Updated on July 6, 2021:
As analysis of the ransomware attack affecting organizations using Kaseya VSA has continued, we are sharing an update containing additional information. As new details are identified, this information may be updated as needed.
- This event consisted of two separate, but related incidents. The initial compromise was the result of a zero-day attack against MSSPs that enabled adversaries to conduct a service supply chain attack on additional victims.
- The initial compromise of Kaseya VSA servers appears to have been the result of the successful exploitation of an unpatched software vulnerability (CVE-2021-30116) which allowed attackers to obtain privileged access to vulnerable Kaseya VSA servers for the purposes of ransomware deployment.
- Ransom demands varied across victim organizations. This indicates that once attackers obtained access to VSA servers, the server configuration was analyzed to identify victims prior to the activation of malicious ransomware payloads.
- The absence of data exfiltration activity, deletion of shadow copies on infected systems, and the advertisement of a campaign-wide decryption key is a notable divergence from the TTPs typically observed during REvil ransomware attacks.
- The REvil ransomware samples identified as being associated with this attack were configured to disable communication with C2 infrastructure that is normally used to send encryption information and statistics.
- During the infection process, the current system time is compared to July 2, 2021 at 12:30 ET. At this time, the ping function is executed, which causes a delay between the initial infection and when additional malicious activity may be detected on systems.
Event Timeline
July 2, 2021
- The first observed command execution activity indicating an attack in progress occurred at 10:30:58 ET. The parent process, in this case, was the Kaseya Agentmon process.
- The first observed execution of the dropper mechanism in the wild occurred at 12:26:00 EDT. (D55F983C994CAA160EC63A59F6B4250FE67FB3E8C43A388AEC60A4A6978E9F1E)
- Gen:Variant.Graftor.952042 was first detected on July 2, 2021 at 12:31:40 ET when malicious activity resumed following the previously described initial delay period.
- Users with malicious activity protection detected this activity as W32.MAP.Ransomware.rewrite. The initial detection of activity associated with this attack occurred on 07/02/21 at 12:32:08 EDT.
- Additional detection was provided by W32.D55F983C99-100.SBX.TG, W32.File.MalParent, W32.RetroDetected.
- The first observed execution of the DLL in the wild occurred at 12:30:24 EDT. (8DD620D9AEB35960BB766458C8890EDE987C33D239CF730F93FE49D90AE759DD)
- A Reddit thread was posted around 12:30 ET.
- Reports began to surface of a large-scale REvil ransomware attack associated with Kaseya VSA within a few hours.
- Kaseya released a statement at 16:11 EDT with recommendations to shut down all VSA and SaaS Servers.
- CISA released an alert related to the ongoing campaign.
July 4, 2021
- Kaseya released the VSA Detection Tool to help determine if the VSA server or managed endpoint has been compromised.
- CISA & FBI released additional guidance for MSPs.
- Dutch Institute for Vulnerability Disclosure (DIVD) announced they alerted Kaseya to CVE-2021-30116 and were working through the coordinated disclosure process when the attacks started.
- The White House released a statement by the deputy national security advisor for cyber and emerging technology on reporting Kaseya compromises.
July 6, 2021
- Kaseya released additional details, confirming the use of a zero-day vulnerability and including IOCs as well as victimology information indicating that at least 60 customers and 1,500 downstream businesses had been affected.
Key Takeaways
It is important to note that organizations that make use of Kaseya VSA may have been compromised even in the absence of a successful ransomware deployment. This is not the first instance of remote management software being used as the initial entry point during a ransomware campaign. Given how Kaseya VSA is typically deployed, many organizations are being targeted due to the successful compromise of upstream services providers like MSSPs similar to previous services supply chain attacks such as DNSpionage and Sea Turtle, which Cisco Talos uncovered in 2018.
Coverage
The following coverage has been issued to detect various components of this attack.
SNORTⓇ SID: 57879
Cisco Secure Endpoint
- Gen:Variant.Graftor.952042
- W32.D55F983C99-100.SBX.TG
- W32.File.MalParent
- W32.RetroDetected
ClamAV
- Win.Dropper.REvil-9875493-0
- Win.Ransomware.REvil-9875494-0
Cloud IOCs
- W32.PingPredicatedDel.ioc
- W32.DisableRealtimeMonitoring.ioc
- W32.CertutilDecodedExecutableFile.ioc
- W32.CertUtilCopy.ioc
Executive Summary
Attackers are actively exploiting the Kaseya VSA endpoint monitoring software to conduct a widespread supply chain attack targeting a number of Managed Service Providers (MSPs), according to multiple reports. Organizations usually use Kaseya VSA to perform centralized orchestration of systems in customer environments.Attackers first infected victims via a malicious automatic update to the software, eventually delivering the REvil/Sodinokibi ransomware. Once active in victim environments, the ransomware encrypts the contents of systems on the network, causing widespread operational disruptions to a variety of organizations that use this software. REvil operates using a ransomware-as-a-service (RaaS) model, with affiliates leveraging a variety of tactics, techniques and procedures (TTPs) to infect victims and coerce them into paying to regain access to systems and data that are affected by the ransomware. In many cases, backup servers are also targeted during network-based ransomware attacks highlighting the importance of a regularly tested offline backup and recovery strategy. A text-based README is written into various directories on the system and functions as a ransom note. An example of one of these files can be seen below:
Below, you can also see the portal the attackers use as a way to receive their extortion payments
Kaseya’s current recommendation is to, “IMMEDIATELY shutdown your VSA server until you receive further notice from us. It's critical that you do this immediately, because one of the first things the attacker does is shutoff administrative access to the VSA.”
As mentioned above, backup servers may be targeted, so it’s paramount to have regularly tested offline backups and recovery strategies in place. Attackers can target backups that may be accessible via the network. Utilize the 3-2-1 method to keep your data safe: three copies of your data, on two different systems, with one copy stored offline.
Coverage
Ways our customers can detect and block this threat are listed below.
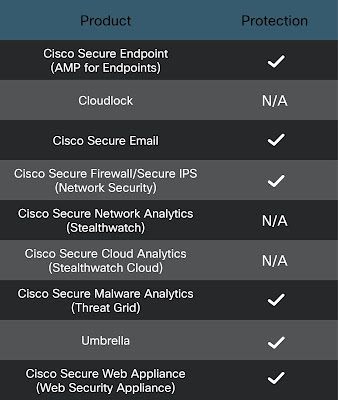
Cisco Secure Endpoint (formerly AMP for Endpoints) is ideally suited to prevent the execution of the malware detailed in this post. Try Secure Endpoint for freehere.
In the event that these malicious files are sent via email Cisco Secure Email (formerly Cisco Email Security) will convict them. You can try Secure Email for free here.
Cisco Secure Web Appliance web scanning prevents access to malicious websites and detects malware used in these attacks in the event these files are download via web.
Umbrella, Cisco’s secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs and URLs, whether users are on or off the corporate network. In this attack in the event these malicious files are download via web they will be blocked. Sign up for a free trial of Umbrella here.
Cisco Secure Firewall and Meraki MX can detect malicious activity associated with this threat using the AMP engine.
Additional protections with context to your specific environment and threat data are available from the Cisco Secure Firewall Management Center.
If you are experiencing an emergency or in need of an incident response retainer, Cisco Talos Incident Response is available for proactive and emergency response.
Indicators of Compromise (IOCs)
Hashes (SHA256)
d55f983c994caa160ec63a59f6b4250fe67fb3e8c43a388aec60a4a6978e9f1e
e2a24ab94f865caeacdf2c3ad015f31f23008ac6db8312c2cbfb32e4a5466ea2
8dd620d9aeb35960bb766458c8890ede987c33d239cf730f93fe49d90ae759dd
