What the continued escalation of tensions in the Middle East means for security
Cisco Talos works with many organizations around the world, monitoring and protecting against sophisticated threats every day. As such, we are watching the current state of events in the Middle East very closely for our customers and partners who may be impacted by the ongoing si
Incident Response lessons from recent Maze ransomware attacks
By JJ Cummings and Dave Liebenberg This year, we have been flooded with reports of targeted ransomware attacks. Whether it's a city, hospital, large- or medium-sized enterprise — they are all being targeted. These attacks can result in significant damage, cost, and have many
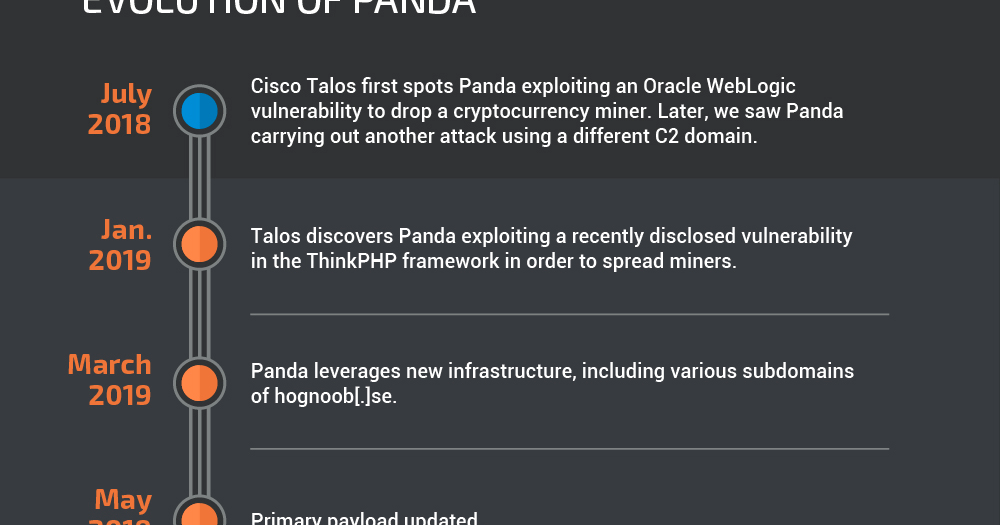
Cryptocurrency miners aren’t dead yet: Documenting the voracious but simple “Panda”
By Christopher Evans and David Liebenberg. Executive summary A new threat actor named "Panda" has generated thousands of dollars worth of the Monero cryptocurrency through the use of remote access tools (RATs) and illicit cryptocurrency-mining malware. This is far fr
Threat Roundup for July 26 to Aug. 2
Today, Talos is publishing a glimpse into the most prevalent threats we've observed between July 26 and Aug. 2. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting ke
Malvertising: Online advertising's darker side
Executive summary One of the trickiest challenges enterprises face is managing the balance between aggressively blocking malicious advertisements (aka malvertising) and allowing content to remain online, accessible for the average user. The days of installing a basic ad blocker
Let's Destroy Democracy
* /what-to-expect-when-youre-electing * /election-roundtable-video * /what-to-expect-electing-disinformation-building-blocks Executive summary Over the past few years, Cisco Talos has increasingly been involved in election security research and support, most recently support
Welcome Spelevo: New exploit kit full of old tricks
EXECUTIVE SUMMARY Exploit kits are an ever-present and often forgotten threat on the landscape today. Their popularity seemed to peak several years ago with the success and eventual downfall of some of the best compromise platforms ever created, including the Angler Exploit Kit.
Using Firepower to defend against encrypted RDP attacks like BlueKeep
This blog was authored by Brandon Stultz Microsoft recently released fixes for a critical pre-authentication remote code execution vulnerability in Remote Desktop Protocol Services (RDP). Identified as CVE-2019-0708 in May's Patch Tuesday, the vulnerability caught the attent