Threat Roundup for November 26 to December 3
Today, Talos is publishing a glimpse into the most prevalent threats we've observed between Nov. 26 and Dec. 3. As with previous roundups, this post isn't meant to be an in-depth analysis. Instead, this post will summarize the threats we've observed by highlighting ke
Talos Takes Ep. #79: Emotet's back with the worst type of holiday present
The latest episode of Talos Takes is available now. Download this episode and subscribe to Talos Takes using the buttons below, or visit the Talos Takes page. Emotet is back, and it brought the worst possible holiday present (just in time for peak spam season, too!). We recently
Threat Source Newsletter (Dec. 2, 2021)
Good afternoon, Talos readers. The Thanksgiving holiday in the U.S. didn't slow us down at all, even though we were all still trying to sleep off the food coma from the long weekend. But we came back this week with lots of fun content. Cisco received an early Christmas pres
Magnat campaigns use malvertising to deliver information stealer, backdoor and malicious Chrome extension
By Tiago Pereira. * Talos recently observed a malicious campaign offering fake installers of popular software as bait to get users to execute malware on their systems. * This campaign includes a set of malware distribution campaigns that started in late 2018 and have targeted
Vulnerability Spotlight: Use-after-free condition in Google Chrome could lead to code execution
Marcin Towalski of Cisco Talos discovered this vulnerability. Cisco Talos recently discovered an exploitable use-after-free vulnerability in Google Chrome. Google Chrome is a cross-platform web browser — and Chromium is the open-source version of the browser that other software
Cisco named leader in Incident Response Services
It has been more than two years already since Cisco Incident Response became a part of the Talos family. Since then, my team has continued a journey to simplify our offering for consumption and make incident response the ultimate team sport. That is why I could not be more humbl
Case Study: Catching threats ahead of time with a penetration test from the Cisco Talos Incident Response Red Team
By Brad Garnett, Miguel Alvarez Esmoris, Terryn Valikodath and Bob Doyle. As we mentioned in a previous case study, relationships are tried and tested during incident response. So, when a customer came to Cisco Talos Incident Response (Talos IR) with concerns about their public-
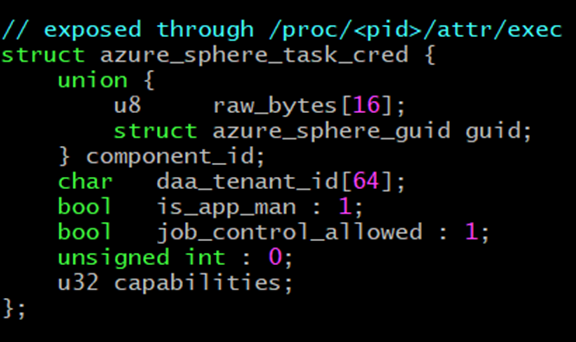
An Azure Sphere kernel exploit — or how I learned to stop worrying and love the IoT
By Claudio Bozzato and Lilith [^.^];. As part of our continued research into Microsoft Azure Sphere, there are two vulnerabilities we discovered that we feel are particularly dangerous. For a full rundown of the 31 vulnerabilities we’ve discovered over the past year, check out o
Talos Takes Ep. #78: Attackers would love to buy you a non-existent PS5 this holiday season
By Jon Munshaw. The latest episode of Talos Takes is available now. Download this episode and subscribe to Talos Takes using the buttons below, or visit the Talos Takes page. We know this episode comes around every year, but people keep falling for scams, so we have to remind p