How do cryptocurrency drainer phishing scams work?
In recent months, a surge in cryptodrainer phishing attacks has been observed, targeting cryptocurrency holders with sophisticated schemes aimed at tricking them into divulging their valuable credentials.
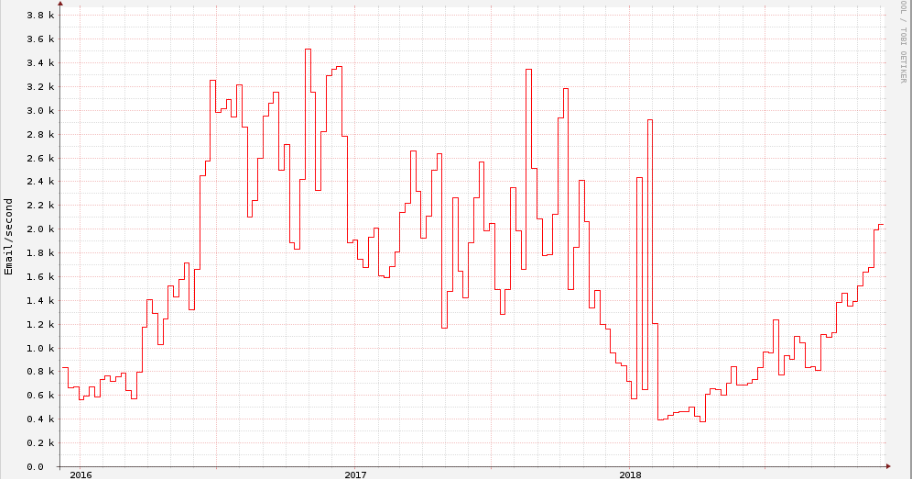
Following the Money: Comparing cryptocurrency value to illicit mining activity
By Nick Biasini In the age of meme stocks, Robinhood and Elon Musk's tweets influencing the global economy, cryptocurrency mining has not seemed as fringe as it once did. Mining has been around as long as these crytocurrencies have, but only really started to gather the att
Lemon Duck brings cryptocurrency miners back into the spotlight
By Vanja Svajcer, with contributions from Caitlin Huey. * We are used to ransomware attacks and big-game hunting making headlines, but there are still methods adversaries use to monetize their efforts in less intrusive ways. * Cisco Talos recently recorded increased activity
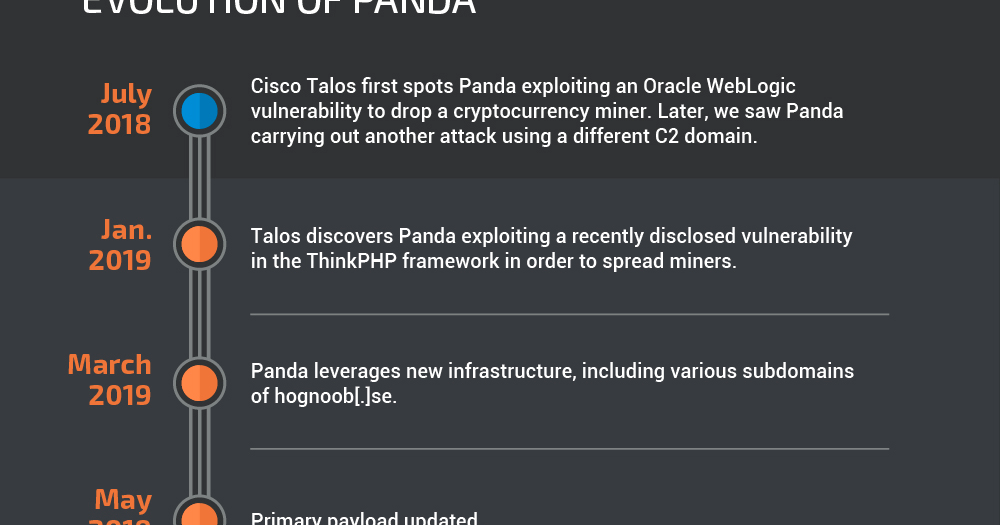
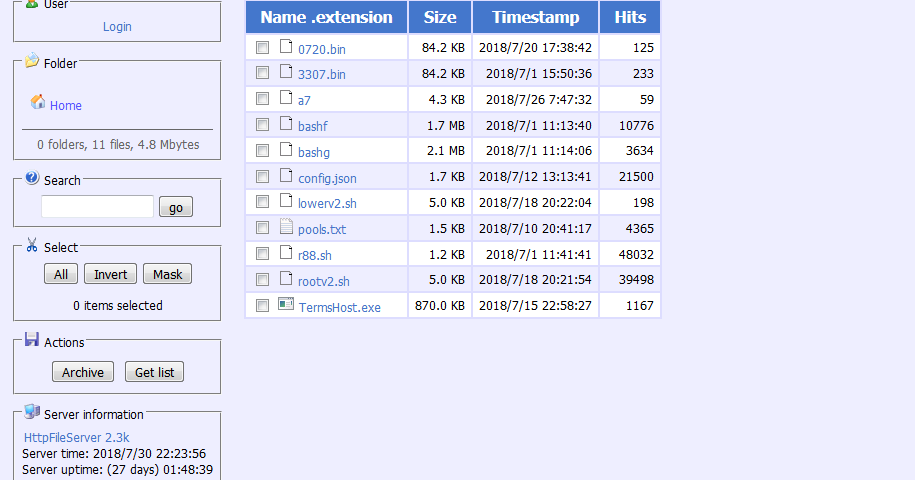
Cryptocurrency miners aren’t dead yet: Documenting the voracious but simple “Panda”
By Christopher Evans and David Liebenberg. Executive summary A new threat actor named "Panda" has generated thousands of dollars worth of the Monero cryptocurrency through the use of remote access tools (RATs) and illicit cryptocurrency-mining malware. This is far fr
Cyber Security Week in Review (March 1)
Cyber Security Week in Review (Feb. 15, 2019)
Cyber Security Week in Review (Feb. 8)
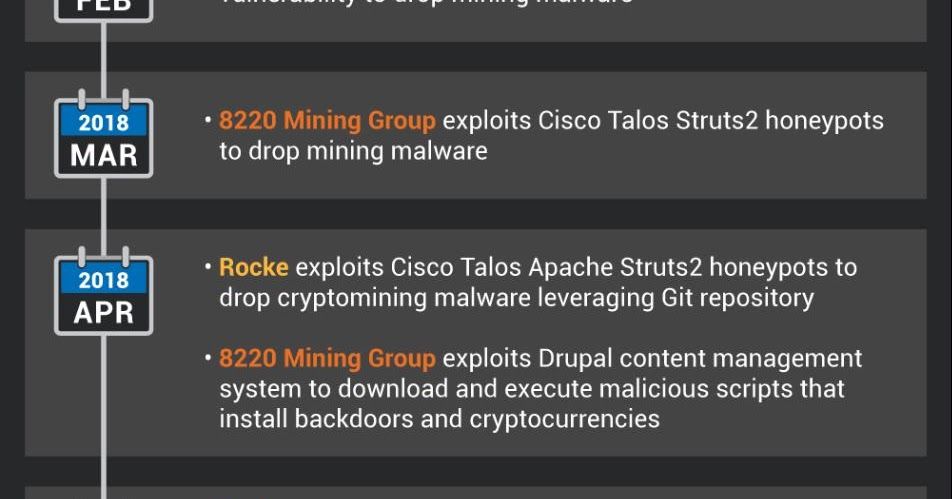
Connecting the dots between recently active cryptominers
Post authored by David Liebenberg and Andrew Williams. Executive Summary Through Cisco Talos' investigation of illicit cryptocurrency mining campaigns in the past year, we began to notice that many of these campaigns shared remarkably similar TTPs, which we at first mistak
As Cryptocurrency Crash Continues, Will Mining Threat Follow?
Rocke: The Champion of Monero Miners
This post was authored by David Liebenberg. Summary Cryptocurrency miners are becoming an increasingly significant part of the threat landscape. These malicious miners steal CPU cycles from compromised devices to mine cryptocurrencies and bring in income for the threat actor.
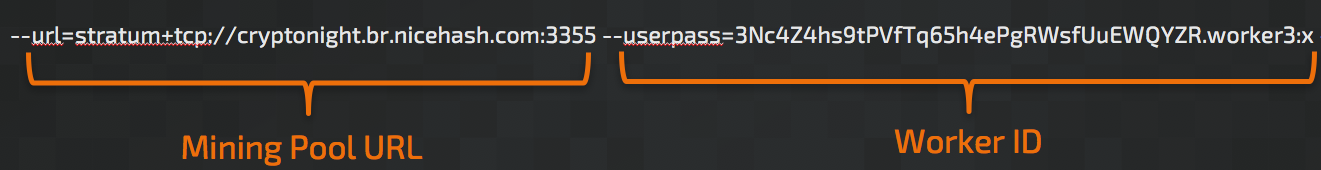
Blocking Cryptocurrency Mining Using Cisco Security Products
Cisco Talos is releasing a whitepaper addressing Cryptocurrency mining and all the ways to block it using Cisco Security products. The value of cryptocurrencies has fluctuated wildly, but the value is still high enough to garner a lot of attention, both legitimate and malicious.
Cryptomining Campaign Returns Coal and Not Diamond
Ransom Where? Malicious Cryptocurrency Miners Takeover, Generating Millions
his post was authored by Nick Biasini, Edmund Brumaghin, Warren Mercer and Josh Reynolds with contributions from Azim Khodijbaev and David Liebenberg. Executive Summary The threat landscape is constantly changing; over the last few years malware threat vectors, methods and pay