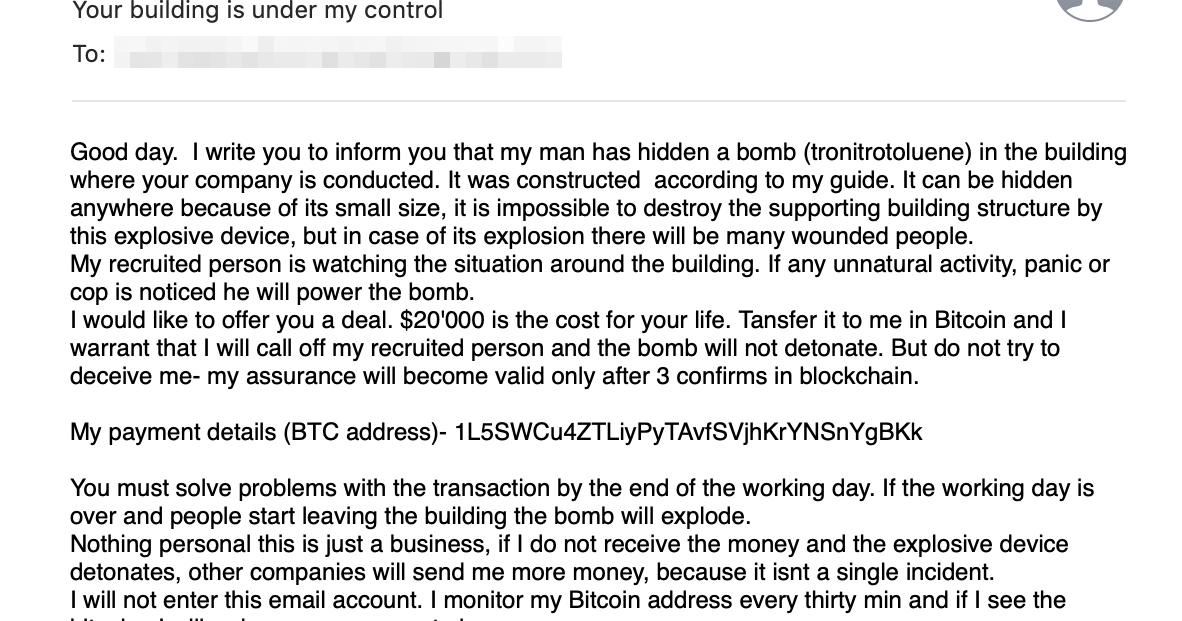
Bitcoin Bomb Scare Associated with Sextortion Scammers
The claims in the emails we've seen from this actor are completely false, yet they have caused untold amounts of damage as organizations have evacuated buildings and called upon law enforcement to investigate.
Anatomy of a sextortion scam
While these attacks have been in the wild for months, Talos wanted to take a closer look at some of these campaigns to see why users were being tricked into sending the attackers large amounts of bitcoin despite the attackers' empty threats.
The Many Tentacles of the Necurs Botnet
This post was written by Jaeson Schultz. Introduction Over the past five years the Necurs botnet has established itself as the largest purveyor of spam worldwide. Necurs is responsible for emailing massive amounts of banking malware, ransomware, dating spam, pump-n-dump stock s
On Conveying Doubt
This post was authored by Matt Olney. Typically, Talos has the luxury of time when conducting research. We can carefully draft a report that clearly lays out the evidence and leads the reader to a clear understanding of our well supported findings. A great deal of time is spent
In the Eye of the Hailstorm
This blog post was authored by Jakob Dohrmann, David Rodriguez, and Jaeson Schultz. The Cisco Talos and Umbrella research teams are deploying a distributed hailstorm detection system which brings together machine learning, stream processing of DNS requests and the curated Talos
The Rising Tides of Spam
This blog post was authored by Jaeson Schultz. For the past five years we have enjoyed a relatively calm period with respect to spam volumes. Back at the turn of the decade the world was experiencing record-high volumes of spam. However, with the evolution of new anti-spam techn
Microsoft Patch Tuesday - September 2016
This post was authored by Jaeson Schultz. Well it's Microsoft Patch Tuesday, again, and that must mean we are girding our systems against another round of security vulnerabilities. This month Microsoft has released fourteen (14) bulletins covering fifty (50) security vulnera
Vulnerability Spotlight: Oracle's Outside In Technology, Turned Inside-Out
Vulnerabilities discovered by Aleksandar Nikolic. Blog post authored by Jaeson Schultz and Aleksandar Nikolic. One of the most fundamental tasks performed by many software programs involves the reading, writing, and general processing of files. In today's highly networked en
The Poisoned Archives
Vulnerabilities discovered by Marcin “Icewall” Noga. Blog post authored by Marcin Noga and Jaeson Schultz. Update 2016-08-01: Talos has produced a video demonstrating how flaws in libarchive can be exploited using Splunk 6.4.1 as an attack vector. Release 3.2.1 of Libarchive add