My wife (no stranger to weird types of scams) recently received a fake text message from someone claiming to be New Jersey’s E-ZPass program saying that she had an outstanding balance from highway tolls that she owed, prompting her to visit a site so she could pay and avoid additional fines.
There was plenty of reason to believe this was a legitimate ask. Her family is from New Jersey, so we make frequent trips there, paying $20-plus in tolls along the way. We had also just completed a trip from there a few weeks prior (though I’m not sure if this was a coincidence to the timing of the spam text or not), and we both have E-ZPass accounts.
For the uninitiated, or anyone who lives in a country where taxes are paid as normal and therefore pay for appropriate road repairs, E-ZPass is a small device drivers in more than a dozen countries in the U.S. can register for so they can automatically pay tolls along highways rather than having to stop and use cash or coins, or spending a few extra minutes manually processing a transaction.
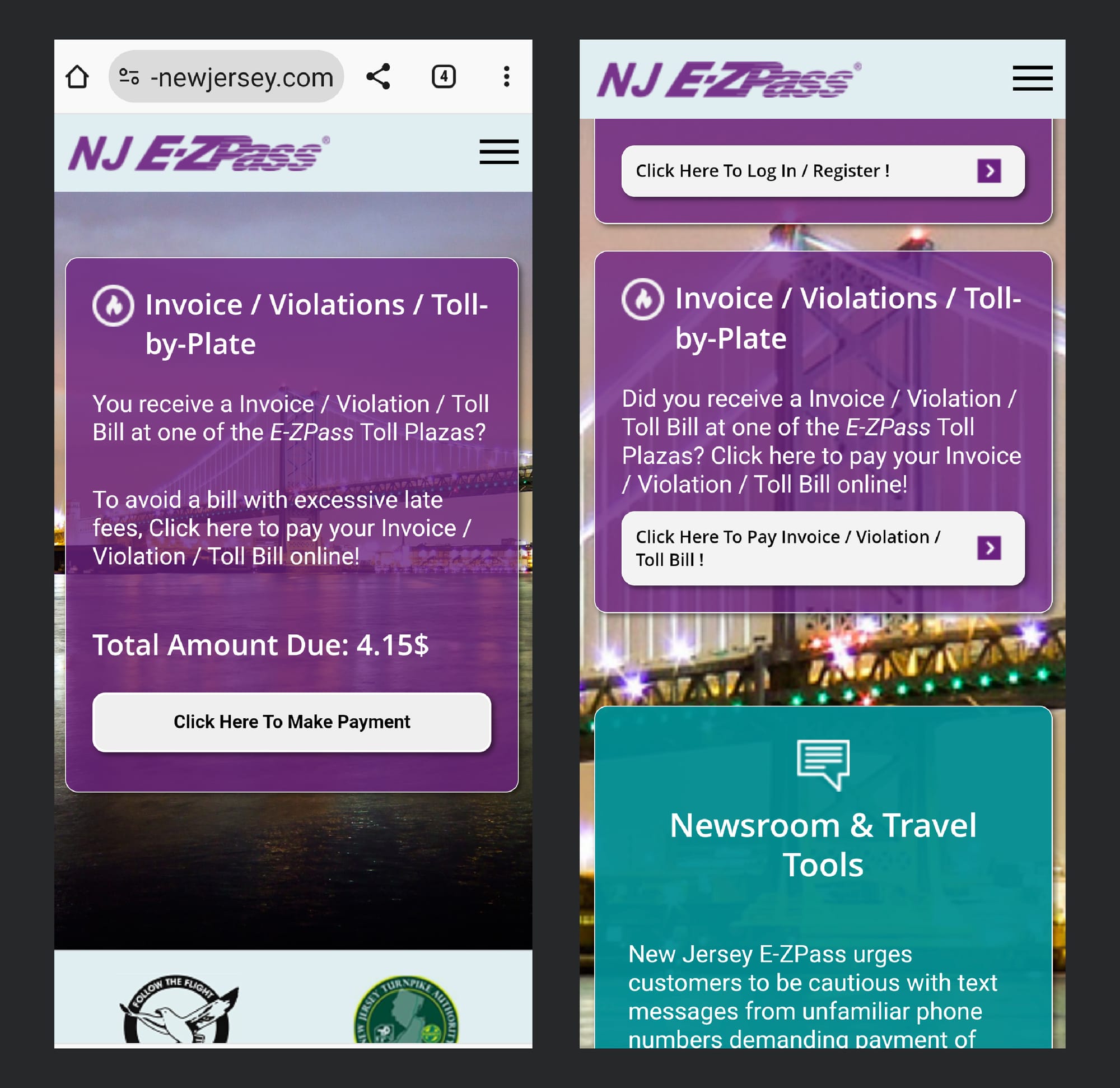
Each state or city has its own agencies that deal with E-ZPass, each with its own payment processing system and website. For this case with New Jersey, the phishing site the scammers set up was shockingly convincing and looked remarkably similar to the legitimate New Jersey E-ZPass website.
Once we logged into our legitimate E-ZPass account to check to make sure we had, in fact, paid all the appropriate tolls, I alerted my team about this scam, and we appropriately blocked the phishing URL in question in Cisco Secure products.
Since this victory and foray into threat hunting, I have learned that this is a problem everywhere, not just for New Jersey drivers.
Since this experience, E-ZPass has sent out an alert in all the states they operate in warning about these types of scams. Drivers from New York to Georgia and Pennsylvania have received these types of texts with equally convincing phishing text messages and lure pages.
It’s unclear what the adversaries’ goals are in this case, but it’s probably safe to assume they’re looking to collect users’ credit card information after they go in to pay the alleged overdue toll. They could also be collecting E-ZPass login information to collect further data about the drivers.
In April, the FBI also warned of SMS phishing scams, in which adversaries pretended to be toll collection services from three different U.S. states. SunPass, the equivalent to E-ZPass in Florida, also alerted about similar scams around the same time as these E-ZPass scams started being reported. And in March, the FasTrak service in California warned of the same problems.
My hunch is that these types of services are being impersonated all over the U.S. for several reasons — thousands of drivers use these services (especially in states with a high commuter population), which makes it likely that whoever receives the text will be familiar with these devices and will have recently driven on a highway that makes drivers pay tolls. The amounts they’re asking for are also small, no more than $5 USD, so it doesn’t set off any immediate alarm bells, unlike similar scams that ask for hundreds of dollars for health care services. The requests coming through as SMS messages also make the targets more likely to open them on their mobile devices, which may not have the same security in place as a laptop or managed company device.
No individual state or local agency is immune from this style of scam, so if you’re ever in doubt of receiving a text like this, it’s best to call your area government program in question and ask them about any suspicious activity before clicking on any links or submitting payment information.
The one big thing
Cisco Talos’ Vulnerability Research team has helped to disclose and patch more than 20 vulnerabilities over the past three weeks, including two in the popular Adobe Acrobat Reader software. Acrobat, one of the most popular PDF readers currently available, contains two out-of-bounds read vulnerabilities that could lead to the exposure of sensitive contents of arbitrary memory in the application. There are also eight vulnerabilities in a popular line of PLC CPU modules commonly used in automated environments. We have more detailed information in our full Vulnerability Roundup from this week.
Why do I care?
Several vulnerabilities were identified in the AutomationDirect P3 line of CPU modules. The P3-550E is the most recent CPU module released in the Productivity3000 line of Programmable Automation Controllers from AutomationDirect. The device communicates remotely via ethernet, serial and USB and exposes a variety of control services, including MQTT, Modbus, ENIP and the engineering workstation protocol DirectNET. Four of the vulnerabilities found in these PLC CPU modules received a CVSS security score of 9.8 out of 10, making them particularly notable. TALOS-2024-1942 (CVE-2024-21785) is a leftover debug code vulnerability that allow an adversary who can communicate to the device over ModbusRTU to enable the device’s diagnostic interface without any other knowledge of the target device. There is also TALOS-2024-1943 (CVE-2024-23601) which can lead to remote code execution if the attacker sends a specially crafted file to the targeted device and TALOS-2024-1939 (CVE-2024-24963 and CVE-2024-24962) which are stack-based buffer overflows that can also lead to remote code execution if the attacker sends a specially formatted packet to the device.
So now what?
Each of the vendors mentioned in this week’s Vulnerability Roundup have released patches for affected products, and users should download these patches as soon as possible. For Snort coverage that can detect the exploitation of these vulnerabilities, download the latest rule sets from Snort.org, and our latest Vulnerability Advisories are always posted on Talos Intelligence’s website.
Top security headlines of the week
Security researchers are warning about the dangers of a new AI “Recall” feature for Microsoft Windows 11. Microsoft recently announced a new update, that will allow a computer to remember past actions taken by the user and then use a simple search to query that information (ex., “Where did I store that document again?”). However, because Recall essentially takes individual snapshots of a machine and stores them locally, there are several security concerns. If an adversary were to infect a targeted machine with information-stealing malware, they could steal important databases stored locally and anything stored by Windows Recall. Recall also contains what are essentially keylogging functions, leaving the door open for adversaries to easily steal login credentials or other personal information that had been entered into the machine over the previous three months. The United Kingdom’s data protection agency has already contacted Microsoft inquiring about the way this information is stored and used, and they’ve asked for assurance that users’ data will be properly safeguarded and not used by the company. Other unauthorized users may be able to access and query Recall’s information, should they obtain physical access to the device. (Bleeping Computer, Double Pulsar)
Popular spyware app pcTattletale had to completely shut down after a data breach and having its website seized. The company that operates the app, which quietly and remotely tracks users’ activities on infected machines and takes screenshots, had its website defaced earlier this week by a hacker, along with a dump of data belonging to alleged pcTattletale customers and victims. Just days before the disruption, reports surfaced that the software was quietly installed on computers that handled the check-in process at least three Wyndham hotels across the U.S. A vulnerability in the platform could have allowed anyone on the internet who exploits it can download screenshots captured by the software directly from its servers. pcTattletale advertised itself as software that could allow anyone to control it remotely and view the target’s Android or Windows devices and their data from anywhere in the world. The founder of the spyware said that, after the data breach, the company was “out of business and completely done.” The now-defunct app had 138,000 registered customers, according to data breach notification website Have I Been Pwned. (TechCrunch, TechCrunch (again))
Ascension hospitals across the U.S. still have to delay patient care more than three weeks after a cyber attack. As of earlier this week, the national hospital system is still experiencing network disruptions, forcing staff to write care notes by hand and deliver orders for tests and prescriptions in person. Patients have also been unable to use their online portals to contact their doctors or view their medical records. Ascension is one of the largest health systems in the U.S., with more than 140 hospitals across the country. It first alerted patients and doctors about “unusual activity” on May 8, and there is no timeline for when services will be fully restored. News reports indicate that the disruption is a ransomware attack that can be attributed to the BlackBasta threat actor, which has links to Russia. Large health care organizations have increasingly become the target of ransomware attacks, with a previous campaign targeting Change Healthcare earlier this year disrupting payments to medical providers across the U.S. for weeks. (NPR, The New York Times)
Can’t get enough Talos?
- Attackers are probing Check Point Remote Access VPN devices
- Out-of-bounds reads in Adobe Acrobat; Foxit PDF Reader contains vulnerability that could lead to SYSTEM-level privileges
- New Generative AI category added to Talos reputation services
- From trust to trickery: Brand impersonation over the email attack vector
Upcoming events where you can find Talos
Cisco Live (June 2 - 6)
Las Vegas, Nevada
Bill Largent from Talos' Strategic Communications team will be giving our annual "State of Cybersecurity" talk at Cisco Live on Tuesday, June 4 at 11 a.m. Pacific time. Jaeson Schultz from Talos Outreach will have a talk of his own on Thursday, June 6 at 8:30 a.m. Pacific, and there will be several Talos IR-specific lightning talks at the Cisco Secure booth throughout the conference.
AREA41 (June 6 – 7)
Zurich, Switzerland
Gergana Karadzhova-Dangela from Cisco Talos Incident Response will highlight the primordial importance of actionable incident response documentation for the overall response readiness of an organization. During this talk, she will share commonly observed mistakes when writing IR documentation and ways to avoid them. She will draw on her experiences as a responder who works with customers during proactive activities and actual cybersecurity breaches.
Most prevalent malware files from Talos telemetry over the past week
SHA 256: 9be2103d3418d266de57143c2164b31c27dfa73c22e42137f3fe63a21f793202
MD5: e4acf0e303e9f1371f029e013f902262
Typical Filename: FileZilla_3.67.0_win64_sponsored2-setup.exe
Claimed Product: FileZilla
Detection Name: W32.Application.27hg.1201
SHA 256: 0e2263d4f239a5c39960ffa6b6b688faa7fc3075e130fe0d4599d5b95ef20647
MD5: bbcf7a68f4164a9f5f5cb2d9f30d9790
Typical Filename: bbcf7a68f4164a9f5f5cb2d9f30d9790.vir
Claimed Product: N/A
Detection Name: Win.Dropper.Scar::1201
SHA 256: a024a18e27707738adcd7b5a740c5a93534b4b8c9d3b947f6d85740af19d17d0
MD5: b4440eea7367c3fb04a89225df4022a6
Typical Filename: Pdfixers.exe
Claimed Product: Pdfixers
Detection Name: W32.Superfluss:PUPgenPUP.27gq.1201
SHA 256: c67b03c0a91eaefffd2f2c79b5c26a2648b8d3c19a22cadf35453455ff08ead0
MD5: 8c69830a50fb85d8a794fa46643493b2
Typical Filename: AAct.exe
Claimed Product: N/A
Detection Name: PUA.Win.Dropper.Generic::1201
SHA 256: e12b6641d7e7e4da97a0ff8e1a0d4840c882569d47b8fab8fb187ac2b475636c
MD5: a087b2e6ec57b08c0d0750c60f96a74c
Typical Filename: AAct.exe
Claimed Product: N/A
Detection Name: PUA.Win.Tool.Kmsauto::1201