- Cisco Talos recently discovered a new ransomware actor called RA Group that has been operating since at least April 22, 2023.
- The actor is swiftly expanding its operations. To date, the group has compromised three organizations in the U.S. and one in South Korea across several business verticals, including manufacturing, wealth management, insurance providers and pharmaceuticals.
- Talos assesses with high confidence that RA Group is leveraging leaked Babuk ransomware source code.
Who is the RA Group?
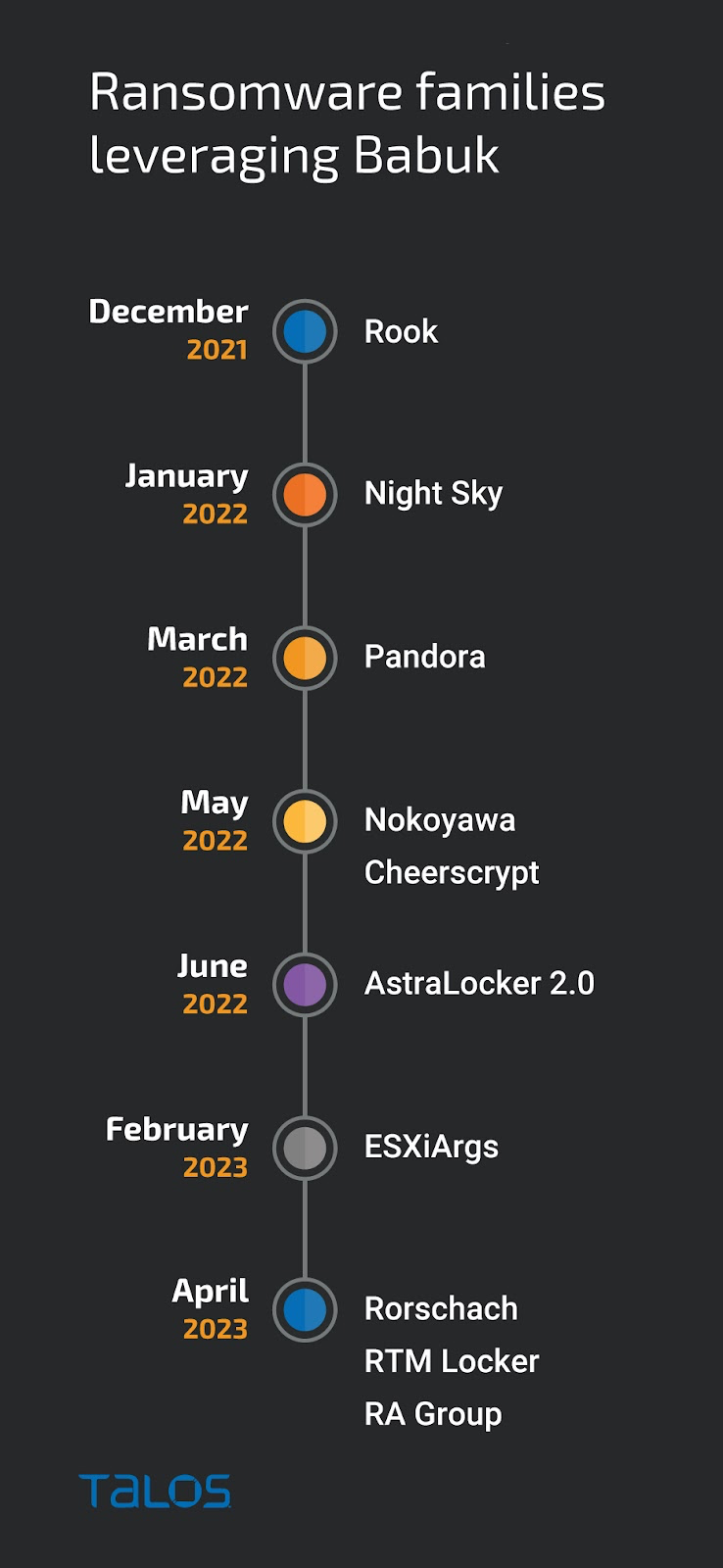
Talos recently discovered a new ransomware actor, RA Group, who emerged in April 2023 and seems to be using leaked Babuk source code in its attacks. After an alleged member of the Babuk group leaked the full source code of its ransomware in September 2021, various ransomware families have emerged leveraging the leaked Babuk code. Talos has compiled a timeline of these attacks conducted by different actors using ransomware families that branched off the leaked source code.
The group is launching double extortion attacks. Like other ransomware actors, RA Group also operates a data leak site in which they threaten to publish the data exfiltrated from victims who fail to contact them within a specified time or do not meet their ransom demands. This form of double extortion increases the chances that a victim will pay the requested ransom.
RA Group leak site contents April 22 - 28, 2023.
This actor is expanding its operations at a fast pace. RA Group launched their data leak site on April 22, 2023, and on April 27, we observed the first batch of victims, three in total, followed by another one on April 28. We also observed the actor making cosmetic changes to their leak site after disclosing the victim’s details, confirming they are in the early stages of their operation.
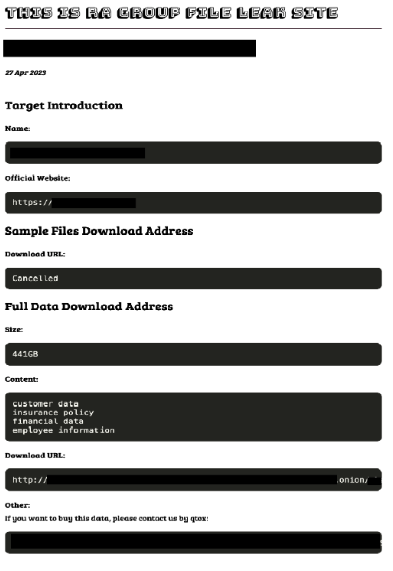
In their leak site, RA Group discloses the name of the victim's organization, a list of their exfiltrated data and the total size, and the victim’s official URL, which is typical among other ransomware groups’ leak sites. The RA Group is also selling the victim’s exfiltrated data on their leak site by hosting the victims’ leaked data on a secured Tor site.
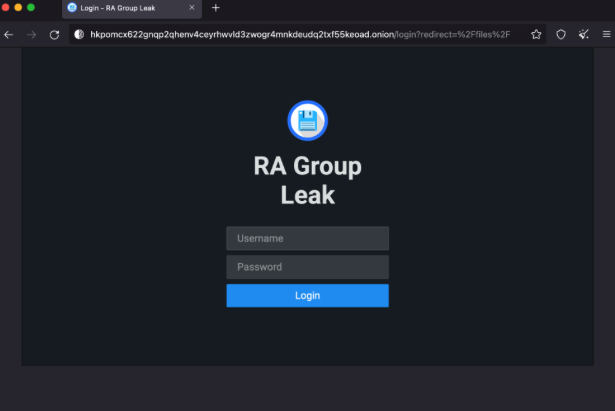
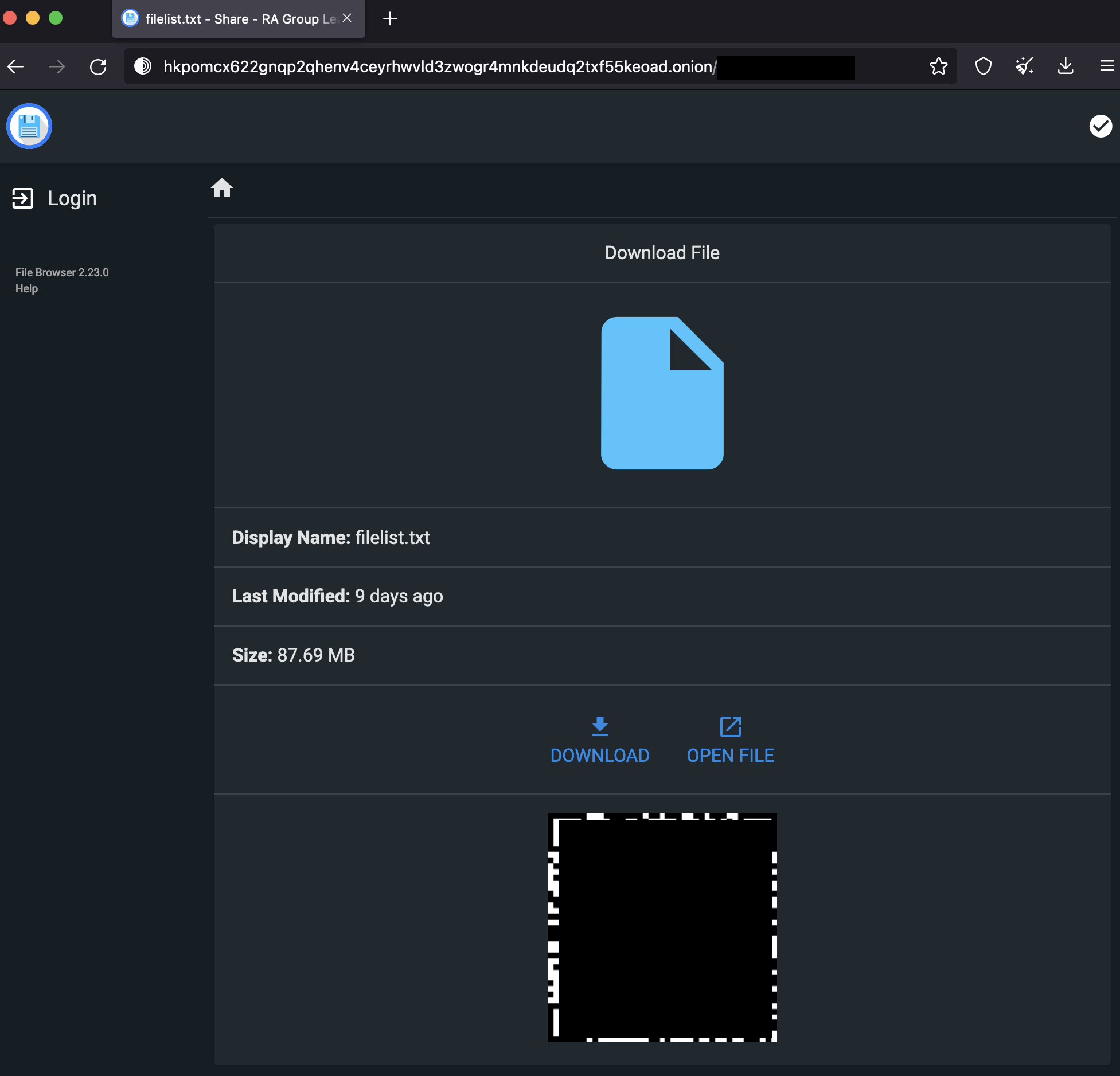
RA Group also provides URLs to download the full file listings of the victim’s data on their leak site.
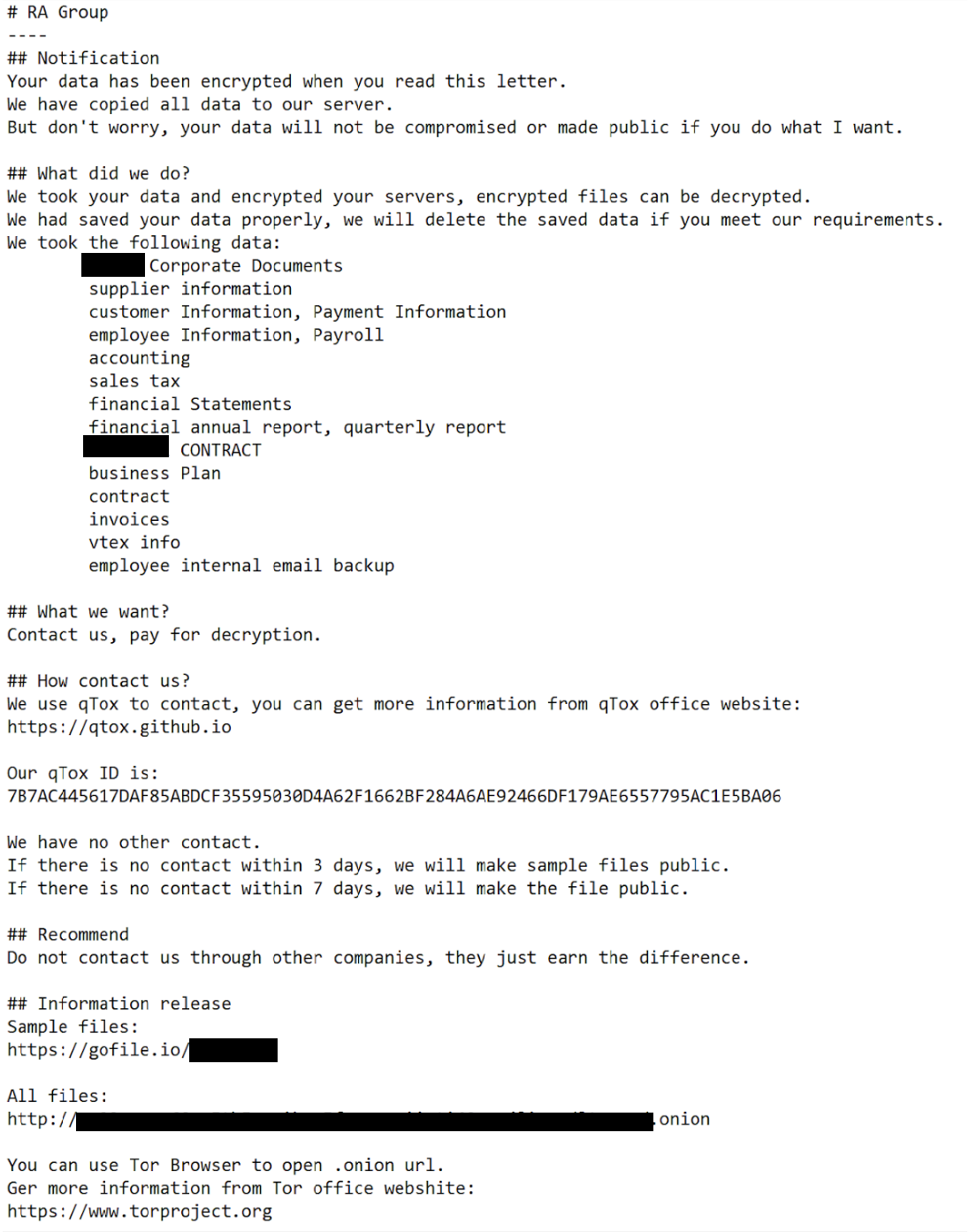
RA Group uses customized ransom notes, including the victim’s name and a unique link to download the exfiltration proofs. After activating the ransomware executable on the victim’s machine, the actor drops the ransom note file called “How To Restore Your Files.txt.”
Based on the ransom notes we analyzed, if the victim fails to contact the actors within three days, the group leaks the victim’s files. The victims can confirm the exfiltration of their information by downloading a file using the gofile[.]io link in the ransom note.
RA Group ransomware code appears highly customized
RA Group deploys their ransomware with a built-in ransom note specifically written to each victim with their name on it, a common practice among ransomware groups. However, it is unusual that RA Group names the victim in the executable, as well.
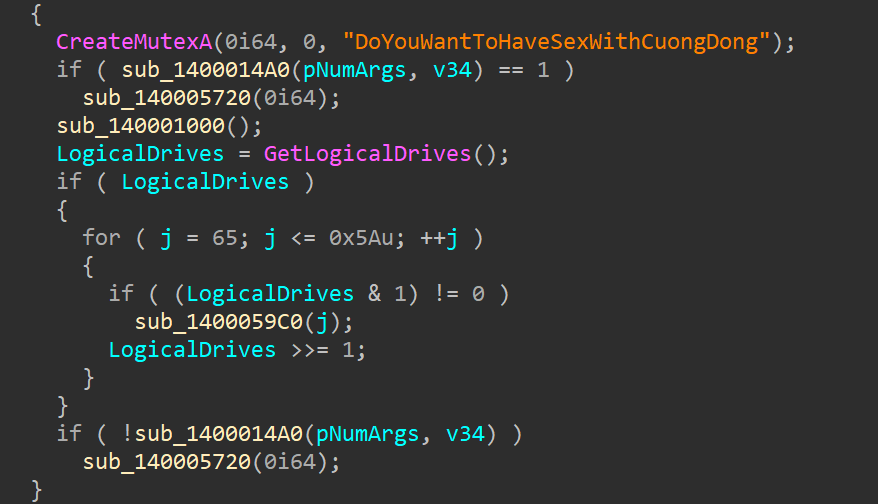
Our analysis shows that RA Group’s ransomware sample is written in C++ and was compiled on April 23, 2023. The binary has the debug path “C:\Users\attack\Desktop\Ransomware.Multi.Babuk.c\windows\x64\Release\e.pdb”. It contains the same mutex name as the Babuk ransomware, supporting our high-confidence assessment that RA Group built their ransomware using Babuk’s leaked source code.
RA Group’s ransomware executable uses the cryptography scheme with curve25519 and eSTREAM cipher hc-128 algorithm for encryption. This process encrypts only a certain part of the source file’s contents, not the entire file. It uses WinAPI CryptGenRandom to generate cryptographically random bytes used as a private key for each victim. After encrypting the files, the ransomware appends the file extension “.GAGUP” to the encrypted files on the victim’s machine.
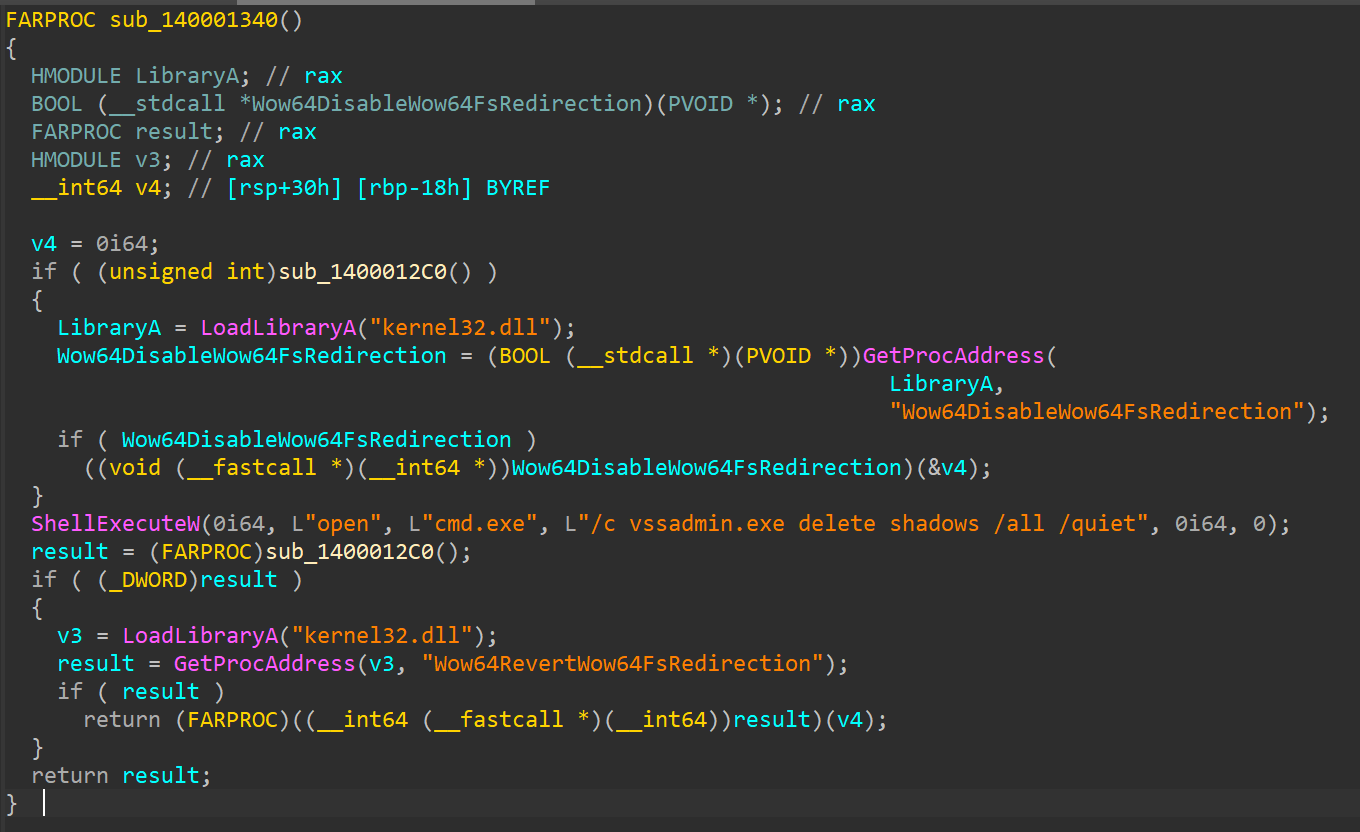
The ransomware deletes the contents of the victim machine’s Recycle Bin with the API SHEmptyRecyclebinA. It deletes the volume shadow copy by executing the local Windows binary vssadmin.exe, an administrative tool used to manipulate shadow copies.
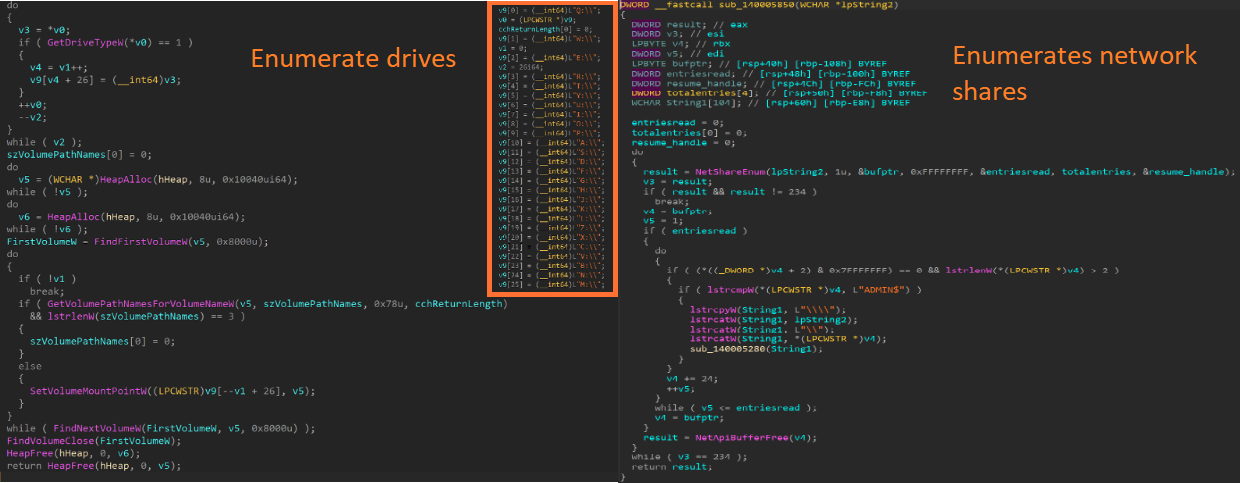
The ransomware enumerates every logical drive on the victim’s machine by comparing logical drive letters with the list of drive letter strings in the binary and mounts the identified drives to perform the encryption process. RA Group’s malware enumerates the network shares and available network resources on the victim’s machine using the APIs NetShareEnum, WNetOpenEnumW and WNetEnumResourceW to encrypt files on the remotely mapped drives of other machines or servers.
The ransomware does not encrypt all files and folders. The image below shows the hardcoded list of folders the malware won’t encrypt so the victim can contact the RA Group operators.
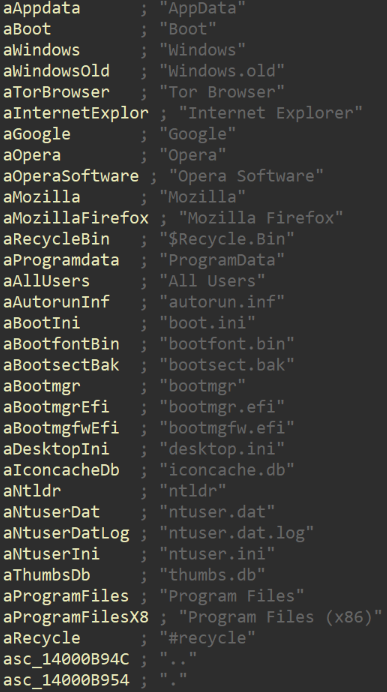
These files and folders are necessary for the system to work properly and to allow the victims to download the qTox application and contact RA group operators using the qTox ID provided on the ransom note.
Coverage

Cisco Secure Endpoint (formerly AMP for Endpoints) is ideally suited to prevent the execution of the malware detailed in this post. Try Secure Endpoint for free here.
Cisco Secure Web Appliance web scanning prevents access to malicious websites and detects malware used in these attacks.
Cisco Secure Email (formerly Cisco Email Security) can block malicious emails sent by threat actors as part of their campaign. You can try Secure Email for free here.
Cisco Secure Firewall (formerly Next-Generation Firewall and Firepower NGFW) appliances such as Threat Defense Virtual, Adaptive Security Appliance and Meraki MX can detect malicious activity associated with this threat.
Cisco Secure Malware Analytics (Threat Grid) identifies malicious binaries and builds protection into all Cisco Secure products.
Umbrella, Cisco's secure internet gateway (SIG), blocks users from connecting to malicious domains, IPs, and URLs, whether users are on or off the corporate network. Sign up for a free trial of Umbrella here.
Cisco Secure Web Appliance (formerly Web Security Appliance) automatically blocks potentially dangerous sites and tests suspicious sites before users access them.
Additional protections with context to your specific environment and threat data are available from the Firewall Management Center.
Cisco Duo provides multi-factor authentication for users to ensure only those authorized are accessing your network.
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org. Snort SIDs for this threat are 61761-61764 for Snort 2 and 300543-30054 for Snort 3.
ClamAV detections are available for this threat:
Win.Ransomware.Babuk-9819006-0
Indicators of Compromise
Indicators of Compromise associated with this threat can be found here.
