 <HKCU>\SOFTWARE\AASPPAPMMXKVS\-993627007Value Name: 1011363011 21 <HKCU>\SOFTWARE\AASPPAPMMXKVS\-993627007Value Name: -1514827516 21 <HKCU>\SOFTWARE\AASPPAPMMXKVS\-993627007Value Name: 253949253 21
Mutexes Occurrences uxJLpe1m23 smss.exeM_204_15 <process name>.exeM_<pid>_3
IP Addresses contacted by malware. Does not indicate maliciousness Occurrences 20[.]72[.]235[.]8214 23[.]207[.]52[.]10913 23[.]207[.]56[.]10910 20[.]109[.]209[.]1089 20[.]103[.]85[.]339 20[.]81[.]111[.]858 20[.]84[.]181[.]625 20[.]53[.]203[.]501
Domain Names contacted by malware. Does not indicate maliciousness Occurrences support[.]microsoft[.]com23 updatewindows[.]net23
Files and or directories created Occurrences \409153595223 %SystemRoot%\system.ini19 %ProgramData%\dxwaolen.exe1 %ProgramData%\dxfbqp.exe1 %ProgramData%\dxpxcwowo.exe1 %ProgramData%\dxdaph.exe1 %ProgramData%\dxiybfjm.exe1 %ProgramData%\dxuiyaear.exe1 %ProgramData%\dxrflamrh.exe1 %ProgramData%\dxiaolh.exe1 %ProgramData%\dxczvbx.exe1 %ProgramData%\dxezxtat.exe1 %ProgramData%\dxayaahen.exe1 %ProgramData%\dxvdovort.exe1 %ProgramData%\dxupnglb.exe1 %ProgramData%\dxzliuhie.exe1 %ProgramData%\dxvros.exe1 %ProgramData%\dxxakx.exe1 %ProgramData%\dxueoa.exe1 %ProgramData%\dxoupe.exe1 %ProgramData%\dxhbtsa.exe1 %ProgramData%\dxquorfdh.exe1 %ProgramData%\dxyjlzmr.exe1 %ProgramData%\dxwetlif.exe1 %ProgramData%\dxcmiazi.exe1
File Hashes 155b235838bb38a009d3959a22afeefe29990bf08b886d450d5523a1e8ef52e9 1ab9fcb9422511f11ce386dd89602256b4423cc13df20d8cae15cf74ac96899c 1ebee245aa20139a5c0d78869e42cb7700b2c746fe554000dc24fd6d79b2dc7a 37ef12da9294aa84a551a49705c9aaeffa3e440ac9183e670aaae18de6f0cee9 38690107fc5ab4fc661469ab6d179f6a8f98ffc6abeeae8e8fb879fa24c92818 3c73ee4a0a2a9d2f78dd95d11df24a3d27c3a14ff2e6f56e014f10d0832bb869 4888ce37000aa2d5029dcdf080efb7ccf3b4ba347ee24103df15a3cb9be4dc5b 4d9868767a8260a2c0f663eb424f491de8cc1706ade137c59ce84c9da5e15e50 541a54f29dbcd3412f244a16098acf87f466699a5832270e4d7d642b067c32a1 56ecf33836287e107f9bda8a3522fddf9cc699f6e291990ab66753d692ac92b2 605c9f1b05b0b47ed4e99a34a526adfed8eb56ce724815fd207708c94313883e 6e99fec151c58577d9360fd6f846a0e436907258ad24b0117be07ab438b89abb 79e56d2705ee36750de0b2b521777d73ea3fec9faca7ca78a39c06ac5e689b0a 7bd446737e62430c0ed764392c1573c8b3b81ac3c969a473a7cab9849302eff4 83f4e46b5dd1811bd62b184710cb206ab7ac5ae0a52a797745fe400cde4ed2f4 8a99d2f8e63dc8bdfe9c10be15e65a881e473afa45dc349ad8a9bf387cb90e91 8f618126cfbdd291e149f978420a885cbc31876de6771c78a32b60edf47225a6 9c447450d5f5767d268341ebd7fdf3e50b302bae87d7ea1ca7ffc45d81b271ac aca2c69def78f145126fd8f2a9e88326ee74c80e59b704dd5a48a3de91effe94 c9216a18da434cd1d24b0e57e2f1236d3ebcd9d38d4b772153db4bb60a661b54 da3ee20e162f6ee44397e737ca1f7c3d371f41075414c959ddbdbb4d06dfbd94 e15c93bf9e1f8ad217103c0d9156cabc5a923ba3bf177b7cde178854a1efb243 f254301a5209750c391375336d9b93e19b45e557e0cd97a504df6b22d52facce
Coverage Product Protection Secure Endpoint Cloudlock N/A CWS Email Security Network Security Stealthwatch N/A Stealthwatch Cloud N/A Secure Malware Analytics Umbrella N/A WSA N/A
Screenshots of Detection Secure Endpoint
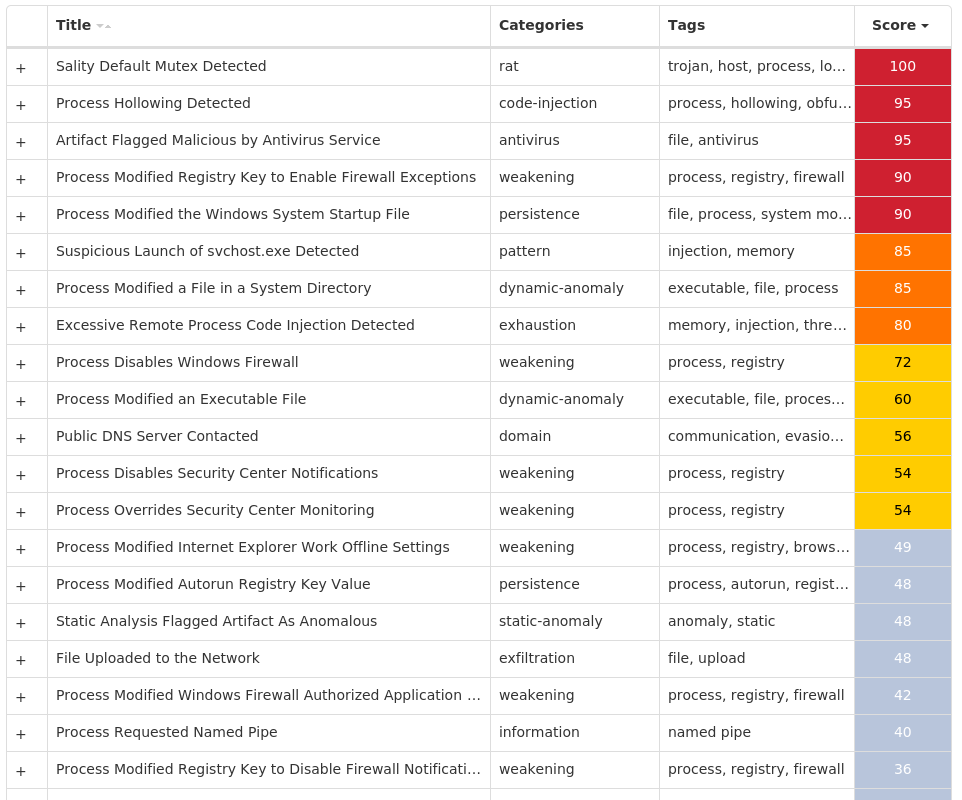
Secure Malware Analytics
MITRE ATT&CK