Any urgent malware campaigns or security vulnerabilities that Talos is actively researching. These posts include the latest threat detection our researchers develop to address these issues.
Ongoing exploitation of Cisco Catalyst SD-WAN vulnerabilities
Cisco Talos is tracking the active exploitation of CVE-2026-20182, an authentication bypass vulnerability in Cisco Catalyst SD-WAN Controller, formerly SD-WAN vSmart, and Cisco Catalyst SD-WAN Manager, formerly SD-WAN vManage.
UAT-4356's Targeting of Cisco Firepower Devices
Cisco Talos is aware of UAT-4356's continued active targeting of Cisco Firepower devices’ Firepower eXtensible Operating System (FXOS). UAT-4356 exploited n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) to gain unauthorized access to vulnerable devices.
Axios NPM supply chain incident
Overview of the recent Axios NPM supply chain incident including details of the payloads delivered from actor-controlled infrastructure.
Update, March 13: Talos on the developing situation in the Middle East
Cisco Talos updates this blog with additional IOCs, guidance, recommendations and timelines as of March 10, 2026.
Active exploitation of Cisco Catalyst SD-WAN by UAT-8616
Cisco Talos is tracking the active exploitation of CVE-2026-20127, a vulnerability in Cisco Catalyst SD-WAN Controller, formerly vSmart, that allows an unauthenticated remote attacker to bypass authentication and obtain administrative privileges.
New threat actor, UAT-9921, leverages VoidLink framework in campaigns
Cisco Talos recently discovered a new threat actor, UAT-9221, leveraging VoidLink in campaigns. Their activities may go as far back as 2019, even without VoidLink.
UAT-9686 actively targets Cisco Secure Email Gateway and Secure Email and Web Manager
Cisco Talos is tracking the active targeting of Cisco AsyncOS Software for Cisco Secure Email Gateway, formerly known as Cisco Email Security Appliance (ESA), and Cisco Secure Email and Web Manager, formerly known as Cisco Content Security Management Appliance (SMA).
Russian state-sponsored espionage group Static Tundra compromises unpatched end-of-life network devices
A Russian state-sponsored group, Static Tundra, is exploiting an old Cisco IOS vulnerability to compromise unpatched network devices worldwide, targeting key sectors for intelligence gathering.
ToolShell: Details of CVEs affecting SharePoint servers
Cisco Talos is aware of the ongoing exploitation of CVE-2025-53770 and CVE-2025-53771 in the wild. These are path traversal vulnerabilities affecting SharePoint Server Subscription Edition, SharePoint Server 2016, and SharePoint Server 2019.
MaaS operation using Emmenhtal and Amadey linked to threats against Ukrainian entities
Cisco Talos uncovered a stealthy Malware-as-a-Service (MaaS) operation that used fake GitHub accounts to distribute a variety of dangerous payloads and evade security defenses.
Newly identified wiper malware “PathWiper” targets critical infrastructure in Ukraine
Cisco Talos observed a destructive attack on a critical infrastructure entity within Ukraine, using a previously unknown wiper we are calling “PathWiper.”
UAT-6382 exploits Cityworks zero-day vulnerability to deliver malware
Talos has observed exploitation of CVE-2025-0994 in the wild by UAT-6382, a Chinese-speaking threat actor, who then deployed malware payloads via TetraLoader.
ArcaneDoor - New espionage-focused campaign found targeting perimeter network devices
Cisco is aware of new activity targeting certain Cisco Adaptive Security Appliances (ASA) 5500-X Series and has released three CVEs related to the event. We assess with high confidence this activity is related to same threat actor as ArcaneDoor in 2024.
Large-scale brute-force activity targeting VPNs, SSH services with commonly used login credentials
Cisco Talos would like to acknowledge Anna Bennett and Brandon White of Cisco Talos and Phillip Schafer, Mike Moran, and Becca Lynch of the Duo Security Research team for their research that led to the identification of these attacks. Cisco Talos is actively monitoring a global
Active exploitation of Cisco IOS XE Software Web Management User Interface vulnerabilities
Cisco has identified active exploitation of two previously unknown vulnerabilities in the Web User Interface (Web UI) feature of Cisco IOS XE software — CVE-2023-20198 and CVE-2023-20273 — when exposed to the internet or untrusted networks.
What to know about the HTTP/2 Rapid Reset DDoS attacks
CVE-2023-44487, a vulnerability in the HTTP/2 protocol, was recently used to launch intensive DDoS attacks against several targets.
What Cisco Talos knows about the Rhysida ransomware
The group appears to commonly deploy double extortion — of the victims that have been listed on the leak site, several of them have had some portion of their exfiltrated data exposed.
Undocumented driver-based browser hijacker RedDriver targets Chinese speakers and internet cafes
Cisco Talos has identified multiple versions of an undocumented malicious driver named “RedDriver,” a driver-based browser hijacker that uses the Windows Filtering Platform (WFP) to intercept browser traffic.
Old certificate, new signature: Open-source tools forge signature timestamps on Windows drivers
Actors are leveraging multiple open-source tools that alter the signing date of kernel mode drivers to load malicious and unverified drivers signed with expired certificates.
Active exploitation of the MOVEit Transfer vulnerability — CVE-2023-34362 — by Clop ransomware group
The Clop ransomware group has claimed responsibility for exploiting the vulnerability to deploy a previously unseen web shell, LemurLoot.
Mercenary mayhem: A technical analysis of Intellexa's PREDATOR spyware
Commercial spyware use is on the rise, with actors leveraging these sophisticated tools to conduct surveillance operations against a growing number of targets. Cisco Talos has new details of a commercial spyware product sold by the spyware firm Intellexa (formerly known as Cytrox).
New phishing-as-a-service tool “Greatness” already seen in the wild
Greatness incorporates features seen in some of the most advanced PaaS offerings, such as multi-factor authentication (MFA) bypass, IP filtering and integration with Telegram bots.
Video: Everything you need to know about ongoing state-sponsored attacks targeting network infrastructure across the globe
Video explanation of the Jaguar Tooth vulnerabilities with Matt Olney, J.J. Cummings and Hazel Burton.
State-sponsored campaigns target global network infrastructure
This campaign, dubbed "Jaguar Tooth," is an example of a much broader trend of sophisticated adversaries targeting networking infrastructure to advance espionage objectives or pre-position for future destructive activity.
Threat Advisory: 3CX Softphone Supply Chain Compromise
This is just the latest supply chain attack threatening users, after the SolarWinds incident in 2020 and the REvil ransomware group exploiting Kaseya VSA in 2021.
Emotet resumes spam operations, switches to OneNote
Since returning, Emotet has leveraged several distinct infection chains, indicating that they are modifying their approach based on their perceived success in infecting new systems.
Threat Advisory: Microsoft Outlook privilege escalation vulnerability being exploited in the wild
Cisco Talos is urging all users to update Microsoft Outlook after the discovery of a critical vulnerability, CVE-2023-23397, in the email client that attackers are actively exploiting in the wild.
HTML smugglers turn to SVG images
* HTML smuggling is a technique attackers use to hide an encoded malicious script within an HTML email attachment or webpage. * Once a victim receives the email and opens the attachment, their browser decodes and runs the script, which then assembles a malicious payload directl
Breaking the silence - Recent Truebot activity
Since August 2022, we have seen an increase in infections of Truebot (aka Silence.Downloader) malware. Truebot was first identified in 2017 and researchers have linked it to a threat actor called Silence Group that is responsible for several high-impact attacks on financial insti
Get a Loda This: LodaRAT meets new friends
* LodaRAT samples were deployed alongside other malware families, including RedLine and Neshta. * Cisco Talos identified several variants and altered versions of LodaRAT with updated functionality have been seen in the wild. * Changes in these LodaRAT variants include new f
Threat Advisory: High Severity OpenSSL Vulnerabilities
In late October two new buffer overflow vulnerabilities, CVE-2022-3602 and CVE-2022-3786, were announced in OpenSSL versions 3.0.0 to 3.0.6. These vulnerabilities can be exploited by sending an X.509 certificate with a specially crafted email address, potentially causing a buffer
Threat Advisory: Microsoft warns of actively exploited vulnerabilities in Exchange Server
Even organizations that use Exchange Online may still be affected if they run a hybrid server.
Avos ransomware group expands with new attack arsenal
By Flavio Costa, * In a recent customer engagement, we observed a month-long AvosLocker campaign. * The attackers utilized several different tools, including Cobalt Strike, Sliver and multiple commercial network scanners. * The initial ingress point in this incident was a pa
Threat Advisory: Atlassian Confluence zero-day vulnerability under active exploitation
Cisco Talos is monitoring reports of an actively exploited zero-day vulnerability in Confluence Data Center and Server. Confluence is a Java-based corporate Wiki employed by numerous enterprises. At this time, it is confirmed that all supported versions of Confluence are affecte
Threat Advisory: Zero-day vulnerability in Microsoft diagnostic tool MSDT could lead to code execution
A recently discovered zero-day vulnerability in the Microsoft Windows Support Diagnostic Tool (MSDT) made headlines over the past few days. CVE-2022-30190, also known under the name "Follina," exists when MSDT is called using the URL protocol from an application, such
Threat Advisory: Critical F5 BIG-IP Vulnerability
Summary A recently disclosed vulnerability in F5 Networks' BIG-IP could allow an unauthenticated attacker to access the BIG-IP system to execute arbitrary system commands, create and delete files, disable services and could lead to additional malicious activity. This vulner
Mustang Panda deploys a new wave of malware targeting Europe
* In February 2022, corresponding roughly with the start of the Russian Invasion of Ukraine, Cisco Talos began observing the China-based threat actor Mustang Panda conducting phishing campaigns against European entities, including Russian organizations. Some phishing messages co
TeamTNT Targeting AWS, Alibaba
By Darin Smith. * TeamTNT is actively modifying its scripts after they were made public by security researchers. * These scripts primarily target Amazon Web Services, but can also run in on-premise, container, or other forms of Linux instances. * The group's payloads inc
Threat Advisory: Spring4Shell
UPDATE, APRIL 4, 2022: The Kenna Risk Score for CVE-2022-22965 is currently at maximum 100. This is an exceptionally rare score, of which only 415 out of 184,000 CVEs (or 0.22 percent) have achieved, reflecting the severity and potential effects of this vulnerability. To get a r
Threat Advisory: DoubleZero
This post is also available in: Українська (Ukrainian) Overview The Computer Emergency Response Team of Ukraine released an advisory on March 22, 2022 disclosing another wiper dubbed "DoubleZero" targeting Ukrainian enterprises during Russia's invasion of the co
Threat Advisory: Opportunistic cyber criminals take advantage of Ukraine invasion
By Edmund Brumaghin, with contributions from Jonathan Byrne, Perceo Lemos and Vasileios Koutsoumpogeras. This post is also available in: 日本語 (Japanese) Українська (Ukrainian) Executive Summary * Since the beginning of the war in Ukraine, we have observed threat actors usin
Current executive guidance for ongoing cyberattacks in Ukraine
This post is also available in: 日本語 (Japanese) Українська (Ukrainian) Cyber threat activity against Ukraine, and around the world, has long been a central focus of our work. We continue to monitor the Ukraine-Russia situation by enacting a comprehensive, Talos-wide effort to p
Crowd-sourced attacks present new risk of crisis escalation
This post is also available in: 日本語 (Japanese) * An unpredictable and largely unknown set of actors present a threat to organizations, despite their sometimes unsophisticated techniques. Customers who are typically focused on top-tier, state-sponsored attacks should remain awa
Talos on the developing situation in Ukraine
This post is also available in: 日本語 (Japanese) Українська (Ukrainian) In the last month, Talos has seen a shift in activity in response to the unjust invasion of Ukraine. This post is meant to serve as our executive overview of the situation and provide you with the most up-to
Threat Advisory: Cyclops Blink
Update Mar. 17, 2022 Today, Asus released a product security advisory listing their products affected by Cyclops Blink. While the investigation is currently ongoing, this advisory provides guidance on taking necessary precautions via a checklist for the affected product versions
Threat Advisory: HermeticWiper
This post is also available in: 日本語 (Japanese) Українська (Ukrainian) Update: March 1, 2022 Cisco Talos is aware of reporting related to additional components discovered to be associated with ongoing HermeticWiper attacks. These additional components include: * HermeticWiz
Threat Advisory: Critical Apache Log4j vulnerability being exploited in the wild
Update History DateDescription of UpdatesDec. 20, 2021 Additional coverage and IOCs; additional detection capabilities for customers via Cisco Global Threat Alerts. Dec. 18, 2021 Additional mitigation guidance; updated coverage information. Dec. 17, 2021 Added additional vulner
Attackers exploiting zero-day vulnerability in Windows Installer — Here’s what you need to know and Talos’ coverage
Cisco Talos is releasing new SNORTⓇ rules to protect against the exploitation of a zero-day elevation of privilege vulnerability in Microsoft Windows Installer. This vulnerability allows an attacker with a limited user account to elevate their privileges to become an administrato
Back from the dead: Emotet re-emerges, begins rebuilding to wrap up 2021
Executive Summary Emotet has been one of the most widely distributed threats over the past several years. It has typically been observed being distributed via malicious spam email campaigns, and often leads to additional malware infections as it provides threat actors with an in
Threat Advisory: Apache HTTP Server zero-day vulnerability opens door for attackers
A recently discovered vulnerability in Apache HTTP Server (CVE-2021-41733) is being actively exploited in the wild. This vulnerability is a path traversal and file disclosure vulnerability that could allow an attacker to map URLs outside of the document root. It could also resu
PrintNightmare: Here’s what you need to know and Talos’ coverage
Over the past several weeks, there's been a lot of discussion about a particular privilege escalation vulnerability in Windows affecting the print spooler, dubbed PrintNightmare. The vulnerability (CVE-2021-1675/CVE-2021-34527) has now been patched multiple times but is belie
Threat Advisory: Pulse Secure Connect Coverage
Pulse Secure announced that a critical vulnerability (CVE-2021-22893) was discovered in their VPN service "Pulse Secure Connect" in a recent security advisory. The advisory states that, "a vulnerability was discovered under Pulse Connect Secure (PCS). This include
Threat Advisory: NSA SVR Advisory Coverage
The U.S. National Security Agency released an advisory outlining several vulnerabilities that the Russian Foreign Intelligence Services (SVR) is exploiting in the wild. The U.S. formally attributed the recent SolarWinds supply chain attack to the SVR group in this advisory and de
Hafnium Update: Continued Microsoft Exchange Server Exploitation
Update 3/11: The following OSQuery detects active commands being run through webshells observed used by actors on compromised Exchange servers. While systems may have been patched to defend against Hafnium and others, threat actors may have leveraged these vulnerabilities to esta
Threat Advisory: HAFNIUM and Microsoft Exchange zero-day
Microsoft released patches for four vulnerabilities in Exchange Server on March 2, disclosing that these vulnerabilities were being exploited by a previously unknown threat actor, referred to as HAFNIUM. The vulnerabilities in question — CVE-2021-26855, CVE-2021-26857, CVE-2021-
Nation-state campaign targets Talos researchers
Google's Threat Analysis Group published a blog Monday evening warning of an ongoing campaign attempting to compromise security researchers. Google TAG's blog outlines the attacker's motivations and various TTPs used in these attacks. We can confirm that multiple Ci
Threat Advisory: SolarWinds supply chain attack
Update 12/21: IOC section updated to include new information and associated stage. Update 12/18: We have been able to verify the name server for the DGA domain was updated as far back as late February. Compromised binaries appear to have been available on the SolarWinds website
FireEye Breach Detection Guidance
Update 12/14: Cisco Talos has implemented additional blocks in relation to the supply chain attack on SolarWinds® Orion® Platform. The U.S. Cybersecurity and Infrastructure Security Agency has issued Emergency Directive 21-01 due to this campaign. Talos is continuing to investiga
Cisco Talos Advisory on Adversaries Targeting the Healthcare and Public Health Sector
Background Cisco Talos has become aware that an adversary is leveraging Trickbot banking trojan and Ryuk ransomware to target U.S. hospitals and healthcare providers at an increasing rate. Security journalists reported on October 28, 2020 that the adversary was preparing to encr
Sea Turtle keeps on swimming, finds new victims, DNS hijacking techniques
By Danny Adamitis with contributions from Paul Rascagneres. Executive summary After several months of activity, the actors behind the "Sea Turtle" DNS hijacking campaign are not slowing down. Cisco Talos recently discovered new details that suggest they regrouped af
Recent MuddyWater-associated BlackWater campaign shows signs of new anti-detection techniques
By Danny Adamitis, David Maynor, and Kendall McKay. Cisco Talos assesses with moderate confidence that a campaign we recently discovered called "BlackWater" is associated with suspected persistent threat actor MuddyWater. Newly associated samples from April 2019 indica
Sodinokibi ransomware exploits WebLogic Server vulnerability
By Pierre Cadieux, Colin Grady, Jaeson Schultz and Matt Valites. Attackers are actively exploiting a recently disclosed vulnerability in Oracle WebLogic to install a new variant of ransomware called "Sodinokibi." Sodinokibi attempts to encrypt data in a user's dire
DNS Hijacking Abuses Trust In Core Internet Service
By Danny Adamitis, David Maynor, Warren Mercer, Matthew Olney and Paul Rascagneres. Update 4/18: A correction has been made to our research based on feedback from Packet Clearing House, we thank them for their assistance Preface This blog post discusses the technical details
Bitcoin Bomb Scare Associated with Sextortion Scammers
The claims in the emails we've seen from this actor are completely false, yet they have caused untold amounts of damage as organizations have evacuated buildings and called upon law enforcement to investigate.
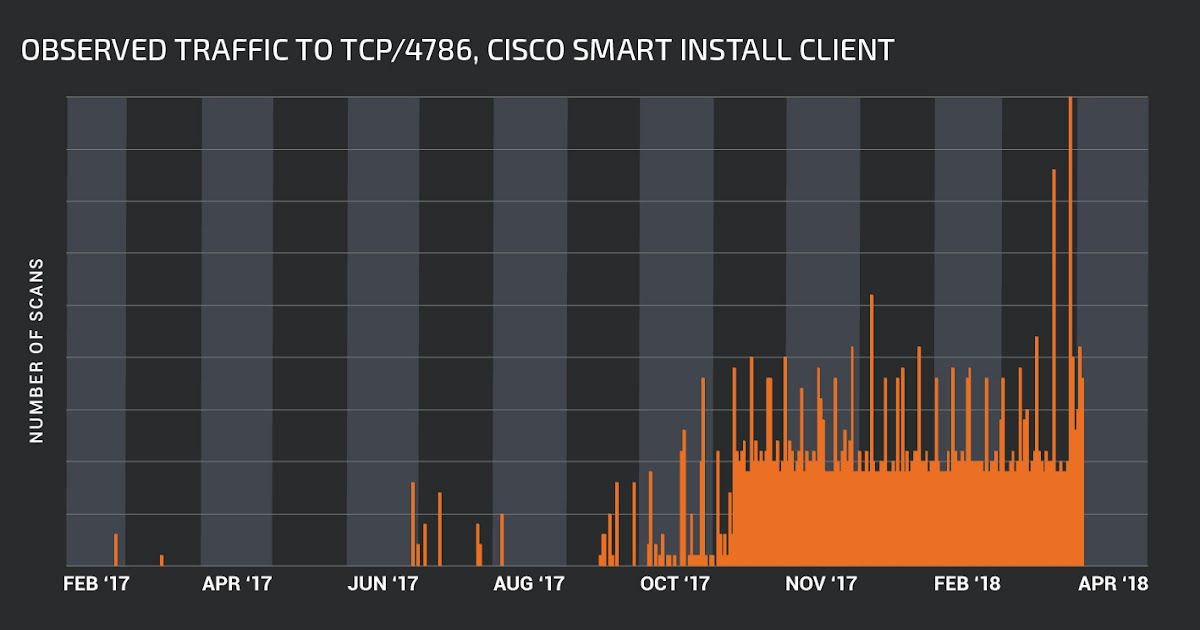
Critical Infrastructure at Risk: Advanced Actors Target Smart Install Client
Update: 4/9 Cisco PSIRT has released additional guidance available here. Cisco has recently become aware of specific advanced actors targeting Cisco switches by leveraging a protocol misuse issue in the Cisco Smart Install Client. Several incidents in multiple countries, includi
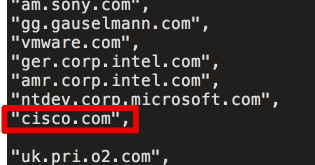
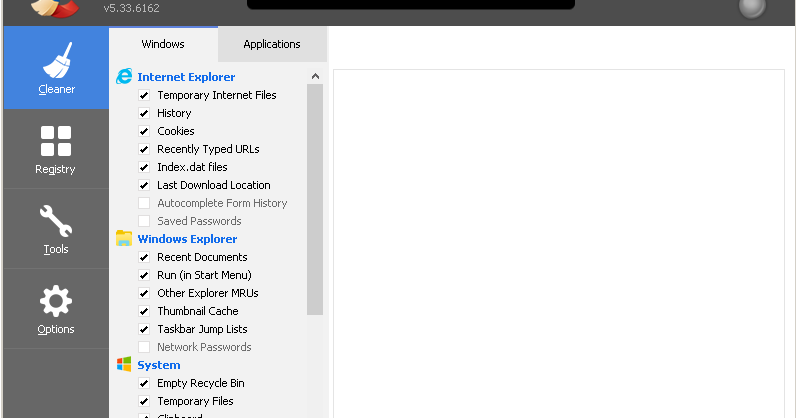
CCleaner Command and Control Causes Concern
Introduction Talos recently published a technical analysis of a backdoor which was included with version 5.33 of the CCleaner application. During our investigation we were provided an archive containing files that were stored on the C2 server. Initially, we had concerns about th
CCleanup: A Vast Number of Machines at Risk
Update 9/18: CCleaner Cloud version 1.07.3191 is also reported to be affected Update 9/19: This issue was discovered and reported by both Morphisec and Cisco in separate in-field cases and reported separately to Avast. Update 9/19: There has been some confusion on how the DGA do
Attack on Critical Infrastructure Leverages Template Injection
Executive Summary Attackers are continually trying to find new ways to target users with malware sent via email. Talos has identified an email-based attack targeting the energy sector, including nuclear power, that puts a new spin on the classic word document attachment phish. T
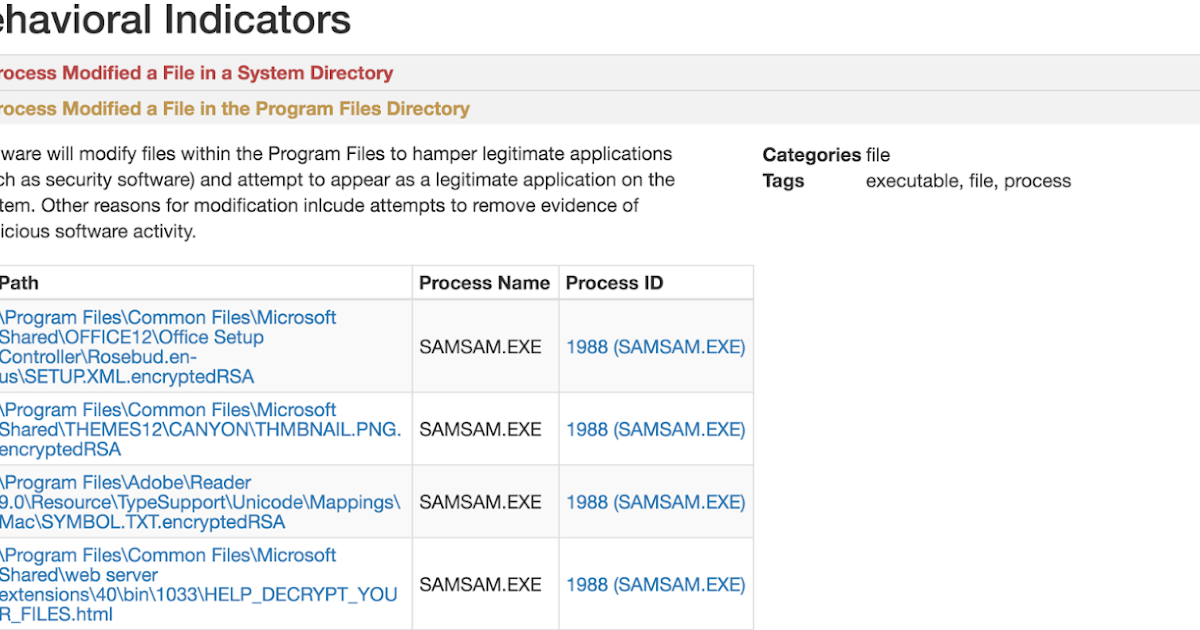
SamSam: The Doctor Will See You, After He Pays The Ransom
Cisco Talos is currently observing a widespread campaign leveraging the Samas/Samsam/MSIL.B/C ransomware variant. Unlike most ransomware, SamSam is not launched via user focused attack vectors, such as phishing campaigns and exploit kits. This particular family seems to be distri