A Deep Dive into Lokibot Infection Chain
Lokibot is one of the most well-known information stealers on the malware landscape. In this post, we'll provide a technical breakdown of one of the latest Lokibot campaigns. Talos also has a new script to unpack the dropper's third stage. The actors behind Lokibot usu
Talos tools of the trade
By Andrea Marcelli and Holger Unterbrink. If you're looking for something to keep you busy while we're all stuck inside during the holidays, Cisco Talos has a few tools for you you can play with in the coming days and weeks. We recently updated GhIDA to work with the l
Dynamic Data Resolver - Version 1.0.1 beta
By Holger Unterbrink. 12/17/20 Update: A new version of this software and associated blog can be found here Cisco Talos is releasing a new beta version of Dynamic Data Resolver (DDR) today. This release comes with a new architecture for samples using multi-threading. The proce
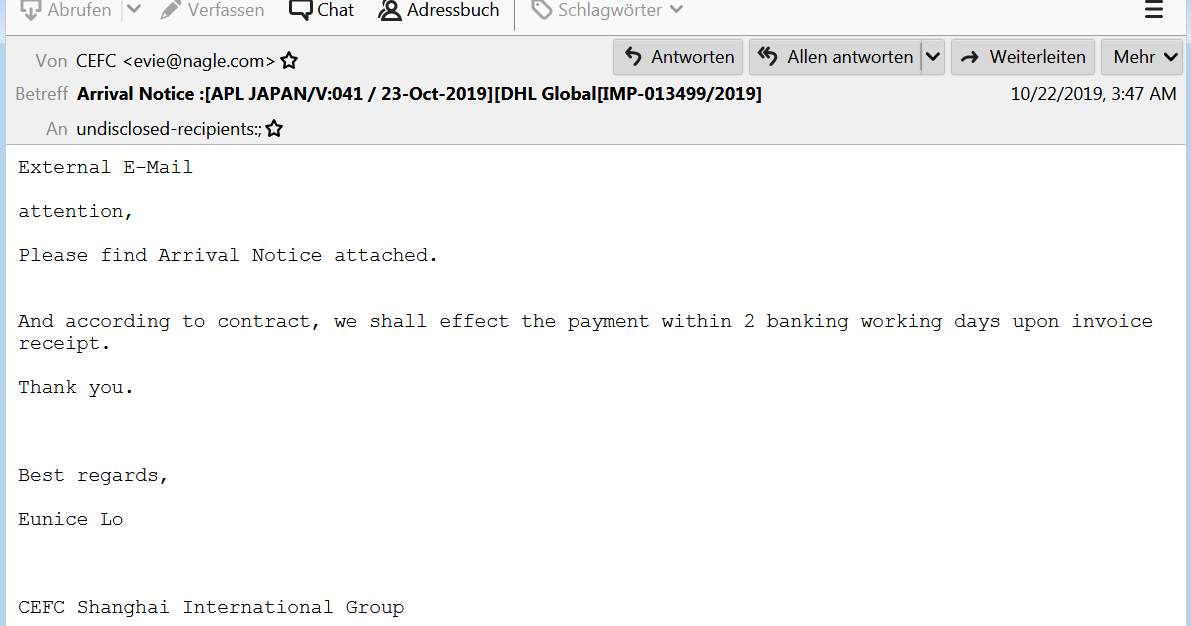
Salfram: Robbing the place without removing your name tag
Threat summary * Cisco Talos recently uncovered a series of email campaigns utilizing links to malicious documents hosted on legitimate file-sharing platforms to spread malware. * The campaigns distributed various malware payloads including Gozi ISFB, ZLoader, SmokeLoader and
Barbervisor: Journey developing a snapshot fuzzer with Intel VT-x
By Cory Duplantis. One of the ways vulnerability researchers find bugs is with fuzzing. At a high level, fuzzing is the process of generating and mutating random inputs for a given target to crash it. In 2017, I started developing a bare metal hypervisor for the purposes of snap
Dynamic Data Resolver (DDR) — IDA Plugin 1.0 beta
10/20/20 Update: A new version of this software and associated blog can be found here Executive summary Static reverse-engineering in IDA can often be problematic. Certain values are calculated at run time, which makes it difficult to understand what a certain basic block is d