Astaroth, Mekotio & Ousaban abusing Google Cloud Run in LATAM-focused malware campaigns
Since September 2023, we have observed a significant increase in the volume of malicious emails leveraging the Google Cloud Run service to infect potential victims with banking trojans.
TinyTurla Next Generation - Turla APT spies on Polish NGOs
This new backdoor we’re calling “TinyTurla-NG” (TTNG) is similar to Turla’s previously disclosed implant, TinyTurla, in coding style and functionality implementation.
Generating FLIRT signatures for Nim and other non-C programming languages
Cisco Talos is excited to announce a new project to find an automated way to generate custom FLIRT signatures for IDA.
Microsoft Patch Tuesday for February 2023 — Snort rules and prominent vulnerabilities
Microsoft released its monthly security update on Tuesday, disclosing 73 vulnerabilities. Of these vulnerabilities, 8 are classified as “Critical”, 64 are classified as “Important”, one vulnerability is classified as “Moderate.” According to Microsoft none of the vulnerabilities
Microsoft Patch Tuesday for January 2023 — Snort rules and prominent vulnerabilities
Microsoft released its monthly security update on Tuesday, disclosing 101 vulnerabilities. Of these vulnerabilities, 11 are classified as “Critical”, 89 are classified as “Important”, no vulnerability classified as “Moderate.”
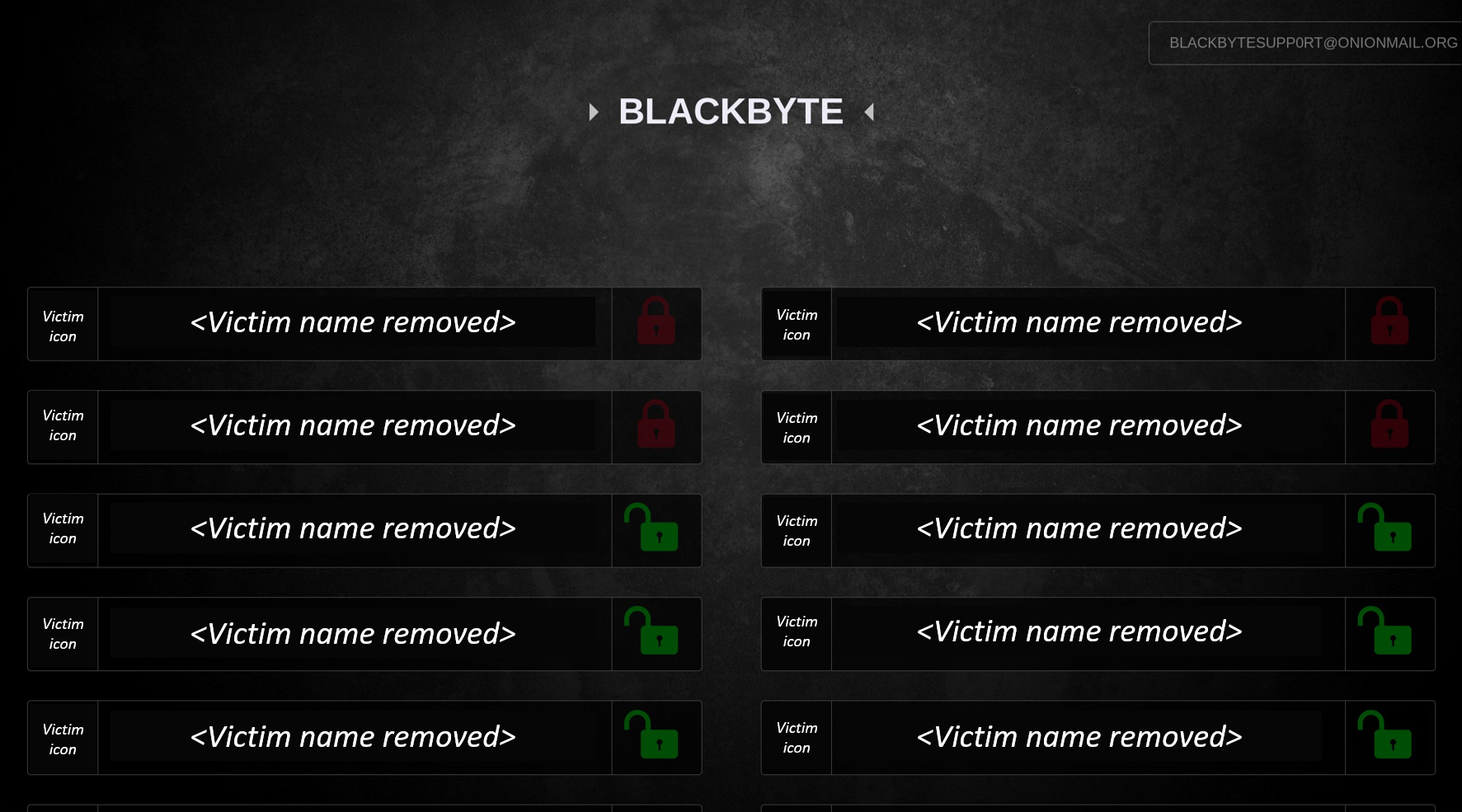
The BlackByte ransomware group is striking users all over the globe
News summary * Cisco Talos has been monitoring the BlackByte Ransomware Group for several months, infecting victims all over the world, from North America to Colombia, Netherlands, China, Mexico and Vietnam. * The FBI released a joint cybersecurity advisory in February 2022 wa
The BlackByte ransomware group is striking users all over the globe
News summary * Cisco Talos has been monitoring the BlackByte Ransomware Group for several months, infecting victims all over the world, from North America to Colombia, Netherlands, China, Mexico and Vietnam. * The FBI released a joint cybersecurity advisory in February 2022 wa
TinyTurla - Turla deploys new malware to keep a secret backdoor on victim machines
News summary * Cisco Talos recently discovered a new backdoor used by the Russian Turla APT group. * We have seen infections in the U.S., Germany and, more recently, in Afghanistan. * It is likely used as a stealth second-chance backdoor to keep access to infected devices *
Cheating the cheater: How adversaries are using backdoored video game cheat engines and modding tools
By Nick Lister and Holger Unterbrink, with contributions from Vanja Svajcer. News summary * Cisco Talos recently discovered a new campaign targeting video game players and other PC modders. * Talos detected a new cryptor used in several different malware campaigns hidden