This post is also available in:
- An unpredictable and largely unknown set of actors present a threat to organizations, despite their sometimes unsophisticated techniques. Customers who are typically focused on top-tier, state-sponsored attacks should remain aware of these highly motivated threat actors, as well.
- Misattribution of these actors carries the risk of nations escalating an already dangerous conflict in Ukraine.
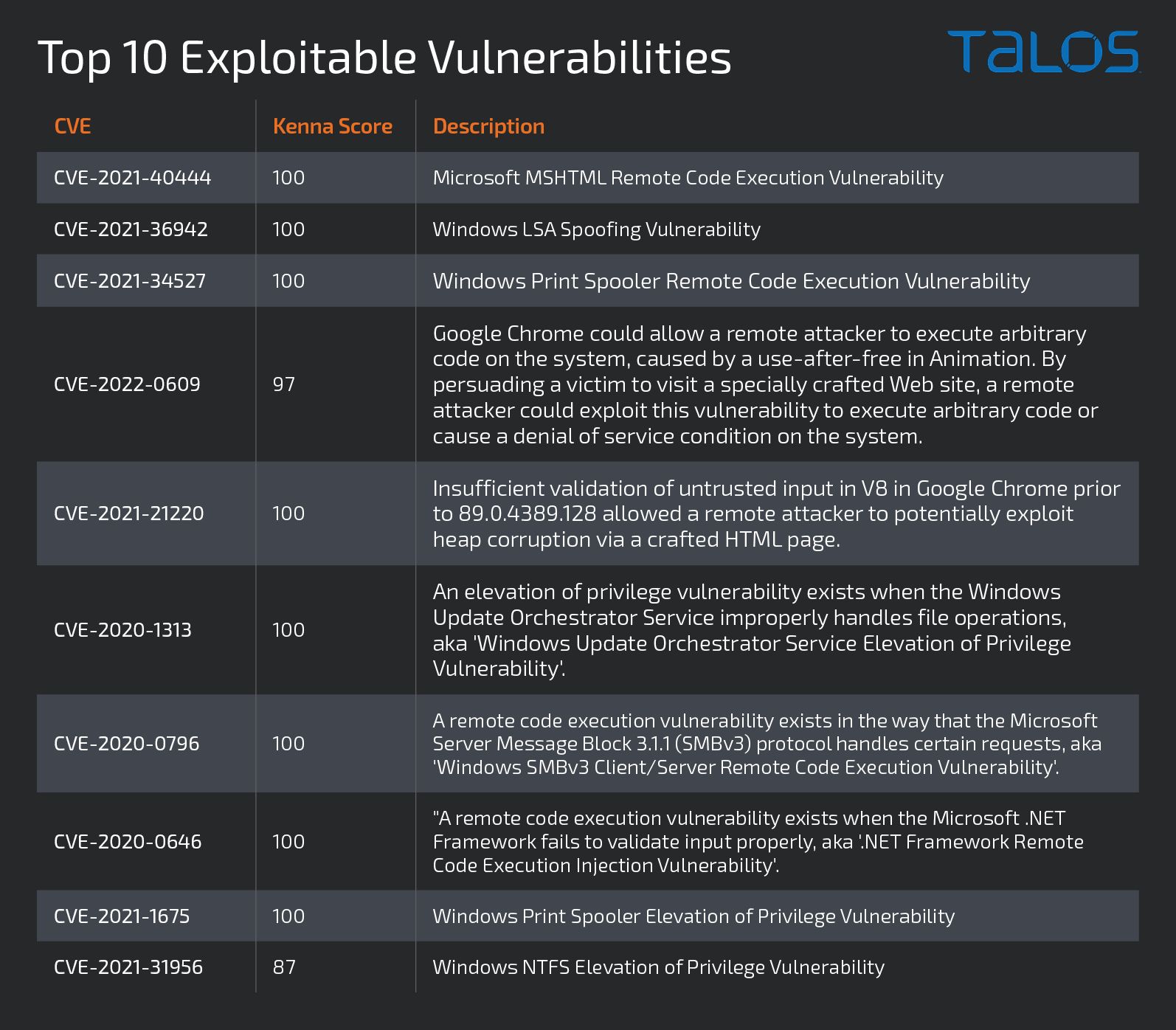
- Based on data from our fellow researchers at Cisco Kenna, customers should be most concerned about threat actors exploiting several recently disclosed vulnerabilities, highlighting the importance of consistently updating software and related systems.
- With this rising and diverse threat, we recommend defenders continue to employ security fundamentals, patch aggressively, and leverage finished intelligence reports or other sources to enhance their understanding of the threat landscape.
Each of us, in the face of an unjustified outrage, will look to try and help – but some of these efforts carry the risk of escalating an already dangerous situation. For those of us at Talos, helping has meant standing beside our partners and customers in Ukraine, long nights and weekends looking at telemetry and consoles, and hours of examining the individual instructions of malware deployed in Ukraine. As we monitored the intelligence in the region, we started to see groups assemble who intended to attack critical infrastructure – either in Ukraine or in Russia.
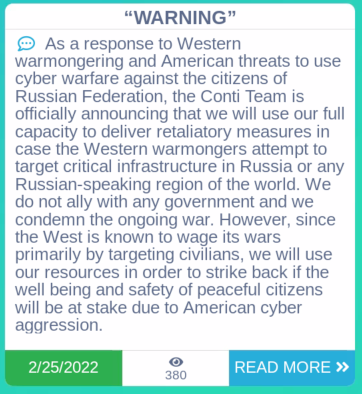
Conti announcement of support for the Russian Federation.