
Contributions from Matt Thaxton.
- Cisco Talos discovered a new attack framework including a command and control (C2) tool called "Alchimist" and a new malware "Insekt" with remote administration capabilities.
- The Alchimist has a web interface in Simplified Chinese with remote administration features.
- The attack framework is designed to target Windows, Linux and Mac machines.
- Alchimist and Insekt binaries are implemented in GoLang.
- This campaign consists of additional bespoke tools such as a MacOS exploitation tool, a custom backdoor and multiple off-the-shelf tools such as reverse proxies.
Cisco Talos has discovered a new single-file command and control (C2) framework the authors call "Alchimist [sic]." Talos researchers found this C2 on a server that had a file listing active on the root directory along with a set of post-exploitation tools.
Cisco Talos assesses with moderate-high confidence that this framework is being used in the wild.
"Alchimist" is a 64-bit Linux executable written in GoLang and packed with assets including resources for the web interface and Insekt RAT payloads compiled for Windows and Linux.
Insekt RAT, a new trojan Cisco Talos discovered, is Alchimist's beacon implant written in GoLang and has a variety of remote access capabilities that can be instrumented by the Alchimist C2 server.
Alchimist C2 has a web interface written in Simplified Chinese and can generate a configured payload, establish remote sessions, deploy payload to the remote machines, capture screenshots, perform remote shellcode execution and run arbitrary commands.
Among the remaining tools, Cisco Talos found a Mach-O dropper embedded with an exploit to target a known vulnerability CVE-2021-4034, a privilege escalation issue in polkit's pkexec utility, and a Mach-O bind shell backdoor. The Qualys Research Team discovered CVE-2021-4034 in November 2021, and in January 2022, the U.S.'s National Security Agency Cybersecurity Director warned that the vulnerability was being exploited in the wild.
The server also contained dual-use tools like psexec and netcat, along with a scanning tool called "fscan," which the author defines as an "intranet scanning tool," essentially all the necessary tools for lateral movement.
Alchimist framework
The attack framework we discovered during the course of this research consists of a standalone C2 server called "Alchimist" and its corresponding implants the authors call the "Insekt" RAT family.
Alchimist isn't the first self-contained framework we've discovered recently, with Manjusaka being another single file-based C2 framework disclosed by Talos recently. Both follow the same design philosophy, albeit implemented in different ways, to the point where they both seem to have the same list of requirements despite being implemented by different programmers.
However, Manjusaka and Alchimist have virtually the same set of features. They both have been designed and implemented to operate as standalone GoLang-based executables that can be distributed with relative ease to operators. The frameworks inside carry the implants and the whole web user interface. The implant configuration is defined using the Web UI (Web User Interface), which in both cases is completely written in Simplified Chinese. Also, they both mention the uncommon protocol SNI in one case already supported (Alchimist), with plans to support it in the other (Manjusaka).
The main differences lie in the approaches taken to implement the Web UI and the way the frameworks implement the single-file feature. Manjusaka developers take advantage of the Gin web framework and use packr, an asset bundling framework, to embed and store the implants. Alchimist authors took a more basic approach, using only the basic GoLang features to implement the same features.
There are also differences in the implant code, but functionality-wise, they are pretty similar, as they implement the features made available by the C2. We've observed that Alchimist, apart from the regular HTTP/S also supports protocols like SNI, WSS/WS, Manjusaka on the other hand, mentions SNI, WSS/WS on its documentation but only supports HTTP.
Unwrapping Alchimist
Assets
Alchimist uses GoLang-based assets (custom-made embedded packages) to store all the resources required for it to function as a C2 server. During the initialization of the C2 service, the process extracts all the embedded assets from the GoLang-based ELF binary of the C2 and drops them into hardcoded locations under the /tmp/Res/ directory.
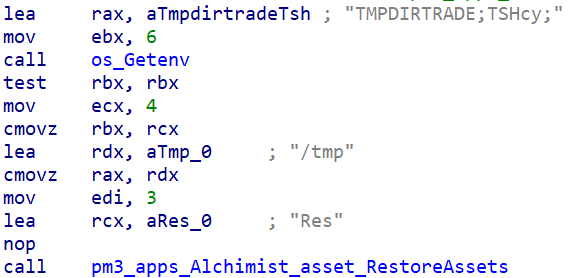
C2 ELF contains hardcoded destination directories for dropping the embedded assets.
All embedded assets are recursively placed in directories based on the way they are embedded in the GoLang asset package.
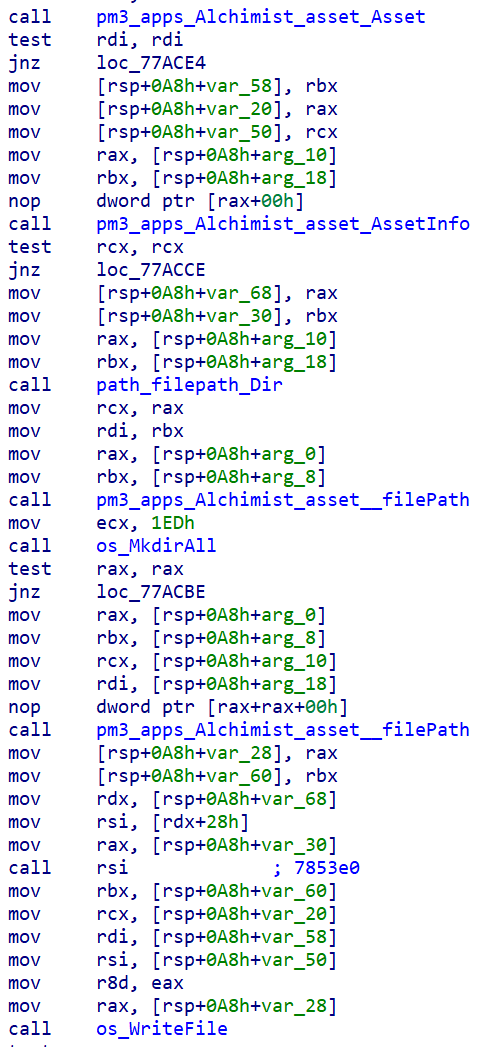
The "Res" directory contains web interface code, HTML files and other directories. It also unpacks its "Insekt" implant binaries, for the Windows and Linux operating systems into the "/tmp/Res/Payload" directory.
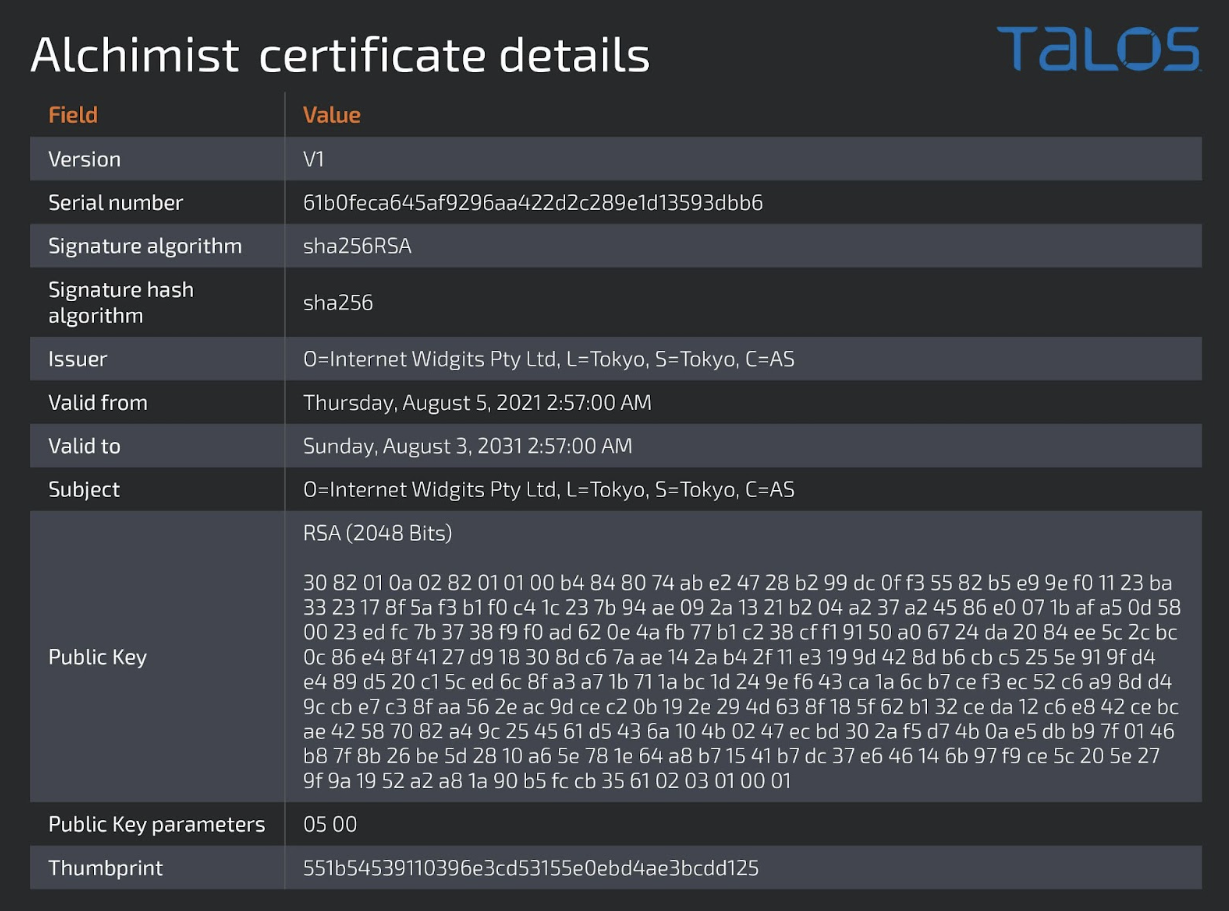
In the /tmp directory, the C2 also writes the self-signed certificate and the key used in HTTPS communications. Even though it is self-signed, the certificate is not generated upon execution. Rather, it is a hardcoded certificate added to the C2 at the time of compilation. The details of the certificate below also shows that the certificate doesn't contain any server name.
The web interface is written in Simplified Chinese, presenting several options to the operators.
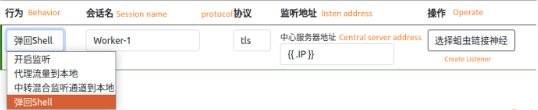
A detailed look into the Web UI shows features it supports all the common features one would expect in a RAT's C2.
One, however, stood out: The ability to generate PowerShell and wget code snippets for Windows and Linux, respectively. An attacker could use these commands to build their infection mechanism for distributing Insekt RAT. An attacker can embed these commands in a script (instrumented via a malicious entry point such as a maldoc, LNK, etc.) and deliver it to the victims by various means to gain an initial foothold, thereby downloading and implanting the Insekt RAT.

Delivery command snippets generated by Alchimist for Insekt payloads.
Payload generation
Alchimist accepts several parameters from the Web UI for generating a payload. This operator inputs the parameters into the "session[.]html" Web UI and consists of the following configuration:
- Protocol value: TLS, SNI, WSS/WS.
- Remote C2 host IP/URL.
- Platform type: Windows or Linux to select the type of Insekt RAT payload.
- Daemon flag: Indicates if the Insekt implant runs as a daemon on the infected endpoint.
- Predomain value: For the SNI protocol type only.
The Web UI will take these configuration values to construct a JSON and send a POST request to the "/pay" URL of the current C2 server to request a new payload that can be downloaded.

Web UI HTML code requesting the payload generation from the C2.
The request for generating the payload hits the "/pay" URL, where the C2 accepts the configuration parameters from the JSON, parses them and then generates the customized Insekt payload.
The C2 doesn't compile the Insekt payloads (also GoLang based) at all. It simply reads a dummy/skeleton Insekt binary (winx64 or ELFx64) that was unpacked during its initialization from the "/tmp/Res/Payloads/" directory into memory and hot patches the Insket binary in memory based on specific placeholder flags for the various values and dumps the patched Insekt binary to disk again. This new binary is then read from the disk by another helper routine in the C2 process and served to the operator via the Web UI.
C2 is looking to patch the C2 server value ${RHOST} in the Insekt dummy binary.
Communication protocol
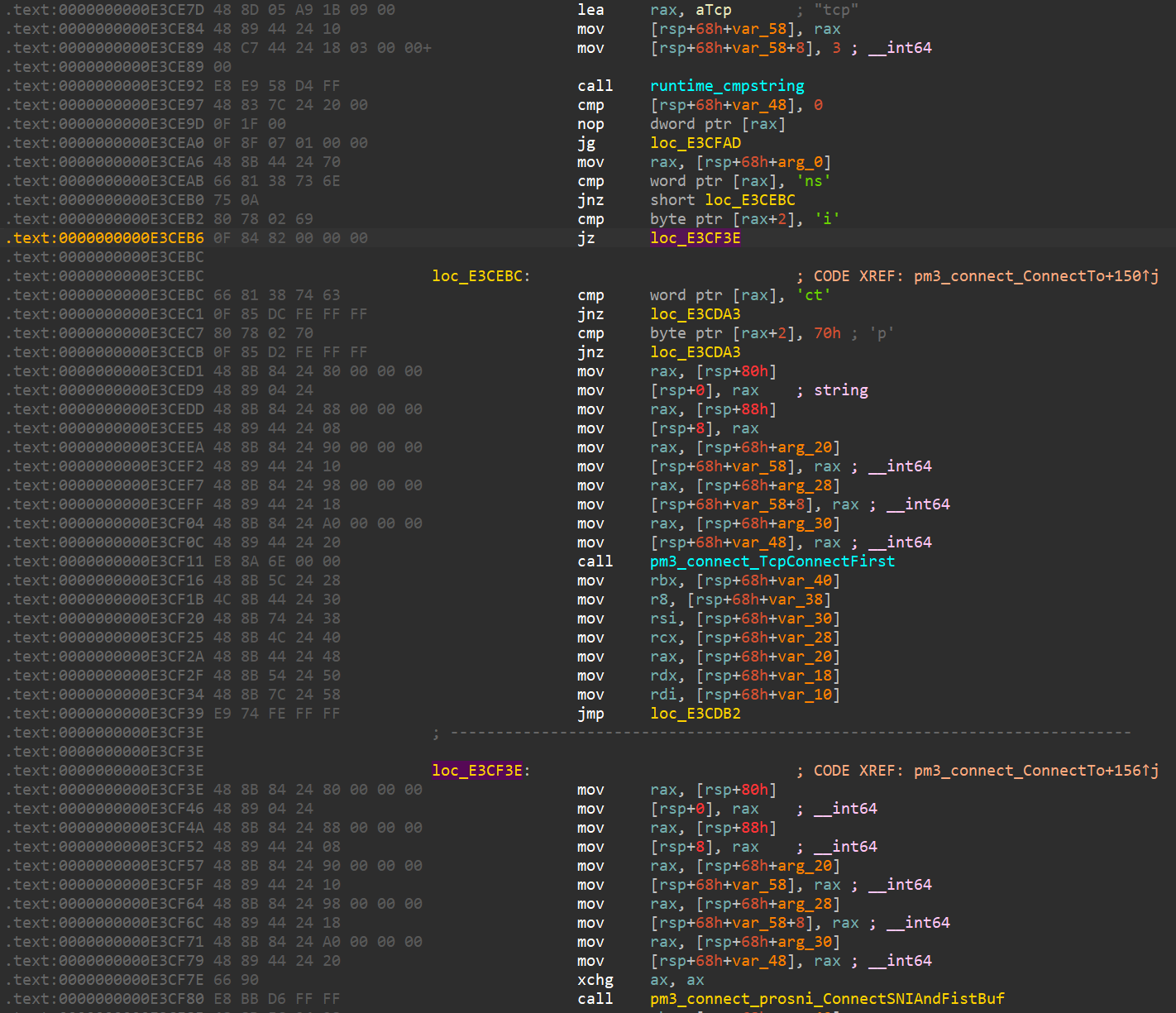
The communication logic with the Windows and Linux Insekt variants is similar. The communication is managed by the "pm3" GoLang package which implements establishing and managing connections to the WebSockets, plugin codes to scan IP addresses using the ICMP protocol, utility code to perform port forwarding, upload files to the remote machine and perform remote execution.
The C2 address is hard-coded on the implant at configuration time, which attempts to connect to the C2 server 10 times with an interval of one second. After ten unsuccessful attempts, the backdoor pauses and again attempts to connect to the C2 server once every hour.

The implant supports connecting to the C2 over either WSS/WS, TLS or SNI protocols.
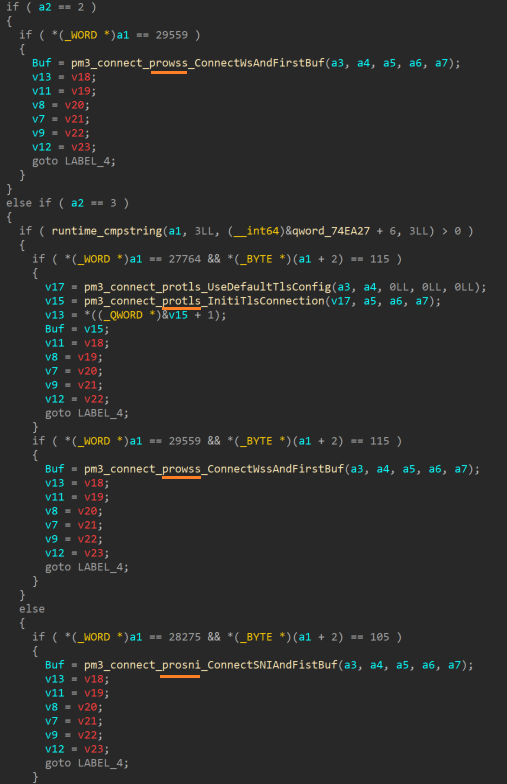
Based on the C2 URLs specified, the implant will use a specific protocol to initiate the check-in with the C2 server.
Insekt implant
Insekt is a 64-bit implant written in GoLang, compiled for Windows and Linux environments with a variety of RAT capabilities, all directed to execute by the Alchimist C2 server.
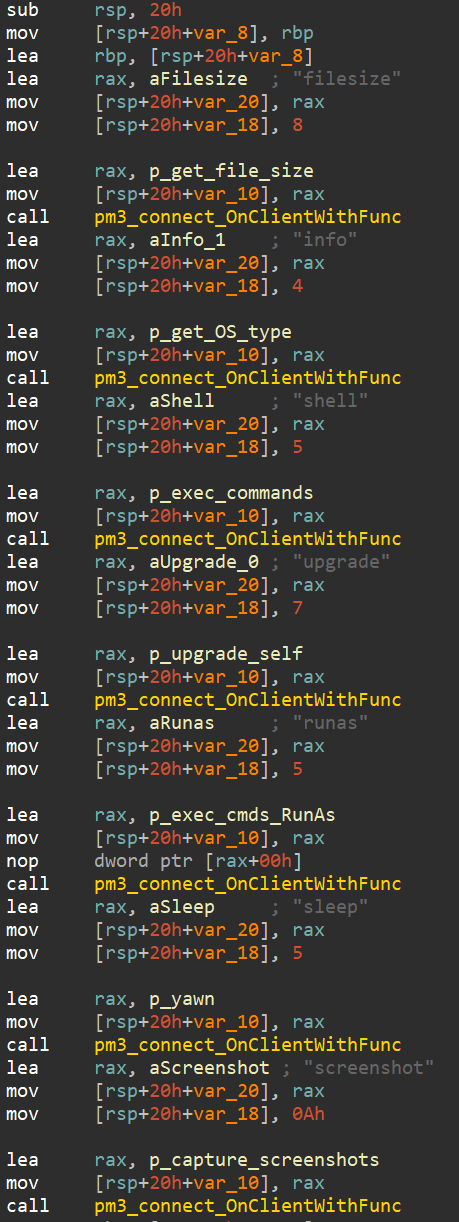
During initialization, the implant will set up multiple handlers for seven primary capabilities:
- Get file sizes.
- Get OS information.
- Run arbitrary commands via cmd[.]exe.
- Upgrade the current Insekt implant.
- Run arbitrary commands as a different user.
- Sleep for periods of time defined by the C2.
- Start/stop taking screenshots.
Insekt also checks the internet connectivity and port status by connecting to the addresses/ports below.
| Host | Port |
|---|---|
| localhost | 22 |
| localhost | 80 |
| localhost | 23 |
| localhost | 445 |
| localhost | 139 |
| www[.]google[.]com | 443 |
| www[.]apple[.]com | 443 |
| github[.]com | 443 |
Apart from these capabilities, the implant consists of other capabilities such as shellcode execution, port and IP scanning, SSH key manipulation, proxying connections, etc. described below.
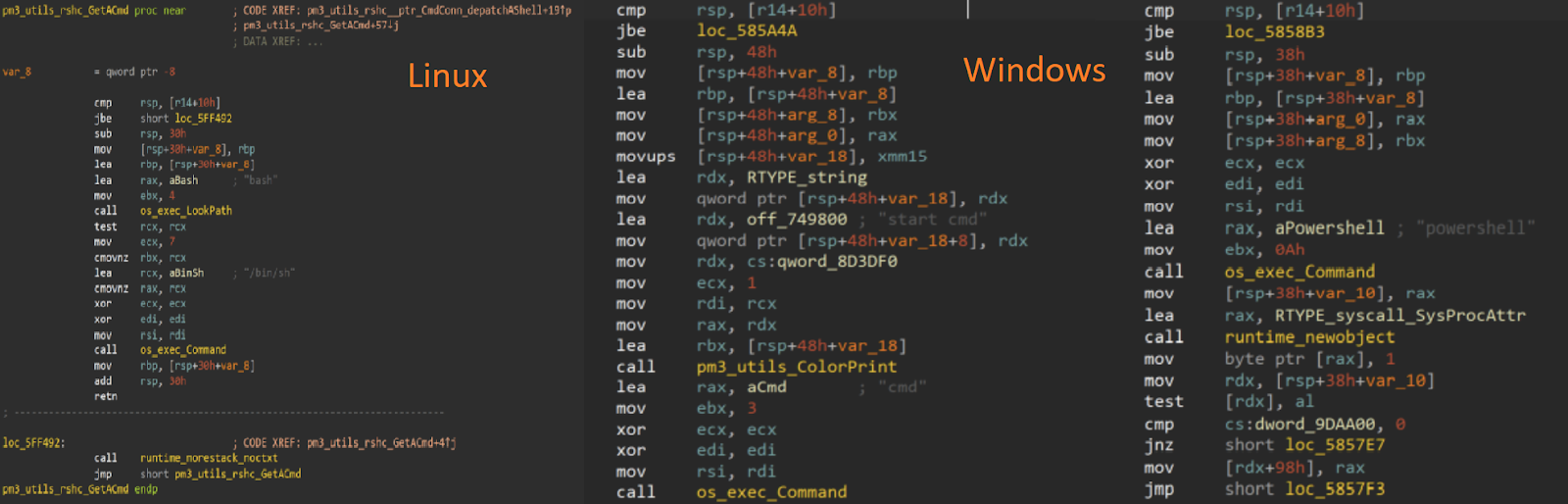
Both variants can execute arbitrary commands on the operating system shell, upon request from the operators.
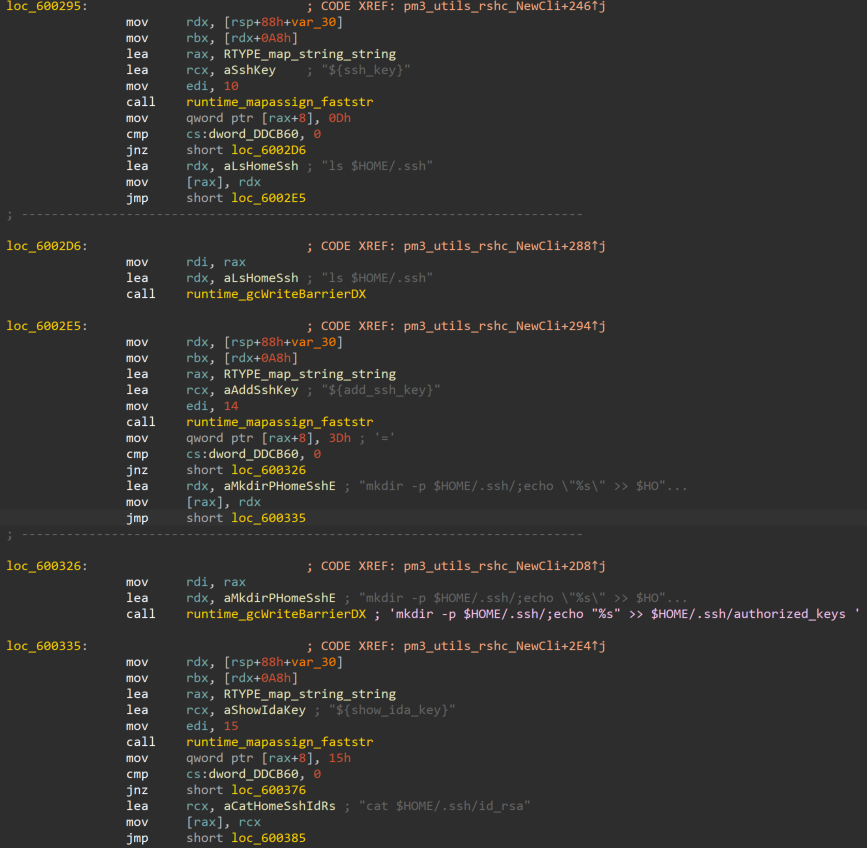
The Linux variant of Insekt also has the functionality to list the contents of ".ssh" directory in the victim's home directory and adds new SSH keys to the authorised_Keys file. Using this feature, the attacker can communicate with the victim's machine from the C2 over SSH.
From the network point-of-view, Insekt can create "proxy" connections to other systems by its own mechanism or by simply using the socks5 protocol.
Insekt also includes a module that implements the different commands that can be issued by the operators. In particular, it implements interactive shells based on PowerShell, bash and cmd[.]exe. It also has the ability to accept command codes from the Alchimist C2 to execute a predefined set of commands on the victim system. The table below lists such commands.
| Command | Action | Description |
|---|---|---|
| ${add_user} | net user add {user} /random /add | Creates a user [T1136] |
| ${add_admin} | net localgroup administrators {user} /add | Assign privileges [T1136] |
| ${domain_ls} | net user /domain | List users in domain [T1087/002] |
| ${domain_show} | net group "domain admins" /domain | List domain administrators [T1087/002] |
| ${dc} | net group "domain controllers" /domain | List domain controllers [T1087/002] |
| ${2003_rdp_reg} | “hklm/system/CurrentControlSet/Control/Terminal Server" /v fDenyTSConnections | Activate terminal services [T1021/001] |
| ${close_firewall} | netsh firewall set opmode mode=disable | Disable firewall [T1562/004] |
| ${in-port-allow-tcp} | netsh advfirewall firewall add rule name=\"Allow port\" dir=in action=allow protocol=TCP localport={port} | Change firewall rules to allow incoming connections on a specific tcp port [T1562/004] |
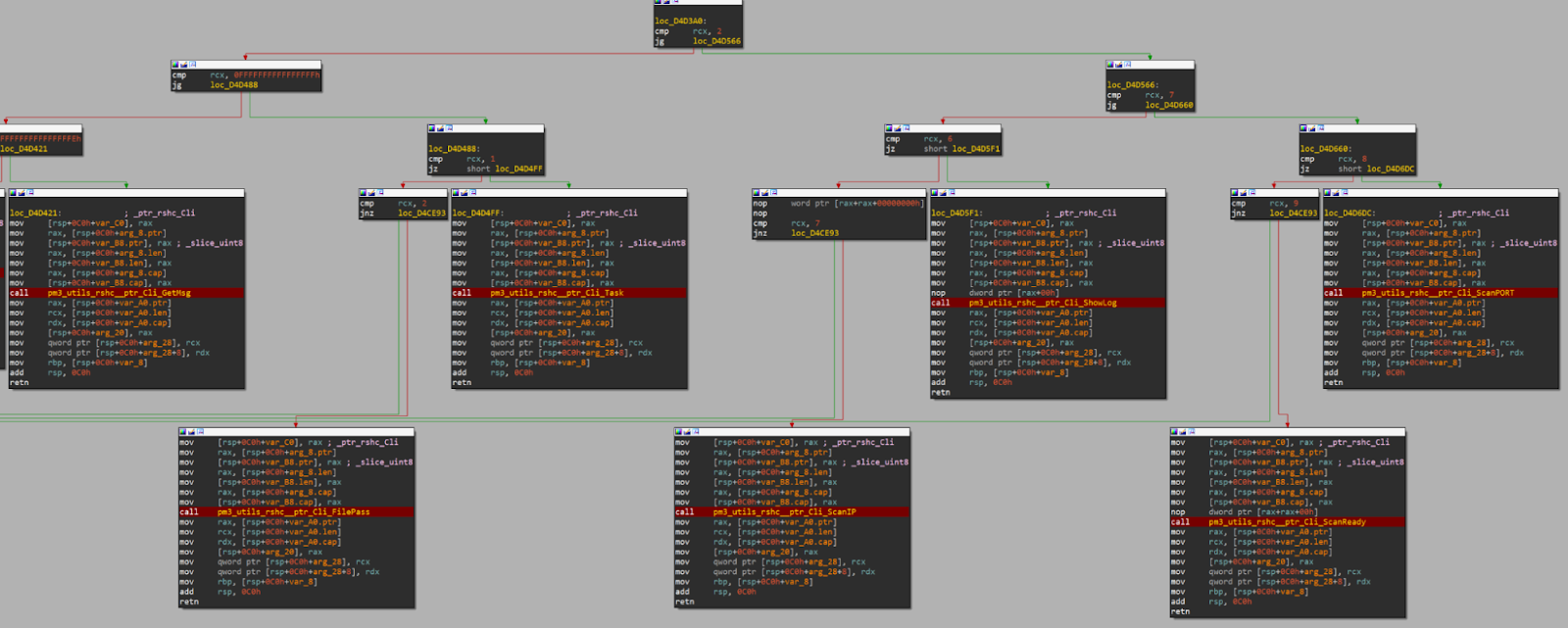
A module named "Command Line Interface (CLI)" in Insekt contains RAT styled capability implementations — command codes and data received from the C2 — for carrying out specific RAT actions on the infected endpoint. These capabilities consist of:
- Change directory - cd.
- Write files to disk.
- Execute arbitrary commands.
- Scan IPs.
- Scan specific ports for an IP.
- Enumerate file in a directory path.
- Download files from a remote location.
- Unzip archive files to a location on disk.
Other tools
Along with Alchimist, Cisco Talos also found tools for the elevation of privileges and eventual exploitation of MacOSX platforms. Talos found two tools whose source code can be found on GitHub: Fast reverse proxy (frp), which can be used for data exfiltration and Fscan, an intranet-scanning tool.
MacOSX exploitation
The Mach-O file discovered in the open directory is a 64-bit executable written in GoLang embedded with an exploit and a bind shell backdoor. The dropper contains an exploit for a privilege escalation vulnerability (CVE-2021-4034) in polkit's pkexec utility. However, this utility is not installed on MacOSX by default, meaning the elevation of privileges is not guaranteed. Along with the exploit, the dropper would bind a shell to a port providing the operators with a remote shell on the victim machine. The same exploit was also found for Linux.
Scriptlet
Alchimist can generate scripts to be used in the first stage of infections. One of these scripts was found with the name "down[.]sct." The script launches a WScript[.]shell object to run a PowerShell command and download the Insekt implant from http[://]45[.]32[.]132[.]166/msconfig[.]zip.
Shellcode
A meterpreter shellcode was found on a file with the name shell.msi. It has the malicious configuration containing the host and the port details for the shell code to connect to 18[.]167[.]90[.]252, providing Talos with one more piece of the operator's infrastructure.
Infrastructure
Malicious Infrastructure
The web archive scans report of the host 45[.]32[.]132[.]166 showed us that it had an open directory in January 2022, but it was offline at the time of our analysis.

Command and control
The certificate shows the serial number — 61b0feca645af9296aa422d2c289e1d13593dbb6 — and fingerprint — 134a3d105eef24fab27ed0fb3729e271306bde6dc4e9d2a4a5c5d1c82b0390fe — we discovered five hosts containing the same certificate:
- 149[.]28[.]54[.]212
- 95[.]179[.]246[.]73
- 149[.]28[.]36[.]160
- 45[.]76[.]68[.]112
- 3[.]86[.]255[.]88
Our analysis revealed that the backdoors communicated over HTTPS to the server 149[.]28[.]54[.]212 and the Alchimist user interface was accessible via ports 8443 and 50423 from servers 149[.]28[.]54[.]212, 95[.]179[.]246[.]73, and 149[.]28[.]36[.]160.
The rise of all-inclusive C2 frameworks
Our discovery of Alchimist is yet another indication that threat actors are rapidly adopting off-the-shelf C2 frameworks to carry out their operations. A similar ready-to-go C2 framework called "Manjusaka'' was recently disclosed by Talos. Alchimist also comprises a single-file based, ready-to-go C2 tool along with its remote access tool Insekt, implemented in GoLang and compiled to target Windows and Linux machines.
The functionality of Manjusaka and Alchimist's web interfaces exhibiting remote administration capabilities, performed through the RATs, signifies the plethora of functionalities packed into these C2 frameworks. A threat actor gaining privileged shell access on a victim's machine is like having a Swiss Army knife, enabling the execution of arbitrary commands or shellcodes in the victim's environment, resulting in significant effects on the target organization.
Endpoint security teams should implement layered security defense, be constantly vigilant in monitoring the privileged operations in their environments and detect any unauthorized programs attempting to gain root privileges. Network security teams should be looking for any unusual traffic to their organizations' environment and be cautious about suspicious artifacts downloaded to their network. Having controlled download and file execution policies on the endpoints and servers can effectively protect organizational assets from threats.
Organizations and users who are using the vulnerable versions of polkits pkexec utilities should patch their systems following the mitigation steps as advised by RedHat. For the users of Unix-like systems other than Linux, who cannot find patches for their operating systems, a workaround could be implemented by removing the SUID-bit of pkexec utility.
Coverage
Ways our customers can detect and block this threat are listed below.

Cisco Secure Endpoint (formerly AMP for Endpoints) is ideally suited to prevent the execution of the malware detailed in this post. Try Secure Endpoint for free here.
Cisco Secure Web Appliance web scanning prevents access to malicious websites and detects malware used in these attacks.
Cisco Secure Email (formerly Cisco Email Security) can block malicious emails sent by threat actors as part of their campaign. You can try Secure Email for free here.
Cisco Secure Firewall (formerly Next-Generation Firewall and Firepower NGFW) appliances such as Threat Defense Virtual, Adaptive Security Appliance and Meraki MX can detect malicious activity associated with this threat.
Cisco Secure Malware Analytics (Threat Grid) identifies malicious binaries and builds protection into all Cisco Secure products.
Umbrella, Cisco's secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs and URLs, whether users are on or off the corporate network. Sign up for a free trial of Umbrella here.
Cisco Secure Web Appliance (formerly Web Security Appliance) automatically blocks potentially dangerous sites and tests suspicious sites before users access them.
Additional protections with context to your specific environment and threat data are available from the Firewall Management Center.
Cisco Duo provides multi-factor authentication for users to ensure only those authorized are accessing your network.
The following ClamAV signatures have been released to detect this threat:
- Osx.Exploit.CVE_2021_4034-9951522-2
- Unix.Exploit.CVE_2021_4034-9951523-0
- Unix.Exploit.CVE_2021_4034-9951524-0
- Unix.Exploit.CVE_2021_4034-9951525-0
- Unix.Exploit.CVE_2021_4034-9951526-0
- Unix.Malware.Insekt-9955436-0
- Win.Malware.Insekt-9955440-0
- Unix.Malware.Alchimist-9955784-0
- Multios.Malware.Insekt-9961177-0
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org. Snort SIDs for this threat are 58955 - 58956.
IOCs
The IOC list is available in Talos' Github repo here.