Connecting the Dots Reveals Crimeware Shake-up
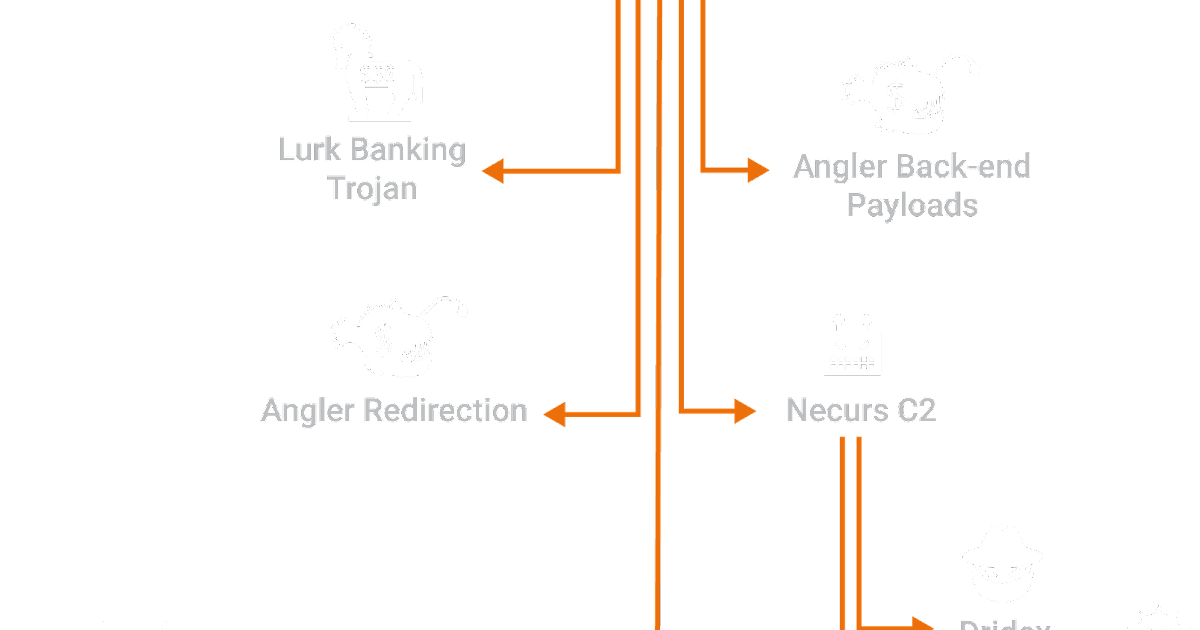
This Post Authored by Nick Biasini For a couple of weeks in June the threat landscape was changed. Several high profile threats fell off the scene, causing a shake-up that hadn't been seen before. For a period of three weeks the internet was safer, if only for a short time.
Angler Catches Victims Using Spam as Bait
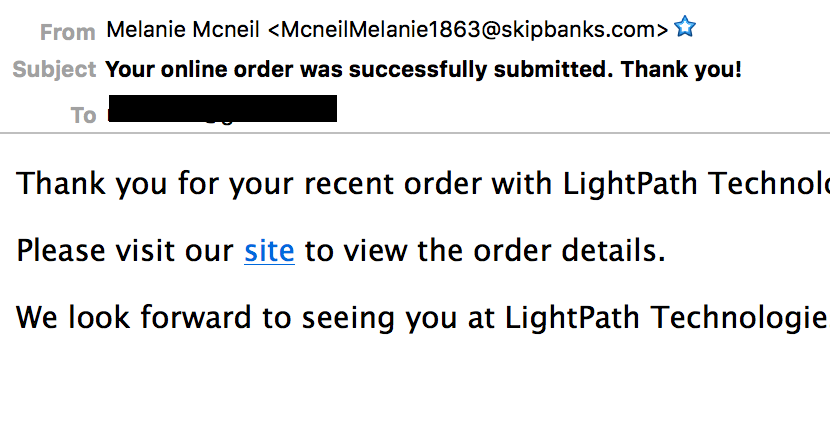
This post is authored by Nick Biasini with contributions from Erick Galinkin and Alex McDonnell Exploit kits have been a recurring threat that we've discussed here on this blog as a method of driving users to maliciousness. Users typically encounter exploit kit landing pages
Threat Spotlight: Spin to Win...Malware
This post was authored by Nick Biasini with contributions from Tom Schoellhammer and Emmanuel Tacheau. The threat landscape is ever changing and adversaries are always working to find more efficient ways to compromise users. One of the many ways that users are driven to maliciou
Threat Spotlight: Exploit Kit Goes International Hits 150+ Countries
Overview Talos is constantly monitoring the threat landscape and exploit kits are a constantly evolving component of it. An ongoing goal of Talos is to expose and disrupt these kits to protect the average internet user being targeted and compromised. We were able to gain unprece
Nuclear Drops Tor Runs and Hides
Introduction Exploit kits are constantly compromising users, whether it's via malvertising or compromised websites, they are interacting with a large amount of users on a daily basis. Talos is continuously monitoring these exploit kits to ensure protection, analyze changes as
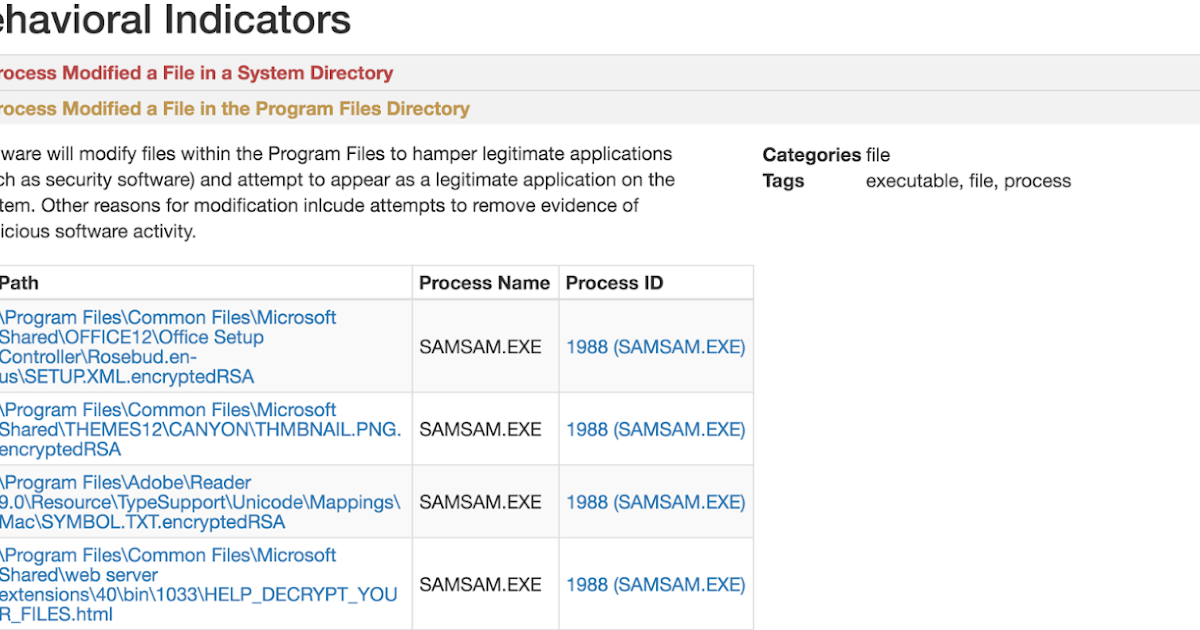
SamSam: The Doctor Will See You, After He Pays The Ransom
Cisco Talos is currently observing a widespread campaign leveraging the Samas/Samsam/MSIL.B/C ransomware variant. Unlike most ransomware, SamSam is not launched via user focused attack vectors, such as phishing campaigns and exploit kits. This particular family seems to be distri
Malware Word Search: Identifying Angler's Dictionary
This post authored by Steve Poulson with contributions from Nick Biasini. Exploit kits are constantly evolving and changing. We recently wrote about some subtle Angler changes but then Angler changed drastically on March 8. In this blog post, we will briefly cover these changes,
Angler Attempts to Slip the Hook
This post authored by Nick Biasini with contributions from Joel Esler, Erick Galinkin and Melissa Taylor Talos has discussed at length the sophistication of the Angler exploit kit. One thing that always makes Angler stand apart is the speed with which they develop and implement
Threat Spotlight: Upatre - Say No to Drones, Say Yes to Malware
Talos has observed an explosion of malicious downloaders in 2015 which we’ve documented on several occasions on our blog. These downloaders provide a method for attackers to push different types of malware to endpoint systems easily and effectively. Upatre is an example of a mali